mirror of
https://github.com/nostr-protocol/nips.git
synced 2024-11-13 23:39:08 -05:00
Merge remote-tracking branch 'nostr-protocol/master'
This commit is contained in:
commit
907153469c
149
01.md
149
01.md
|
|
@ -4,7 +4,7 @@ NIP-01
|
||||||
Basic protocol flow description
|
Basic protocol flow description
|
||||||
-------------------------------
|
-------------------------------
|
||||||
|
|
||||||
`draft` `mandatory` `author:fiatjaf` `author:distbit` `author:scsibug` `author:kukks` `author:jb55` `author:semisol`
|
`draft` `mandatory`
|
||||||
|
|
||||||
This NIP defines the basic protocol that should be implemented by everybody. New NIPs may add new optional (or mandatory) fields and messages and features to the structures and flows described here.
|
This NIP defines the basic protocol that should be implemented by everybody. New NIPs may add new optional (or mandatory) fields and messages and features to the structures and flows described here.
|
||||||
|
|
||||||
|
|
@ -14,28 +14,27 @@ Each user has a keypair. Signatures, public key, and encodings are done accordin
|
||||||
|
|
||||||
The only object type that exists is the `event`, which has the following format on the wire:
|
The only object type that exists is the `event`, which has the following format on the wire:
|
||||||
|
|
||||||
```json
|
```jsonc
|
||||||
{
|
{
|
||||||
"id": <32-bytes lowercase hex-encoded sha256 of the serialized event data>,
|
"id": <32-bytes lowercase hex-encoded sha256 of the serialized event data>,
|
||||||
"pubkey": <32-bytes lowercase hex-encoded public key of the event creator>,
|
"pubkey": <32-bytes lowercase hex-encoded public key of the event creator>,
|
||||||
"created_at": <unix timestamp in seconds>,
|
"created_at": <unix timestamp in seconds>,
|
||||||
"kind": <integer>,
|
"kind": <integer between 0 and 65535>,
|
||||||
"tags": [
|
"tags": [
|
||||||
["e", <32-bytes hex of the id of another event>, <recommended relay URL>],
|
[<arbitrary string>...],
|
||||||
["p", <32-bytes hex of a pubkey>, <recommended relay URL>],
|
// ...
|
||||||
... // other kinds of tags may be included later
|
|
||||||
],
|
],
|
||||||
"content": <arbitrary string>,
|
"content": <arbitrary string>,
|
||||||
"sig": <64-bytes hex of the signature of the sha256 hash of the serialized event data, which is the same as the "id" field>
|
"sig": <64-bytes lowercase hex of the signature of the sha256 hash of the serialized event data, which is the same as the "id" field>
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
To obtain the `event.id`, we `sha256` the serialized event. The serialization is done over the UTF-8 JSON-serialized string (with no white space or line breaks) of the following structure:
|
To obtain the `event.id`, we `sha256` the serialized event. The serialization is done over the UTF-8 JSON-serialized string (which is described below) of the following structure:
|
||||||
|
|
||||||
```json
|
```
|
||||||
[
|
[
|
||||||
0,
|
0,
|
||||||
<pubkey, as a (lowercase) hex string>,
|
<pubkey, as a lowercase hex string>,
|
||||||
<created_at, as a number>,
|
<created_at, as a number>,
|
||||||
<kind, as a number>,
|
<kind, as a number>,
|
||||||
<tags, as an array of arrays of non-null strings>,
|
<tags, as an array of arrays of non-null strings>,
|
||||||
|
|
@ -43,71 +42,135 @@ To obtain the `event.id`, we `sha256` the serialized event. The serialization is
|
||||||
]
|
]
|
||||||
```
|
```
|
||||||
|
|
||||||
|
To prevent implementation differences from creating a different event ID for the same event, the following rules MUST be followed while serializing:
|
||||||
|
- No whitespace, line breaks or other unnecessary formatting should be included in the output JSON.
|
||||||
|
- No characters except the following should be escaped, and instead should be included verbatim:
|
||||||
|
- A line break, `0x0A`, as `\n`
|
||||||
|
- A double quote, `0x22`, as `\"`
|
||||||
|
- A backslash, `0x5C`, as `\\`
|
||||||
|
- A carriage return, `0x0D`, as `\r`
|
||||||
|
- A tab character, `0x09`, as `\t`
|
||||||
|
- A backspace, `0x08`, as `\b`
|
||||||
|
- A form feed, `0x0C`, as `\f`
|
||||||
|
- UTF-8 should be used for encoding.
|
||||||
|
|
||||||
|
### Tags
|
||||||
|
|
||||||
|
Each tag is an array of one or more strings, with some conventions around them. Take a look at the example below:
|
||||||
|
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"tags": [
|
||||||
|
["e", "5c83da77af1dec6d7289834998ad7aafbd9e2191396d75ec3cc27f5a77226f36", "wss://nostr.example.com"],
|
||||||
|
["p", "f7234bd4c1394dda46d09f35bd384dd30cc552ad5541990f98844fb06676e9ca"],
|
||||||
|
["a", "30023:f7234bd4c1394dda46d09f35bd384dd30cc552ad5541990f98844fb06676e9ca:abcd", "wss://nostr.example.com"],
|
||||||
|
["alt", "reply"],
|
||||||
|
// ...
|
||||||
|
],
|
||||||
|
// ...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
The first element of the tag array is referred to as the tag _name_ or _key_ and the second as the tag _value_. So we can safely say that the event above has an `e` tag set to `"5c83da77af1dec6d7289834998ad7aafbd9e2191396d75ec3cc27f5a77226f36"`, an `alt` tag set to `"reply"` and so on. All elements after the second do not have a conventional name.
|
||||||
|
|
||||||
|
This NIP defines 3 standard tags that can be used across all event kinds with the same meaning. They are as follows:
|
||||||
|
|
||||||
|
- The `e` tag, used to refer to an event: `["e", <32-bytes lowercase hex of the id of another event>, <recommended relay URL, optional>]`
|
||||||
|
- The `p` tag, used to refer to another user: `["p", <32-bytes lowercase hex of a pubkey>, <recommended relay URL, optional>]`
|
||||||
|
- The `a` tag, used to refer to a (maybe parameterized) replaceable event
|
||||||
|
- for a parameterized replaceable event: `["a", <kind integer>:<32-bytes lowercase hex of a pubkey>:<d tag value>, <recommended relay URL, optional>]`
|
||||||
|
- for a non-parameterized replaceable event: `["a", <kind integer>:<32-bytes lowercase hex of a pubkey>:, <recommended relay URL, optional>]`
|
||||||
|
|
||||||
|
As a convention, all single-letter (only english alphabet letters: a-z, A-Z) key tags are expected to be indexed by relays, such that it is possible, for example, to query or subscribe to events that reference the event `"5c83da77af1dec6d7289834998ad7aafbd9e2191396d75ec3cc27f5a77226f36"` by using the `{"#e": ["5c83da77af1dec6d7289834998ad7aafbd9e2191396d75ec3cc27f5a77226f36"]}` filter.
|
||||||
|
|
||||||
|
### Kinds
|
||||||
|
|
||||||
|
Kinds specify how clients should interpret the meaning of each event and the other fields of each event (e.g. an `"r"` tag may have a meaning in an event of kind 1 and an entirely different meaning in an event of kind 10002). Each NIP may define the meaning of a set of kinds that weren't defined elsewhere. This NIP defines two basic kinds:
|
||||||
|
|
||||||
|
- `0`: **metadata**: the `content` is set to a stringified JSON object `{name: <username>, about: <string>, picture: <url, string>}` describing the user who created the event. [Extra metadata fields](24.md#kind-0) may be set. A relay may delete older events once it gets a new one for the same pubkey.
|
||||||
|
- `1`: **text note**: the `content` is set to the **plaintext** content of a note (anything the user wants to say). Content that must be parsed, such as Markdown and HTML, should not be used. Clients should also not parse content as those.
|
||||||
|
|
||||||
|
And also a convention for kind ranges that allow for easier experimentation and flexibility of relay implementation:
|
||||||
|
|
||||||
|
- for kind `n` such that `1000 <= n < 10000`, events are **regular**, which means they're all expected to be stored by relays.
|
||||||
|
- for kind `n` such that `10000 <= n < 20000 || n == 0 || n == 3`, events are **replaceable**, which means that, for each combination of `pubkey` and `kind`, only the latest event MUST be stored by relays, older versions MAY be discarded.
|
||||||
|
- for kind `n` such that `20000 <= n < 30000`, events are **ephemeral**, which means they are not expected to be stored by relays.
|
||||||
|
- for kind `n` such that `30000 <= n < 40000`, events are **parameterized replaceable**, which means that, for each combination of `pubkey`, `kind` and the `d` tag's first value, only the latest event MUST be stored by relays, older versions MAY be discarded.
|
||||||
|
|
||||||
|
In case of replaceable events with the same timestamp, the event with the lowest id (first in lexical order) should be retained, and the other discarded.
|
||||||
|
|
||||||
|
When answering to `REQ` messages for replaceable events such as `{"kinds":[0],"authors":[<hex-key>]}`, even if the relay has more than one version stored, it SHOULD return just the latest one.
|
||||||
|
|
||||||
|
These are just conventions and relay implementations may differ.
|
||||||
|
|
||||||
## Communication between clients and relays
|
## Communication between clients and relays
|
||||||
|
|
||||||
Relays expose a websocket endpoint to which clients can connect.
|
Relays expose a websocket endpoint to which clients can connect. Clients SHOULD open a single websocket connection to each relay and use it for all their subscriptions. Relays MAY limit number of connections from specific IP/client/etc.
|
||||||
|
|
||||||
### From client to relay: sending events and creating subscriptions
|
### From client to relay: sending events and creating subscriptions
|
||||||
|
|
||||||
Clients can send 3 types of messages, which must be JSON arrays, according to the following patterns:
|
Clients can send 3 types of messages, which must be JSON arrays, according to the following patterns:
|
||||||
|
|
||||||
* `["EVENT", <event JSON as defined above>]`, used to publish events.
|
* `["EVENT", <event JSON as defined above>]`, used to publish events.
|
||||||
* `["REQ", <subscription_id>, <filters JSON>...]`, used to request events and subscribe to new updates.
|
* `["REQ", <subscription_id>, <filters1>, <filters2>, ...]`, used to request events and subscribe to new updates.
|
||||||
* `["CLOSE", <subscription_id>]`, used to stop previous subscriptions.
|
* `["CLOSE", <subscription_id>]`, used to stop previous subscriptions.
|
||||||
|
|
||||||
`<subscription_id>` is an arbitrary, non-empty string of max length 64 chars, that should be used to represent a subscription.
|
`<subscription_id>` is an arbitrary, non-empty string of max length 64 chars. It represents a subscription per connection. Relays MUST manage `<subscription_id>`s independently for each WebSocket connection. `<subscription_id>`s are not guaranteed to be globally unique.
|
||||||
|
|
||||||
`<filters>` is a JSON object that determines what events will be sent in that subscription, it can have the following attributes:
|
`<filtersX>` is a JSON object that determines what events will be sent in that subscription, it can have the following attributes:
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"ids": <a list of event ids or prefixes>,
|
"ids": <a list of event ids>,
|
||||||
"authors": <a list of pubkeys or prefixes, the pubkey of an event must be one of these>,
|
"authors": <a list of lowercase pubkeys, the pubkey of an event must be one of these>,
|
||||||
"kinds": <a list of a kind numbers>,
|
"kinds": <a list of a kind numbers>,
|
||||||
"#e": <a list of event ids that are referenced in an "e" tag>,
|
"#<single-letter (a-zA-Z)>": <a list of tag values, for #e — a list of event ids, for #p — a list of pubkeys, etc.>,
|
||||||
"#p": <a list of pubkeys that are referenced in a "p" tag>,
|
"since": <an integer unix timestamp in seconds, events must be newer than this to pass>,
|
||||||
"since": <an integer unix timestamp, events must be newer than this to pass>,
|
"until": <an integer unix timestamp in seconds, events must be older than this to pass>,
|
||||||
"until": <an integer unix timestamp, events must be older than this to pass>,
|
"limit": <maximum number of events relays SHOULD return in the initial query>
|
||||||
"limit": <maximum number of events to be returned in the initial query>
|
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
Upon receiving a `REQ` message, the relay SHOULD query its internal database and return events that match the filter, then store that filter and send again all future events it receives to that same websocket until the websocket is closed. The `CLOSE` event is received with the same `<subscription_id>` or a new `REQ` is sent using the same `<subscription_id>`, in which case it should overwrite the previous subscription.
|
Upon receiving a `REQ` message, the relay SHOULD query its internal database and return events that match the filter, then store that filter and send again all future events it receives to that same websocket until the websocket is closed. The `CLOSE` event is received with the same `<subscription_id>` or a new `REQ` is sent using the same `<subscription_id>`, in which case relay MUST overwrite the previous subscription.
|
||||||
|
|
||||||
Filter attributes containing lists (such as `ids`, `kinds`, or `#e`) are JSON arrays with one or more values. At least one of the array's values must match the relevant field in an event for the condition itself to be considered a match. For scalar event attributes such as `kind`, the attribute from the event must be contained in the filter list. For tag attributes such as `#e`, where an event may have multiple values, the event and filter condition values must have at least one item in common.
|
Filter attributes containing lists (`ids`, `authors`, `kinds` and tag filters like `#e`) are JSON arrays with one or more values. At least one of the arrays' values must match the relevant field in an event for the condition to be considered a match. For scalar event attributes such as `authors` and `kind`, the attribute from the event must be contained in the filter list. In the case of tag attributes such as `#e`, for which an event may have multiple values, the event and filter condition values must have at least one item in common.
|
||||||
|
|
||||||
The `ids` and `authors` lists contain lowercase hexadecimal strings, which may either be an exact 64-character match, or a prefix of the event value. A prefix match is when the filter string is an exact string prefix of the event value. The use of prefixes allows for more compact filters where a large number of values are queried, and can provide some privacy for clients that may not want to disclose the exact authors or events they are searching for.
|
The `ids`, `authors`, `#e` and `#p` filter lists MUST contain exact 64-character lowercase hex values.
|
||||||
|
|
||||||
|
The `since` and `until` properties can be used to specify the time range of events returned in the subscription. If a filter includes the `since` property, events with `created_at` greater than or equal to `since` are considered to match the filter. The `until` property is similar except that `created_at` must be less than or equal to `until`. In short, an event matches a filter if `since <= created_at <= until` holds.
|
||||||
|
|
||||||
All conditions of a filter that are specified must match for an event for it to pass the filter, i.e., multiple conditions are interpreted as `&&` conditions.
|
All conditions of a filter that are specified must match for an event for it to pass the filter, i.e., multiple conditions are interpreted as `&&` conditions.
|
||||||
|
|
||||||
A `REQ` message may contain multiple filters. In this case, events that match any of the filters are to be returned, i.e., multiple filters are to be interpreted as `||` conditions.
|
A `REQ` message may contain multiple filters. In this case, events that match any of the filters are to be returned, i.e., multiple filters are to be interpreted as `||` conditions.
|
||||||
|
|
||||||
The `limit` property of a filter is only valid for the initial query and can be ignored afterward. When `limit: n` is present it is assumed that the events returned in the initial query will be the latest `n` events. It is safe to return less events than `limit` specifies, but it is expected that relays do not return (much) more events than requested so clients don't get unnecessarily overwhelmed by data.
|
The `limit` property of a filter is only valid for the initial query and MUST be ignored afterwards. When `limit: n` is present it is assumed that the events returned in the initial query will be the last `n` events ordered by the `created_at`. It is safe to return less events than `limit` specifies, but it is expected that relays do not return (much) more events than requested so clients don't get unnecessarily overwhelmed by data.
|
||||||
|
|
||||||
### From relay to client: sending events and notices
|
### From relay to client: sending events and notices
|
||||||
|
|
||||||
Relays can send 3 types of messages, which must also be JSON arrays, according to the following patterns:
|
Relays can send 5 types of messages, which must also be JSON arrays, according to the following patterns:
|
||||||
|
|
||||||
* `["EVENT", <subscription_id>, <event JSON as defined above>]`, used to send events requested by clients.
|
* `["EVENT", <subscription_id>, <event JSON as defined above>]`, used to send events requested by clients.
|
||||||
|
* `["OK", <event_id>, <true|false>, <message>]`, used to indicate acceptance or denial of an `EVENT` message.
|
||||||
* `["EOSE", <subscription_id>]`, used to indicate the _end of stored events_ and the beginning of events newly received in real-time.
|
* `["EOSE", <subscription_id>]`, used to indicate the _end of stored events_ and the beginning of events newly received in real-time.
|
||||||
|
* `["CLOSED", <subscription_id>, <message>]`, used to indicate that a subscription was ended on the server side.
|
||||||
* `["NOTICE", <message>]`, used to send human-readable error messages or other things to clients.
|
* `["NOTICE", <message>]`, used to send human-readable error messages or other things to clients.
|
||||||
|
|
||||||
This NIP defines no rules for how `NOTICE` messages should be sent or treated.
|
This NIP defines no rules for how `NOTICE` messages should be sent or treated.
|
||||||
|
|
||||||
`EVENT` messages MUST be sent only with a subscription ID related to a subscription previously initiated by the client (using the `REQ` message above).
|
- `EVENT` messages MUST be sent only with a subscription ID related to a subscription previously initiated by the client (using the `REQ` message above).
|
||||||
|
- `OK` messages MUST be sent in response to `EVENT` messages received from clients, they must have the 3rd parameter set to `true` when an event has been accepted by the relay, `false` otherwise. The 4th parameter MUST always be present, but MAY be an empty string when the 3rd is `true`, otherwise it MUST be a string formed by a machine-readable single-word prefix followed by a `:` and then a human-readable message. Some examples:
|
||||||
## Basic Event Kinds
|
* `["OK", "b1a649ebe8...", true, ""]`
|
||||||
|
* `["OK", "b1a649ebe8...", true, "pow: difficulty 25>=24"]`
|
||||||
- `0`: `set_metadata`: the `content` is set to a stringified JSON object `{name: <username>, about: <string>, picture: <url, string>}` describing the user who created the event. A relay may delete past `set_metadata` events once it gets a new one for the same pubkey.
|
* `["OK", "b1a649ebe8...", true, "duplicate: already have this event"]`
|
||||||
- `1`: `text_note`: the `content` is set to the **plaintext** content of a note (anything the user wants to say). Content that must be parsed, such as Markdown and HTML, should not be used. Clients should also not parse content as those.
|
* `["OK", "b1a649ebe8...", false, "blocked: you are banned from posting here"]`
|
||||||
- `2`: `recommend_server`: the `content` is set to the URL (e.g., `wss://somerelay.com`) of a relay the event creator wants to recommend to its followers.
|
* `["OK", "b1a649ebe8...", false, "blocked: please register your pubkey at https://my-expensive-relay.example.com"]`
|
||||||
|
* `["OK", "b1a649ebe8...", false, "rate-limited: slow down there chief"]`
|
||||||
A relay may choose to treat different message kinds differently, and it may or may not choose to have a default way to handle kinds it doesn't know about.
|
* `["OK", "b1a649ebe8...", false, "invalid: event creation date is too far off from the current time"]`
|
||||||
|
* `["OK", "b1a649ebe8...", false, "pow: difficulty 26 is less than 30"]`
|
||||||
## Other Notes:
|
* `["OK", "b1a649ebe8...", false, "error: could not connect to the database"]`
|
||||||
|
- `CLOSED` messages MUST be sent in response to a `REQ` when the relay refuses to fulfill it. It can also be sent when a relay decides to kill a subscription on its side before a client has disconnected or sent a `CLOSE`. This message uses the same pattern of `OK` messages with the machine-readable prefix and human-readable message. Some examples:
|
||||||
- Clients should not open more than one websocket to each relay. One channel can support an unlimited number of subscriptions, so clients should do that.
|
* `["CLOSED", "sub1", "duplicate: sub1 already opened"]`
|
||||||
- The `tags` array can store a tag identifier as the first element of each subarray, plus arbitrary information afterward (always as strings). This NIP defines `"p"` — meaning "pubkey", which points to a pubkey of someone that is referred to in the event —, and `"e"` — meaning "event", which points to the id of an event this event is quoting, replying to or referring to somehow. See [NIP-10](10.md) for a detailed description of "e" and "p" tags.
|
* `["CLOSED", "sub1", "unsupported: filter contains unknown elements"]`
|
||||||
- The `<recommended relay URL>` item present on the `"e"` and `"p"` tags is an optional (could be set to `""`) URL of a relay the client could attempt to connect to fetch the tagged event or other events from a tagged profile. It MAY be ignored, but it exists to increase censorship resistance and make the spread of relay addresses more seamless across clients.
|
* `["CLOSED", "sub1", "error: could not connect to the database"]`
|
||||||
- Clients should use the created_at field to judge the age of a metadata event and completely replace older metadata events with newer metadata events regardless of the order in which they arrive. Clients should not merge any filled fields within older metadata events into empty fields of newer metadata events.
|
* `["CLOSED", "sub1", "error: shutting down idle subscription"]`
|
||||||
- When a websocket is closed by the relay with a status code 4000 that means the client shouldn't try to connect again.
|
- The standardized machine-readable prefixes for `OK` and `CLOSED` are: `duplicate`, `pow`, `blocked`, `rate-limited`, `invalid`, and `error` for when none of that fits.
|
||||||
|
|
|
||||||
28
02.md
28
02.md
|
|
@ -1,14 +1,16 @@
|
||||||
NIP-02
|
NIP-02
|
||||||
======
|
======
|
||||||
|
|
||||||
Contact List and Petnames
|
Follow List
|
||||||
-------------------------
|
-----------
|
||||||
|
|
||||||
`final` `optional` `author:fiatjaf` `author:arcbtc`
|
`final` `optional`
|
||||||
|
|
||||||
A special event with kind `3`, meaning "contact list" is defined as having a list of `p` tags, one for each of the followed/known profiles one is following.
|
A special event with kind `3`, meaning "follow list" is defined as having a list of `p` tags, one for each of the followed/known profiles one is following.
|
||||||
|
|
||||||
Each tag entry should contain the key for the profile, a relay URL where events from that key can be found (can be set to an empty string if not needed), and a local name (or "petname") for that profile (can also be set to an empty string or not provided), i.e., `["p", <32-bytes hex key>, <main relay URL>, <petname>]`. The `content` can be anything and should be ignored.
|
Each tag entry should contain the key for the profile, a relay URL where events from that key can be found (can be set to an empty string if not needed), and a local name (or "petname") for that profile (can also be set to an empty string or not provided), i.e., `["p", <32-bytes hex key>, <main relay URL>, <petname>]`.
|
||||||
|
|
||||||
|
The `.content` is not used.
|
||||||
|
|
||||||
For example:
|
For example:
|
||||||
|
|
||||||
|
|
@ -25,27 +27,29 @@ For example:
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
Every new contact list that gets published overwrites the past ones, so it should contain all entries. Relays and clients SHOULD delete past contact lists as soon as they receive a new one.
|
Every new following list that gets published overwrites the past ones, so it should contain all entries. Relays and clients SHOULD delete past following lists as soon as they receive a new one.
|
||||||
|
|
||||||
|
Whenever new follows are added to an existing list, clients SHOULD append them to the end of the list, so they are stored in chronological order.
|
||||||
|
|
||||||
## Uses
|
## Uses
|
||||||
|
|
||||||
### Contact list backup
|
### Follow list backup
|
||||||
|
|
||||||
If one believes a relay will store their events for sufficient time, they can use this kind-3 event to backup their following list and recover on a different device.
|
If one believes a relay will store their events for sufficient time, they can use this kind-3 event to backup their following list and recover on a different device.
|
||||||
|
|
||||||
### Profile discovery and context augmentation
|
### Profile discovery and context augmentation
|
||||||
|
|
||||||
A client may rely on the kind-3 event to display a list of followed people by profiles one is browsing; make lists of suggestions on who to follow based on the contact lists of other people one might be following or browsing; or show the data in other contexts.
|
A client may rely on the kind-3 event to display a list of followed people by profiles one is browsing; make lists of suggestions on who to follow based on the follow lists of other people one might be following or browsing; or show the data in other contexts.
|
||||||
|
|
||||||
### Relay sharing
|
### Relay sharing
|
||||||
|
|
||||||
A client may publish a full list of contacts with good relays for each of their contacts so other clients may use these to update their internal relay lists if needed, increasing censorship-resistance.
|
A client may publish a follow list with good relays for each of their follows so other clients may use these to update their internal relay lists if needed, increasing censorship-resistance.
|
||||||
|
|
||||||
### Petname scheme
|
### Petname scheme
|
||||||
|
|
||||||
The data from these contact lists can be used by clients to construct local ["petname"](http://www.skyhunter.com/marcs/petnames/IntroPetNames.html) tables derived from other people's contact lists. This alleviates the need for global human-readable names. For example:
|
The data from these follow lists can be used by clients to construct local ["petname"](http://www.skyhunter.com/marcs/petnames/IntroPetNames.html) tables derived from other people's follow lists. This alleviates the need for global human-readable names. For example:
|
||||||
|
|
||||||
A user has an internal contact list that says
|
A user has an internal follow list that says
|
||||||
|
|
||||||
```json
|
```json
|
||||||
[
|
[
|
||||||
|
|
@ -53,7 +57,7 @@ A user has an internal contact list that says
|
||||||
]
|
]
|
||||||
```
|
```
|
||||||
|
|
||||||
And receives two contact lists, one from `21df6d143fb96c2ec9d63726bf9edc71` that says
|
And receives two follow lists, one from `21df6d143fb96c2ec9d63726bf9edc71` that says
|
||||||
|
|
||||||
```json
|
```json
|
||||||
[
|
[
|
||||||
|
|
|
||||||
31
03.md
31
03.md
|
|
@ -4,20 +4,31 @@ NIP-03
|
||||||
OpenTimestamps Attestations for Events
|
OpenTimestamps Attestations for Events
|
||||||
--------------------------------------
|
--------------------------------------
|
||||||
|
|
||||||
`draft` `optional` `author:fiatjaf`
|
`draft` `optional`
|
||||||
|
|
||||||
When there is an OTS available it MAY be included in the existing event body under the `ots` key:
|
This NIP defines an event with `kind:1040` that can contain an [OpenTimestamps](https://opentimestamps.org/) proof for any other event:
|
||||||
|
|
||||||
```
|
```json
|
||||||
{
|
{
|
||||||
"id": ...,
|
"kind": 1040
|
||||||
"kind": ...,
|
"tags": [
|
||||||
...,
|
["e", <event-id>, <relay-url>],
|
||||||
...,
|
["alt", "opentimestamps attestation"]
|
||||||
"ots": <base64-encoded OTS file data>
|
],
|
||||||
|
"content": <base64-encoded OTS file data>
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
The _event id_ MUST be used as the raw hash to be included in the OpenTimestamps merkle tree.
|
- The OpenTimestamps proof MUST prove the referenced `e` event id as its digest.
|
||||||
|
- The `content` MUST be the full content of an `.ots` file containing at least one Bitcoin attestation. This file SHOULD contain a **single** Bitcoin attestation (as not more than one valid attestation is necessary and less bytes is better than more) and no reference to "pending" attestations since they are useless in this context.
|
||||||
|
|
||||||
The attestation can be either provided by relays automatically (and the OTS binary contents just appended to the events it receives) or by clients themselves when they first upload the event to relays — and used by clients to show that an event is really "at least as old as [OTS date]".
|
### Example OpenTimestamps proof verification flow
|
||||||
|
|
||||||
|
Using [`nak`](https://github.com/fiatjaf/nak), [`jq`](https://jqlang.github.io/jq/) and [`ots`](https://github.com/fiatjaf/ots):
|
||||||
|
|
||||||
|
```bash
|
||||||
|
~> nak req -i e71c6ea722987debdb60f81f9ea4f604b5ac0664120dd64fb9d23abc4ec7c323 wss://nostr-pub.wellorder.net | jq -r .content | ots verify
|
||||||
|
> using an esplora server at https://blockstream.info/api
|
||||||
|
- sequence ending on block 810391 is valid
|
||||||
|
timestamp validated at block [810391]
|
||||||
|
```
|
||||||
|
|
|
||||||
4
04.md
4
04.md
|
|
@ -1,10 +1,12 @@
|
||||||
|
> __Warning__ `unrecommended`: deprecated in favor of [NIP-17](17.md)
|
||||||
|
|
||||||
NIP-04
|
NIP-04
|
||||||
======
|
======
|
||||||
|
|
||||||
Encrypted Direct Message
|
Encrypted Direct Message
|
||||||
------------------------
|
------------------------
|
||||||
|
|
||||||
`final` `optional` `author:arcbtc`
|
`final` `unrecommended` `optional`
|
||||||
|
|
||||||
A special event with kind `4`, meaning "encrypted direct message". It is supposed to have the following attributes:
|
A special event with kind `4`, meaning "encrypted direct message". It is supposed to have the following attributes:
|
||||||
|
|
||||||
|
|
|
||||||
10
05.md
10
05.md
|
|
@ -4,13 +4,13 @@ NIP-05
|
||||||
Mapping Nostr keys to DNS-based internet identifiers
|
Mapping Nostr keys to DNS-based internet identifiers
|
||||||
----------------------------------------------------
|
----------------------------------------------------
|
||||||
|
|
||||||
`final` `optional` `author:fiatjaf` `author:mikedilger`
|
`final` `optional`
|
||||||
|
|
||||||
On events of kind `0` (`set_metadata`) one can specify the key `"nip05"` with an [internet identifier](https://datatracker.ietf.org/doc/html/rfc5322#section-3.4.1) (an email-like address) as the value. Although there is a link to a very liberal "internet identifier" specification above, NIP-05 assumes the `<local-part>` part will be restricted to the characters `a-z0-9-_.`, case-insensitive.
|
On events of kind `0` (`metadata`) one can specify the key `"nip05"` with an [internet identifier](https://datatracker.ietf.org/doc/html/rfc5322#section-3.4.1) (an email-like address) as the value. Although there is a link to a very liberal "internet identifier" specification above, NIP-05 assumes the `<local-part>` part will be restricted to the characters `a-z0-9-_.`, case-insensitive.
|
||||||
|
|
||||||
Upon seeing that, the client splits the identifier into `<local-part>` and `<domain>` and use these values to make a GET request to `https://<domain>/.well-known/nostr.json?name=<local-part>`.
|
Upon seeing that, the client splits the identifier into `<local-part>` and `<domain>` and use these values to make a GET request to `https://<domain>/.well-known/nostr.json?name=<local-part>`.
|
||||||
|
|
||||||
The result should be a JSON document object with a key `"names"` that should then be a mapping of names to hex formatted public keys. If the public key for the given `<name>` matches the `pubkey` from the `set_metadata` event, the client then concludes that the given pubkey can indeed be referenced by its identifier.
|
The result should be a JSON document object with a key `"names"` that should then be a mapping of names to hex formatted public keys. If the public key for the given `<name>` matches the `pubkey` from the `metadata` event, the client then concludes that the given pubkey can indeed be referenced by its identifier.
|
||||||
|
|
||||||
### Example
|
### Example
|
||||||
|
|
||||||
|
|
@ -35,7 +35,7 @@ It will make a GET request to `https://example.com/.well-known/nostr.json?name=b
|
||||||
}
|
}
|
||||||
````
|
````
|
||||||
|
|
||||||
or with the **optional** `"relays"` attribute:
|
or with the **recommended** `"relays"` attribute:
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
|
|
@ -50,7 +50,7 @@ or with the **optional** `"relays"` attribute:
|
||||||
|
|
||||||
If the pubkey matches the one given in `"names"` (as in the example above) that means the association is right and the `"nip05"` identifier is valid and can be displayed.
|
If the pubkey matches the one given in `"names"` (as in the example above) that means the association is right and the `"nip05"` identifier is valid and can be displayed.
|
||||||
|
|
||||||
The optional `"relays"` attribute may contain an object with public keys as properties and arrays of relay URLs as values. When present, that can be used to help clients learn in which relays the specific user may be found. Web servers which serve `/.well-known/nostr.json` files dynamically based on the query string SHOULD also serve the relays data for any name they serve in the same reply when that is available.
|
The recommended `"relays"` attribute may contain an object with public keys as properties and arrays of relay URLs as values. When present, that can be used to help clients learn in which relays the specific user may be found. Web servers which serve `/.well-known/nostr.json` files dynamically based on the query string SHOULD also serve the relays data for any name they serve in the same reply when that is available.
|
||||||
|
|
||||||
## Finding users from their NIP-05 identifier
|
## Finding users from their NIP-05 identifier
|
||||||
|
|
||||||
|
|
|
||||||
18
06.md
18
06.md
|
|
@ -4,7 +4,7 @@ NIP-06
|
||||||
Basic key derivation from mnemonic seed phrase
|
Basic key derivation from mnemonic seed phrase
|
||||||
----------------------------------------------
|
----------------------------------------------
|
||||||
|
|
||||||
`draft` `optional` `author:fiatjaf`
|
`draft` `optional`
|
||||||
|
|
||||||
[BIP39](https://bips.xyz/39) is used to generate mnemonic seed words and derive a binary seed from them.
|
[BIP39](https://bips.xyz/39) is used to generate mnemonic seed words and derive a binary seed from them.
|
||||||
|
|
||||||
|
|
@ -13,3 +13,19 @@ Basic key derivation from mnemonic seed phrase
|
||||||
A basic client can simply use an `account` of `0` to derive a single key. For more advanced use-cases you can increment `account`, allowing generation of practically infinite keys from the 5-level path with hardened derivation.
|
A basic client can simply use an `account` of `0` to derive a single key. For more advanced use-cases you can increment `account`, allowing generation of practically infinite keys from the 5-level path with hardened derivation.
|
||||||
|
|
||||||
Other types of clients can still get fancy and use other derivation paths for their own other purposes.
|
Other types of clients can still get fancy and use other derivation paths for their own other purposes.
|
||||||
|
|
||||||
|
### Test vectors
|
||||||
|
|
||||||
|
mnemonic: leader monkey parrot ring guide accident before fence cannon height naive bean\
|
||||||
|
private key (hex): 7f7ff03d123792d6ac594bfa67bf6d0c0ab55b6b1fdb6249303fe861f1ccba9a\
|
||||||
|
nsec: nsec10allq0gjx7fddtzef0ax00mdps9t2kmtrldkyjfs8l5xruwvh2dq0lhhkp\
|
||||||
|
public key (hex): 17162c921dc4d2518f9a101db33695df1afb56ab82f5ff3e5da6eec3ca5cd917\
|
||||||
|
npub: npub1zutzeysacnf9rru6zqwmxd54mud0k44tst6l70ja5mhv8jjumytsd2x7nu
|
||||||
|
|
||||||
|
---
|
||||||
|
|
||||||
|
mnemonic: what bleak badge arrange retreat wolf trade produce cricket blur garlic valid proud rude strong choose busy staff weather area salt hollow arm fade\
|
||||||
|
private key (hex): c15d739894c81a2fcfd3a2df85a0d2c0dbc47a280d092799f144d73d7ae78add\
|
||||||
|
nsec: nsec1c9wh8xy5eqdzln7n5t0ctgxjcrdug73gp5yj0x03gntn67h83twssdfhel\
|
||||||
|
public key (hex): d41b22899549e1f3d335a31002cfd382174006e166d3e658e3a5eecdb6463573\
|
||||||
|
npub: npub16sdj9zv4f8sl85e45vgq9n7nsgt5qphpvmf7vk8r5hhvmdjxx4es8rq74h
|
||||||
|
|
|
||||||
20
07.md
20
07.md
|
|
@ -4,7 +4,7 @@ NIP-07
|
||||||
`window.nostr` capability for web browsers
|
`window.nostr` capability for web browsers
|
||||||
------------------------------------------
|
------------------------------------------
|
||||||
|
|
||||||
`draft` `optional` `author:fiatjaf`
|
`draft` `optional`
|
||||||
|
|
||||||
The `window.nostr` object may be made available by web browsers or extensions and websites or web-apps may make use of it after checking its availability.
|
The `window.nostr` object may be made available by web browsers or extensions and websites or web-apps may make use of it after checking its availability.
|
||||||
|
|
||||||
|
|
@ -12,24 +12,18 @@ That object must define the following methods:
|
||||||
|
|
||||||
```
|
```
|
||||||
async window.nostr.getPublicKey(): string // returns a public key as hex
|
async window.nostr.getPublicKey(): string // returns a public key as hex
|
||||||
async window.nostr.signEvent(event: Event): Event // takes an event object, adds `id`, `pubkey` and `sig` and returns it
|
async window.nostr.signEvent(event: { created_at: number, kind: number, tags: string[][], content: string }): Event // takes an event object, adds `id`, `pubkey` and `sig` and returns it
|
||||||
```
|
```
|
||||||
|
|
||||||
Aside from these two basic above, the following functions can also be implemented optionally:
|
Aside from these two basic above, the following functions can also be implemented optionally:
|
||||||
```
|
```
|
||||||
async window.nostr.getRelays(): { [url: string]: {read: boolean, write: boolean} } // returns a basic map of relay urls to relay policies
|
async window.nostr.getRelays(): { [url: string]: {read: boolean, write: boolean} } // returns a basic map of relay urls to relay policies
|
||||||
async window.nostr.nip04.encrypt(pubkey, plaintext): string // returns ciphertext and iv as specified in nip-04
|
async window.nostr.nip04.encrypt(pubkey, plaintext): string // returns ciphertext and iv as specified in nip-04 (deprecated)
|
||||||
async window.nostr.nip04.decrypt(pubkey, ciphertext): string // takes ciphertext and iv as specified in nip-04
|
async window.nostr.nip04.decrypt(pubkey, ciphertext): string // takes ciphertext and iv as specified in nip-04 (deprecated)
|
||||||
|
async window.nostr.nip44.encrypt(pubkey, plaintext): string // returns ciphertext as specified in nip-44
|
||||||
|
async window.nostr.nip44.decrypt(pubkey, ciphertext): string // takes ciphertext as specified in nip-44
|
||||||
```
|
```
|
||||||
|
|
||||||
### Implementation
|
### Implementation
|
||||||
|
|
||||||
- [horse](https://github.com/fiatjaf/horse) (Chrome and derivatives)
|
See https://github.com/aljazceru/awesome-nostr#nip-07-browser-extensions.
|
||||||
- [nos2x](https://github.com/fiatjaf/nos2x) (Chrome and derivatives)
|
|
||||||
- [Alby](https://getalby.com) (Chrome and derivatives, Firefox)
|
|
||||||
- [Blockcore](https://www.blockcore.net/wallet) (Chrome and derivatives)
|
|
||||||
- [nos2x-fox](https://diegogurpegui.com/nos2x-fox/) (Firefox)
|
|
||||||
- [Flamingo](https://www.getflamingo.org/) (Chrome and derivatives)
|
|
||||||
- [AKA Profiles](https://github.com/neilck/aka-extension) (Chrome, stores multiple keys)
|
|
||||||
- [TokenPocket](https://www.tokenpocket.pro/) (Android, IOS, Chrome and derivatives)
|
|
||||||
- [Nostrmo](https://github.com/haorendashu/nostrmo_faq#download) (Android, IOS)
|
|
||||||
|
|
|
||||||
2
08.md
2
08.md
|
|
@ -6,7 +6,7 @@ NIP-08
|
||||||
Handling Mentions
|
Handling Mentions
|
||||||
-----------------
|
-----------------
|
||||||
|
|
||||||
`final` `unrecommended` `optional` `author:fiatjaf` `author:scsibug`
|
`final` `unrecommended` `optional`
|
||||||
|
|
||||||
This document standardizes the treatment given by clients of inline mentions of other events and pubkeys inside the content of `text_note`s.
|
This document standardizes the treatment given by clients of inline mentions of other events and pubkeys inside the content of `text_note`s.
|
||||||
|
|
||||||
|
|
|
||||||
4
09.md
4
09.md
|
|
@ -4,11 +4,11 @@ NIP-09
|
||||||
Event Deletion
|
Event Deletion
|
||||||
--------------
|
--------------
|
||||||
|
|
||||||
`draft` `optional` `author:scsibug`
|
`draft` `optional`
|
||||||
|
|
||||||
A special event with kind `5`, meaning "deletion" is defined as having a list of one or more `e` tags, each referencing an event the author is requesting to be deleted.
|
A special event with kind `5`, meaning "deletion" is defined as having a list of one or more `e` tags, each referencing an event the author is requesting to be deleted.
|
||||||
|
|
||||||
Each tag entry must contain an "e" event id and/or NIP-33 `a` tags intended for deletion.
|
Each tag entry must contain an "e" event id and/or `a` tags intended for deletion.
|
||||||
|
|
||||||
The event's `content` field MAY contain a text note describing the reason for the deletion.
|
The event's `content` field MAY contain a text note describing the reason for the deletion.
|
||||||
|
|
||||||
|
|
|
||||||
10
10.md
10
10.md
|
|
@ -5,7 +5,7 @@ NIP-10
|
||||||
On "e" and "p" tags in Text Events (kind 1).
|
On "e" and "p" tags in Text Events (kind 1).
|
||||||
--------------------------------------------
|
--------------------------------------------
|
||||||
|
|
||||||
`draft` `optional` `author:unclebobmartin`
|
`draft` `optional`
|
||||||
|
|
||||||
## Abstract
|
## Abstract
|
||||||
This NIP describes how to use "e" and "p" tags in text events, especially those that are replies to other text events. It helps clients thread the replies into a tree rooted at the original event.
|
This NIP describes how to use "e" and "p" tags in text events, especially those that are replies to other text events. It helps clients thread the replies into a tree rooted at the original event.
|
||||||
|
|
@ -33,25 +33,27 @@ Where:
|
||||||
|
|
||||||
* Many "e" tags: `["e", <root-id>]` `["e", <mention-id>]`, ..., `["e", <reply-id>]`<br>
|
* Many "e" tags: `["e", <root-id>]` `["e", <mention-id>]`, ..., `["e", <reply-id>]`<br>
|
||||||
There may be any number of `<mention-ids>`. These are the ids of events which may, or may not be in the reply chain.
|
There may be any number of `<mention-ids>`. These are the ids of events which may, or may not be in the reply chain.
|
||||||
They are citings from this event. `root-id` and `reply-id` are as above.
|
They are citing from this event. `root-id` and `reply-id` are as above.
|
||||||
|
|
||||||
>This scheme is deprecated because it creates ambiguities that are difficult, or impossible to resolve when an event references another but is not a reply.
|
>This scheme is deprecated because it creates ambiguities that are difficult, or impossible to resolve when an event references another but is not a reply.
|
||||||
|
|
||||||
## Marked "e" tags (PREFERRED)
|
## Marked "e" tags (PREFERRED)
|
||||||
`["e", <event-id>, <relay-url>, <marker>]`
|
`["e", <event-id>, <relay-url>, <marker>, <pubkey>]`
|
||||||
|
|
||||||
Where:
|
Where:
|
||||||
|
|
||||||
* `<event-id>` is the id of the event being referenced.
|
* `<event-id>` is the id of the event being referenced.
|
||||||
* `<relay-url>` is the URL of a recommended relay associated with the reference. Clients SHOULD add a valid `<relay-URL>` field, but may instead leave it as `""`.
|
* `<relay-url>` is the URL of a recommended relay associated with the reference. Clients SHOULD add a valid `<relay-URL>` field, but may instead leave it as `""`.
|
||||||
* `<marker>` is optional and if present is one of `"reply"`, `"root"`, or `"mention"`.
|
* `<marker>` is optional and if present is one of `"reply"`, `"root"`, or `"mention"`.
|
||||||
|
* `<pubkey>` is optional, SHOULD be the pubkey of the author of the referenced event
|
||||||
|
|
||||||
**The order of marked "e" tags is not relevant.** Those marked with `"reply"` denote the id of the reply event being responded to. Those marked with `"root"` denote the root id of the reply thread being responded to. For top level replies (those replying directly to the root event), only the `"root"` marker should be used. Those marked with `"mention"` denote a quoted or reposted event id.
|
Those marked with `"reply"` denote the id of the reply event being responded to. Those marked with `"root"` denote the root id of the reply thread being responded to. For top level replies (those replying directly to the root event), only the `"root"` marker should be used. Those marked with `"mention"` denote a quoted or reposted event id.
|
||||||
|
|
||||||
A direct reply to the root of a thread should have a single marked "e" tag of type "root".
|
A direct reply to the root of a thread should have a single marked "e" tag of type "root".
|
||||||
|
|
||||||
>This scheme is preferred because it allows events to mention others without confusing them with `<reply-id>` or `<root-id>`.
|
>This scheme is preferred because it allows events to mention others without confusing them with `<reply-id>` or `<root-id>`.
|
||||||
|
|
||||||
|
`<pubkey>` SHOULD be the pubkey of the author of the `e` tagged event, this is used in the outbox model to search for that event from the authors write relays where relay hints did not resolve the event.
|
||||||
|
|
||||||
## The "p" tag
|
## The "p" tag
|
||||||
Used in a text event contains a list of pubkeys used to record who is involved in a reply thread.
|
Used in a text event contains a list of pubkeys used to record who is involved in a reply thread.
|
||||||
|
|
|
||||||
133
11.md
133
11.md
|
|
@ -4,7 +4,7 @@ NIP-11
|
||||||
Relay Information Document
|
Relay Information Document
|
||||||
---------------------------
|
---------------------------
|
||||||
|
|
||||||
`draft` `optional` `author:scsibug` `author:doc-hex` `author:cameri`
|
`draft` `optional`
|
||||||
|
|
||||||
Relays may provide server metadata to clients to inform them of capabilities, administrative contacts, and various server attributes. This is made available as a JSON document over HTTP, on the same URI as the relay's websocket.
|
Relays may provide server metadata to clients to inform them of capabilities, administrative contacts, and various server attributes. This is made available as a JSON document over HTTP, on the same URI as the relay's websocket.
|
||||||
|
|
||||||
|
|
@ -25,42 +25,42 @@ When a relay receives an HTTP(s) request with an `Accept` header of `application
|
||||||
Any field may be omitted, and clients MUST ignore any additional fields they do not understand. Relays MUST accept CORS requests by sending `Access-Control-Allow-Origin`, `Access-Control-Allow-Headers`, and `Access-Control-Allow-Methods` headers.
|
Any field may be omitted, and clients MUST ignore any additional fields they do not understand. Relays MUST accept CORS requests by sending `Access-Control-Allow-Origin`, `Access-Control-Allow-Headers`, and `Access-Control-Allow-Methods` headers.
|
||||||
|
|
||||||
Field Descriptions
|
Field Descriptions
|
||||||
-----------------
|
------------------
|
||||||
|
|
||||||
### Name ###
|
### Name
|
||||||
|
|
||||||
A relay may select a `name` for use in client software. This is a string, and SHOULD be less than 30 characters to avoid client truncation.
|
A relay may select a `name` for use in client software. This is a string, and SHOULD be less than 30 characters to avoid client truncation.
|
||||||
|
|
||||||
### Description ###
|
### Description
|
||||||
|
|
||||||
Detailed plain-text information about the relay may be contained in the `description` string. It is recommended that this contain no markup, formatting or line breaks for word wrapping, and simply use double newline characters to separate paragraphs. There are no limitations on length.
|
Detailed plain-text information about the relay may be contained in the `description` string. It is recommended that this contain no markup, formatting or line breaks for word wrapping, and simply use double newline characters to separate paragraphs. There are no limitations on length.
|
||||||
|
|
||||||
### Pubkey ###
|
### Pubkey
|
||||||
|
|
||||||
An administrative contact may be listed with a `pubkey`, in the same format as Nostr events (32-byte hex for a `secp256k1` public key). If a contact is listed, this provides clients with a recommended address to send encrypted direct messages (See `NIP-04`) to a system administrator. Expected uses of this address are to report abuse or illegal content, file bug reports, or request other technical assistance.
|
An administrative contact may be listed with a `pubkey`, in the same format as Nostr events (32-byte hex for a `secp256k1` public key). If a contact is listed, this provides clients with a recommended address to send encrypted direct messages (See [NIP-17](17.md)) to a system administrator. Expected uses of this address are to report abuse or illegal content, file bug reports, or request other technical assistance.
|
||||||
|
|
||||||
Relay operators have no obligation to respond to direct messages.
|
Relay operators have no obligation to respond to direct messages.
|
||||||
|
|
||||||
### Contact ###
|
### Contact
|
||||||
|
|
||||||
An alternative contact may be listed under the `contact` field as well, with the same purpose as `pubkey`. Use of a Nostr public key and direct message SHOULD be preferred over this. Contents of this field SHOULD be a URI, using schemes such as `mailto` or `https` to provide users with a means of contact.
|
An alternative contact may be listed under the `contact` field as well, with the same purpose as `pubkey`. Use of a Nostr public key and direct message SHOULD be preferred over this. Contents of this field SHOULD be a URI, using schemes such as `mailto` or `https` to provide users with a means of contact.
|
||||||
|
|
||||||
### Supported NIPs ###
|
### Supported NIPs
|
||||||
|
|
||||||
As the Nostr protocol evolves, some functionality may only be available by relays that implement a specific `NIP`. This field is an array of the integer identifiers of `NIP`s that are implemented in the relay. Examples would include `1`, for `"NIP-01"` and `9`, for `"NIP-09"`. Client-side `NIPs` SHOULD NOT be advertised, and can be ignored by clients.
|
As the Nostr protocol evolves, some functionality may only be available by relays that implement a specific `NIP`. This field is an array of the integer identifiers of `NIP`s that are implemented in the relay. Examples would include `1`, for `"NIP-01"` and `9`, for `"NIP-09"`. Client-side `NIPs` SHOULD NOT be advertised, and can be ignored by clients.
|
||||||
|
|
||||||
### Software ###
|
### Software
|
||||||
|
|
||||||
The relay server implementation MAY be provided in the `software` attribute. If present, this MUST be a URL to the project's homepage.
|
The relay server implementation MAY be provided in the `software` attribute. If present, this MUST be a URL to the project's homepage.
|
||||||
|
|
||||||
### Version ###
|
### Version
|
||||||
|
|
||||||
The relay MAY choose to publish its software version as a string attribute. The string format is defined by the relay implementation. It is recommended this be a version number or commit identifier.
|
The relay MAY choose to publish its software version as a string attribute. The string format is defined by the relay implementation. It is recommended this be a version number or commit identifier.
|
||||||
|
|
||||||
Extra Fields
|
Extra Fields
|
||||||
-----------------
|
------------
|
||||||
|
|
||||||
### Server Limitations ###
|
### Server Limitations
|
||||||
|
|
||||||
These are limitations imposed by the relay on clients. Your client
|
These are limitations imposed by the relay on clients. Your client
|
||||||
should expect that requests which exceed these *practical* limitations
|
should expect that requests which exceed these *practical* limitations
|
||||||
|
|
@ -68,20 +68,21 @@ are rejected or fail immediately.
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
...
|
|
||||||
"limitation": {
|
"limitation": {
|
||||||
"max_message_length": 16384,
|
"max_message_length": 16384,
|
||||||
"max_subscriptions": 20,
|
"max_subscriptions": 20,
|
||||||
"max_filters": 100,
|
"max_filters": 100,
|
||||||
"max_limit": 5000,
|
"max_limit": 5000,
|
||||||
"max_subid_length": 100,
|
"max_subid_length": 100,
|
||||||
"min_prefix": 4,
|
|
||||||
"max_event_tags": 100,
|
"max_event_tags": 100,
|
||||||
"max_content_length": 8196,
|
"max_content_length": 8196,
|
||||||
"min_pow_difficulty": 30,
|
"min_pow_difficulty": 30,
|
||||||
"auth_required": true,
|
"auth_required": true,
|
||||||
"payment_required": true,
|
"payment_required": true,
|
||||||
}
|
"restricted_writes": true,
|
||||||
|
"created_at_lower_limit": 31536000,
|
||||||
|
"created_at_upper_limit": 3
|
||||||
|
},
|
||||||
...
|
...
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
@ -102,9 +103,6 @@ Must be one or higher.
|
||||||
|
|
||||||
- `max_subid_length`: maximum length of subscription id as a string.
|
- `max_subid_length`: maximum length of subscription id as a string.
|
||||||
|
|
||||||
- `min_prefix`: for `authors` and `ids` filters which are to match against
|
|
||||||
a hex prefix, you must provide at least this many hex digits in the prefix.
|
|
||||||
|
|
||||||
- `max_limit`: the relay server will clamp each filter's `limit` value to this number.
|
- `max_limit`: the relay server will clamp each filter's `limit` value to this number.
|
||||||
This means the client won't be able to get more than this number
|
This means the client won't be able to get more than this number
|
||||||
of events from a single subscription filter. This clamping is typically done silently
|
of events from a single subscription filter. This clamping is typically done silently
|
||||||
|
|
@ -127,7 +125,17 @@ Even if set to False, authentication may be required for specific actions.
|
||||||
|
|
||||||
- `payment_required`: this relay requires payment before a new connection may perform any action.
|
- `payment_required`: this relay requires payment before a new connection may perform any action.
|
||||||
|
|
||||||
### Event Retention ###
|
- `restricted_writes`: this relay requires some kind of condition to be fulfilled in order to
|
||||||
|
accept events (not necessarily, but including `payment_required` and `min_pow_difficulty`).
|
||||||
|
This should only be set to `true` when users are expected to know the relay policy before trying
|
||||||
|
to write to it -- like belonging to a special pubkey-based whitelist or writing only events of
|
||||||
|
a specific niche kind or content. Normal anti-spam heuristics, for example, do not qualify.
|
||||||
|
|
||||||
|
- `created_at_lower_limit`: 'created_at' lower limit
|
||||||
|
|
||||||
|
- `created_at_upper_limit`: 'created_at' upper limit
|
||||||
|
|
||||||
|
### Event Retention
|
||||||
|
|
||||||
There may be a cost associated with storing data forever, so relays
|
There may be a cost associated with storing data forever, so relays
|
||||||
may wish to state retention times. The values stated here are defaults
|
may wish to state retention times. The values stated here are defaults
|
||||||
|
|
@ -140,14 +148,12 @@ all, and preferably an error will be provided when those are received.
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
...
|
|
||||||
"retention": [
|
"retention": [
|
||||||
{"kinds": [0, 1, [5, 7], [40, 49]], "time": 3600},
|
{"kinds": [0, 1, [5, 7], [40, 49]], "time": 3600},
|
||||||
{"kinds": [[40000, 49999]], "time": 100},
|
{"kinds": [[40000, 49999]], "time": 100},
|
||||||
{"kinds": [[30000, 39999]], "count": 1000},
|
{"kinds": [[30000, 39999]], "count": 1000},
|
||||||
{"time": 3600, "count": 10000}
|
{"time": 3600, "count": 10000}
|
||||||
]
|
]
|
||||||
...
|
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
|
|
@ -161,11 +167,9 @@ a specific `kind` number, by giving a retention time of zero for those `kind` va
|
||||||
While that is unfortunate, it does allow clients to discover servers that will
|
While that is unfortunate, it does allow clients to discover servers that will
|
||||||
support their protocol quickly via a single HTTP fetch.
|
support their protocol quickly via a single HTTP fetch.
|
||||||
|
|
||||||
There is no need to specify retention times for _ephemeral events_ as defined
|
There is no need to specify retention times for _ephemeral events_ since they are not retained.
|
||||||
in [NIP-16](16.md) since they are not retained.
|
|
||||||
|
|
||||||
|
### Content Limitations
|
||||||
### Content Limitations ###
|
|
||||||
|
|
||||||
Some relays may be governed by the arbitrary laws of a nation state. This
|
Some relays may be governed by the arbitrary laws of a nation state. This
|
||||||
may limit what content can be stored in cleartext on those relays. All
|
may limit what content can be stored in cleartext on those relays. All
|
||||||
|
|
@ -184,7 +188,6 @@ flexibility is up to the client software.
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
...
|
|
||||||
"relay_countries": [ "CA", "US" ],
|
"relay_countries": [ "CA", "US" ],
|
||||||
...
|
...
|
||||||
}
|
}
|
||||||
|
|
@ -198,7 +201,7 @@ country of the legal entities who own the relay, so it's very
|
||||||
likely a number of countries are involved.
|
likely a number of countries are involved.
|
||||||
|
|
||||||
|
|
||||||
### Community Preferences ###
|
### Community Preferences
|
||||||
|
|
||||||
For public text notes at least, a relay may try to foster a
|
For public text notes at least, a relay may try to foster a
|
||||||
local community. This would encourage users to follow the global
|
local community. This would encourage users to follow the global
|
||||||
|
|
@ -207,7 +210,6 @@ To support this goal, relays MAY specify some of the following values.
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
...
|
|
||||||
"language_tags": ["en", "en-419"],
|
"language_tags": ["en", "en-419"],
|
||||||
"tags": ["sfw-only", "bitcoin-only", "anime"],
|
"tags": ["sfw-only", "bitcoin-only", "anime"],
|
||||||
"posting_policy": "https://example.com/posting-policy.html",
|
"posting_policy": "https://example.com/posting-policy.html",
|
||||||
|
|
@ -238,13 +240,12 @@ detail and legal terms. Use the `tags` field to signify limitations
|
||||||
on content, or topics to be discussed, which could be machine
|
on content, or topics to be discussed, which could be machine
|
||||||
processed by appropriate client software.
|
processed by appropriate client software.
|
||||||
|
|
||||||
### Pay-To-Relay ###
|
### Pay-to-Relay
|
||||||
|
|
||||||
Relays that require payments may want to expose their fee schedules.
|
Relays that require payments may want to expose their fee schedules.
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
...
|
|
||||||
"payments_url": "https://my-relay/payments",
|
"payments_url": "https://my-relay/payments",
|
||||||
"fees": {
|
"fees": {
|
||||||
"admission": [{ "amount": 1000000, "unit": "msats" }],
|
"admission": [{ "amount": 1000000, "unit": "msats" }],
|
||||||
|
|
@ -255,43 +256,59 @@ Relays that require payments may want to expose their fee schedules.
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
### Icon ###
|
### Icon
|
||||||
|
|
||||||
A URL pointing to an image to be used as an icon for the relay. Recommended to be squared in shape.
|
A URL pointing to an image to be used as an icon for the relay. Recommended to be squared in shape.
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
...
|
|
||||||
"icon": "https://nostr.build/i/53866b44135a27d624e99c6165cabd76ac8f72797209700acb189fce75021f47.jpg",
|
"icon": "https://nostr.build/i/53866b44135a27d624e99c6165cabd76ac8f72797209700acb189fce75021f47.jpg",
|
||||||
...
|
...
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
### Examples ###
|
### Examples
|
||||||
As of 2 May 2023 the following `curl` command provided these results.
|
|
||||||
|
|
||||||
>curl -H "Accept: application/nostr+json" https://eden.nostr.land
|
As of 2 May 2023 the following command provided these results:
|
||||||
|
|
||||||
{"name":"eden.nostr.land",
|
```
|
||||||
"description":"Eden Nostr Land - Toronto 1-01",
|
~> curl -H "Accept: application/nostr+json" https://eden.nostr.land | jq
|
||||||
"pubkey":"00000000827ffaa94bfea288c3dfce4422c794fbb96625b6b31e9049f729d700",
|
|
||||||
"contact":"me@ricardocabral.io",
|
{
|
||||||
"supported_nips":[1,2,4,9,11,12,15,16,20,22,26,28,33,40],
|
"description": "nostr.land family of relays (us-or-01)",
|
||||||
"supported_nip_extensions":["11a"],
|
"name": "nostr.land",
|
||||||
"software":"git+https://github.com/Cameri/nostream.git",
|
"pubkey": "52b4a076bcbbbdc3a1aefa3735816cf74993b1b8db202b01c883c58be7fad8bd",
|
||||||
"version":"1.22.6",
|
"software": "custom",
|
||||||
"limitation":{"max_message_length":1048576,
|
"supported_nips": [
|
||||||
"max_subscriptions":10,
|
1,
|
||||||
"max_filters":2500,
|
2,
|
||||||
"max_limit":5000,
|
4,
|
||||||
"max_subid_length":256,
|
9,
|
||||||
"min_prefix":4,
|
11,
|
||||||
"max_event_tags":2500,
|
12,
|
||||||
"max_content_length":65536,
|
16,
|
||||||
"min_pow_difficulty":0,
|
20,
|
||||||
"auth_required":false,
|
22,
|
||||||
"payment_required":true},
|
28,
|
||||||
"payments_url":"https://eden.nostr.land/invoices",
|
33,
|
||||||
"fees":{"admission":[{"amount":5000000,"unit":"msats"}],
|
40
|
||||||
"publication":[]}},
|
],
|
||||||
"icon": "https://nostr.build/i/53866b44135a27d624e99c6165cabd76ac8f72797209700acb189fce75021f47.jpg"
|
"version": "1.0.1",
|
||||||
|
"limitation": {
|
||||||
|
"payment_required": true,
|
||||||
|
"max_message_length": 65535,
|
||||||
|
"max_event_tags": 2000,
|
||||||
|
"max_subscriptions": 20,
|
||||||
|
"auth_required": false
|
||||||
|
},
|
||||||
|
"payments_url": "https://eden.nostr.land",
|
||||||
|
"fees": {
|
||||||
|
"subscription": [
|
||||||
|
{
|
||||||
|
"amount": 2500000,
|
||||||
|
"unit": "msats",
|
||||||
|
"period": 2592000
|
||||||
|
}
|
||||||
|
]
|
||||||
|
},
|
||||||
|
}
|
||||||
|
|
|
||||||
37
12.md
37
12.md
|
|
@ -4,39 +4,6 @@ NIP-12
|
||||||
Generic Tag Queries
|
Generic Tag Queries
|
||||||
-------------------
|
-------------------
|
||||||
|
|
||||||
`draft` `optional` `author:scsibug` `author:fiatjaf`
|
`final` `mandatory`
|
||||||
|
|
||||||
Relays may support subscriptions over arbitrary tags. `NIP-01` requires relays to respond to queries for `e` and `p` tags. This NIP allows any single-letter tag present in an event to be queried.
|
Moved to [NIP-01](01.md).
|
||||||
|
|
||||||
The `<filters>` object described in `NIP-01` is expanded to contain arbitrary keys with a `#` prefix. Any single-letter key in a filter beginning with `#` is a tag query, and MUST have a value of an array of strings. The filter condition matches if the event has a tag with the same name, and there is at least one tag value in common with the filter and event. The tag name is the letter without the `#`, and the tag value is the second element. Subsequent elements are ignored for the purposes of tag queries.
|
|
||||||
|
|
||||||
Example Subscription Filter
|
|
||||||
---------------------------
|
|
||||||
|
|
||||||
The following provides an example of a filter that matches events of kind `1` with an `r` tag set to either `foo` or `bar`.
|
|
||||||
|
|
||||||
```
|
|
||||||
{
|
|
||||||
"kinds": [1],
|
|
||||||
"#r": ["foo", "bar"]
|
|
||||||
}
|
|
||||||
```
|
|
||||||
|
|
||||||
Client Behavior
|
|
||||||
---------------
|
|
||||||
|
|
||||||
Clients SHOULD use the `supported_nips` field to learn if a relay supports generic tag queries. Clients MAY send generic tag queries to any relay, if they are prepared to filter out extraneous responses from relays that do not support this NIP.
|
|
||||||
|
|
||||||
Rationale
|
|
||||||
---------
|
|
||||||
|
|
||||||
The decision to reserve only single-letter tags to be usable in queries allow applications to make use of tags for all sorts of metadata, as it is their main purpose, without worrying that they might be bloating relay indexes. That also makes relays more lightweight, of course. And if some application or user is abusing single-letter tags with the intention of bloating relays that becomes easier to detect as single-letter tags will hardly be confused with some actually meaningful metadata some application really wanted to attach to the event with no spammy intentions.
|
|
||||||
|
|
||||||
Suggested Use Cases
|
|
||||||
-------------------
|
|
||||||
|
|
||||||
Motivating examples for generic tag queries are provided below. This NIP does not promote or standardize the use of any specific tag for any purpose.
|
|
||||||
|
|
||||||
* Decentralized Commenting System: clients can comment on arbitrary web pages, and easily search for other comments, by using a `r` ("reference", in this case an URL) tag and value.
|
|
||||||
* Location-specific Posts: clients can use a `g` ("geohash") tag to associate a post with a physical location. Clients can search for a set of geohashes of varying precisions near them to find local content.
|
|
||||||
* Hashtags: clients can use simple `t` ("hashtag") tags to associate an event with an easily searchable topic name. Since Nostr events themselves are not searchable through the protocol, this provides a mechanism for user-driven search.
|
|
||||||
|
|
|
||||||
10
13.md
10
13.md
|
|
@ -4,7 +4,7 @@ NIP-13
|
||||||
Proof of Work
|
Proof of Work
|
||||||
-------------
|
-------------
|
||||||
|
|
||||||
`draft` `optional` `author:jb55` `author:cameri`
|
`draft` `optional`
|
||||||
|
|
||||||
This NIP defines a way to generate and interpret Proof of Work for nostr notes. Proof of Work (PoW) is a way to add a proof of computational work to a note. This is a bearer proof that all relays and clients can universally validate with a small amount of code. This proof can be used as a means of spam deterrence.
|
This NIP defines a way to generate and interpret Proof of Work for nostr notes. Proof of Work (PoW) is a way to add a proof of computational work to a note. This is a bearer proof that all relays and clients can universally validate with a small amount of code. This proof can be used as a means of spam deterrence.
|
||||||
|
|
||||||
|
|
@ -35,11 +35,7 @@ Example mined note
|
||||||
"created_at": 1651794653,
|
"created_at": 1651794653,
|
||||||
"kind": 1,
|
"kind": 1,
|
||||||
"tags": [
|
"tags": [
|
||||||
[
|
["nonce", "776797", "20"]
|
||||||
"nonce",
|
|
||||||
"776797",
|
|
||||||
"21"
|
|
||||||
]
|
|
||||||
],
|
],
|
||||||
"content": "It's just me mining my own business",
|
"content": "It's just me mining my own business",
|
||||||
"sig": "284622fc0a3f4f1303455d5175f7ba962a3300d136085b9566801bc2e0699de0c7e31e44c81fb40ad9049173742e904713c3594a1da0fc5d2382a25c11aba977"
|
"sig": "284622fc0a3f4f1303455d5175f7ba962a3300d136085b9566801bc2e0699de0c7e31e44c81fb40ad9049173742e904713c3594a1da0fc5d2382a25c11aba977"
|
||||||
|
|
@ -110,7 +106,7 @@ function countLeadingZeroes(hex) {
|
||||||
Querying relays for PoW notes
|
Querying relays for PoW notes
|
||||||
-----------------------------
|
-----------------------------
|
||||||
|
|
||||||
Since relays allow searching on prefixes, you can use this as a way to filter notes of a certain difficulty:
|
If relays allow searching on prefixes, you can use this as a way to filter notes of a certain difficulty:
|
||||||
|
|
||||||
```
|
```
|
||||||
$ echo '["REQ", "subid", {"ids": ["000000000"]}]' | websocat wss://some-relay.com | jq -c '.[2]'
|
$ echo '["REQ", "subid", {"ids": ["000000000"]}]' | websocat wss://some-relay.com | jq -c '.[2]'
|
||||||
|
|
|
||||||
10
14.md
10
14.md
|
|
@ -1,15 +1,17 @@
|
||||||
NIP-14
|
NIP-14
|
||||||
======
|
======
|
||||||
|
|
||||||
Subject tag in Text events.
|
Subject tag in Text events
|
||||||
---------------------------
|
--------------------------
|
||||||
|
|
||||||
`draft` `optional` `author:unclebobmartin`
|
`draft` `optional`
|
||||||
|
|
||||||
This NIP defines the use of the "subject" tag in text (kind: 1) events.
|
This NIP defines the use of the "subject" tag in text (kind: 1) events.
|
||||||
(implemented in more-speech)
|
(implemented in more-speech)
|
||||||
|
|
||||||
`["subject": <string>]`
|
```json
|
||||||
|
["subject": <string>]
|
||||||
|
```
|
||||||
|
|
||||||
Browsers often display threaded lists of messages. The contents of the subject tag can be used in such lists, instead of the more ad hoc approach of using the first few words of the message. This is very similar to the way email browsers display lists of incoming emails by subject rather than by contents.
|
Browsers often display threaded lists of messages. The contents of the subject tag can be used in such lists, instead of the more ad hoc approach of using the first few words of the message. This is very similar to the way email browsers display lists of incoming emails by subject rather than by contents.
|
||||||
|
|
||||||
|
|
|
||||||
260
15.md
260
15.md
|
|
@ -1,14 +1,14 @@
|
||||||
NIP-15
|
NIP-15
|
||||||
======
|
======
|
||||||
|
|
||||||
Nostr Marketplace (for resilient marketplaces)
|
Nostr Marketplace
|
||||||
-----------------------------------
|
-----------------
|
||||||
|
|
||||||
`draft` `optional` `author:fiatjaf` `author:benarc` `author:motorina0` `author:talvasconcelos`
|
`draft` `optional`
|
||||||
|
|
||||||
> Based on https://github.com/lnbits/Diagon-Alley
|
Based on https://github.com/lnbits/Diagon-Alley.
|
||||||
|
|
||||||
> Implemented here https://github.com/lnbits/nostrmarket
|
Implemented in [NostrMarket](https://github.com/lnbits/nostrmarket) and [Plebeian Market](https://github.com/PlebeianTech/plebeian-market).
|
||||||
|
|
||||||
## Terms
|
## Terms
|
||||||
|
|
||||||
|
|
@ -33,29 +33,30 @@ The `merchant` admin software can be purely clientside, but for `convenience` an
|
||||||
## `Merchant` publishing/updating products (event)
|
## `Merchant` publishing/updating products (event)
|
||||||
|
|
||||||
A merchant can publish these events:
|
A merchant can publish these events:
|
||||||
| Kind | | Description | NIP |
|
| Kind | | Description |
|
||||||
|---------|------------------|---------------------------------------------------------------------------------------------------------------|-----------------------------------------|
|
| --------- | ------------------ | --------------------------------------------------------------------------------------------------------------- |
|
||||||
| `0 ` | `set_meta` | The merchant description (similar with any `nostr` public key). | [NIP01 ](https://github.com/nostr-protocol/nips/blob/master/01.md) |
|
| `0` | `set_meta` | The merchant description (similar with any `nostr` public key). |
|
||||||
| `30017` | `set_stall` | Create or update a stall. | [NIP33](https://github.com/nostr-protocol/nips/blob/master/33.md) (Parameterized Replaceable Event) |
|
| `30017` | `set_stall` | Create or update a stall. |
|
||||||
| `30018` | `set_product` | Create or update a product. | [NIP33](https://github.com/nostr-protocol/nips/blob/master/33.md) (Parameterized Replaceable Event) |
|
| `30018` | `set_product` | Create or update a product. |
|
||||||
| `4 ` | `direct_message` | Communicate with the customer. The messages can be plain-text or JSON. | [NIP04](https://github.com/nostr-protocol/nips/blob/master/04.md) |
|
| `4` | `direct_message` | Communicate with the customer. The messages can be plain-text or JSON. |
|
||||||
| `5 ` | `delete` | Delete a product or a stall. | [NIP09](https://github.com/nostr-protocol/nips/blob/master/09.md) |
|
| `5` | `delete` | Delete a product or a stall. |
|
||||||
|
|
||||||
### Event `30017`: Create or update a stall.
|
### Event `30017`: Create or update a stall.
|
||||||
|
|
||||||
**Event Content**:
|
**Event Content**
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"id": <String, UUID generated by the merchant. Sequential IDs (`0`, `1`, `2`...) are discouraged>,
|
"id": <string, id generated by the merchant. Sequential IDs (`0`, `1`, `2`...) are discouraged>,
|
||||||
"name": <String, stall name>,
|
"name": <string, stall name>,
|
||||||
"description": <String (optional), stall description>,
|
"description": <string (optional), stall description>,
|
||||||
"currency": <String, currency used>,
|
"currency": <string, currency used>,
|
||||||
"shipping": [
|
"shipping": [
|
||||||
{
|
{
|
||||||
"id": <String, UUID of the shipping zone, generated by the merchant>,
|
"id": <string, id of the shipping zone, generated by the merchant>,
|
||||||
"name": <String (optional), zone name>,
|
"name": <string (optional), zone name>,
|
||||||
"cost": <float, cost for shipping. The currency is defined at the stall level>,
|
"cost": <float, base cost for shipping. The currency is defined at the stall level>,
|
||||||
"countries": [<String, countries included in this zone>],
|
"regions": [<string, regions included in this zone>]
|
||||||
}
|
}
|
||||||
]
|
]
|
||||||
}
|
}
|
||||||
|
|
@ -63,58 +64,82 @@ A merchant can publish these events:
|
||||||
|
|
||||||
Fields that are not self-explanatory:
|
Fields that are not self-explanatory:
|
||||||
- `shipping`:
|
- `shipping`:
|
||||||
- an array with possible shipping zones for this stall. The customer MUST choose exactly one shipping zone.
|
- an array with possible shipping zones for this stall.
|
||||||
|
- the customer MUST choose exactly one of those shipping zones.
|
||||||
- shipping to different zones can have different costs. For some goods (digital for example) the cost can be zero.
|
- shipping to different zones can have different costs. For some goods (digital for example) the cost can be zero.
|
||||||
- the `id` is an internal value used by the merchant. This value must be sent back as the customer selection.
|
- the `id` is an internal value used by the merchant. This value must be sent back as the customer selection.
|
||||||
|
- each shipping zone contains the base cost for orders made to that shipping zone, but a specific shipping cost per
|
||||||
|
product can also be specified if the shipping cost for that product is higher than what's specified by the base cost.
|
||||||
|
|
||||||
|
**Event Tags**
|
||||||
|
|
||||||
**Event Tags**:
|
|
||||||
```json
|
```json
|
||||||
"tags": [["d", <String, id of stall]]
|
{
|
||||||
|
"tags": [["d", <string, id of stall]],
|
||||||
|
...
|
||||||
|
}
|
||||||
```
|
```
|
||||||
- the `d` tag is required by [NIP33](https://github.com/nostr-protocol/nips/blob/master/33.md). Its value MUST be the same as the stall `id`.
|
- the `d` tag is required, its value MUST be the same as the stall `id`.
|
||||||
|
|
||||||
### Event `30018`: Create or update a product
|
### Event `30018`: Create or update a product
|
||||||
|
|
||||||
**Event Content**:
|
**Event Content**
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"id": <String, UUID generated by the merchant.Sequential IDs (`0`, `1`, `2`...) are discouraged>,
|
"id": <string, id generated by the merchant (sequential ids are discouraged)>,
|
||||||
"stall_id": <String, UUID of the stall to which this product belong to>,
|
"stall_id": <string, id of the stall to which this product belong to>,
|
||||||
"name": <String, product name>,
|
"name": <string, product name>,
|
||||||
"description": <String (optional), product description>,
|
"description": <string (optional), product description>,
|
||||||
"images": <[String], array of image URLs, optional>,
|
"images": <[string], array of image URLs, optional>,
|
||||||
"currency": <String, currency used>,
|
"currency": <string, currency used>,
|
||||||
"price": <float, cost of product>,
|
"price": <float, cost of product>,
|
||||||
"quantity": <int, available items>,
|
"quantity": <int or null, available items>,
|
||||||
"specs": [
|
"specs": [
|
||||||
[ <String, spec key>, <String, spec value>]
|
[<string, spec key>, <string, spec value>]
|
||||||
|
],
|
||||||
|
"shipping": [
|
||||||
|
{
|
||||||
|
"id": <string, id of the shipping zone (must match one of the zones defined for the stall)>,
|
||||||
|
"cost": <float, extra cost for shipping. The currency is defined at the stall level>
|
||||||
|
}
|
||||||
]
|
]
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
Fields that are not self-explanatory:
|
Fields that are not self-explanatory:
|
||||||
|
- `quantity` can be null in the case of items with unlimited availability, like digital items, or services
|
||||||
- `specs`:
|
- `specs`:
|
||||||
- an array of key pair values. It allows for the Customer UI to present present product specifications in a structure mode. It also allows comparison between products
|
- an optional array of key pair values. It allows for the Customer UI to present product specifications in a structure mode. It also allows comparison between products
|
||||||
- eg: `[["operating_system", "Android 12.0"], ["screen_size", "6.4 inches"], ["connector_type", "USB Type C"]]`
|
- eg: `[["operating_system", "Android 12.0"], ["screen_size", "6.4 inches"], ["connector_type", "USB Type C"]]`
|
||||||
|
|
||||||
_Open_: better to move `spec` in the `tags` section of the event?
|
_Open_: better to move `spec` in the `tags` section of the event?
|
||||||
|
|
||||||
**Event Tags**:
|
- `shipping`:
|
||||||
|
- an _optional_ array of extra costs to be used per shipping zone, only for products that require special shipping costs to be added to the base shipping cost defined in the stall
|
||||||
|
- the `id` should match the id of the shipping zone, as defined in the `shipping` field of the stall
|
||||||
|
- to calculate the total cost of shipping for an order, the user will choose a shipping option during checkout, and then the client must consider this costs:
|
||||||
|
- the `base cost from the stall` for the chosen shipping option
|
||||||
|
- the result of multiplying the product units by the `shipping costs specified in the product`, if any.
|
||||||
|
|
||||||
|
**Event Tags**
|
||||||
|
|
||||||
```json
|
```json
|
||||||
"tags": [
|
"tags": [
|
||||||
["d", <String, id of product],
|
["d", <string, id of product],
|
||||||
["t", <String (optional), product category],
|
["t", <string (optional), product category],
|
||||||
["t", <String (optional), product category],
|
["t", <string (optional), product category],
|
||||||
|
...
|
||||||
|
],
|
||||||
...
|
...
|
||||||
]
|
|
||||||
```
|
```
|
||||||
|
|
||||||
- the `d` tag is required by [NIP33](https://github.com/nostr-protocol/nips/blob/master/33.md). Its value MUST be the same as the product `id`.
|
- the `d` tag is required, its value MUST be the same as the product `id`.
|
||||||
- the `t` tag is as searchable tag ([NIP12](https://github.com/nostr-protocol/nips/blob/master/12.md)). It represents different categories that the product can be part of (`food`, `fruits`). Multiple `t` tags can be present.
|
- the `t` tag is as searchable tag, it represents different categories that the product can be part of (`food`, `fruits`). Multiple `t` tags can be present.
|
||||||
|
|
||||||
## Checkout events
|
## Checkout events
|
||||||
|
|
||||||
All checkout events are sent as JSON strings using ([NIP04](https://github.com/nostr-protocol/nips/blob/master/04.md)).
|
All checkout events are sent as JSON strings using ([NIP-04](https://github.com/nostr-protocol/nips/blob/master/04.md)).
|
||||||
|
|
||||||
The `merchant` and the `customer` can exchange JSON messages that represent different actions. Each `JSON` message `MUST` have a `type` field indicating the what the JSON represents. Possible types:
|
The `merchant` and the `customer` can exchange JSON messages that represent different actions. Each `JSON` message `MUST` have a `type` field indicating the what the JSON represents. Possible types:
|
||||||
|
|
||||||
|
|
@ -124,29 +149,28 @@ The `merchant` and the `customer` can exchange JSON messages that represent diff
|
||||||
| 1 | Merchant | Payment Request |
|
| 1 | Merchant | Payment Request |
|
||||||
| 2 | Merchant | Order Status Update |
|
| 2 | Merchant | Order Status Update |
|
||||||
|
|
||||||
|
|
||||||
### Step 1: `customer` order (event)
|
### Step 1: `customer` order (event)
|
||||||
The below json goes in content of [NIP04](https://github.com/nostr-protocol/nips/blob/master/04.md).
|
The below JSON goes in content of [NIP-04](https://github.com/nostr-protocol/nips/blob/master/04.md).
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"id": <String, UUID generated by the customer>,
|
"id": <string, id generated by the customer>,
|
||||||
"type": 0,
|
"type": 0,
|
||||||
"name": <String (optional), ???>,
|
"name": <string (optional), ???>,
|
||||||
"address": <String (optional), for physical goods an address should be provided>
|
"address": <string (optional), for physical goods an address should be provided>,
|
||||||
"message": "<String (optional), message for merchant>,
|
"message": "<string (optional), message for merchant>,
|
||||||
"contact": {
|
"contact": {
|
||||||
"nostr": <32-bytes hex of a pubkey>,
|
"nostr": <32-bytes hex of a pubkey>,
|
||||||
"phone": <String (optional), if the customer wants to be contacted by phone>,
|
"phone": <string (optional), if the customer wants to be contacted by phone>,
|
||||||
"email": <String (optional), if the customer wants to be contacted by email>,
|
"email": <string (optional), if the customer wants to be contacted by email>
|
||||||
},
|
},
|
||||||
"items": [
|
"items": [
|
||||||
{
|
{
|
||||||
"product_id": <String, UUID of the product>,
|
"product_id": <string, id of the product>,
|
||||||
"quantity": <int, how many products the customer is ordering>
|
"quantity": <int, how many products the customer is ordering>
|
||||||
}
|
}
|
||||||
],
|
],
|
||||||
"shipping_id": <String, UUID of the shipping zone>
|
"shipping_id": <string, id of the shipping zone>
|
||||||
}
|
}
|
||||||
|
|
||||||
```
|
```
|
||||||
|
|
@ -158,7 +182,7 @@ _Open_: is `contact.nostr` required?
|
||||||
|
|
||||||
Sent back from the merchant for payment. Any payment option is valid that the merchant can check.
|
Sent back from the merchant for payment. Any payment option is valid that the merchant can check.
|
||||||
|
|
||||||
The below json goes in `content` of [NIP04](https://github.com/nostr-protocol/nips/blob/master/04.md).
|
The below JSON goes in `content` of [NIP-04](https://github.com/nostr-protocol/nips/blob/master/04.md).
|
||||||
|
|
||||||
`payment_options`/`type` include:
|
`payment_options`/`type` include:
|
||||||
|
|
||||||
|
|
@ -169,21 +193,21 @@ The below json goes in `content` of [NIP04](https://github.com/nostr-protocol/ni
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"id": <String, UUID of the order>,
|
"id": <string, id of the order>,
|
||||||
"type": 1,
|
"type": 1,
|
||||||
"message": <String, message to customer, optional>,
|
"message": <string, message to customer, optional>,
|
||||||
"payment_options": [
|
"payment_options": [
|
||||||
{
|
{
|
||||||
"type": <String, option type>,
|
"type": <string, option type>,
|
||||||
"link": <String, url, btc address, ln invoice, etc>
|
"link": <string, url, btc address, ln invoice, etc>
|
||||||
},
|
},
|
||||||
{
|
{
|
||||||
"type": <String, option type>,
|
"type": <string, option type>,
|
||||||
"link": <String, url, btc address, ln invoice, etc>
|
"link": <string, url, btc address, ln invoice, etc>
|
||||||
},
|
},
|
||||||
{
|
{
|
||||||
"type": <String, option type>,
|
"type": <string, option type>,
|
||||||
"link": <String, url, btc address, ln invoice, etc>
|
"link": <string, url, btc address, ln invoice, etc>
|
||||||
}
|
}
|
||||||
]
|
]
|
||||||
}
|
}
|
||||||
|
|
@ -193,22 +217,122 @@ The below json goes in `content` of [NIP04](https://github.com/nostr-protocol/ni
|
||||||
|
|
||||||
Once payment has been received and processed.
|
Once payment has been received and processed.
|
||||||
|
|
||||||
The below json goes in `content` of [NIP04](https://github.com/nostr-protocol/nips/blob/master/04.md).
|
The below JSON goes in `content` of [NIP-04](https://github.com/nostr-protocol/nips/blob/master/04.md).
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"id": <String, UUID of the order>,
|
"id": <string, id of the order>,
|
||||||
"type": 2,
|
"type": 2,
|
||||||
"message": <String, message to customer>,
|
"message": <string, message to customer>,
|
||||||
"paid": <Bool, true/false has received payment>,
|
"paid": <bool: has received payment>,
|
||||||
"shipped": <Bool, true/false has been shipped>,
|
"shipped": <bool: has been shipped>,
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
|
## Customize Marketplace
|
||||||
|
|
||||||
|
Create a customized user experience using the `naddr` from [NIP-19](https://github.com/nostr-protocol/nips/blob/master/19.md#shareable-identifiers-with-extra-metadata). The use of `naddr` enables easy sharing of marketplace events while incorporating a rich set of metadata. This metadata can include relays, merchant profiles, and more. Subsequently, it allows merchants to be grouped into a market, empowering the market creator to configure the marketplace's user interface and user experience, and share that marketplace. This customization can encompass elements such as market name, description, logo, banner, themes, and even color schemes, offering a tailored and unique marketplace experience.
|
||||||
|
|
||||||
|
### Event `30019`: Create or update marketplace UI/UX
|
||||||
|
|
||||||
|
**Event Content**
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"name": <string (optional), market name>,
|
||||||
|
"about": <string (optional), market description>,
|
||||||
|
"ui": {
|
||||||
|
"picture": <string (optional), market logo image URL>,
|
||||||
|
"banner": <string (optional), market logo banner URL>,
|
||||||
|
"theme": <string (optional), market theme>,
|
||||||
|
"darkMode": <bool, true/false>
|
||||||
|
},
|
||||||
|
"merchants": [array of pubkeys (optional)],
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
This event leverages naddr to enable comprehensive customization and sharing of marketplace configurations, fostering a unique and engaging marketplace environment.
|
||||||
|
|
||||||
|
## Auctions
|
||||||
|
|
||||||
|
### Event `30020`: Create or update a product sold as an auction
|
||||||
|
|
||||||
|
**Event Content**:
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"id": <String, UUID generated by the merchant. Sequential IDs (`0`, `1`, `2`...) are discouraged>,
|
||||||
|
"stall_id": <String, UUID of the stall to which this product belong to>,
|
||||||
|
"name": <String, product name>,
|
||||||
|
"description": <String (optional), product description>,
|
||||||
|
"images": <[String], array of image URLs, optional>,
|
||||||
|
"starting_bid": <int>,
|
||||||
|
"start_date": <int (optional) UNIX timestamp, date the auction started / will start>,
|
||||||
|
"duration": <int, number of seconds the auction will run for, excluding eventual time extensions that might happen>,
|
||||||
|
"specs": [
|
||||||
|
[<String, spec key>, <String, spec value>]
|
||||||
|
],
|
||||||
|
"shipping": [
|
||||||
|
{
|
||||||
|
"id": <String, UUID of the shipping zone. Must match one of the zones defined for the stall>,
|
||||||
|
"cost": <float, extra cost for shipping. The currency is defined at the stall level>
|
||||||
|
}
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
> [!NOTE]
|
||||||
|
> Items sold as an auction are very similar in structure to fixed-price items, with some important differences worth noting.
|
||||||
|
|
||||||
|
* The `start_date` can be set to a date in the future if the auction is scheduled to start on that date, or can be omitted if the start date is unknown/hidden. If the start date is not specified, the auction will have to be edited later to set an actual date.
|
||||||
|
|
||||||
|
* The auction runs for an initial number of seconds after the `start_date`, specified by `duration`.
|
||||||
|
|
||||||
|
### Event `1021`: Bid
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"content": <int, amount of sats>,
|
||||||
|
"tags": [["e", <event ID of the auction to bid on>]],
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Bids are simply events of kind `1021` with a `content` field specifying the amount, in the currency of the auction. Bids must reference an auction.
|
||||||
|
|
||||||
|
> [!NOTE]
|
||||||
|
> Auctions can be edited as many times as desired (they are "parameterized replaceable events") by the author - even after the start_date, but they cannot be edited after they have received the first bid! This is enforced by the fact that bids reference the event ID of the auction (rather than the product UUID), which changes with every new version of the auctioned product. So a bid is always attached to one "version". Editing the auction after a bid would result in the new product losing the bid!
|
||||||
|
|
||||||
|
### Event `1022`: Bid confirmation
|
||||||
|
|
||||||
|
**Event Content**:
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"status": <String, "accepted" | "rejected" | "pending" | "winner">,
|
||||||
|
"message": <String (optional)>,
|
||||||
|
"duration_extended": <int (optional), number of seconds>
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
**Event Tags**:
|
||||||
|
```json
|
||||||
|
"tags": [["e" <event ID of the bid being confirmed>], ["e", <event ID of the auction>]],
|
||||||
|
```
|
||||||
|
|
||||||
|
Bids should be confirmed by the merchant before being considered as valid by other clients. So clients should subscribe to *bid confirmation* events (kind `1022`) for every auction that they follow, in addition to the actual bids and should check that the pubkey of the bid confirmation matches the pubkey of the merchant (in addition to checking the signature).
|
||||||
|
|
||||||
|
The `content` field is a JSON which includes *at least* a `status`. `winner` is how the *winning bid* is replied to after the auction ends and the winning bid is picked by the merchant.
|
||||||
|
|
||||||
|
The reasons for which a bid can be marked as `rejected` or `pending` are up to the merchant's implementation and configuration - they could be anything from basic validation errors (amount too low) to the bidder being blacklisted or to the bidder lacking sufficient *trust*, which could lead to the bid being marked as `pending` until sufficient verification is performed. The difference between the two is that `pending` bids *might* get approved after additional steps are taken by the bidder, whereas `rejected` bids can not be later approved.
|
||||||
|
|
||||||
|
An additional `message` field can appear in the `content` JSON to give further context as of why a bid is `rejected` or `pending`.
|
||||||
|
|
||||||
|
Another thing that can happen is - if bids happen very close to the end date of the auction - for the merchant to decide to extend the auction duration for a few more minutes. This is done by passing a `duration_extended` field as part of a bid confirmation, which would contain a number of seconds by which the initial duration is extended. So the actual end date of an auction is always `start_date + duration + (SUM(c.duration_extended) FOR c in all confirmations`.
|
||||||
|
|
||||||
## Customer support events
|
## Customer support events
|
||||||
|
|
||||||
Customer support is handled over whatever communication method was specified. If communicating via nostr, NIP-04 is used https://github.com/nostr-protocol/nips/blob/master/04.md.
|
Customer support is handled over whatever communication method was specified. If communicating via nostr, NIP-04 is used https://github.com/nostr-protocol/nips/blob/master/04.md.
|
||||||
|
|
||||||
## Additional
|
## Additional
|
||||||
|
|
||||||
Standard data models can be found here <a href="https://raw.githubusercontent.com/lnbits/nostrmarket/main/models.py">here</a>
|
Standard data models can be found <a href="https://raw.githubusercontent.com/lnbits/nostrmarket/main/models.py">here</a>
|
||||||
|
|
|
||||||
35
16.md
35
16.md
|
|
@ -4,37 +4,6 @@ NIP-16
|
||||||
Event Treatment
|
Event Treatment
|
||||||
---------------
|
---------------
|
||||||
|
|
||||||
`draft` `optional` `author:Semisol`
|
`final` `mandatory`
|
||||||
|
|
||||||
Relays may decide to allow replaceable and/or ephemeral events.
|
Moved to [NIP-01](01.md).
|
||||||
|
|
||||||
Regular Events
|
|
||||||
------------------
|
|
||||||
A *regular event* is defined as an event with a kind `1000 <= n < 10000`.
|
|
||||||
Upon a regular event being received, the relay SHOULD send it to all clients with a matching filter, and SHOULD store it. New events of the same kind do not affect previous events in any way.
|
|
||||||
|
|
||||||
Replaceable Events
|
|
||||||
------------------
|
|
||||||
A *replaceable event* is defined as an event with a kind `10000 <= n < 20000`.
|
|
||||||
Upon a replaceable event with a newer timestamp than the currently known latest replaceable event with the same kind and author being received, the old event SHOULD be discarded,
|
|
||||||
effectively replacing what gets returned when querying for
|
|
||||||
`author:kind` tuples.
|
|
||||||
|
|
||||||
If two events have the same timestamp, the event with the lowest id (first in lexical order) SHOULD be retained, and the other discarded.
|
|
||||||
|
|
||||||
Ephemeral Events
|
|
||||||
----------------
|
|
||||||
An *ephemeral event* is defined as an event with a kind `20000 <= n < 30000`.
|
|
||||||
Upon an ephemeral event being received, the relay SHOULD send it to all clients with a matching filter, and MUST NOT store it.
|
|
||||||
|
|
||||||
Client Behavior
|
|
||||||
---------------
|
|
||||||
|
|
||||||
Clients SHOULD use the `supported_nips` field to learn if a relay supports this NIP. Clients SHOULD NOT send ephemeral events to relays that do not support this NIP; they will most likely be persisted. Clients MAY send replaceable events to relays that may not support this NIP, and clients querying SHOULD be prepared for the relay to send multiple events and should use the latest one.
|
|
||||||
|
|
||||||
Suggested Use Cases
|
|
||||||
-------------------
|
|
||||||
|
|
||||||
* States: An application may create a state event that is replaced every time a new state is set (such as statuses)
|
|
||||||
* Typing indicators: A chat application may use ephemeral events as a typing indicator.
|
|
||||||
* Messaging: Two pubkeys can message over nostr using ephemeral events.
|
|
||||||
|
|
|
||||||
164
17.md
Normal file
164
17.md
Normal file
|
|
@ -0,0 +1,164 @@
|
||||||
|
NIP-17
|
||||||
|
======
|
||||||
|
|
||||||
|
Private Direct Messages
|
||||||
|
-----------------------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
This NIP defines an encrypted direct messaging scheme using [NIP-44](44.md) encryption and [NIP-59](59.md) seals and gift wraps.
|
||||||
|
|
||||||
|
## Direct Message Kind
|
||||||
|
|
||||||
|
Kind `14` is a chat message. `p` tags identify one or more receivers of the message.
|
||||||
|
|
||||||
|
```js
|
||||||
|
{
|
||||||
|
"id": "<usual hash>",
|
||||||
|
"pubkey": "<sender-pubkey>",
|
||||||
|
"created_at": now(),
|
||||||
|
"kind": 14,
|
||||||
|
"tags": [
|
||||||
|
["p", "<receiver-1-pubkey>", "<relay-url>"],
|
||||||
|
["p", "<receiver-2-pubkey>", "<relay-url>"],
|
||||||
|
["e", "<kind-14-id>", "<relay-url>", "reply"] // if this is a reply
|
||||||
|
["subject", "<conversation-title>"],
|
||||||
|
...
|
||||||
|
],
|
||||||
|
"content": "<message-in-plain-text>",
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
`.content` MUST be plain text. Fields `id` and `created_at` are required.
|
||||||
|
|
||||||
|
Tags that mention, quote and assemble threading structures MUST follow [NIP-10](10.md).
|
||||||
|
|
||||||
|
Kind `14`s MUST never be signed. If it is signed, the message might leak to relays and become **fully public**.
|
||||||
|
|
||||||
|
## Chat Rooms
|
||||||
|
|
||||||
|
The set of `pubkey` + `p` tags defines a chat room. If a new `p` tag is added or a current one is removed, a new room is created with clean message history.
|
||||||
|
|
||||||
|
Clients SHOULD render messages of the same room in a continuous thread.
|
||||||
|
|
||||||
|
An optional `subject` tag defines the current name/topic of the conversation. Any member can change the topic by simply submitting a new `subject` to an existing `pubkey` + `p`-tags room. There is no need to send `subject` in every message. The newest `subject` in the thread is the subject of the conversation.
|
||||||
|
|
||||||
|
## Encrypting
|
||||||
|
|
||||||
|
Following [NIP-59](59.md), the **unsigned** `kind:14` chat message must be sealed (`kind:13`) and then gift-wrapped (`kind:1059`) to each receiver and the sender individually.
|
||||||
|
|
||||||
|
```js
|
||||||
|
{
|
||||||
|
"id": "<usual hash>",
|
||||||
|
"pubkey": randomPublicKey,
|
||||||
|
"created_at": randomTimeUpTo2DaysInThePast(),
|
||||||
|
"kind": 1059, // gift wrap
|
||||||
|
"tags": [
|
||||||
|
["p", receiverPublicKey, "<relay-url>"] // receiver
|
||||||
|
],
|
||||||
|
"content": nip44Encrypt(
|
||||||
|
{
|
||||||
|
"id": "<usual hash>",
|
||||||
|
"pubkey": senderPublicKey,
|
||||||
|
"created_at": randomTimeUpTo2DaysInThePast(),
|
||||||
|
"kind": 13, // seal
|
||||||
|
"tags": [], // no tags
|
||||||
|
"content": nip44Encrypt(unsignedKind14, senderPrivateKey, receiverPublicKey),
|
||||||
|
"sig": "<signed by senderPrivateKey>"
|
||||||
|
},
|
||||||
|
randomPrivateKey, receiverPublicKey
|
||||||
|
),
|
||||||
|
"sig": "<signed by randomPrivateKey>"
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
The encryption algorithm MUST use the latest version of [NIP-44](44.md).
|
||||||
|
|
||||||
|
Clients MUST verify if pubkey of the `kind:13` is the same pubkey on the `kind:14`, otherwise any sender can impersonate others by simply changing the pubkey on `kind:14`.
|
||||||
|
|
||||||
|
Clients SHOULD randomize `created_at` in up to two days in the past in both the seal and the gift wrap to make sure grouping by `created_at` doesn't reveal any metadata.
|
||||||
|
|
||||||
|
The gift wrap's `p`-tag can be the receiver's main pubkey or an alias key created to receive DMs without exposing the receiver's identity.
|
||||||
|
|
||||||
|
Clients CAN offer disappearing messages by setting an `expiration` tag in the gift wrap of each receiver or by not generating a gift wrap to the sender's public key
|
||||||
|
|
||||||
|
## Publishing
|
||||||
|
|
||||||
|
Kind `10050` indicates the user's preferred relays to receive DMs. The event MUST include a list of `relay` tags with relay URIs.
|
||||||
|
|
||||||
|
```js
|
||||||
|
{
|
||||||
|
"kind": 10050,
|
||||||
|
"tags": [
|
||||||
|
["relay", "wss://inbox.nostr.wine"],
|
||||||
|
["relay", "wss://myrelay.nostr1.com"],
|
||||||
|
],
|
||||||
|
"content": "",
|
||||||
|
//...other fields
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Clients SHOULD publish kind `14` events to the `10050`-listed relays. If that is not found that indicates the user is not ready to receive messages under this NIP and clients shouldn't try.
|
||||||
|
|
||||||
|
## Relays
|
||||||
|
|
||||||
|
It's advisable that relays do not serve `kind:14` to clients other than the ones tagged in them.
|
||||||
|
|
||||||
|
It's advisable that users choose relays that conform to these practices.
|
||||||
|
|
||||||
|
Clients SHOULD guide users to keep `kind:10050` lists small (1-3 relays) and SHOULD spread it to as many relays as viable.
|
||||||
|
|
||||||
|
## Benefits & Limitations
|
||||||
|
|
||||||
|
This NIP offers the following privacy and security features:
|
||||||
|
|
||||||
|
1. **No Metadata Leak**: Participant identities, each message's real date and time, event kinds, and other event tags are all hidden from the public. Senders and receivers cannot be linked with public information alone.
|
||||||
|
2. **No Public Group Identifiers**: There is no public central queue, channel or otherwise converging identifier to correlate or count all messages in the same group.
|
||||||
|
3. **No Moderation**: There are no group admins: no invitations or bans.
|
||||||
|
4. **No Shared Secrets**: No secret must be known to all members that can leak or be mistakenly shared
|
||||||
|
5. **Fully Recoverable**: Messages can be fully recoverable by any client with the user's private key
|
||||||
|
6. **Optional Forward Secrecy**: Users and clients can opt-in for "disappearing messages".
|
||||||
|
7. **Uses Public Relays**: Messages can flow through public relays without loss of privacy. Private relays can increase privacy further, but they are not required.
|
||||||
|
8. **Cold Storage**: Users can unilaterally opt-in to sharing their messages with a separate key that is exclusive for DM backup and recovery.
|
||||||
|
|
||||||
|
The main limitation of this approach is having to send a separate encrypted event to each receiver. Group chats with more than 100 participants should find a more suitable messaging scheme.
|
||||||
|
|
||||||
|
## Implementation
|
||||||
|
|
||||||
|
Clients implementing this NIP should by default only connect to the set of relays found in their `kind:10050` list. From that they should be able to load all messages both sent and received as well as get new live updates, making it for a very simple and lightweight implementation that should be fast.
|
||||||
|
|
||||||
|
When sending a message to anyone, clients must then connect to the relays in the receiver's `kind:10050` and send the events there, but can disconnect right after unless more messages are expected to be sent (e.g. the chat tab is still selected). Clients should also send a copy of their outgoing messages to their own `kind:10050` relay set.
|
||||||
|
|
||||||
|
## Examples
|
||||||
|
|
||||||
|
This example sends the message `Hola, que tal?` from `nsec1w8udu59ydjvedgs3yv5qccshcj8k05fh3l60k9x57asjrqdpa00qkmr89m` to `nsec12ywtkplvyq5t6twdqwwygavp5lm4fhuang89c943nf2z92eez43szvn4dt`.
|
||||||
|
|
||||||
|
The two final GiftWraps, one to the receiver and the other to the sender, are:
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"id":"2886780f7349afc1344047524540ee716f7bdc1b64191699855662330bf235d8",
|
||||||
|
"pubkey":"8f8a7ec43b77d25799281207e1a47f7a654755055788f7482653f9c9661c6d51",
|
||||||
|
"created_at":1703128320,
|
||||||
|
"kind":1059,
|
||||||
|
"tags":[
|
||||||
|
[ "p", "918e2da906df4ccd12c8ac672d8335add131a4cf9d27ce42b3bb3625755f0788"]
|
||||||
|
],
|
||||||
|
"content":"AsqzdlMsG304G8h08bE67dhAR1gFTzTckUUyuvndZ8LrGCvwI4pgC3d6hyAK0Wo9gtkLqSr2rT2RyHlE5wRqbCOlQ8WvJEKwqwIJwT5PO3l2RxvGCHDbd1b1o40ZgIVwwLCfOWJ86I5upXe8K5AgpxYTOM1BD+SbgI5jOMA8tgpRoitJedVSvBZsmwAxXM7o7sbOON4MXHzOqOZpALpS2zgBDXSAaYAsTdEM4qqFeik+zTk3+L6NYuftGidqVluicwSGS2viYWr5OiJ1zrj1ERhYSGLpQnPKrqDaDi7R1KrHGFGyLgkJveY/45y0rv9aVIw9IWF11u53cf2CP7akACel2WvZdl1htEwFu/v9cFXD06fNVZjfx3OssKM/uHPE9XvZttQboAvP5UoK6lv9o3d+0GM4/3zP+yO3C0NExz1ZgFmbGFz703YJzM+zpKCOXaZyzPjADXp8qBBeVc5lmJqiCL4solZpxA1865yPigPAZcc9acSUlg23J1dptFK4n3Tl5HfSHP+oZ/QS/SHWbVFCtq7ZMQSRxLgEitfglTNz9P1CnpMwmW/Y4Gm5zdkv0JrdUVrn2UO9ARdHlPsW5ARgDmzaxnJypkfoHXNfxGGXWRk0sKLbz/ipnaQP/eFJv/ibNuSfqL6E4BnN/tHJSHYEaTQ/PdrA2i9laG3vJti3kAl5Ih87ct0w/tzYfp4SRPhEF1zzue9G/16eJEMzwmhQ5Ec7jJVcVGa4RltqnuF8unUu3iSRTQ+/MNNUkK6Mk+YuaJJs6Fjw6tRHuWi57SdKKv7GGkr0zlBUU2Dyo1MwpAqzsCcCTeQSv+8qt4wLf4uhU9Br7F/L0ZY9bFgh6iLDCdB+4iABXyZwT7Ufn762195hrSHcU4Okt0Zns9EeiBOFxnmpXEslYkYBpXw70GmymQfJlFOfoEp93QKCMS2DAEVeI51dJV1e+6t3pCSsQN69Vg6jUCsm1TMxSs2VX4BRbq562+VffchvW2BB4gMjsvHVUSRl8i5/ZSDlfzSPXcSGALLHBRzy+gn0oXXJ/447VHYZJDL3Ig8+QW5oFMgnWYhuwI5QSLEyflUrfSz+Pdwn/5eyjybXKJftePBD9Q+8NQ8zulU5sqvsMeIx/bBUx0fmOXsS3vjqCXW5IjkmSUV7q54GewZqTQBlcx+90xh/LSUxXex7UwZwRnifvyCbZ+zwNTHNb12chYeNjMV7kAIr3cGQv8vlOMM8ajyaZ5KVy7HpSXQjz4PGT2/nXbL5jKt8Lx0erGXsSsazkdoYDG3U",
|
||||||
|
"sig":"a3c6ce632b145c0869423c1afaff4a6d764a9b64dedaf15f170b944ead67227518a72e455567ca1c2a0d187832cecbde7ed478395ec4c95dd3e71749ed66c480"
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"id":"162b0611a1911cfcb30f8a5502792b346e535a45658b3a31ae5c178465509721",
|
||||||
|
"pubkey":"626be2af274b29ea4816ad672ee452b7cf96bbb4836815a55699ae402183f512",
|
||||||
|
"created_at":1702711587,
|
||||||
|
"kind":1059,
|
||||||
|
"tags":[
|
||||||
|
[ "p", "44900586091b284416a0c001f677f9c49f7639a55c3f1e2ec130a8e1a7998e1b"]
|
||||||
|
],
|
||||||
|
"content":"AsTClTzr0gzXXji7uye5UB6LYrx3HDjWGdkNaBS6BAX9CpHa+Vvtt5oI2xJrmWLen+Fo2NBOFazvl285Gb3HSM82gVycrzx1HUAaQDUG6HI7XBEGqBhQMUNwNMiN2dnilBMFC3Yc8ehCJT/gkbiNKOpwd2rFibMFRMDKai2mq2lBtPJF18oszKOjA+XlOJV8JRbmcAanTbEK5nA/GnG3eGUiUzhiYBoHomj3vztYYxc0QYHOx0WxiHY8dsC6jPsXC7f6k4P+Hv5ZiyTfzvjkSJOckel1lZuE5SfeZ0nduqTlxREGeBJ8amOykgEIKdH2VZBZB+qtOMc7ez9dz4wffGwBDA7912NFS2dPBr6txHNxBUkDZKFbuD5wijvonZDvfWq43tZspO4NutSokZB99uEiRH8NAUdGTiNb25m9JcDhVfdmABqTg5fIwwTwlem5aXIy8b66lmqqz2LBzJtnJDu36bDwkILph3kmvaKPD8qJXmPQ4yGpxIbYSTCohgt2/I0TKJNmqNvSN+IVoUuC7ZOfUV9lOV8Ri0AMfSr2YsdZ9ofV5o82ClZWlWiSWZwy6ypa7CuT1PEGHzywB4CZ5ucpO60Z7hnBQxHLiAQIO/QhiBp1rmrdQZFN6PUEjFDloykoeHe345Yqy9Ke95HIKUCS9yJurD+nZjjgOxZjoFCsB1hQAwINTIS3FbYOibZnQwv8PXvcSOqVZxC9U0+WuagK7IwxzhGZY3vLRrX01oujiRrevB4xbW7Oxi/Agp7CQGlJXCgmRE8Rhm+Vj2s+wc/4VLNZRHDcwtfejogjrjdi8p6nfUyqoQRRPARzRGUnnCbh+LqhigT6gQf3sVilnydMRScEc0/YYNLWnaw9nbyBa7wFBAiGbJwO40k39wj+xT6HTSbSUgFZzopxroO3f/o4+ubx2+IL3fkev22mEN38+dFmYF3zE+hpE7jVxrJpC3EP9PLoFgFPKCuctMnjXmeHoiGs756N5r1Mm1ffZu4H19MSuALJlxQR7VXE/LzxRXDuaB2u9days/6muP6gbGX1ASxbJd/ou8+viHmSC/ioHzNjItVCPaJjDyc6bv+gs1NPCt0qZ69G+JmgHW/PsMMeL4n5bh74g0fJSHqiI9ewEmOG/8bedSREv2XXtKV39STxPweceIOh0k23s3N6+wvuSUAJE7u1LkDo14cobtZ/MCw/QhimYPd1u5HnEJvRhPxz0nVPz0QqL/YQeOkAYk7uzgeb2yPzJ6DBtnTnGDkglekhVzQBFRJdk740LEj6swkJ",
|
||||||
|
"sig":"c94e74533b482aa8eeeb54ae72a5303e0b21f62909ca43c8ef06b0357412d6f8a92f96e1a205102753777fd25321a58fba3fb384eee114bd53ce6c06a1c22bab"
|
||||||
|
}
|
||||||
|
```
|
||||||
9
18.md
9
18.md
|
|
@ -4,7 +4,7 @@ NIP-18
|
||||||
Reposts
|
Reposts
|
||||||
-------
|
-------
|
||||||
|
|
||||||
`draft` `optional` `author:jb55` `author:fiatjaf` `author:arthurfranca`
|
`draft` `optional`
|
||||||
|
|
||||||
A repost is a `kind 6` event that is used to signal to followers
|
A repost is a `kind 6` event that is used to signal to followers
|
||||||
that a `kind 1` text note is worth reading.
|
that a `kind 1` text note is worth reading.
|
||||||
|
|
@ -20,9 +20,10 @@ reposted.
|
||||||
|
|
||||||
## Quote Reposts
|
## Quote Reposts
|
||||||
|
|
||||||
Quote reposts are `kind 1` events with an embedded `e` tag
|
Quote reposts are `kind 1` events with an embedded `q` tag of the note being
|
||||||
(see [NIP-08](08.md) and [NIP-27](27.md)). Because a quote repost includes
|
quote reposted. The `q` tag ensures quote reposts are not pulled and included
|
||||||
an `e` tag, it may show up along replies to the reposted note.
|
as replies in threads. It also allows you to easily pull and count all of the
|
||||||
|
quotes for a post.
|
||||||
|
|
||||||
## Generic Reposts
|
## Generic Reposts
|
||||||
|
|
||||||
|
|
|
||||||
6
19.md
6
19.md
|
|
@ -4,7 +4,7 @@ NIP-19
|
||||||
bech32-encoded entities
|
bech32-encoded entities
|
||||||
-----------------------
|
-----------------------
|
||||||
|
|
||||||
`draft` `optional` `author:jb55` `author:fiatjaf` `author:Semisol`
|
`draft` `optional`
|
||||||
|
|
||||||
This NIP standardizes bech32-formatted strings that can be used to display keys, ids and other information in clients. These formats are not meant to be used anywhere in the core protocol, they are only meant for displaying to users, copy-pasting, sharing, rendering QR codes and inputting data.
|
This NIP standardizes bech32-formatted strings that can be used to display keys, ids and other information in clients. These formats are not meant to be used anywhere in the core protocol, they are only meant for displaying to users, copy-pasting, sharing, rendering QR codes and inputting data.
|
||||||
|
|
||||||
|
|
@ -35,7 +35,7 @@ These are the possible bech32 prefixes with `TLV`:
|
||||||
- `nprofile`: a nostr profile
|
- `nprofile`: a nostr profile
|
||||||
- `nevent`: a nostr event
|
- `nevent`: a nostr event
|
||||||
- `nrelay`: a nostr relay
|
- `nrelay`: a nostr relay
|
||||||
- `naddr`: a nostr parameterized replaceable event coordinate (NIP-33)
|
- `naddr`: a nostr _replaceable event_ coordinate
|
||||||
|
|
||||||
These possible standardized `TLV` types are indicated here:
|
These possible standardized `TLV` types are indicated here:
|
||||||
|
|
||||||
|
|
@ -44,7 +44,7 @@ These possible standardized `TLV` types are indicated here:
|
||||||
- for `nprofile` it will be the 32 bytes of the profile public key
|
- for `nprofile` it will be the 32 bytes of the profile public key
|
||||||
- for `nevent` it will be the 32 bytes of the event id
|
- for `nevent` it will be the 32 bytes of the event id
|
||||||
- for `nrelay`, this is the relay URL
|
- for `nrelay`, this is the relay URL
|
||||||
- for `naddr`, it is the identifier (the `"d"` tag) of the event being referenced
|
- for `naddr`, it is the identifier (the `"d"` tag) of the event being referenced. For non-parameterized replaceable events, use an empty string.
|
||||||
- `1`: `relay`
|
- `1`: `relay`
|
||||||
- for `nprofile`, `nevent` and `naddr`, _optionally_, a relay in which the entity (profile or event) is more likely to be found, encoded as ascii
|
- for `nprofile`, `nevent` and `naddr`, _optionally_, a relay in which the entity (profile or event) is more likely to be found, encoded as ascii
|
||||||
- this may be included multiple times
|
- this may be included multiple times
|
||||||
|
|
|
||||||
88
20.md
88
20.md
|
|
@ -1,93 +1,9 @@
|
||||||
NIP-20
|
NIP-20
|
||||||
======
|
======
|
||||||
|
|
||||||
|
|
||||||
Command Results
|
Command Results
|
||||||
---------------
|
---------------
|
||||||
|
|
||||||
`draft` `optional` `author:jb55`
|
`final` `mandatory`
|
||||||
|
|
||||||
When submitting events to relays, clients currently have no way to know if an event was successfully committed to the database. This NIP introduces the concept of command results which are like NOTICE's except provide more information about if an event was accepted or rejected.
|
Moved to [NIP-01](01.md).
|
||||||
|
|
||||||
A command result is a JSON object with the following structure that is returned when an event is successfully saved to the database or rejected:
|
|
||||||
|
|
||||||
["OK", <event_id>, <true|false>, <message>]
|
|
||||||
|
|
||||||
Relays MUST return `true` when the event is a duplicate and has already been saved. The `message` SHOULD start with `duplicate:` in this case.
|
|
||||||
|
|
||||||
Relays MUST return `false` when the event was rejected and not saved.
|
|
||||||
|
|
||||||
The `message` SHOULD provide additional information as to why the command succeeded or failed.
|
|
||||||
|
|
||||||
The `message` SHOULD start with `blocked:` if the pubkey or network address has been blocked, banned, or is not on a whitelist.
|
|
||||||
|
|
||||||
The `message` SHOULD start with `invalid:` if the event is invalid or doesn't meet some specific criteria (created_at is too far off, id is wrong, signature is wrong, etc)
|
|
||||||
|
|
||||||
The `message` SHOULD start with `pow:` if the event doesn't meet some proof-of-work difficulty. The client MAY consult the relay metadata at this point to retrieve the required posting difficulty.
|
|
||||||
|
|
||||||
The `message` SHOULD start with `rate-limited:` if the event was rejected due to rate limiting techniques.
|
|
||||||
|
|
||||||
The `message` SHOULD start with `error:` if the event failed to save due to a server issue.
|
|
||||||
|
|
||||||
Ephemeral events are not acknowledged with OK responses, unless there is a failure.
|
|
||||||
|
|
||||||
If the event or `EVENT` command is malformed and could not be parsed, a NOTICE message SHOULD be used instead of a command result. This NIP only applies to non-malformed EVENT commands.
|
|
||||||
|
|
||||||
|
|
||||||
Examples
|
|
||||||
--------
|
|
||||||
|
|
||||||
Event successfully written to the database:
|
|
||||||
|
|
||||||
["OK", "b1a649ebe8b435ec71d3784793f3bbf4b93e64e17568a741aecd4c7ddeafce30", true, ""]
|
|
||||||
|
|
||||||
Event successfully written to the database because of a reason:
|
|
||||||
|
|
||||||
["OK", "b1a649ebe8b435ec71d3784793f3bbf4b93e64e17568a741aecd4c7ddeafce30", true, "pow: difficulty 25>=24"]
|
|
||||||
|
|
||||||
Event blocked due to ip filter
|
|
||||||
|
|
||||||
["OK", "b1a649ebe8...", false, "blocked: tor exit nodes not allowed"]
|
|
||||||
|
|
||||||
Event blocked due to pubkey ban
|
|
||||||
|
|
||||||
["OK", "b1a649ebe8...", false, "blocked: you are banned from posting here"]
|
|
||||||
|
|
||||||
Event blocked, pubkey not registered
|
|
||||||
|
|
||||||
["OK", "b1a649ebe8...", false, "blocked: please register your pubkey at https://my-expensive-relay.example.com"]
|
|
||||||
|
|
||||||
Event rejected, rate limited
|
|
||||||
|
|
||||||
["OK", "b1a649ebe8...", false, "rate-limited: slow down there chief"]
|
|
||||||
|
|
||||||
Event rejected, `created_at` too far off
|
|
||||||
|
|
||||||
["OK", "b1a649ebe8...", false, "invalid: event creation date is too far off from the current time. Is your system clock in sync?"]
|
|
||||||
|
|
||||||
Event rejected, insufficient proof-of-work difficulty
|
|
||||||
|
|
||||||
["OK", "b1a649ebe8...", false, "pow: difficulty 26 is less than 30"]
|
|
||||||
|
|
||||||
Event failed to save,
|
|
||||||
|
|
||||||
["OK", "b1a649ebe8...", false, "error: could not connect to the database"]
|
|
||||||
|
|
||||||
|
|
||||||
|
|
||||||
Client Handling
|
|
||||||
---------------
|
|
||||||
|
|
||||||
`messages` are meant for humans, with `reason:` prefixes so that clients can be slightly more intelligent with what to do with them. For example, with a `rate-limited:` reason the client may not show anything and simply try again with a longer timeout.
|
|
||||||
|
|
||||||
For the `pow:` prefix it may query relay metadata to get the updated difficulty requirement and try again in the background.
|
|
||||||
|
|
||||||
For the `invalid:` and `blocked:` prefix the client may wish to show these as styled error popups.
|
|
||||||
|
|
||||||
The prefixes include a colon so that the message can be cleanly separated from the prefix by taking everything after `:` and trimming it.
|
|
||||||
|
|
||||||
|
|
||||||
Future Extensions
|
|
||||||
-----------------
|
|
||||||
|
|
||||||
This proposal SHOULD be extended to support further commands in the future, such as REQ and AUTH. They are left out of this initial version to keep things simpler.
|
|
||||||
|
|
|
||||||
2
21.md
2
21.md
|
|
@ -4,7 +4,7 @@ NIP-21
|
||||||
`nostr:` URI scheme
|
`nostr:` URI scheme
|
||||||
-------------------
|
-------------------
|
||||||
|
|
||||||
`draft` `optional` `author:fiatjaf`
|
`draft` `optional`
|
||||||
|
|
||||||
This NIP standardizes the usage of a common URI scheme for maximum interoperability and openness in the network.
|
This NIP standardizes the usage of a common URI scheme for maximum interoperability and openness in the network.
|
||||||
|
|
||||||
|
|
|
||||||
45
22.md
45
22.md
|
|
@ -1,45 +0,0 @@
|
||||||
NIP-22
|
|
||||||
======
|
|
||||||
|
|
||||||
Event `created_at` Limits
|
|
||||||
---------------------------
|
|
||||||
|
|
||||||
`draft` `optional` `author:jeffthibault` `author:Giszmo`
|
|
||||||
|
|
||||||
Relays may define both upper and lower limits within which they will consider an event's `created_at` to be acceptable. Both the upper and lower limits MUST be unix timestamps in seconds as defined in [NIP-01](01.md).
|
|
||||||
|
|
||||||
If a relay supports this NIP, the relay SHOULD send the client a [NIP-20](20.md) command result saying the event was not stored for the `created_at` timestamp not being within the permitted limits.
|
|
||||||
|
|
||||||
Client Behavior
|
|
||||||
---------------
|
|
||||||
|
|
||||||
Clients SHOULD use the [NIP-11](11.md) `supported_nips` field to learn if a relay uses event `created_at` time limits as defined by this NIP.
|
|
||||||
|
|
||||||
Motivation
|
|
||||||
----------
|
|
||||||
|
|
||||||
This NIP formalizes restrictions on event timestamps as accepted by a relay and allows clients to be aware of relays that have these restrictions.
|
|
||||||
|
|
||||||
The event `created_at` field is just a unix timestamp and can be set to a time in the past or future. Relays accept and share events dated to 20 years ago or 50,000 years in the future. This NIP aims to define a way for relays that do not want to store events with *any* timestamp to set their own restrictions.
|
|
||||||
|
|
||||||
[Replaceable events](16.md#replaceable-events) can behave rather unexpectedly if the user wrote them - or tried to write them - with a wrong system clock. Persisting an update with a backdated system now would result in the update not getting persisted without a notification and if they did the last update with a forward dated system, they will again fail to do another update with the now correct time.
|
|
||||||
|
|
||||||
A wide adoption of this NIP could create a better user experience as it would decrease the amount of events that appear wildly out of order or even from impossible dates in the distant past or future.
|
|
||||||
|
|
||||||
Keep in mind that there is a use case where a user migrates their old posts onto a new relay. If a relay rejects events that were not recently created, it cannot serve this use case.
|
|
||||||
|
|
||||||
|
|
||||||
Python (pseudocode) Example
|
|
||||||
---------------------------
|
|
||||||
|
|
||||||
```python
|
|
||||||
import time
|
|
||||||
|
|
||||||
TIME = int(time.time())
|
|
||||||
LOWER_LIMIT = TIME - (60 * 60 * 24) # Define lower limit as 1 day into the past
|
|
||||||
UPPER_LIMIT = TIME + (60 * 15) # Define upper limit as 15 minutes into the future
|
|
||||||
|
|
||||||
if event.created_at not in range(LOWER_LIMIT, UPPER_LIMIT):
|
|
||||||
ws.send('["OK", event.id, False, "invalid: the event created_at field is out of the acceptable range (-24h, +15min) for this relay"]')
|
|
||||||
```
|
|
||||||
Note: These are just example limits, the relay operator can choose whatever limits they want.
|
|
||||||
16
23.md
16
23.md
|
|
@ -4,19 +4,23 @@ NIP-23
|
||||||
Long-form Content
|
Long-form Content
|
||||||
-----------------
|
-----------------
|
||||||
|
|
||||||
`draft` `optional` `author:fiatjaf`
|
`draft` `optional`
|
||||||
|
|
||||||
This NIP defines `kind:30023` (a parameterized replaceable event according to [NIP-33](33.md)) for long-form text content, generally referred to as "articles" or "blog posts". `kind:30024` has the same structure as `kind:30023` and is used to save long form drafts.
|
This NIP defines `kind:30023` (a _parameterized replaceable event_) for long-form text content, generally referred to as "articles" or "blog posts". `kind:30024` has the same structure as `kind:30023` and is used to save long form drafts.
|
||||||
|
|
||||||
"Social" clients that deal primarily with `kind:1` notes should not be expected to implement this NIP.
|
"Social" clients that deal primarily with `kind:1` notes should not be expected to implement this NIP.
|
||||||
|
|
||||||
### Format
|
### Format
|
||||||
|
|
||||||
The `.content` of these events should be a string text in Markdown syntax.
|
The `.content` of these events should be a string text in Markdown syntax. To maximize compatibility and readability between different clients and devices, any client that is creating long form notes:
|
||||||
|
|
||||||
|
- MUST NOT hard line-break paragraphs of text, such as arbitrary line breaks at 80 column boundaries.
|
||||||
|
|
||||||
|
- MUST NOT support adding HTML to Markdown.
|
||||||
|
|
||||||
### Metadata
|
### Metadata
|
||||||
|
|
||||||
For the date of the last update the `.created_at` field should be used, for "tags"/"hashtags" (i.e. topics about which the event might be of relevance) the `"t"` event tag should be used, as per NIP-12.
|
For the date of the last update the `.created_at` field should be used, for "tags"/"hashtags" (i.e. topics about which the event might be of relevance) the `t` tag should be used, as per NIP-12.
|
||||||
|
|
||||||
Other metadata fields can be added as tags to the event as necessary. Here we standardize 4 that may be useful, although they remain strictly optional:
|
Other metadata fields can be added as tags to the event as necessary. Here we standardize 4 that may be useful, although they remain strictly optional:
|
||||||
|
|
||||||
|
|
@ -27,11 +31,11 @@ Other metadata fields can be added as tags to the event as necessary. Here we st
|
||||||
|
|
||||||
### Editability
|
### Editability
|
||||||
|
|
||||||
These articles are meant to be editable, so they should make use of the replaceability feature of NIP-33 and include a `"d"` tag with an identifier for the article. Clients should take care to only publish and read these events from relays that implement that. If they don't do that they should also take care to hide old versions of the same article they may receive.
|
These articles are meant to be editable, so they should make use of the parameterized replaceability feature and include a `d` tag with an identifier for the article. Clients should take care to only publish and read these events from relays that implement that. If they don't do that they should also take care to hide old versions of the same article they may receive.
|
||||||
|
|
||||||
### Linking
|
### Linking
|
||||||
|
|
||||||
The article may be linked to using the NIP-19 `naddr` code along with the `"a"` tag (see [NIP-33](33.md) and [NIP-19](19.md)).
|
The article may be linked to using the [NIP-19](19.md) `naddr` code along with the `a` tag.
|
||||||
|
|
||||||
### References
|
### References
|
||||||
|
|
||||||
|
|
|
||||||
43
24.md
Normal file
43
24.md
Normal file
|
|
@ -0,0 +1,43 @@
|
||||||
|
NIP-24
|
||||||
|
======
|
||||||
|
|
||||||
|
Extra metadata fields and tags
|
||||||
|
------------------------------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
This NIP defines extra optional fields added to events.
|
||||||
|
|
||||||
|
kind 0
|
||||||
|
======
|
||||||
|
|
||||||
|
These are extra fields not specified in NIP-01 that may be present in the stringified JSON of metadata events:
|
||||||
|
|
||||||
|
- `display_name`: an alternative, bigger name with richer characters than `name`. `name` should always be set regardless of the presence of `display_name` in the metadata.
|
||||||
|
- `website`: a web URL related in any way to the event author.
|
||||||
|
- `banner`: an URL to a wide (~1024x768) picture to be optionally displayed in the background of a profile screen.
|
||||||
|
- `bot`: a boolean to clarify that the content is entirely or partially the result of automation, such as with chatbots or newsfeeds.
|
||||||
|
|
||||||
|
### Deprecated fields
|
||||||
|
|
||||||
|
These are fields that should be ignored or removed when found in the wild:
|
||||||
|
|
||||||
|
- `displayName`: use `display_name` instead.
|
||||||
|
- `username`: use `name` instead.
|
||||||
|
|
||||||
|
kind 3
|
||||||
|
======
|
||||||
|
|
||||||
|
These are extra fields not specified in NIP-02 that may be present in the stringified JSON of contacts events:
|
||||||
|
|
||||||
|
### Deprecated fields
|
||||||
|
|
||||||
|
- `{<relay-url>: {"read": <true|false>, "write": <true|false>}, ...}`: an object of relays used by a user to read/write. [NIP-65](65.md) should be used instead.
|
||||||
|
|
||||||
|
tags
|
||||||
|
====
|
||||||
|
|
||||||
|
These tags may be present in multiple event kinds. Whenever a different meaning is not specified by some more specific NIP, they have the following meanings:
|
||||||
|
|
||||||
|
- `r`: a web URL the event is referring to in some way
|
||||||
|
- `title`: name of [NIP-51](51.md) sets, [NIP-52](52.md) calendar event, [NIP-53](53.md) live event or [NIP-99](99.md) listing
|
||||||
51
25.md
51
25.md
|
|
@ -5,9 +5,9 @@ NIP-25
|
||||||
Reactions
|
Reactions
|
||||||
---------
|
---------
|
||||||
|
|
||||||
`draft` `optional` `author:jb55`
|
`draft` `optional`
|
||||||
|
|
||||||
A reaction is a `kind 7` note that is used to react to other notes.
|
A reaction is a `kind 7` event that is used to react to other events.
|
||||||
|
|
||||||
The generic reaction, represented by the `content` set to a `+` string, SHOULD
|
The generic reaction, represented by the `content` set to a `+` string, SHOULD
|
||||||
be interpreted as a "like" or "upvote".
|
be interpreted as a "like" or "upvote".
|
||||||
|
|
@ -18,32 +18,57 @@ downvote or dislike on a post. A client MAY also choose to tally likes against
|
||||||
dislikes in a reddit-like system of upvotes and downvotes, or display them as
|
dislikes in a reddit-like system of upvotes and downvotes, or display them as
|
||||||
separate tallies.
|
separate tallies.
|
||||||
|
|
||||||
The `content` MAY be an emoji, in this case it MAY be interpreted as a "like" or "dislike",
|
The `content` MAY be an emoji, or [NIP-30](30.md) custom emoji in this case it MAY be interpreted as a "like" or "dislike",
|
||||||
or the client MAY display this emoji reaction on the post.
|
or the client MAY display this emoji reaction on the post. If the `content` is an empty string then the client should
|
||||||
|
consider it a "+".
|
||||||
|
|
||||||
Tags
|
Tags
|
||||||
----
|
----
|
||||||
|
|
||||||
The reaction event SHOULD include `e` and `p` tags from the note the user is
|
The reaction event SHOULD include `a`, `e` and `p` tags pointing to the note the user is
|
||||||
reacting to. This allows users to be notified of reactions to posts they were
|
reacting to. The `p` tag allows authors to be notified. The `e` tags enables clients
|
||||||
mentioned in. Including the `e` tags enables clients to pull all the reactions
|
to pull all the reactions to individual events and `a` tags enables clients to seek reactions
|
||||||
associated with individual posts or all the posts in a thread.
|
for all versions of a replaceable event.
|
||||||
|
|
||||||
The last `e` tag MUST be the `id` of the note that is being reacted to.
|
The `e` tag MUST be the `id` of the note that is being reacted to.
|
||||||
|
|
||||||
The last `p` tag MUST be the `pubkey` of the event being reacted to.
|
The `a` tag MUST contain the coordinates (`kind:pubkey:d-tag`) of the replaceable being reacted to.
|
||||||
|
|
||||||
|
The `p` tag MUST be the `pubkey` of the event being reacted to.
|
||||||
|
|
||||||
|
The reaction event MAY include a `k` tag with the stringified kind number
|
||||||
|
of the reacted event as its value.
|
||||||
|
|
||||||
Example code
|
Example code
|
||||||
|
|
||||||
```swift
|
```swift
|
||||||
func make_like_event(pubkey: String, privkey: String, liked: NostrEvent) -> NostrEvent {
|
func make_like_event(pubkey: String, privkey: String, liked: NostrEvent) -> NostrEvent {
|
||||||
var tags: [[String]] = liked.tags.filter {
|
|
||||||
tag in tag.count >= 2 && (tag[0] == "e" || tag[0] == "p")
|
|
||||||
}
|
|
||||||
tags.append(["e", liked.id])
|
tags.append(["e", liked.id])
|
||||||
tags.append(["p", liked.pubkey])
|
tags.append(["p", liked.pubkey])
|
||||||
|
tags.append(["k", liked.kind])
|
||||||
let ev = NostrEvent(content: "+", pubkey: pubkey, kind: 7, tags: tags)
|
let ev = NostrEvent(content: "+", pubkey: pubkey, kind: 7, tags: tags)
|
||||||
ev.calculate_id()
|
ev.calculate_id()
|
||||||
ev.sign(privkey: privkey)
|
ev.sign(privkey: privkey)
|
||||||
return ev
|
return ev
|
||||||
}
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Custom Emoji Reaction
|
||||||
|
---------------------
|
||||||
|
|
||||||
|
The client may specify a custom emoji ([NIP-30](30.md)) `:shortcode:` in the
|
||||||
|
reaction content. The client should refer to the emoji tag and render the
|
||||||
|
content as an emoji if shortcode is specified.
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"kind": 7,
|
||||||
|
"content": ":soapbox:",
|
||||||
|
"tags": [
|
||||||
|
["emoji", "soapbox", "https://gleasonator.com/emoji/Gleasonator/soapbox.png"]
|
||||||
|
],
|
||||||
|
...other fields
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
The content can be set only one `:shortcode:`. And emoji tag should be one.
|
||||||
|
|
|
||||||
2
26.md
2
26.md
|
|
@ -4,7 +4,7 @@ NIP-26
|
||||||
Delegated Event Signing
|
Delegated Event Signing
|
||||||
-----
|
-----
|
||||||
|
|
||||||
`draft` `optional` `author:markharding` `author:minds`
|
`draft` `optional`
|
||||||
|
|
||||||
This NIP defines how events can be delegated so that they can be signed by other keypairs.
|
This NIP defines how events can be delegated so that they can be signed by other keypairs.
|
||||||
|
|
||||||
|
|
|
||||||
2
27.md
2
27.md
|
|
@ -4,7 +4,7 @@ NIP-27
|
||||||
Text Note References
|
Text Note References
|
||||||
--------------------
|
--------------------
|
||||||
|
|
||||||
`draft` `optional` `author:arthurfranca` `author:hodlbod` `author:fiatjaf`
|
`draft` `optional`
|
||||||
|
|
||||||
This document standardizes the treatment given by clients of inline references of other events and profiles inside the `.content` of any event that has readable text in its `.content` (such as kinds 1 and 30023).
|
This document standardizes the treatment given by clients of inline references of other events and profiles inside the `.content` of any event that has readable text in its `.content` (such as kinds 1 and 30023).
|
||||||
|
|
||||||
|
|
|
||||||
16
28.md
16
28.md
|
|
@ -5,7 +5,7 @@ NIP-28
|
||||||
Public Chat
|
Public Chat
|
||||||
-----------
|
-----------
|
||||||
|
|
||||||
`draft` `optional` `author:ChristopherDavid` `author:fiatjaf` `author:jb55` `author:Cameri`
|
`draft` `optional`
|
||||||
|
|
||||||
This NIP defines new event kinds for public chat channels, channel messages, and basic client-side moderation.
|
This NIP defines new event kinds for public chat channels, channel messages, and basic client-side moderation.
|
||||||
|
|
||||||
|
|
@ -23,11 +23,11 @@ Client-centric moderation gives client developers discretion over what types of
|
||||||
|
|
||||||
Create a public chat channel.
|
Create a public chat channel.
|
||||||
|
|
||||||
In the channel creation `content` field, Client SHOULD include basic channel metadata (`name`, `about`, `picture` as specified in kind 41).
|
In the channel creation `content` field, Client SHOULD include basic channel metadata (`name`, `about`, `picture` and `relays` as specified in kind 41).
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"content": "{\"name\": \"Demo Channel\", \"about\": \"A test channel.\", \"picture\": \"https://placekitten.com/200/200\"}",
|
"content": "{\"name\": \"Demo Channel\", \"about\": \"A test channel.\", \"picture\": \"https://placekitten.com/200/200\", \"relays\": [\"wss://nos.lol\", \"wss://nostr.mom\"]}",
|
||||||
...
|
...
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
@ -46,6 +46,7 @@ Clients SHOULD support basic metadata fields:
|
||||||
- `name` - string - Channel name
|
- `name` - string - Channel name
|
||||||
- `about` - string - Channel description
|
- `about` - string - Channel description
|
||||||
- `picture` - string - URL of channel picture
|
- `picture` - string - URL of channel picture
|
||||||
|
- `relays` - array - List of relays to download and broadcast events to
|
||||||
|
|
||||||
Clients MAY add additional metadata fields.
|
Clients MAY add additional metadata fields.
|
||||||
|
|
||||||
|
|
@ -53,7 +54,7 @@ Clients SHOULD use [NIP-10](10.md) marked "e" tags to recommend a relay.
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"content": "{\"name\": \"Updated Demo Channel\", \"about\": \"Updating a test channel.\", \"picture\": \"https://placekitten.com/201/201\"}",
|
"content": "{\"name\": \"Updated Demo Channel\", \"about\": \"Updating a test channel.\", \"picture\": \"https://placekitten.com/201/201\", \"relays\": [\"wss://nos.lol\", \"wss://nostr.mom\"]}",
|
||||||
"tags": [["e", <channel_create_event_id>, <relay-url>]],
|
"tags": [["e", <channel_create_event_id>, <relay-url>]],
|
||||||
...
|
...
|
||||||
}
|
}
|
||||||
|
|
@ -132,12 +133,11 @@ Clients MAY hide event 42s for users other than the user who sent the event 44.
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
## NIP-10 relay recommendations
|
## Relay recommendations
|
||||||
|
|
||||||
For [NIP-10](10.md) relay recommendations, clients generally SHOULD use the relay URL of the original (oldest) kind 40 event.
|
Clients SHOULD use the relay URLs of the metadata events.
|
||||||
|
|
||||||
Clients MAY recommend any relay URL. For example, if a relay hosting the original kind 40 event for a channel goes offline, clients could instead fetch channel data from a backup relay, or a relay that clients trust more than the original relay.
|
|
||||||
|
|
||||||
|
Clients MAY use any relay URL. For example, if a relay hosting the original kind 40 event for a channel goes offline, clients could instead fetch channel data from a backup relay, or a relay that clients trust more than the original relay.
|
||||||
|
|
||||||
Motivation
|
Motivation
|
||||||
----------
|
----------
|
||||||
|
|
|
||||||
197
29.md
Normal file
197
29.md
Normal file
|
|
@ -0,0 +1,197 @@
|
||||||
|
NIP-29
|
||||||
|
======
|
||||||
|
|
||||||
|
Relay-based Groups
|
||||||
|
------------------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
This NIP defines a standard for groups that are only writable by a closed set of users. They can be public for reading by external users or not.
|
||||||
|
|
||||||
|
Groups are identified by a random string of any length that serves as an _id_.
|
||||||
|
|
||||||
|
There is no way to create a group, what happens is just that relays (most likely when asked by users) will create rules around some specific ids so these ids can serve as an actual group, henceforth messages sent to that group will be subject to these rules.
|
||||||
|
|
||||||
|
Normally a group will originally belong to one specific relay, but the community may choose to move the group to other relays or even fork the group so it exists in different forms -- still using the same _id_ -- across different relays.
|
||||||
|
|
||||||
|
## Relay-generated events
|
||||||
|
|
||||||
|
Relays are supposed to generate the events that describe group metadata and group admins. These are parameterized replaceable events signed by the relay keypair directly, with the group _id_ as the `d` tag.
|
||||||
|
|
||||||
|
## Group identifier
|
||||||
|
|
||||||
|
A group may be identified by a string in the format `<host>'<group-id>`. For example, a group with _id_ `abcdef` hosted at the relay `wss://groups.nostr.com` would be identified by the string `groups.nostr.com'abcdef`.
|
||||||
|
|
||||||
|
## The `h` tag
|
||||||
|
|
||||||
|
Events sent by users to groups (chat messages, text notes, moderation events etc) must have an `h` tag with the value set to the group _id_.
|
||||||
|
|
||||||
|
## Timeline references
|
||||||
|
|
||||||
|
In order to not be used out of context, events sent to these groups may contain references to previous events seen from the same relay in the `previous` tag. The choice of which previous events to pick belongs to the clients. The references are to be made using the first 8 characters (4 bytes) of any event in the last 50 events seen by the user in the relay, excluding events by themselves. There can be any number of references (including zero), but it's recommended that clients include at least 3 and that relays enforce this.
|
||||||
|
|
||||||
|
This is a hack to prevent messages from being broadcasted to external relays that have forks of one group out of context. Relays are expected to reject any events that contain timeline references to events not found in their own database. Clients should also check these to keep relays honest about them.
|
||||||
|
|
||||||
|
## Late publication
|
||||||
|
|
||||||
|
Relays should prevent late publication (messages published now with a timestamp from days or even hours ago) unless they are open to receive a group forked or moved from another relay.
|
||||||
|
|
||||||
|
## Event definitions
|
||||||
|
|
||||||
|
- *text root note* (`kind:11`)
|
||||||
|
|
||||||
|
This is the basic unit of a "microblog" root text note sent to a group.
|
||||||
|
|
||||||
|
```js
|
||||||
|
"kind": 11,
|
||||||
|
"content": "hello my friends lovers of pizza",
|
||||||
|
"tags": [
|
||||||
|
["h", "<group-id>"],
|
||||||
|
["previous", "<event-id-first-chars>", "<event-id-first-chars>", ...]
|
||||||
|
]
|
||||||
|
...
|
||||||
|
```
|
||||||
|
|
||||||
|
- *threaded text reply* (`kind:12`)
|
||||||
|
|
||||||
|
This is the basic unit of a "microblog" reply note sent to a group. It's the same as `kind:11`, except for the fact that it must be used whenever it's in reply to some other note (either in reply to a `kind:11` or a `kind:12`). `kind:12` events SHOULD use NIP-10 markers, leaving an empty relay url:
|
||||||
|
|
||||||
|
* `["e", "<kind-11-root-id>", "", "root"]`
|
||||||
|
* `["e", "<kind-12-event-id>", "", "reply"]`
|
||||||
|
|
||||||
|
- *chat message* (`kind:9`)
|
||||||
|
|
||||||
|
This is the basic unit of a _chat message_ sent to a group.
|
||||||
|
|
||||||
|
```js
|
||||||
|
"kind": 9,
|
||||||
|
"content": "hello my friends lovers of pizza",
|
||||||
|
"tags": [
|
||||||
|
["h", "<group-id>"],
|
||||||
|
["previous", "<event-id-first-chars>", "<event-id-first-chars>", ...]
|
||||||
|
]
|
||||||
|
...
|
||||||
|
```
|
||||||
|
|
||||||
|
- *chat message threaded reply* (`kind:10`)
|
||||||
|
|
||||||
|
Similar to `kind:12`, this is the basic unit of a chat message sent to a group. This is intended for in-chat threads that may be hidden by default. Not all in-chat replies MUST use `kind:10`, only when the intention is to create a hidden thread that isn't part of the normal flow of the chat (although clients are free to display those by default too).
|
||||||
|
|
||||||
|
`kind:10` SHOULD use NIP-10 markers, just like `kind:12`.
|
||||||
|
|
||||||
|
- *join request* (`kind:9021`)
|
||||||
|
|
||||||
|
Any user can send one of these events to the relay in order to be automatically or manually added to the group. If the group is `open` the relay will automatically issue a `kind:9000` in response adding this user. Otherwise group admins may choose to query for these requests and act upon them.
|
||||||
|
|
||||||
|
```js
|
||||||
|
{
|
||||||
|
"kind": 9021,
|
||||||
|
"content": "optional reason",
|
||||||
|
"tags": [
|
||||||
|
["h", "<group-id>"]
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
- *moderation events* (`kinds:9000-9020`) (optional)
|
||||||
|
|
||||||
|
Clients can send these events to a relay in order to accomplish a moderation action. Relays must check if the pubkey sending the event is capable of performing the given action. The relay may discard the event after taking action or keep it as a moderation log.
|
||||||
|
|
||||||
|
```js
|
||||||
|
{
|
||||||
|
"kind": 90xx,
|
||||||
|
"content": "optional reason",
|
||||||
|
"tags": [
|
||||||
|
["h", "<group-id>"],
|
||||||
|
["previous", ...]
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Each moderation action uses a different kind and requires different arguments, which are given as tags. These are defined in the following table:
|
||||||
|
|
||||||
|
| kind | name | tags |
|
||||||
|
| --- | --- | --- |
|
||||||
|
| 9000 | `add-user` | `p` (pubkey hex) |
|
||||||
|
| 9001 | `remove-user` | `p` (pubkey hex) |
|
||||||
|
| 9002 | `edit-metadata` | `name`, `about`, `picture` (string) |
|
||||||
|
| 9003 | `add-permission` | `p` (pubkey), `permission` (name) |
|
||||||
|
| 9004 | `remove-permission` | `p` (pubkey), `permission` (name) |
|
||||||
|
| 9005 | `delete-event` | `e` (id hex) |
|
||||||
|
| 9006 | `edit-group-status` | `public` or `private`, `open` or `closed` |
|
||||||
|
|
||||||
|
- *group metadata* (`kind:39000`) (optional)
|
||||||
|
|
||||||
|
This event defines the metadata for the group -- basically how clients should display it. It must be generated and signed by the relay in which is found. Relays shouldn't accept these events if they're signed by anyone else.
|
||||||
|
|
||||||
|
If the group is forked and hosted in multiple relays, there will be multiple versions of this event in each different relay and so on.
|
||||||
|
|
||||||
|
```js
|
||||||
|
{
|
||||||
|
"kind": 39000,
|
||||||
|
"content": "",
|
||||||
|
"tags": [
|
||||||
|
["d", "<group-id>"],
|
||||||
|
["name", "Pizza Lovers"],
|
||||||
|
["picture", "https://pizza.com/pizza.png"],
|
||||||
|
["about", "a group for people who love pizza"],
|
||||||
|
["public"], // or ["private"]
|
||||||
|
["open"] // or ["closed"]
|
||||||
|
]
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
`name`, `picture` and `about` are basic metadata for the group for display purposes. `public` signals the group can be _read_ by anyone, while `private` signals that only AUTHed users can read. `open` signals that anyone can request to join and the request will be automatically granted, while `closed` signals that members must be pre-approved or that requests to join will be manually handled.
|
||||||
|
|
||||||
|
- *group admins* (`kind:39001`) (optional)
|
||||||
|
|
||||||
|
Similar to the group metadata, this event is supposed to be generated by relays that host the group.
|
||||||
|
|
||||||
|
Each admin gets a label that is only used for display purposes, and a list of permissions it has are listed afterwards. These permissions can inform client building UI, but ultimately are evaluated by the relay in order to become effective.
|
||||||
|
|
||||||
|
The list of capabilities, as defined by this NIP, for now, is the following:
|
||||||
|
|
||||||
|
- `add-user`
|
||||||
|
- `edit-metadata`
|
||||||
|
- `delete-event`
|
||||||
|
- `remove-user`
|
||||||
|
- `add-permission`
|
||||||
|
- `remove-permission`
|
||||||
|
- `edit-group-status`
|
||||||
|
|
||||||
|
```js
|
||||||
|
{
|
||||||
|
"kind": 39001,
|
||||||
|
"content": "list of admins for the pizza lovers group",
|
||||||
|
"tags": [
|
||||||
|
["d", "<group-id>"],
|
||||||
|
["p", "<pubkey1-as-hex>", "ceo", "add-user", "edit-metadata", "delete-event", "remove-user"],
|
||||||
|
["p", "<pubkey2-as-hex>", "secretary", "add-user", "delete-event"]
|
||||||
|
]
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
- *group members* (`kind:39002`) (optional)
|
||||||
|
|
||||||
|
Similar to *group admins*, this event is supposed to be generated by relays that host the group.
|
||||||
|
|
||||||
|
It's a NIP-51-like list of pubkeys that are members of the group. Relays might choose to not to publish this information or to restrict what pubkeys can fetch it.
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"kind": 39002,
|
||||||
|
"content": "list of members for the pizza lovers group",
|
||||||
|
"tags": [
|
||||||
|
["d", "<group-id>"],
|
||||||
|
["p", "<admin1>"],
|
||||||
|
["p", "<member-pubkey1>"],
|
||||||
|
["p", "<member-pubkey2>"],
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## Storing the list of groups a user belongs to
|
||||||
|
|
||||||
|
A definition for kind `10009` was included in [NIP-51](51.md) that allows clients to store the list of groups a user wants to remember being in.
|
||||||
4
30.md
4
30.md
|
|
@ -4,9 +4,9 @@ NIP-30
|
||||||
Custom Emoji
|
Custom Emoji
|
||||||
------------
|
------------
|
||||||
|
|
||||||
`draft` `optional` `author:alexgleason`
|
`draft` `optional`
|
||||||
|
|
||||||
Custom emoji may be added to **kind 0** and **kind 1** events by including one or more `"emoji"` tags, in the form:
|
Custom emoji may be added to **kind 0**, **kind 1**, **kind 7** ([NIP-25](25.md)) and **kind 30315** ([NIP-38](38.md)) events by including one or more `"emoji"` tags, in the form:
|
||||||
|
|
||||||
```
|
```
|
||||||
["emoji", <shortcode>, <image-url>]
|
["emoji", <shortcode>, <image-url>]
|
||||||
|
|
|
||||||
2
31.md
2
31.md
|
|
@ -4,7 +4,7 @@ NIP-31
|
||||||
Dealing with unknown event kinds
|
Dealing with unknown event kinds
|
||||||
--------------------------------
|
--------------------------------
|
||||||
|
|
||||||
`draft` `optional` `author:pablof7z` `author:fiatjaf`
|
`draft` `optional`
|
||||||
|
|
||||||
When creating a new custom event kind that is part of a custom protocol and isn't meant to be read as text (like `kind:1`), clients should use an `alt` tag to write a short human-readable plaintext summary of what that event is about.
|
When creating a new custom event kind that is part of a custom protocol and isn't meant to be read as text (like `kind:1`), clients should use an `alt` tag to write a short human-readable plaintext summary of what that event is about.
|
||||||
|
|
||||||
|
|
|
||||||
127
32.md
127
32.md
|
|
@ -4,9 +4,32 @@ NIP-32
|
||||||
Labeling
|
Labeling
|
||||||
---------
|
---------
|
||||||
|
|
||||||
`draft` `optional` `author:staab` `author:gruruya` `author:s3x-jay`
|
`draft` `optional`
|
||||||
|
|
||||||
A label is a `kind 1985` event that is used to label other entities. This supports a number of use cases, from distributed moderation and content recommendations to reviews and ratings.
|
A label is a `kind 1985` event that is used to label other entities. This supports a number of use cases,
|
||||||
|
including distributed moderation, collection management, license assignment, and content classification.
|
||||||
|
|
||||||
|
This NIP introduces two new tags:
|
||||||
|
|
||||||
|
- `L` denotes a label namespace
|
||||||
|
- `l` denotes a label
|
||||||
|
|
||||||
|
Label Namespace Tag
|
||||||
|
----
|
||||||
|
|
||||||
|
An `L` tag can be any string, but publishers SHOULD ensure they are unambiguous by using a well-defined namespace
|
||||||
|
(such as an ISO standard) or reverse domain name notation.
|
||||||
|
|
||||||
|
`L` tags are REQUIRED in order to support searching by namespace rather than by a specific tag. The special `ugc`
|
||||||
|
("user generated content") namespace MAY be used when the label content is provided by an end user.
|
||||||
|
|
||||||
|
`L` tags starting with `#` indicate that the label target should be associated with the label's value.
|
||||||
|
This is a way of attaching standard nostr tags to events, pubkeys, relays, urls, etc.
|
||||||
|
|
||||||
|
Label Tag
|
||||||
|
----
|
||||||
|
|
||||||
|
An `l` tag's value can be any string. `l` tags MUST include a `mark` matching an `L` tag value in the same event.
|
||||||
|
|
||||||
Label Target
|
Label Target
|
||||||
----
|
----
|
||||||
|
|
@ -16,47 +39,18 @@ labeled: `e`, `p`, `a`, `r`, or `t` tags. This allows for labeling of events, pe
|
||||||
or topics respectively. As with NIP-01, a relay hint SHOULD be included when using `e` and
|
or topics respectively. As with NIP-01, a relay hint SHOULD be included when using `e` and
|
||||||
`p` tags.
|
`p` tags.
|
||||||
|
|
||||||
Label Tag
|
|
||||||
----
|
|
||||||
|
|
||||||
This NIP introduces a new tag `l` which denotes a label, and a new `L` tag which denotes a label namespace.
|
|
||||||
A label MUST include a mark matching an `L` tag. `L` tags refer to a tag type within nostr, or a nomenclature
|
|
||||||
external to nostr defined either formally or by convention. Any string can be a namespace, but publishers SHOULD
|
|
||||||
ensure they are unambiguous by using a well-defined namespace (such as an ISO standard) or reverse domain name notation.
|
|
||||||
|
|
||||||
Namespaces starting with `#` indicate that the label target should be associated with the label's value.
|
|
||||||
This is a way of attaching standard nostr tags to events, pubkeys, relays, urls, etc.
|
|
||||||
|
|
||||||
Some examples:
|
|
||||||
|
|
||||||
- `["l", "footstr", "#t"]` - the publisher thinks the given entity should have the `footstr` topic applied.
|
|
||||||
- `["l", "<pubkey>", "#p"]` - the publisher thinks the given entity is related to `<pubkey>`
|
|
||||||
- `["l", "IT-MI", "ISO-3166-2"]` - Milano, Italy using ISO 3166-2.
|
|
||||||
- `["l", "VI-hum", "com.example.ontology"]` - Violence toward a human being as defined by ontology.example.com.
|
|
||||||
|
|
||||||
`L` tags containing the label namespaces MUST be included in order to support searching by
|
|
||||||
namespace rather than by a specific tag. The special `ugc` ("user generated content") namespace
|
|
||||||
MAY be used when the label content is provided by an end user.
|
|
||||||
|
|
||||||
`l` and `L` tags MAY be added to other event kinds to support self-reporting. For events
|
|
||||||
with a kind other than 1985, labels refer to the event itself.
|
|
||||||
|
|
||||||
Label Annotations
|
|
||||||
-----
|
|
||||||
|
|
||||||
A label tag MAY include a 4th positional element detailing extra metadata about the label in question. This string
|
|
||||||
should be a json-encoded object. Any key MAY be used, but the following are recommended:
|
|
||||||
|
|
||||||
- `quality` may have a value of 0 to 1. This allows for an absolute, granular scale that can be represented in any way (5 stars, color scale, etc).
|
|
||||||
- `confidence` may have a value of 0 to 1. This indicates the certainty which the author has about their rating.
|
|
||||||
- `context` may be an array of urls (including NIP-21 urls) indicating other context that should be considered when interpreting labels.
|
|
||||||
|
|
||||||
Content
|
Content
|
||||||
-------
|
-------
|
||||||
|
|
||||||
Labels should be short, meaningful strings. Longer discussions, such as for a review, or an
|
Labels should be short, meaningful strings. Longer discussions, such as for a review, or an
|
||||||
explanation of why something was labeled the way it was, should go in the event's `content` field.
|
explanation of why something was labeled the way it was, should go in the event's `content` field.
|
||||||
|
|
||||||
|
Self-Reporting
|
||||||
|
-------
|
||||||
|
|
||||||
|
`l` and `L` tags MAY be added to other event kinds to support self-reporting. For events
|
||||||
|
with a kind other than 1985, labels refer to the event itself.
|
||||||
|
|
||||||
Example events
|
Example events
|
||||||
--------------
|
--------------
|
||||||
|
|
||||||
|
|
@ -71,36 +65,64 @@ A suggestion that multiple pubkeys be associated with the `permies` topic.
|
||||||
["p", <pubkey1>, <relay_url>],
|
["p", <pubkey1>, <relay_url>],
|
||||||
["p", <pubkey2>, <relay_url>]
|
["p", <pubkey2>, <relay_url>]
|
||||||
],
|
],
|
||||||
"content": "",
|
|
||||||
...
|
...
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
A review of a relay.
|
A report flagging violence toward a human being as defined by ontology.example.com.
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"kind": 1985,
|
"kind": 1985,
|
||||||
"tags": [
|
"tags": [
|
||||||
["L", "com.example.ontology"],
|
["L", "com.example.ontology"],
|
||||||
["l", "relay/review", "com.example.ontology", "{\"quality\": 0.1}"],
|
["l", "VI-hum", "com.example.ontology"],
|
||||||
["r", <relay_url>]
|
["p", <pubkey1>, <relay_url>],
|
||||||
|
["p", <pubkey2>, <relay_url>]
|
||||||
],
|
],
|
||||||
"content": "This relay is full of mean people.",
|
|
||||||
...
|
...
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
Publishers can self-label by adding `l` tags to their own non-1985 events.
|
A moderation suggestion for a chat event.
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"kind": 1985,
|
||||||
|
"tags": [
|
||||||
|
["L", "nip28.moderation"],
|
||||||
|
["l", "approve", "nip28.moderation"],
|
||||||
|
["e", <kind40_event_id>, <relay_url>]
|
||||||
|
],
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Assignment of a license to an event.
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"kind": 1985,
|
||||||
|
"tags": [
|
||||||
|
["L", "license"],
|
||||||
|
["l", "MIT", "license"],
|
||||||
|
["e", <event_id>, <relay_url>]
|
||||||
|
],
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Publishers can self-label by adding `l` tags to their own non-1985 events. In this case, the kind 1 event's author
|
||||||
|
is labeling their note as being related to Milan, Italy using ISO 3166-2.
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"kind": 1,
|
"kind": 1,
|
||||||
"tags": [
|
"tags": [
|
||||||
["L", "com.example.ontology"],
|
["L", "ISO-3166-2"],
|
||||||
["l", "IL-frd", "com.example.ontology"]
|
["l", "IT-MI", "ISO-3166-2"]
|
||||||
],
|
],
|
||||||
"content": "Send me 100 sats and I'll send you 200 back",
|
"content": "It's beautiful here in Milan!",
|
||||||
...
|
...
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
@ -124,3 +146,16 @@ Vocabularies MAY choose to fully qualify all labels within a namespace (for exam
|
||||||
formal vocabularies that should not be confused with another namespace when querying
|
formal vocabularies that should not be confused with another namespace when querying
|
||||||
without an `L` tag. For these vocabularies, all labels SHOULD include the namespace
|
without an `L` tag. For these vocabularies, all labels SHOULD include the namespace
|
||||||
(rather than mixing qualified and unqualified labels).
|
(rather than mixing qualified and unqualified labels).
|
||||||
|
|
||||||
|
A good heuristic for whether a use case fits this NIP is whether labels would ever be unique.
|
||||||
|
For example, many events might be labeled with a particular place, topic, or pubkey, but labels
|
||||||
|
with specific values like "John Doe" or "3.18743" are not labels, they are values, and should
|
||||||
|
be handled in some other way.
|
||||||
|
|
||||||
|
|
||||||
|
Appendix: Known Ontologies
|
||||||
|
-------------------------
|
||||||
|
|
||||||
|
Below is a non-exhaustive list of ontologies currently in widespread use.
|
||||||
|
|
||||||
|
- (social.ontolo.categories)[https://ontolo.social/]
|
||||||
|
|
|
||||||
50
33.md
50
33.md
|
|
@ -4,52 +4,6 @@ NIP-33
|
||||||
Parameterized Replaceable Events
|
Parameterized Replaceable Events
|
||||||
--------------------------------
|
--------------------------------
|
||||||
|
|
||||||
`draft` `optional` `author:Semisol` `author:Kukks` `author:Cameri` `author:Giszmo`
|
`final` `mandatory`
|
||||||
|
|
||||||
This NIP adds a new event range that allows for replacement of events that have the same `d` tag and kind unlike NIP-16 which only replaced by kind.
|
Moved to [NIP-01](01.md).
|
||||||
|
|
||||||
Implementation
|
|
||||||
--------------
|
|
||||||
The value of a tag can be any string and is defined as the first parameter of a tag after the tag name.
|
|
||||||
|
|
||||||
A *parameterized replaceable event* is defined as an event with a kind `30000 <= n < 40000`.
|
|
||||||
Upon a parameterized replaceable event with a newer timestamp than the currently known latest
|
|
||||||
replaceable event with the same kind, author and first `d` tag value being received, the old event
|
|
||||||
SHOULD be discarded, effectively replacing what gets returned when querying for
|
|
||||||
`author:kind:d-tag` tuples.
|
|
||||||
|
|
||||||
If two events have the same timestamp, the event with the lowest id (first in lexical order) SHOULD be retained, and the other discarded.
|
|
||||||
|
|
||||||
A missing or a `d` tag with no value should be interpreted equivalent to a `d` tag with the
|
|
||||||
value as an empty string. Events from the same author with any of the following `tags`
|
|
||||||
replace each other:
|
|
||||||
|
|
||||||
* `"tags":[["d",""]]`
|
|
||||||
* `"tags":[]`: implicit `d` tag with empty value
|
|
||||||
* `"tags":[["d"]]`: implicit empty value `""`
|
|
||||||
* `"tags":[["d",""],["d","not empty"]]`: only first `d` tag is considered
|
|
||||||
* `"tags":[["d"],["d","some value"]]`: only first `d` tag is considered
|
|
||||||
* `"tags":[["e"]]`: same as no tags
|
|
||||||
* `"tags":[["d","","1"]]`: only the first value is considered (`""`)
|
|
||||||
|
|
||||||
Clients SHOULD NOT use `d` tags with multiple values and SHOULD include the `d` tag even if it has no value to allow querying using the `#d` filter.
|
|
||||||
|
|
||||||
Referencing and tagging
|
|
||||||
-----------------------
|
|
||||||
|
|
||||||
Normally (as per NIP-01, NIP-12) the `"p"` tag is used for referencing public keys and the
|
|
||||||
`"e"` tag for referencing event ids and the `note`, `npub`, `nprofile` or `nevent` are their
|
|
||||||
equivalents for event tags (i.e. an `nprofile` is generally translated into a tag
|
|
||||||
`["p", "<event hex id>", "<relay url>"]`).
|
|
||||||
|
|
||||||
To support linking to parameterized replaceable events, the `naddr` code is introduced on
|
|
||||||
NIP-19. It includes the public key of the event author and the `d` tag (and relays) such that
|
|
||||||
the referenced combination of public key and `d` tag can be found.
|
|
||||||
|
|
||||||
The equivalent in `tags` to the `naddr` code is the tag `"a"`, comprised of `["a", "<kind>:<pubkey>:<d-identifier>", "<relay url>"]`.
|
|
||||||
|
|
||||||
Client Behavior
|
|
||||||
---------------
|
|
||||||
|
|
||||||
Clients SHOULD use the `supported_nips` field to learn if a relay supports this NIP.
|
|
||||||
Clients MAY send parameterized replaceable events to relays that may not support this NIP, and clients querying SHOULD be prepared for the relay to send multiple events and should use the latest one and are recommended to send a `#d` tag filter. Clients should account for the fact that missing `d` tags or ones with no value are not returned in tag filters, and are recommended to always include a `d` tag with a value.
|
|
||||||
|
|
|
||||||
152
34.md
Normal file
152
34.md
Normal file
|
|
@ -0,0 +1,152 @@
|
||||||
|
NIP-34
|
||||||
|
======
|
||||||
|
|
||||||
|
`git` stuff
|
||||||
|
-----------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
This NIP defines all the ways code collaboration using and adjacent to [`git`](https://git-scm.com/) can be done using Nostr.
|
||||||
|
|
||||||
|
## Repository announcements
|
||||||
|
|
||||||
|
Git repositories are hosted in Git-enabled servers, but their existence can be announced using Nostr events, as well as their willingness to receive patches, bug reports and comments in general.
|
||||||
|
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"kind": 30617,
|
||||||
|
"content": "",
|
||||||
|
"tags": [
|
||||||
|
["d", "<repo-id>"], // usually kebab-case short name
|
||||||
|
["name", "<human-readable project name>"],
|
||||||
|
["description", "brief human-readable project description>"],
|
||||||
|
["web", "<url for browsing>", ...], // a webpage url, if the git server being used provides such a thing
|
||||||
|
["clone", "<url for git-cloning>", ...], // a url to be given to `git clone` so anyone can clone it
|
||||||
|
["relays", "<relay-url>", ...] // relays that this repository will monitor for patches and issues
|
||||||
|
["r", "<earliest-unique-commit-id>", "euc"]
|
||||||
|
["maintainers", "<other-recognized-maintainer>", ...]
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
The tags `web`, `clone`, `relays`, `maintainers` can have multiple values.
|
||||||
|
|
||||||
|
The `r` tag annotated with the `"euc"` marker should be the commit ID of the earliest unique commit of this repo, made to identify it among forks and group it with other repositories hosted elsewhere that may represent essentially the same project. In most cases it will be the root commit of a repository. In case of a permanent fork between two projects, then the first commit after the fork should be used.
|
||||||
|
|
||||||
|
Except `d`, all tags are optional.
|
||||||
|
|
||||||
|
## Patches
|
||||||
|
|
||||||
|
Patches can be sent by anyone to any repository. Patches to a specific repository SHOULD be sent to the relays specified in that repository's announcement event's `"relays"` tag. Patch events SHOULD include an `a` tag pointing to that repository's announcement address.
|
||||||
|
|
||||||
|
Patches in a patch set SHOULD include a NIP-10 `e` `reply` tag pointing to the previous patch.
|
||||||
|
|
||||||
|
The first patch revision in a patch revision SHOULD include a NIP-10 `e` `reply` to the original root patch.
|
||||||
|
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"kind": 1617,
|
||||||
|
"content": "<patch>", // contents of <git format-patch>
|
||||||
|
"tags": [
|
||||||
|
["a", "30617:<base-repo-owner-pubkey>:<base-repo-id>"],
|
||||||
|
["r", "<earliest-unique-commit-id-of-repo>"] // so clients can subscribe to all patches sent to a local git repo
|
||||||
|
["p", "<repository-owner>"],
|
||||||
|
["p", "<other-user>"], // optionally send the patch to another user to bring it to their attention
|
||||||
|
|
||||||
|
["t", "root"], // ommited for additional patches in a series
|
||||||
|
// for the first patch in a revision
|
||||||
|
["t", "root-revision"],
|
||||||
|
|
||||||
|
// optional tags for when it is desirable that the merged patch has a stable commit id
|
||||||
|
// these fields are necessary for ensuring that the commit resulting from applying a patch
|
||||||
|
// has the same id as it had in the proposer's machine -- all these tags can be omitted
|
||||||
|
// if the maintainer doesn't care about these things
|
||||||
|
["commit", "<current-commit-id>"],
|
||||||
|
["r", "<current-commit-id>"] // so clients can find existing patches for a specific commit
|
||||||
|
["parent-commit", "<parent-commit-id>"],
|
||||||
|
["commit-pgp-sig", "-----BEGIN PGP SIGNATURE-----..."], // empty string for unsigned commit
|
||||||
|
["committer", "<name>", "<email>", "<timestamp>", "<timezone offset in minutes>"],
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
The first patch in a series MAY be a cover letter in the format produced by `git format-patch`.
|
||||||
|
|
||||||
|
## Issues
|
||||||
|
|
||||||
|
Issues are Markdown text that is just human-readable conversational threads related to the repository: bug reports, feature requests, questions or comments of any kind. Like patches, these SHOULD be sent to the relays specified in that repository's announcement event's `"relays"` tag.
|
||||||
|
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"kind": 1621,
|
||||||
|
"content": "<markdown text>",
|
||||||
|
"tags": [
|
||||||
|
["a", "30617:<base-repo-owner-pubkey>:<base-repo-id>"],
|
||||||
|
["p", "<repository-owner>"]
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## Replies
|
||||||
|
|
||||||
|
Replies are also Markdown text. The difference is that they MUST be issued as replies to either a `kind:1621` _issue_ or a `kind:1617` _patch_ event. The threading of replies and patches should follow NIP-10 rules.
|
||||||
|
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"kind": 1622,
|
||||||
|
"content": "<markdown text>",
|
||||||
|
"tags": [
|
||||||
|
["a", "30617:<base-repo-owner-pubkey>:<base-repo-id>", "<relay-url>"],
|
||||||
|
["e", "<issue-or-patch-id-hex>", "", "root"],
|
||||||
|
|
||||||
|
// other "e" and "p" tags should be applied here when necessary, following the threading rules of NIP-10
|
||||||
|
["p", "<patch-author-pubkey-hex>", "", "mention"],
|
||||||
|
["e", "<previous-reply-id-hex>", "", "reply"],
|
||||||
|
// ...
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## Status
|
||||||
|
|
||||||
|
Root Patches and Issues have a Status that defaults to 'Open' and can be set by issuing Status events.
|
||||||
|
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"kind": 1630, // Open
|
||||||
|
"kind": 1631, // Applied / Merged for Patches; Resolved for Issues
|
||||||
|
"kind": 1632, // Closed
|
||||||
|
"kind": 1633, // Draft
|
||||||
|
"content": "<markdown text>",
|
||||||
|
"tags": [
|
||||||
|
["e", "<issue-or-original-root-patch-id-hex>", "", "root"],
|
||||||
|
["e", "<accepted-revision-root-id-hex>", "", "reply"], // for when revisions applied
|
||||||
|
["p", "<repository-owner>"],
|
||||||
|
["p", "<root-event-author>"],
|
||||||
|
["p", "<revision-author>"],
|
||||||
|
|
||||||
|
// optional for improved subscription filter efficiency
|
||||||
|
["a", "30617:<base-repo-owner-pubkey>:<base-repo-id>", "<relay-url>"],
|
||||||
|
["r", "<earliest-unique-commit-id-of-repo>"]
|
||||||
|
|
||||||
|
// optional for `1631` status
|
||||||
|
["e", "<applied-or-merged-patch-event-id>", "", "mention"], // for each
|
||||||
|
// when merged
|
||||||
|
["merge-commit", "<merge-commit-id>"]
|
||||||
|
["r", "<merge-commit-id>"]
|
||||||
|
// when applied
|
||||||
|
["applied-as-commits", "<commit-id-in-master-branch>", ...]
|
||||||
|
["r", "<applied-commit-id>"] // for each
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
The Status event with the largest created_at date is valid.
|
||||||
|
|
||||||
|
The Status of a patch-revision defaults to either that of the root-patch, or `1632` (Closed) if the root-patch's Status is `1631` and the patch-revision isn't tagged in the `1631` event.
|
||||||
|
|
||||||
|
|
||||||
|
## Possible things to be added later
|
||||||
|
|
||||||
|
- "branch merge" kind (specifying a URL from where to fetch the branch to be merged)
|
||||||
|
- inline file comments kind (we probably need one for patches and a different one for merged files)
|
||||||
70
35.md
Normal file
70
35.md
Normal file
|
|
@ -0,0 +1,70 @@
|
||||||
|
NIP-35
|
||||||
|
======
|
||||||
|
|
||||||
|
Torrents
|
||||||
|
-----------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
This NIP defined a new `kind 2003` which is a Torrent.
|
||||||
|
|
||||||
|
`kind 2003` is a simple torrent index where there is enough information to search for content and construct the magnet link. No torrent files exist on nostr.
|
||||||
|
|
||||||
|
## Tags
|
||||||
|
- `x`: V1 BitTorrent Info Hash, as seen in the [magnet link](https://www.bittorrent.org/beps/bep_0053.html) `magnet:?xt=urn:btih:HASH`
|
||||||
|
- `file`: A file entry inside the torrent, including the full path ie. `info/example.txt`
|
||||||
|
- `tracker`: (Optional) A tracker to use for this torrent
|
||||||
|
|
||||||
|
In order to make torrents searchable by general category, you SHOULD include a few tags like `movie`, `tv`, `HD`, `UHD` etc.
|
||||||
|
|
||||||
|
## Tag prefixes
|
||||||
|
|
||||||
|
Tag prefixes are used to label the content with references, ie. `["i", "imdb:1234"]`
|
||||||
|
|
||||||
|
- `tcat`: A comma separated text category path, ie. `["i", "tcat:video,movie,4k"]`, this should also match the `newznab` category in a best effort approach.
|
||||||
|
- `newznab`: The category ID from [newznab](https://github.com/Prowlarr/Prowlarr/blob/develop/src/NzbDrone.Core/Indexers/NewznabStandardCategory.cs)
|
||||||
|
- `tmdb`: [The movie database](https://www.themoviedb.org/) id.
|
||||||
|
- `ttvdb`: [TV database](https://thetvdb.com/) id.
|
||||||
|
- `imdb`: [IMDB](https://www.imdb.com/) id.
|
||||||
|
- `mal`: [MyAnimeList](https://myanimelist.net/) id.
|
||||||
|
- `anilist`: [AniList](https://anilist.co/) id.
|
||||||
|
|
||||||
|
A second level prefix should be included where the database supports multiple media types.
|
||||||
|
- `tmdb:movie:693134` maps to `themoviedb.org/movie/693134`
|
||||||
|
- `ttvdb:movie:290272` maps to `thetvdb.com/movies/dune-part-two`
|
||||||
|
- `mal:anime:9253` maps to `myanimelist.net/anime/9253`
|
||||||
|
- `mal:manga:17517` maps to `myanimelist.net/manga/17517`
|
||||||
|
|
||||||
|
In some cases the url mapping isnt direct, mapping the url in general is out of scope for this NIP, the section above is only a guide so that implementers have enough information to succsesfully map the url if they wish.
|
||||||
|
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"kind": 2003,
|
||||||
|
"content": "<long-description-pre-formatted>",
|
||||||
|
"tags": [
|
||||||
|
["title", "<torrent-title>"],
|
||||||
|
["x", "<bittorrent-info-hash>"],
|
||||||
|
["file", "<file-name>", "<file-size-in-bytes>"],
|
||||||
|
["file", "<file-name>", "<file-size-in-bytes>"],
|
||||||
|
["tracker", "udp://mytacker.com:1337"],
|
||||||
|
["tracker", "http://1337-tracker.net/announce"],
|
||||||
|
["i", "tcat:video,movie,4k"],
|
||||||
|
["i", "newznab:2045"],
|
||||||
|
["i", "imdb:tt15239678"],
|
||||||
|
["i", "tmdb:movie:693134"],
|
||||||
|
["i", "ttvdb:movie:290272"],
|
||||||
|
["t", "movie"],
|
||||||
|
["t", "4k"],
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## Torrent Comments
|
||||||
|
|
||||||
|
A torrent comment is a `kind 2004` event which is used to reply to a torrent event.
|
||||||
|
|
||||||
|
This event works exactly like a `kind 1` and should follow `NIP-10` for tagging.
|
||||||
|
|
||||||
|
## Implementations
|
||||||
|
1. [dtan.xyz](https://git.v0l.io/Kieran/dtan)
|
||||||
|
2. [nostrudel.ninja](https://github.com/hzrd149/nostrudel/tree/next/src/views/torrents)
|
||||||
4
36.md
4
36.md
|
|
@ -4,7 +4,7 @@ NIP-36
|
||||||
Sensitive Content / Content Warning
|
Sensitive Content / Content Warning
|
||||||
-----------------------------------
|
-----------------------------------
|
||||||
|
|
||||||
`draft` `optional` `author:fernandolguevara`
|
`draft` `optional`
|
||||||
|
|
||||||
The `content-warning` tag enables users to specify if the event's content needs to be approved by readers to be shown.
|
The `content-warning` tag enables users to specify if the event's content needs to be approved by readers to be shown.
|
||||||
Clients can hide the content until the user acts on it.
|
Clients can hide the content until the user acts on it.
|
||||||
|
|
@ -33,7 +33,7 @@ options:
|
||||||
["l", "reason", "content-warning"],
|
["l", "reason", "content-warning"],
|
||||||
["L", "social.nos.ontology"],
|
["L", "social.nos.ontology"],
|
||||||
["l", "NS-nud", "social.nos.ontology"],
|
["l", "NS-nud", "social.nos.ontology"],
|
||||||
["content-warning", "reason"] /* reason is optional */
|
["content-warning", "<optional reason>"]
|
||||||
],
|
],
|
||||||
"content": "sensitive content with #hastag\n",
|
"content": "sensitive content with #hastag\n",
|
||||||
"id": "<event-id>"
|
"id": "<event-id>"
|
||||||
|
|
|
||||||
61
38.md
Normal file
61
38.md
Normal file
|
|
@ -0,0 +1,61 @@
|
||||||
|
|
||||||
|
NIP-38
|
||||||
|
======
|
||||||
|
|
||||||
|
User Statuses
|
||||||
|
--------------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
## Abstract
|
||||||
|
|
||||||
|
This NIP enables a way for users to share live statuses such as what music they are listening to, as well as what they are currently doing: work, play, out of office, etc.
|
||||||
|
|
||||||
|
## Live Statuses
|
||||||
|
|
||||||
|
A special event with `kind:30315` "User Status" is defined as an *optionally expiring* _parameterized replaceable event_, where the `d` tag represents the status type:
|
||||||
|
|
||||||
|
For example:
|
||||||
|
|
||||||
|
```js
|
||||||
|
{
|
||||||
|
"kind": 30315,
|
||||||
|
"content": "Sign up for nostrasia!",
|
||||||
|
"tags": [
|
||||||
|
["d", "general"],
|
||||||
|
["r", "https://nostr.world"]
|
||||||
|
],
|
||||||
|
}
|
||||||
|
|
||||||
|
{
|
||||||
|
"kind": 30315,
|
||||||
|
"content": "Intergalatic - Beastie Boys",
|
||||||
|
"tags": [
|
||||||
|
["d", "music"],
|
||||||
|
["r", "spotify:search:Intergalatic%20-%20Beastie%20Boys"],
|
||||||
|
["expiration", "1692845589"]
|
||||||
|
],
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Two common status types are defined: `general` and `music`. `general` represent general statuses: "Working", "Hiking", etc.
|
||||||
|
|
||||||
|
`music` status events are for live streaming what you are currently listening to. The expiry of the `music` status should be when the track will stop playing.
|
||||||
|
|
||||||
|
Any other status types can be used but they are not defined by this NIP.
|
||||||
|
|
||||||
|
The status MAY include an `r`, `p`, `e` or `a` tag linking to a URL, profile, note, or parameterized replaceable event.
|
||||||
|
|
||||||
|
The `content` MAY include emoji(s), or [NIP-30](30.md) custom emoji(s). If the `content` is an empty string then the client should clear the status.
|
||||||
|
|
||||||
|
# Client behavior
|
||||||
|
|
||||||
|
Clients MAY display this next to the username on posts or profiles to provide live user status information.
|
||||||
|
|
||||||
|
# Use Cases
|
||||||
|
|
||||||
|
* Calendar nostr apps that update your general status when you're in a meeting
|
||||||
|
* Nostr Nests that update your general status with a link to the nest when you join
|
||||||
|
* Nostr music streaming services that update your music status when you're listening
|
||||||
|
* Podcasting apps that update your music status when you're listening to a podcast, with a link for others to listen as well
|
||||||
|
* Clients can use the system media player to update playing music status
|
||||||
8
39.md
8
39.md
|
|
@ -4,7 +4,7 @@ NIP-39
|
||||||
External Identities in Profiles
|
External Identities in Profiles
|
||||||
-------------------------------
|
-------------------------------
|
||||||
|
|
||||||
`draft` `optional` `author:pseudozach` `author:Semisol`
|
`draft` `optional`
|
||||||
|
|
||||||
## Abstract
|
## Abstract
|
||||||
|
|
||||||
|
|
@ -15,15 +15,13 @@ Nostr protocol users may have other online identities such as usernames, profile
|
||||||
A new optional `i` tag is introduced for `kind 0` metadata event contents in addition to name, about, picture fields as included in [NIP-01](https://github.com/nostr-protocol/nips/blob/master/01.md):
|
A new optional `i` tag is introduced for `kind 0` metadata event contents in addition to name, about, picture fields as included in [NIP-01](https://github.com/nostr-protocol/nips/blob/master/01.md):
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"id": <id>,
|
|
||||||
"pubkey": <pubkey>,
|
|
||||||
...
|
|
||||||
"tags": [
|
"tags": [
|
||||||
["i", "github:semisol", "9721ce4ee4fceb91c9711ca2a6c9a5ab"],
|
["i", "github:semisol", "9721ce4ee4fceb91c9711ca2a6c9a5ab"],
|
||||||
["i", "twitter:semisol_public", "1619358434134196225"],
|
["i", "twitter:semisol_public", "1619358434134196225"],
|
||||||
["i", "mastodon:bitcoinhackers.org/@semisol", "109775066355589974"]
|
["i", "mastodon:bitcoinhackers.org/@semisol", "109775066355589974"]
|
||||||
["i", "telegram:1087295469", "nostrdirectory/770"]
|
["i", "telegram:1087295469", "nostrdirectory/770"]
|
||||||
]
|
],
|
||||||
|
...
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
|
|
|
||||||
4
40.md
4
40.md
|
|
@ -2,9 +2,9 @@ NIP-40
|
||||||
======
|
======
|
||||||
|
|
||||||
Expiration Timestamp
|
Expiration Timestamp
|
||||||
-----------------------------------
|
--------------------
|
||||||
|
|
||||||
`draft` `optional` `author:0xtlt`
|
`draft` `optional`
|
||||||
|
|
||||||
The `expiration` tag enables users to specify a unix timestamp at which the message SHOULD be considered expired (by relays and clients) and SHOULD be deleted by relays.
|
The `expiration` tag enables users to specify a unix timestamp at which the message SHOULD be considered expired (by relays and clients) and SHOULD be deleted by relays.
|
||||||
|
|
||||||
|
|
|
||||||
79
42.md
79
42.md
|
|
@ -4,7 +4,7 @@ NIP-42
|
||||||
Authentication of clients to relays
|
Authentication of clients to relays
|
||||||
-----------------------------------
|
-----------------------------------
|
||||||
|
|
||||||
`draft` `optional` `author:Semisol` `author:fiatjaf`
|
`draft` `optional`
|
||||||
|
|
||||||
This NIP defines a way for clients to authenticate to relays by signing an ephemeral event.
|
This NIP defines a way for clients to authenticate to relays by signing an ephemeral event.
|
||||||
|
|
||||||
|
|
@ -12,69 +12,86 @@ This NIP defines a way for clients to authenticate to relays by signing an ephem
|
||||||
|
|
||||||
A relay may want to require clients to authenticate to access restricted resources. For example,
|
A relay may want to require clients to authenticate to access restricted resources. For example,
|
||||||
|
|
||||||
- A relay may request payment or other forms of whitelisting to publish events -- this can naïvely be achieved by limiting publication
|
- A relay may request payment or other forms of whitelisting to publish events -- this can naïvely be achieved by limiting publication to events signed by the whitelisted key, but with this NIP they may choose to accept any events as long as they are published from an authenticated user;
|
||||||
to events signed by the whitelisted key, but with this NIP they may choose to accept any events as long as they are published from an
|
- A relay may limit access to `kind: 4` DMs to only the parties involved in the chat exchange, and for that it may require authentication before clients can query for that kind.
|
||||||
authenticated user;
|
|
||||||
- A relay may limit access to `kind: 4` DMs to only the parties involved in the chat exchange, and for that it may require authentication
|
|
||||||
before clients can query for that kind.
|
|
||||||
- A relay may limit subscriptions of any kind to paying users or users whitelisted through any other means, and require authentication.
|
- A relay may limit subscriptions of any kind to paying users or users whitelisted through any other means, and require authentication.
|
||||||
|
|
||||||
## Definitions
|
## Definitions
|
||||||
|
|
||||||
This NIP defines a new message, `AUTH`, which relays can send when they support authentication and clients can send to relays when they want
|
### New client-relay protocol messages
|
||||||
to authenticate. When sent by relays, the message is of the following form:
|
|
||||||
|
|
||||||
```
|
This NIP defines a new message, `AUTH`, which relays CAN send when they support authentication and clients can send to relays when they want to authenticate. When sent by relays the message has the following form:
|
||||||
|
|
||||||
|
```json
|
||||||
["AUTH", <challenge-string>]
|
["AUTH", <challenge-string>]
|
||||||
```
|
```
|
||||||
|
|
||||||
And, when sent by clients, of the following form:
|
And, when sent by clients, the following form:
|
||||||
|
|
||||||
```
|
```json
|
||||||
["AUTH", <signed-event-json>]
|
["AUTH", <signed-event-json>]
|
||||||
```
|
```
|
||||||
|
|
||||||
The signed event is an ephemeral event not meant to be published or queried, it must be of `kind: 22242` and it should have at least two tags,
|
`AUTH` messages sent by clients MUST be answered with an `OK` message, like any `EVENT` message.
|
||||||
one for the relay URL and one for the challenge string as received from the relay.
|
|
||||||
Relays MUST exclude `kind: 22242` events from being broadcasted to any client.
|
### Canonical authentication event
|
||||||
`created_at` should be the current time. Example:
|
|
||||||
|
The signed event is an ephemeral event not meant to be published or queried, it must be of `kind: 22242` and it should have at least two tags, one for the relay URL and one for the challenge string as received from the relay. Relays MUST exclude `kind: 22242` events from being broadcasted to any client. `created_at` should be the current time. Example:
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"id": "...",
|
|
||||||
"pubkey": "...",
|
|
||||||
"created_at": 1669695536,
|
|
||||||
"kind": 22242,
|
"kind": 22242,
|
||||||
"tags": [
|
"tags": [
|
||||||
["relay", "wss://relay.example.com/"],
|
["relay", "wss://relay.example.com/"],
|
||||||
["challenge", "challengestringhere"]
|
["challenge", "challengestringhere"]
|
||||||
],
|
],
|
||||||
"content": "",
|
...
|
||||||
"sig": "..."
|
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
|
### `OK` and `CLOSED` machine-readable prefixes
|
||||||
|
|
||||||
|
This NIP defines two new prefixes that can be used in `OK` (in response to event writes by clients) and `CLOSED` (in response to rejected subscriptions by clients):
|
||||||
|
|
||||||
|
- `"auth-required: "` - for when a client has not performed `AUTH` and the relay requires that to fulfill the query or write the event.
|
||||||
|
- `"restricted: "` - for when a client has already performed `AUTH` but the key used to perform it is still not allowed by the relay or is exceeding its authorization.
|
||||||
|
|
||||||
## Protocol flow
|
## Protocol flow
|
||||||
|
|
||||||
At any moment the relay may send an `AUTH` message to the client containing a challenge. After receiving that the client may decide to
|
At any moment the relay may send an `AUTH` message to the client containing a challenge. The challenge is valid for the duration of the connection or until another challenge is sent by the relay. The client MAY decide to send its `AUTH` event at any point and the authenticated session is valid afterwards for the duration of the connection.
|
||||||
authenticate itself or not. The challenge is expected to be valid for the duration of the connection or until a next challenge is sent by
|
|
||||||
the relay.
|
|
||||||
|
|
||||||
The client may send an auth message right before performing an action for which it knows authentication will be required -- for example, right
|
### `auth-required` in response to a `REQ` message
|
||||||
before requesting `kind: 4` chat messages --, or it may do right on connection start or at some other moment it deems best. The authentication
|
|
||||||
is expected to last for the duration of the WebSocket connection.
|
|
||||||
|
|
||||||
Upon receiving a message from an unauthenticated user it can't fulfill without authentication, a relay may choose to notify the client. For
|
Given that a relay is likely to require clients to perform authentication only for certain jobs, like answering a `REQ` or accepting an `EVENT` write, these are some expected common flows:
|
||||||
that it can use a `NOTICE` or `OK` message with a standard prefix `"restricted: "` that is readable both by humans and machines, for example:
|
|
||||||
|
|
||||||
```
|
```
|
||||||
["NOTICE", "restricted: we can't serve DMs to unauthenticated users, does your client implement NIP-42?"]
|
relay: ["AUTH", "<challenge>"]
|
||||||
|
client: ["REQ", "sub_1", {"kinds": [4]}]
|
||||||
|
relay: ["CLOSED", "sub_1", "auth-required: we can't serve DMs to unauthenticated users"]
|
||||||
|
client: ["AUTH", {"id": "abcdef...", ...}]
|
||||||
|
relay: ["OK", "abcdef...", true, ""]
|
||||||
|
client: ["REQ", "sub_1", {"kinds": [4]}]
|
||||||
|
relay: ["EVENT", "sub_1", {...}]
|
||||||
|
relay: ["EVENT", "sub_1", {...}]
|
||||||
|
relay: ["EVENT", "sub_1", {...}]
|
||||||
|
relay: ["EVENT", "sub_1", {...}]
|
||||||
|
...
|
||||||
```
|
```
|
||||||
|
|
||||||
or it can return an `OK` message noting the reason an event was not written using the same prefix:
|
In this case, the `AUTH` message from the relay could be sent right as the client connects or it can be sent immediately before the `CLOSED` is sent. The only requirement is that _the client must have a stored challenge associated with that relay_ so it can act upon that in response to the `auth-required` `CLOSED` message.
|
||||||
|
|
||||||
|
### `auth-required` in response to an `EVENT` message
|
||||||
|
|
||||||
|
The same flow is valid for when a client wants to write an `EVENT` to the relay, except now the relay sends back an `OK` message instead of a `CLOSED` message:
|
||||||
|
|
||||||
```
|
```
|
||||||
["OK", <event-id>, false, "restricted: we do not accept events from unauthenticated users, please sign up at https://example.com/"]
|
relay: ["AUTH", "<challenge>"]
|
||||||
|
client: ["EVENT", {"id": "012345...", ...}]
|
||||||
|
relay: ["OK", "012345...", false, "auth-required: we only accept events from registered users"]
|
||||||
|
client: ["AUTH", {"id": "abcdef...", ...}]
|
||||||
|
relay: ["OK", "abcdef...", true, ""]
|
||||||
|
client: ["EVENT", {"id": "012345...", ...}]
|
||||||
|
relay: ["OK", "012345...", true, ""]
|
||||||
```
|
```
|
||||||
|
|
||||||
## Signed Event Verification
|
## Signed Event Verification
|
||||||
|
|
|
||||||
295
44.md
Normal file
295
44.md
Normal file
|
|
@ -0,0 +1,295 @@
|
||||||
|
NIP-44
|
||||||
|
=====
|
||||||
|
|
||||||
|
Encrypted Payloads (Versioned)
|
||||||
|
------------------------------
|
||||||
|
|
||||||
|
`optional`
|
||||||
|
|
||||||
|
The NIP introduces a new data format for keypair-based encryption. This NIP is versioned
|
||||||
|
to allow multiple algorithm choices to exist simultaneously. This format may be used for
|
||||||
|
many things, but MUST be used in the context of a signed event as described in NIP 01.
|
||||||
|
|
||||||
|
*Note*: this format DOES NOT define any `kind`s related to a new direct messaging standard,
|
||||||
|
only the encryption required to define one. It SHOULD NOT be used as a drop-in replacement
|
||||||
|
for NIP 04 payloads.
|
||||||
|
|
||||||
|
## Versions
|
||||||
|
|
||||||
|
Currently defined encryption algorithms:
|
||||||
|
|
||||||
|
- `0x00` - Reserved
|
||||||
|
- `0x01` - Deprecated and undefined
|
||||||
|
- `0x02` - secp256k1 ECDH, HKDF, padding, ChaCha20, HMAC-SHA256, base64
|
||||||
|
|
||||||
|
## Limitations
|
||||||
|
|
||||||
|
Every nostr user has their own public key, which solves key distribution problems present
|
||||||
|
in other solutions. However, nostr's relay-based architecture makes it difficult to implement
|
||||||
|
more robust private messaging protocols with things like metadata hiding, forward secrecy,
|
||||||
|
and post compromise secrecy.
|
||||||
|
|
||||||
|
The goal of this NIP is to have a _simple_ way to encrypt payloads used in the context of a signed
|
||||||
|
event. When applying this NIP to any use case, it's important to keep in mind your users' threat
|
||||||
|
model and this NIP's limitations. For high-risk situations, users should chat in specialized E2EE
|
||||||
|
messaging software and limit use of nostr to exchanging contacts.
|
||||||
|
|
||||||
|
On its own, messages sent using this scheme have a number of important shortcomings:
|
||||||
|
|
||||||
|
- No deniability: it is possible to prove an event was signed by a particular key
|
||||||
|
- No forward secrecy: when a key is compromised, it is possible to decrypt all previous conversations
|
||||||
|
- No post-compromise security: when a key is compromised, it is possible to decrypt all future conversations
|
||||||
|
- No post-quantum security: a powerful quantum computer would be able to decrypt the messages
|
||||||
|
- IP address leak: user IP may be seen by relays and all intermediaries between user and relay
|
||||||
|
- Date leak: `created_at` is public, since it is a part of NIP 01 event
|
||||||
|
- Limited message size leak: padding only partially obscures true message length
|
||||||
|
- No attachments: they are not supported
|
||||||
|
|
||||||
|
Lack of forward secrecy may be partially mitigated by only sending messages to trusted relays, and asking
|
||||||
|
relays to delete stored messages after a certain duration has elapsed.
|
||||||
|
|
||||||
|
## Version 2
|
||||||
|
|
||||||
|
NIP-44 version 2 has the following design characteristics:
|
||||||
|
|
||||||
|
- Payloads are authenticated using a MAC before signing rather than afterwards because events are assumed
|
||||||
|
to be signed as specified in NIP-01. The outer signature serves to authenticate the full payload, and MUST
|
||||||
|
be validated before decrypting.
|
||||||
|
- ChaCha is used instead of AES because it's faster and has
|
||||||
|
[better security against multi-key attacks](https://datatracker.ietf.org/doc/draft-irtf-cfrg-aead-limits/).
|
||||||
|
- ChaCha is used instead of XChaCha because XChaCha has not been standardized. Also, xChaCha's improved collision
|
||||||
|
resistance of nonces isn't necessary since every message has a new (key, nonce) pair.
|
||||||
|
- HMAC-SHA256 is used instead of Poly1305 because polynomial MACs are much easier to forge.
|
||||||
|
- SHA256 is used instead of SHA3 or BLAKE because it is already used in nostr. Also BLAKE's speed advantage
|
||||||
|
is smaller in non-parallel environments.
|
||||||
|
- A custom padding scheme is used instead of padmé because it provides better leakage reduction for small messages.
|
||||||
|
- Base64 encoding is used instead of another compression algorithm because it is widely available, and is already used in nostr.
|
||||||
|
|
||||||
|
### Encryption
|
||||||
|
|
||||||
|
1. Calculate a conversation key
|
||||||
|
- Execute ECDH (scalar multiplication) of public key B by private key A
|
||||||
|
Output `shared_x` must be unhashed, 32-byte encoded x coordinate of the shared point
|
||||||
|
- Use HKDF-extract with sha256, `IKM=shared_x` and `salt=utf8_encode('nip44-v2')`
|
||||||
|
- HKDF output will be a `conversation_key` between two users.
|
||||||
|
- It is always the same, when key roles are swapped: `conv(a, B) == conv(b, A)`
|
||||||
|
2. Generate a random 32-byte nonce
|
||||||
|
- Always use [CSPRNG](https://en.wikipedia.org/wiki/Cryptographically_secure_pseudorandom_number_generator)
|
||||||
|
- Don't generate a nonce from message content
|
||||||
|
- Don't re-use the same nonce between messages: doing so would make them decryptable,
|
||||||
|
but won't leak the long-term key
|
||||||
|
3. Calculate message keys
|
||||||
|
- The keys are generated from `conversation_key` and `nonce`. Validate that both are 32 bytes long
|
||||||
|
- Use HKDF-expand, with sha256, `PRK=conversation_key`, `info=nonce` and `L=76`
|
||||||
|
- Slice 76-byte HKDF output into: `chacha_key` (bytes 0..32), `chacha_nonce` (bytes 32..44), `hmac_key` (bytes 44..76)
|
||||||
|
4. Add padding
|
||||||
|
- Content must be encoded from UTF-8 into byte array
|
||||||
|
- Validate plaintext length. Minimum is 1 byte, maximum is 65535 bytes
|
||||||
|
- Padding format is: `[plaintext_length: u16][plaintext][zero_bytes]`
|
||||||
|
- Padding algorithm is related to powers-of-two, with min padded msg size of 32
|
||||||
|
- Plaintext length is encoded in big-endian as first 2 bytes of the padded blob
|
||||||
|
5. Encrypt padded content
|
||||||
|
- Use ChaCha20, with key and nonce from step 3
|
||||||
|
6. Calculate MAC (message authentication code)
|
||||||
|
- AAD (additional authenticated data) is used - instead of calculating MAC on ciphertext,
|
||||||
|
it's calculated over a concatenation of `nonce` and `ciphertext`
|
||||||
|
- Validate that AAD (nonce) is 32 bytes
|
||||||
|
7. Base64-encode (with padding) params using `concat(version, nonce, ciphertext, mac)`
|
||||||
|
|
||||||
|
Encrypted payloads MUST be included in an event's payload, hashed, and signed as defined in NIP 01, using schnorr
|
||||||
|
signature scheme over secp256k1.
|
||||||
|
|
||||||
|
### Decryption
|
||||||
|
|
||||||
|
Before decryption, the event's pubkey and signature MUST be validated as defined in NIP 01. The public key MUST be
|
||||||
|
a valid non-zero secp256k1 curve point, and the signature must be valid secp256k1 schnorr signature. For exact
|
||||||
|
validation rules, refer to BIP-340.
|
||||||
|
|
||||||
|
1. Check if first payload's character is `#`
|
||||||
|
- `#` is an optional future-proof flag that means non-base64 encoding is used
|
||||||
|
- The `#` is not present in base64 alphabet, but, instead of throwing `base64 is invalid`,
|
||||||
|
implementations MUST indicate that the encryption version is not yet supported
|
||||||
|
2. Decode base64
|
||||||
|
- Base64 is decoded into `version, nonce, ciphertext, mac`
|
||||||
|
- If the version is unknown, implementations must indicate that the encryption version is not supported
|
||||||
|
- Validate length of base64 message to prevent DoS on base64 decoder: it can be in range from 132 to 87472 chars
|
||||||
|
- Validate length of decoded message to verify output of the decoder: it can be in range from 99 to 65603 bytes
|
||||||
|
3. Calculate conversation key
|
||||||
|
- See step 1 of [encryption](#Encryption)
|
||||||
|
4. Calculate message keys
|
||||||
|
- See step 3 of [encryption](#Encryption)
|
||||||
|
5. Calculate MAC (message authentication code) with AAD and compare
|
||||||
|
- Stop and throw an error if MAC doesn't match the decoded one from step 2
|
||||||
|
- Use constant-time comparison algorithm
|
||||||
|
6. Decrypt ciphertext
|
||||||
|
- Use ChaCha20 with key and nonce from step 3
|
||||||
|
7. Remove padding
|
||||||
|
- Read the first two BE bytes of plaintext that correspond to plaintext length
|
||||||
|
- Verify that the length of sliced plaintext matches the value of the two BE bytes
|
||||||
|
- Verify that calculated padding from step 3 of the [encryption](#Encryption) process matches the actual padding
|
||||||
|
|
||||||
|
### Details
|
||||||
|
|
||||||
|
- Cryptographic methods
|
||||||
|
- `secure_random_bytes(length)` fetches randomness from CSPRNG.
|
||||||
|
- `hkdf(IKM, salt, info, L)` represents HKDF [(RFC 5869)](https://datatracker.ietf.org/doc/html/rfc5869)
|
||||||
|
with SHA256 hash function comprised of methods `hkdf_extract(IKM, salt)` and `hkdf_expand(OKM, info, L)`.
|
||||||
|
- `chacha20(key, nonce, data)` is ChaCha20 [(RFC 8439)](https://datatracker.ietf.org/doc/html/rfc8439) with
|
||||||
|
starting counter set to 0.
|
||||||
|
- `hmac_sha256(key, message)` is HMAC [(RFC 2104)](https://datatracker.ietf.org/doc/html/rfc2104).
|
||||||
|
- `secp256k1_ecdh(priv_a, pub_b)` is multiplication of point B by scalar a (`a ⋅ B`), defined in
|
||||||
|
[BIP340](https://github.com/bitcoin/bips/blob/e918b50731397872ad2922a1b08a5a4cd1d6d546/bip-0340.mediawiki).
|
||||||
|
The operation produces a shared point, and we encode the shared point's 32-byte x coordinate, using method
|
||||||
|
`bytes(P)` from BIP340. Private and public keys must be validated as per BIP340: pubkey must be a valid,
|
||||||
|
on-curve point, and private key must be a scalar in range `[1, secp256k1_order - 1]`.
|
||||||
|
- Operators
|
||||||
|
- `x[i:j]`, where `x` is a byte array and `i, j <= 0` returns a `(j - i)`-byte array with a copy of the
|
||||||
|
`i`-th byte (inclusive) to the `j`-th byte (exclusive) of `x`.
|
||||||
|
- Constants `c`:
|
||||||
|
- `min_plaintext_size` is 1. 1b msg is padded to 32b.
|
||||||
|
- `max_plaintext_size` is 65535 (64kb - 1). It is padded to 65536.
|
||||||
|
- Functions
|
||||||
|
- `base64_encode(string)` and `base64_decode(bytes)` are Base64 ([RFC 4648](https://datatracker.ietf.org/doc/html/rfc4648), with padding)
|
||||||
|
- `concat` refers to byte array concatenation
|
||||||
|
- `is_equal_ct(a, b)` is constant-time equality check of 2 byte arrays
|
||||||
|
- `utf8_encode(string)` and `utf8_decode(bytes)` transform string to byte array and back
|
||||||
|
- `write_u8(number)` restricts number to values 0..255 and encodes into Big-Endian uint8 byte array
|
||||||
|
- `write_u16_be(number)` restricts number to values 0..65535 and encodes into Big-Endian uint16 byte array
|
||||||
|
- `zeros(length)` creates byte array of length `length >= 0`, filled with zeros
|
||||||
|
- `floor(number)` and `log2(number)` are well-known mathematical methods
|
||||||
|
|
||||||
|
### Implementation pseudocode
|
||||||
|
|
||||||
|
The following is a collection of python-like pseudocode functions which implement the above primitives,
|
||||||
|
intended to guide implementers. A collection of implementations in different languages is available at https://github.com/paulmillr/nip44.
|
||||||
|
|
||||||
|
```py
|
||||||
|
# Calculates length of the padded byte array.
|
||||||
|
def calc_padded_len(unpadded_len):
|
||||||
|
next_power = 1 << (floor(log2(unpadded_len - 1))) + 1
|
||||||
|
if next_power <= 256:
|
||||||
|
chunk = 32
|
||||||
|
else:
|
||||||
|
chunk = next_power / 8
|
||||||
|
if unpadded_len <= 32:
|
||||||
|
return 32
|
||||||
|
else:
|
||||||
|
return chunk * (floor((len - 1) / chunk) + 1)
|
||||||
|
|
||||||
|
# Converts unpadded plaintext to padded bytearray
|
||||||
|
def pad(plaintext):
|
||||||
|
unpadded = utf8_encode(plaintext)
|
||||||
|
unpadded_len = len(plaintext)
|
||||||
|
if (unpadded_len < c.min_plaintext_size or
|
||||||
|
unpadded_len > c.max_plaintext_size): raise Exception('invalid plaintext length')
|
||||||
|
prefix = write_u16_be(unpadded_len)
|
||||||
|
suffix = zeros(calc_padded_len(unpadded_len) - unpadded_len)
|
||||||
|
return concat(prefix, unpadded, suffix)
|
||||||
|
|
||||||
|
# Converts padded bytearray to unpadded plaintext
|
||||||
|
def unpad(padded):
|
||||||
|
unpadded_len = read_uint16_be(padded[0:2])
|
||||||
|
unpadded = padded[2:2+unpadded_len]
|
||||||
|
if (unpadded_len == 0 or
|
||||||
|
len(unpadded) != unpadded_len or
|
||||||
|
len(padded) != 2 + calc_padded_len(unpadded_len)): raise Exception('invalid padding')
|
||||||
|
return utf8_decode(unpadded)
|
||||||
|
|
||||||
|
# metadata: always 65b (version: 1b, nonce: 32b, max: 32b)
|
||||||
|
# plaintext: 1b to 0xffff
|
||||||
|
# padded plaintext: 32b to 0xffff
|
||||||
|
# ciphertext: 32b+2 to 0xffff+2
|
||||||
|
# raw payload: 99 (65+32+2) to 65603 (65+0xffff+2)
|
||||||
|
# compressed payload (base64): 132b to 87472b
|
||||||
|
def decode_payload(payload):
|
||||||
|
plen = len(payload)
|
||||||
|
if plen == 0 or payload[0] == '#': raise Exception('unknown version')
|
||||||
|
if plen < 132 or plen > 87472: raise Exception('invalid payload size')
|
||||||
|
data = base64_decode(payload)
|
||||||
|
dlen = len(d)
|
||||||
|
if dlen < 99 or dlen > 65603: raise Exception('invalid data size');
|
||||||
|
vers = data[0]
|
||||||
|
if vers != 2: raise Exception('unknown version ' + vers)
|
||||||
|
nonce = data[1:33]
|
||||||
|
ciphertext = data[33:dlen - 32]
|
||||||
|
mac = data[dlen - 32:dlen]
|
||||||
|
return (nonce, ciphertext, mac)
|
||||||
|
|
||||||
|
def hmac_aad(key, message, aad):
|
||||||
|
if len(aad) != 32: raise Exception('AAD associated data must be 32 bytes');
|
||||||
|
return hmac(sha256, key, concat(aad, message));
|
||||||
|
|
||||||
|
# Calculates long-term key between users A and B: `get_key(Apriv, Bpub) == get_key(Bpriv, Apub)`
|
||||||
|
def get_conversation_key(private_key_a, public_key_b):
|
||||||
|
shared_x = secp256k1_ecdh(private_key_a, public_key_b)
|
||||||
|
return hkdf_extract(IKM=shared_x, salt=utf8_encode('nip44-v2'))
|
||||||
|
|
||||||
|
# Calculates unique per-message key
|
||||||
|
def get_message_keys(conversation_key, nonce):
|
||||||
|
if len(conversation_key) != 32: raise Exception('invalid conversation_key length')
|
||||||
|
if len(nonce) != 32: raise Exception('invalid nonce length')
|
||||||
|
keys = hkdf_expand(OKM=conversation_key, info=nonce, L=76)
|
||||||
|
chacha_key = keys[0:32]
|
||||||
|
chacha_nonce = keys[32:44]
|
||||||
|
hmac_key = keys[44:76]
|
||||||
|
return (chacha_key, chacha_nonce, hmac_key)
|
||||||
|
|
||||||
|
def encrypt(plaintext, conversation_key, nonce):
|
||||||
|
(chacha_key, chacha_nonce, hmac_key) = get_message_keys(conversation_key, nonce)
|
||||||
|
padded = pad(plaintext)
|
||||||
|
ciphertext = chacha20(key=chacha_key, nonce=chacha_nonce, data=padded)
|
||||||
|
mac = hmac_aad(key=hmac_key, message=ciphertext, aad=nonce)
|
||||||
|
return base64_encode(concat(write_u8(2), nonce, ciphertext, mac))
|
||||||
|
|
||||||
|
def decrypt(payload, conversation_key):
|
||||||
|
(nonce, ciphertext, mac) = decode_payload(payload)
|
||||||
|
(chacha_key, chacha_nonce, hmac_key) = get_message_keys(conversation_key, nonce)
|
||||||
|
calculated_mac = hmac_aad(key=hmac_key, message=ciphertext, aad=nonce)
|
||||||
|
if not is_equal_ct(calculated_mac, mac): raise Exception('invalid MAC')
|
||||||
|
padded_plaintext = chacha20(key=chacha_key, nonce=chacha_nonce, data=ciphertext)
|
||||||
|
return unpad(padded_plaintext)
|
||||||
|
|
||||||
|
# Usage:
|
||||||
|
# conversation_key = get_conversation_key(sender_privkey, recipient_pubkey)
|
||||||
|
# nonce = secure_random_bytes(32)
|
||||||
|
# payload = encrypt('hello world', conversation_key, nonce)
|
||||||
|
# 'hello world' == decrypt(payload, conversation_key)
|
||||||
|
```
|
||||||
|
|
||||||
|
### Audit
|
||||||
|
|
||||||
|
The v2 of the standard was audited by [Cure53](https://cure53.de) in December 2023.
|
||||||
|
Check out [audit-2023.12.pdf](https://github.com/paulmillr/nip44/blob/ce63c2eaf345e9f7f93b48f829e6bdeb7e7d7964/audit-2023.12.pdf)
|
||||||
|
and [auditor's website](https://cure53.de/audit-report_nip44-implementations.pdf).
|
||||||
|
|
||||||
|
### Tests and code
|
||||||
|
|
||||||
|
A collection of implementations in different languages is available at https://github.com/paulmillr/nip44.
|
||||||
|
|
||||||
|
We publish extensive test vectors. Instead of having it in the document directly, a sha256 checksum of vectors is provided:
|
||||||
|
|
||||||
|
269ed0f69e4c192512cc779e78c555090cebc7c785b609e338a62afc3ce25040 nip44.vectors.json
|
||||||
|
|
||||||
|
Example of a test vector from the file:
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"sec1": "0000000000000000000000000000000000000000000000000000000000000001",
|
||||||
|
"sec2": "0000000000000000000000000000000000000000000000000000000000000002",
|
||||||
|
"conversation_key": "c41c775356fd92eadc63ff5a0dc1da211b268cbea22316767095b2871ea1412d",
|
||||||
|
"nonce": "0000000000000000000000000000000000000000000000000000000000000001",
|
||||||
|
"plaintext": "a",
|
||||||
|
"payload": "AgAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAABee0G5VSK0/9YypIObAtDKfYEAjD35uVkHyB0F4DwrcNaCXlCWZKaArsGrY6M9wnuTMxWfp1RTN9Xga8no+kF5Vsb"
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
The file also contains intermediate values. A quick guidance with regards to its usage:
|
||||||
|
|
||||||
|
- `valid.get_conversation_key`: calculate conversation_key from secret key sec1 and public key pub2
|
||||||
|
- `valid.get_message_keys`: calculate chacha_key, chacha_nonce, hmac_key from conversation_key and nonce
|
||||||
|
- `valid.calc_padded_len`: take unpadded length (first value), calculate padded length (second value)
|
||||||
|
- `valid.encrypt_decrypt`: emulate real conversation. Calculate pub2 from sec2, verify conversation_key from (sec1, pub2), encrypt, verify payload, then calculate pub1 from sec1, verify conversation_key from (sec2, pub1), decrypt, verify plaintext.
|
||||||
|
- `valid.encrypt_decrypt_long_msg`: same as previous step, but instead of a full plaintext and payload, their checksum is provided.
|
||||||
|
- `invalid.encrypt_msg_lengths`
|
||||||
|
- `invalid.get_conversation_key`: calculating conversation_key must throw an error
|
||||||
|
- `invalid.decrypt`: decrypting message content must throw an error
|
||||||
35
45.md
35
45.md
|
|
@ -4,7 +4,7 @@ NIP-45
|
||||||
Event Counts
|
Event Counts
|
||||||
--------------
|
--------------
|
||||||
|
|
||||||
`draft` `optional` `author:staab`
|
`draft` `optional`
|
||||||
|
|
||||||
Relays may support the verb `COUNT`, which provides a mechanism for obtaining event counts.
|
Relays may support the verb `COUNT`, which provides a mechanism for obtaining event counts.
|
||||||
|
|
||||||
|
|
@ -16,24 +16,45 @@ Some queries a client may want to execute against connected relays are prohibiti
|
||||||
|
|
||||||
This NIP defines the verb `COUNT`, which accepts a subscription id and filters as specified in [NIP 01](01.md) for the verb `REQ`. Multiple filters are OR'd together and aggregated into a single count result.
|
This NIP defines the verb `COUNT`, which accepts a subscription id and filters as specified in [NIP 01](01.md) for the verb `REQ`. Multiple filters are OR'd together and aggregated into a single count result.
|
||||||
|
|
||||||
```
|
```json
|
||||||
["COUNT", <subscription_id>, <filters JSON>...]
|
["COUNT", <subscription_id>, <filters JSON>...]
|
||||||
```
|
```
|
||||||
|
|
||||||
Counts are returned using a `COUNT` response in the form `{"count": <integer>}`. Relays may use probabilistic counts to reduce compute requirements.
|
Counts are returned using a `COUNT` response in the form `{"count": <integer>}`. Relays may use probabilistic counts to reduce compute requirements.
|
||||||
|
In case a relay uses probabilistic counts, it MAY indicate it in the response with `approximate` key i.e. `{"count": <integer>, "approximate": <true|false>}`.
|
||||||
|
|
||||||
```
|
```json
|
||||||
["COUNT", <subscription_id>, {"count": <integer>}]
|
["COUNT", <subscription_id>, {"count": <integer>}]
|
||||||
```
|
```
|
||||||
|
|
||||||
Examples:
|
Whenever the relay decides to refuse to fulfill the `COUNT` request, it MUST return a `CLOSED` message.
|
||||||
|
|
||||||
```
|
## Examples
|
||||||
# Followers count
|
|
||||||
|
### Followers count
|
||||||
|
|
||||||
|
```json
|
||||||
["COUNT", <subscription_id>, {"kinds": [3], "#p": [<pubkey>]}]
|
["COUNT", <subscription_id>, {"kinds": [3], "#p": [<pubkey>]}]
|
||||||
["COUNT", <subscription_id>, {"count": 238}]
|
["COUNT", <subscription_id>, {"count": 238}]
|
||||||
|
```
|
||||||
|
|
||||||
# Count posts and reactions
|
### Count posts and reactions
|
||||||
|
|
||||||
|
```json
|
||||||
["COUNT", <subscription_id>, {"kinds": [1, 7], "authors": [<pubkey>]}]
|
["COUNT", <subscription_id>, {"kinds": [1, 7], "authors": [<pubkey>]}]
|
||||||
["COUNT", <subscription_id>, {"count": 5}]
|
["COUNT", <subscription_id>, {"count": 5}]
|
||||||
```
|
```
|
||||||
|
|
||||||
|
### Count posts approximately
|
||||||
|
|
||||||
|
```
|
||||||
|
["COUNT", <subscription_id>, {"kinds": [1]}]
|
||||||
|
["COUNT", <subscription_id>, {"count": 93412452, "approximate": true}]
|
||||||
|
```
|
||||||
|
|
||||||
|
### Relay refuses to count
|
||||||
|
|
||||||
|
```
|
||||||
|
["COUNT", <subscription_id>, {"kinds": [4], "authors": [<pubkey>], "#p": [<pubkey>]}]
|
||||||
|
["CLOSED", <subscription_id>, "auth-required: cannot count other people's DMs"]
|
||||||
|
```
|
||||||
|
|
|
||||||
279
46.md
279
46.md
|
|
@ -1,162 +1,227 @@
|
||||||
NIP-46
|
# NIP-46 - Nostr Remote Signing
|
||||||
======
|
|
||||||
|
|
||||||
Nostr Connect
|
|
||||||
------------------------
|
|
||||||
|
|
||||||
`draft` `optional` `author:tiero` `author:giowe` `author:vforvalerio87`
|
|
||||||
|
|
||||||
## Rationale
|
## Rationale
|
||||||
|
|
||||||
Private keys should be exposed to as few systems - apps, operating systems, devices - as possible as each system adds to the attack surface.
|
Private keys should be exposed to as few systems - apps, operating systems, devices - as possible as each system adds to the attack surface.
|
||||||
|
|
||||||
Entering private keys can also be annoying and requires exposing them to even more systems such as the operating system's clipboard that might be monitored by malicious apps.
|
This NIP describes a method for 2-way communication between a remote signer and a Nostr client. The remote signer could be, for example, a hardware device dedicated to signing Nostr events, while the client is a normal Nostr client.
|
||||||
|
|
||||||
|
## Terminology
|
||||||
|
|
||||||
## Terms
|
- **Local keypair**: A local public and private key-pair used to encrypt content and communicate with the remote signer. Usually created by the client application.
|
||||||
|
- **Remote user pubkey**: The public key that the user wants to sign as. The remote signer has control of the private key that matches this public key.
|
||||||
|
- **Remote signer pubkey**: This is the public key of the remote signer itself. This is needed in both `create_account` command because you don't yet have a remote user pubkey.
|
||||||
|
|
||||||
* **App**: Nostr app on any platform that *requires* to act on behalf of a nostr account.
|
All pubkeys specified in this NIP are in hex format.
|
||||||
* **Signer**: Nostr app that holds the private key of a nostr account and *can sign* on its behalf.
|
|
||||||
|
|
||||||
|
## Initiating a connection
|
||||||
|
|
||||||
## `TL;DR`
|
To initiate a connection between a client and a remote signer there are a few different options.
|
||||||
|
|
||||||
|
### Direct connection initiated by remote signer
|
||||||
|
|
||||||
**App** and **Signer** sends ephemeral encrypted messages to each other using kind `24133`, using a relay of choice.
|
This is most common in a situation where you have your own nsecbunker or other type of remote signer and want to connect through a client that supports remote signing.
|
||||||
|
|
||||||
App prompts the Signer to do things such as fetching the public key or signing events.
|
The remote signer would provide a connection token in the form:
|
||||||
|
|
||||||
The `content` field must be an encrypted JSONRPC-ish **request** or **response**.
|
```
|
||||||
|
bunker://<remote-user-pubkey>?relay=<wss://relay-to-connect-on>&relay=<wss://another-relay-to-connect-on>&secret=<optional-secret-value>
|
||||||
|
```
|
||||||
|
|
||||||
## Signer Protocol
|
This token is pasted into the client by the user and the client then uses the details to connect to the remote signer via the specified relay(s).
|
||||||
|
|
||||||
### Messages
|
### Direct connection initiated by the client
|
||||||
|
|
||||||
#### Request
|
In this case, basically the opposite direction of the first case, the client provides a connection token (or encodes the token in a QR code) and the signer initiates a connection to the client via the specified relay(s).
|
||||||
|
|
||||||
|
```
|
||||||
|
nostrconnect://<local-keypair-pubkey>?relay=<wss://relay-to-connect-on>&metadata=<json metadata in the form: {"name":"...", "url": "...", "description": "..."}>
|
||||||
|
```
|
||||||
|
|
||||||
|
## The flow
|
||||||
|
|
||||||
|
1. Client creates a local keypair. This keypair doesn't need to be communicated to the user since it's largely disposable (i.e. the user doesn't need to see this pubkey). Clients might choose to store it locally and they should delete it when the user logs out.
|
||||||
|
2. Client gets the remote user pubkey (either via a `bunker://` connection string or a NIP-05 login-flow; shown below)
|
||||||
|
3. Clients use the local keypair to send requests to the remote signer by `p`-tagging and encrypting to the remote user pubkey.
|
||||||
|
4. The remote signer responds to the client by `p`-tagging and encrypting to the local keypair pubkey.
|
||||||
|
|
||||||
|
### Example flow for signing an event
|
||||||
|
|
||||||
|
- Remote user pubkey (e.g. signing as) `fa984bd7dbb282f07e16e7ae87b26a2a7b9b90b7246a44771f0cf5ae58018f52`
|
||||||
|
- Local pubkey is `eff37350d839ce3707332348af4549a96051bd695d3223af4aabce4993531d86`
|
||||||
|
|
||||||
|
#### Signature request
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"kind": 24133,
|
||||||
|
"pubkey": "eff37350d839ce3707332348af4549a96051bd695d3223af4aabce4993531d86",
|
||||||
|
"content": nip04({
|
||||||
|
"id": <random_string>,
|
||||||
|
"method": "sign_event",
|
||||||
|
"params": [json_stringified(<{
|
||||||
|
content: "Hello, I'm signing remotely",
|
||||||
|
kind: 1,
|
||||||
|
tags: [],
|
||||||
|
created_at: 1714078911
|
||||||
|
}>)]
|
||||||
|
}),
|
||||||
|
"tags": [["p", "fa984bd7dbb282f07e16e7ae87b26a2a7b9b90b7246a44771f0cf5ae58018f52"]], // p-tags the remote user pubkey
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
#### Response event
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"kind": 24133,
|
||||||
|
"pubkey": "fa984bd7dbb282f07e16e7ae87b26a2a7b9b90b7246a44771f0cf5ae58018f52",
|
||||||
|
"content": nip04({
|
||||||
|
"id": <random_string>,
|
||||||
|
"result": json_stringified(<signed-event>)
|
||||||
|
}),
|
||||||
|
"tags": [["p", "eff37350d839ce3707332348af4549a96051bd695d3223af4aabce4993531d86"]], // p-tags the local keypair pubkey
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
#### Diagram
|
||||||
|
|
||||||
|

|
||||||
|
|
||||||
|
## Request Events `kind: 24133`
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"id": <id>,
|
||||||
|
"kind": 24133,
|
||||||
|
"pubkey": <local_keypair_pubkey>,
|
||||||
|
"content": <nip04(<request>)>,
|
||||||
|
"tags": [["p", <remote_user_pubkey>]], // NB: in the `create_account` event, the remote signer pubkey should be `p` tagged.
|
||||||
|
"created_at": <unix timestamp in seconds>
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
The `content` field is a JSON-RPC-like message that is [NIP-04](https://github.com/nostr-protocol/nips/blob/master/04.md) encrypted and has the following structure:
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"id": <random_string>,
|
"id": <random_string>,
|
||||||
"method": <one_of_the_methods>,
|
"method": <method_name>,
|
||||||
"params": [<anything>, <else>]
|
"params": [array_of_strings]
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
#### Response
|
- `id` is a random string that is a request ID. This same ID will be sent back in the response payload.
|
||||||
|
- `method` is the name of the method/command (detailed below).
|
||||||
|
- `params` is a positional array of string parameters.
|
||||||
|
|
||||||
|
### Methods/Commands
|
||||||
|
|
||||||
|
Each of the following are methods that the client sends to the remote signer.
|
||||||
|
|
||||||
|
| Command | Params | Result |
|
||||||
|
| ------------------------ | ------------------------------------------------- | ---------------------------------------------------------------------- |
|
||||||
|
| `connect` | `[<remote_user_pubkey>, <optional_secret>, <optional_requested_permissions>]` | "ack" |
|
||||||
|
| `sign_event` | `[<{kind, content, tags, created_at}>]` | `json_stringified(<signed_event>)` |
|
||||||
|
| `ping` | `[]` | "pong" |
|
||||||
|
| `get_relays` | `[]` | `json_stringified({<relay_url>: {read: <boolean>, write: <boolean>}})` |
|
||||||
|
| `get_public_key` | `[]` | `<hex-pubkey>` |
|
||||||
|
| `nip04_encrypt` | `[<third_party_pubkey>, <plaintext_to_encrypt>]` | `<nip04_ciphertext>` |
|
||||||
|
| `nip04_decrypt` | `[<third_party_pubkey>, <nip04_ciphertext_to_decrypt>]` | `<plaintext>` |
|
||||||
|
| `nip44_encrypt` | `[<third_party_pubkey>, <plaintext_to_encrypt>]` | `<nip44_ciphertext>` |
|
||||||
|
| `nip44_decrypt` | `[<third_party_pubkey>, <nip44_ciphertext_to_decrypt>]` | `<plaintext>` |
|
||||||
|
|
||||||
|
### Requested permissions
|
||||||
|
|
||||||
|
The `connect` method may be provided with `optional_requested_permissions` for user convenience. The permissions are a comma-separated list of `method[:params]`, i.e. `nip04_encrypt,sign_event:4` meaning permissions to call `nip04_encrypt` and to call `sign_event` with `kind:4`. Optional parameter for `sign_event` is the kind number, parameters for other methods are to be defined later.
|
||||||
|
|
||||||
|
## Response Events `kind:24133`
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"id": <id>,
|
||||||
|
"kind": 24133,
|
||||||
|
"pubkey": <remote_signer_pubkey>,
|
||||||
|
"content": <nip04(<response>)>,
|
||||||
|
"tags": [["p", <local_keypair_pubkey>]],
|
||||||
|
"created_at": <unix timestamp in seconds>
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
The `content` field is a JSON-RPC-like message that is [NIP-04](https://github.com/nostr-protocol/nips/blob/master/04.md) encrypted and has the following structure:
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"id": <request_id>,
|
"id": <request_id>,
|
||||||
"result": <anything>,
|
"result": <results_string>,
|
||||||
"error": <reason>
|
"error": <optional_error_string>
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
### Methods
|
- `id` is the request ID that this response is for.
|
||||||
|
- `results` is a string of the result of the call (this can be either a string or a JSON stringified object)
|
||||||
|
- `error`, _optionally_, it is an error in string form, if any. Its presence indicates an error with the request.
|
||||||
|
|
||||||
|
### Auth Challenges
|
||||||
|
|
||||||
#### Mandatory
|
An Auth Challenge is a response that a remote signer can send back when it needs the user to authenticate via other means. This is currently used in the OAuth-like flow enabled by signers like [Nsecbunker](https://github.com/kind-0/nsecbunkerd/). The response `content` object will take the following form:
|
||||||
|
|
||||||
These are mandatory methods the remote signer app MUST implement:
|
```json
|
||||||
|
{
|
||||||
- **describe**
|
"id": <request_id>,
|
||||||
- params []
|
"result": "auth_url",
|
||||||
- result `["describe", "get_public_key", "sign_event", "connect", "disconnect", "delegate", ...]`
|
"error": <URL_to_display_to_end_user>
|
||||||
- **get_public_key**
|
}
|
||||||
- params []
|
|
||||||
- result `pubkey`
|
|
||||||
- **sign_event**
|
|
||||||
- params [`event`]
|
|
||||||
- result `event_with_signature`
|
|
||||||
|
|
||||||
#### optional
|
|
||||||
|
|
||||||
|
|
||||||
- **connect**
|
|
||||||
- params [`pubkey`]
|
|
||||||
- **disconnect**
|
|
||||||
- params []
|
|
||||||
- **delegate**
|
|
||||||
- params [`delegatee`, `{ kind: number, since: number, until: number }`]
|
|
||||||
- result `{ from: string, to: string, cond: string, sig: string }`
|
|
||||||
- **get_relays**
|
|
||||||
- params []
|
|
||||||
- result `{ [url: string]: {read: boolean, write: boolean} }`
|
|
||||||
- **nip04_encrypt**
|
|
||||||
- params [`pubkey`, `plaintext`]
|
|
||||||
- result `nip4 ciphertext`
|
|
||||||
- **nip04_decrypt**
|
|
||||||
- params [`pubkey`, `nip4 ciphertext`]
|
|
||||||
- result [`plaintext`]
|
|
||||||
|
|
||||||
|
|
||||||
NOTICE: `pubkey` and `signature` are hex-encoded strings.
|
|
||||||
|
|
||||||
|
|
||||||
### Nostr Connect URI
|
|
||||||
|
|
||||||
**Signer** discovers **App** by scanning a QR code, clicking on a deep link or copy-pasting an URI.
|
|
||||||
|
|
||||||
The **App** generates a special URI with prefix `nostrconnect://` and base path the hex-encoded `pubkey` with the following querystring parameters **URL encoded**
|
|
||||||
|
|
||||||
- `relay` URL of the relay of choice where the **App** is connected and the **Signer** must send and listen for messages.
|
|
||||||
- `metadata` metadata JSON of the **App**
|
|
||||||
- `name` human-readable name of the **App**
|
|
||||||
- `url` (optional) URL of the website requesting the connection
|
|
||||||
- `description` (optional) description of the **App**
|
|
||||||
- `icons` (optional) array of URLs for icons of the **App**.
|
|
||||||
|
|
||||||
#### JavaScript
|
|
||||||
|
|
||||||
```js
|
|
||||||
const uri = `nostrconnect://<pubkey>?relay=${encodeURIComponent("wss://relay.damus.io")}&metadata=${encodeURIComponent(JSON.stringify({"name": "Example"}))}`
|
|
||||||
```
|
```
|
||||||
|
|
||||||
#### Example
|
Clients should display (in a popup or new tab) the URL from the `error` field and then subscribe/listen for another response from the remote signer (reusing the same request ID). This event will be sent once the user authenticates in the other window (or will never arrive if the user doesn't authenticate). It's also possible to add a `redirect_uri` url parameter to the auth_url, which is helpful in situations when a client cannot open a new window or tab to display the auth challenge.
|
||||||
```sh
|
|
||||||
nostrconnect://b889ff5b1513b641e2a139f661a661364979c5beee91842f8f0ef42ab558e9d4?relay=wss%3A%2F%2Frelay.damus.io&metadata=%7B%22name%22%3A%22Example%22%7D
|
|
||||||
```
|
|
||||||
|
|
||||||
|
#### Example event signing request with auth challenge
|
||||||
|
|
||||||
|
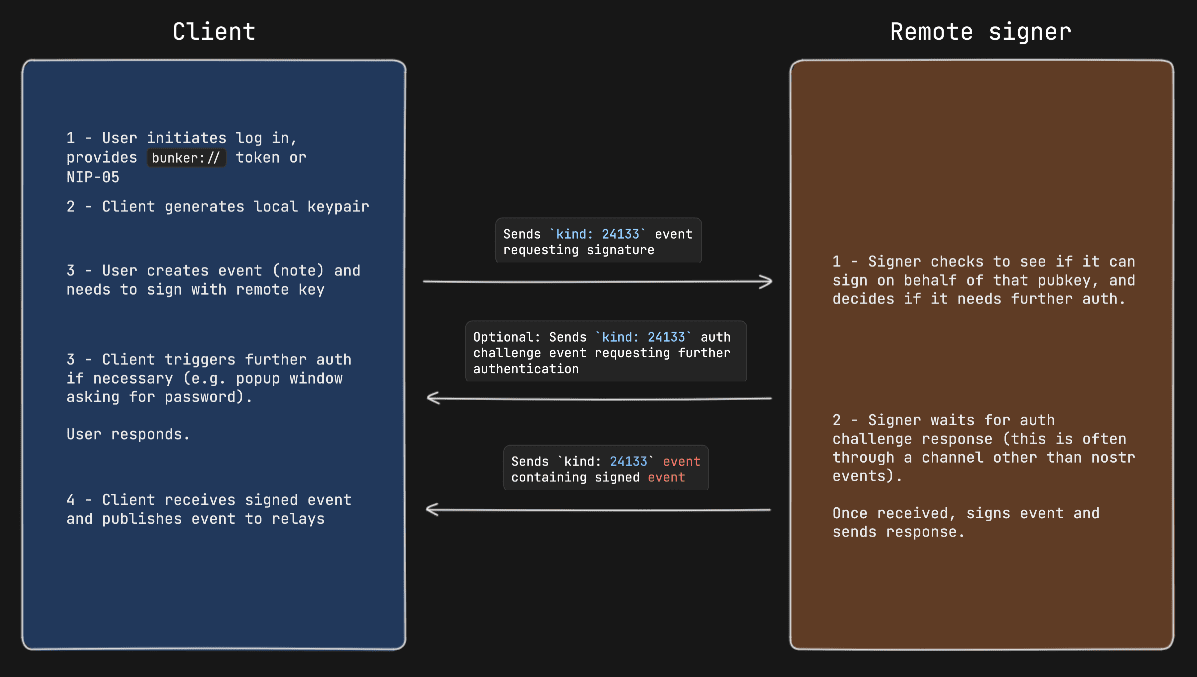
|
||||||
|
|
||||||
## Flows
|
## Remote Signer Commands
|
||||||
|
|
||||||
The `content` field contains encrypted message as specified by [NIP04](https://github.com/nostr-protocol/nips/blob/master/04.md). The `kind` chosen is `24133`.
|
Remote signers might support additional commands when communicating directly with it. These commands follow the same flow as noted above, the only difference is that when the client sends a request event, the `p`-tag is the pubkey of the remote signer itself and the `content` payload is encrypted to the same remote signer pubkey.
|
||||||
|
|
||||||
### Connect
|
### Methods/Commands
|
||||||
|
|
||||||
1. User clicks on **"Connect"** button on a website or scan it with a QR code
|
Each of the following are methods that the client sends to the remote signer.
|
||||||
2. It will show an URI to open a "nostr connect" enabled **Signer**
|
|
||||||
3. In the URI there is a pubkey of the **App** ie. `nostrconnect://<pubkey>&relay=<relay>&metadata=<metadata>`
|
|
||||||
4. The **Signer** will send a message to ACK the `connect` request, along with his public key
|
|
||||||
|
|
||||||
### Disconnect (from App)
|
| Command | Params | Result |
|
||||||
|
| ---------------- | ------------------------------------------ | ------------------------------------ |
|
||||||
|
| `create_account` | `[<username>, <domain>, <optional_email>, <optional_requested_permissions>]` | `<newly_created_remote_user_pubkey>` |
|
||||||
|
|
||||||
1. User clicks on **"Disconnect"** button on the **App**
|
## Appendix
|
||||||
2. The **App** will send a message to the **Signer** with a `disconnect` request
|
|
||||||
3. The **Signer** will send a message to ACK the `disconnect` request
|
|
||||||
|
|
||||||
### Disconnect (from Signer)
|
### NIP-05 Login Flow
|
||||||
|
|
||||||
1. User clicks on **"Disconnect"** button on the **Signer**
|
Clients might choose to present a more familiar login flow, so users can type a NIP-05 address instead of a `bunker://` string.
|
||||||
2. The **Signer** will send a message to the **App** with a `disconnect` request
|
|
||||||
|
|
||||||
|
When the user types a NIP-05 the client:
|
||||||
|
|
||||||
### Get Public Key
|
- Queries the `/.well-known/nostr.json` file from the domain for the NIP-05 address provided to get the user's pubkey (this is the **remote user pubkey**)
|
||||||
|
- In the same `/.well-known/nostr.json` file, queries for the `nip46` key to get the relays that the remote signer will be listening on.
|
||||||
|
- Now the client has enough information to send commands to the remote signer on behalf of the user.
|
||||||
|
|
||||||
1. The **App** will send a message to the **Signer** with a `get_public_key` request
|
### OAuth-like Flow
|
||||||
3. The **Signer** will send back a message with the public key as a response to the `get_public_key` request
|
|
||||||
|
|
||||||
### Sign Event
|
#### Remote signer discovery via NIP-89
|
||||||
|
|
||||||
1. The **App** will send a message to the **Signer** with a `sign_event` request along with the **event** to be signed
|
In this last case, most often used to facilitate an OAuth-like signin flow, the client first looks for remote signers that have announced themselves via NIP-89 application handler events.
|
||||||
2. The **Signer** will show a popup to the user to inspect the event and sign it
|
|
||||||
3. The **Signer** will send back a message with the event including the `id` and the schnorr `signature` as a response to the `sign_event` request
|
|
||||||
|
|
||||||
### Delegate
|
First the client will query for `kind: 31990` events that have a `k` tag of `24133`.
|
||||||
|
|
||||||
1. The **App** will send a message with metadata to the **Signer** with a `delegate` request along with the **conditions** query string and the **pubkey** of the **App** to be delegated.
|
These are generally shown to a user, and once the user selects which remote signer to use and provides the remote user pubkey they want to use (via npub, pubkey, or nip-05 value), the client can initiate a connection. Note that it's on the user to select the remote signer that is actually managing the remote key that they would like to use in this case. If the remote user pubkey is managed on another remote signer, the connection will fail.
|
||||||
2. The **Signer** will show a popup to the user to delegate the **App** to sign on his behalf
|
|
||||||
3. The **Signer** will send back a message with the signed [NIP-26 delegation token](https://github.com/nostr-protocol/nips/blob/master/26.md) or reject it
|
|
||||||
|
|
||||||
|
In addition, it's important that clients validate that the pubkey of the announced remote signer matches the pubkey of the `_` entry in the `/.well-known/nostr.json` file of the remote signer's announced domain.
|
||||||
|
|
||||||
|
Clients that allow users to create new accounts should also consider validating the availability of a given username in the namespace of remote signer's domain by checking the `/.well-known/nostr.json` file for existing usernames. Clients can then show users feedback in the UI before sending a `create_account` event to the remote signer and receiving an error in return. Ideally, remote signers would also respond with understandable error messages if a client tries to create an account with an existing username.
|
||||||
|
|
||||||
|
#### Example Oauth-like flow to create a new user account with Nsecbunker
|
||||||
|
|
||||||
|
Coming soon...
|
||||||
|
|
||||||
|
## References
|
||||||
|
|
||||||
|
- [NIP-04 - Encryption](https://github.com/nostr-protocol/nips/blob/master/04.md)
|
||||||
|
|
|
||||||
288
47.md
288
47.md
|
|
@ -4,7 +4,7 @@ NIP-47
|
||||||
Nostr Wallet Connect
|
Nostr Wallet Connect
|
||||||
--------------------
|
--------------------
|
||||||
|
|
||||||
`draft` `optional` `author:kiwiidb` `author:bumi` `author:semisol` `author:vitorpamplona`
|
`draft` `optional`
|
||||||
|
|
||||||
## Rationale
|
## Rationale
|
||||||
|
|
||||||
|
|
@ -17,7 +17,7 @@ This NIP describes a way for clients to access a remote Lightning wallet through
|
||||||
* **wallet service**: Nostr app that typically runs on an always-on computer (eg. in the cloud or on a Raspberry Pi). This app has access to the APIs of the wallets it serves.
|
* **wallet service**: Nostr app that typically runs on an always-on computer (eg. in the cloud or on a Raspberry Pi). This app has access to the APIs of the wallets it serves.
|
||||||
|
|
||||||
## Theory of Operation
|
## Theory of Operation
|
||||||
1. **Users** who which to use this NIP to send lightning payments to other nostr users must first acquire a special "connection" URI from their NIP-47 compliant wallet application. The wallet application may provide this URI using a QR screen, or a pasteable string, or some other means.
|
1. **Users** who wish to use this NIP to send lightning payments to other nostr users must first acquire a special "connection" URI from their NIP-47 compliant wallet application. The wallet application may provide this URI using a QR screen, or a pasteable string, or some other means.
|
||||||
|
|
||||||
2. The **user** should then copy this URI into their **client(s)** by pasting, or scanning the QR, etc. The **client(s)** should save this URI and use it later whenever the **user** makes a payment. The **client** should then request an `info` (13194) event from the relay(s) specified in the URI. The **wallet service** will have sent that event to those relays earlier, and the relays will hold it as a replaceable event.
|
2. The **user** should then copy this URI into their **client(s)** by pasting, or scanning the QR, etc. The **client(s)** should save this URI and use it later whenever the **user** makes a payment. The **client** should then request an `info` (13194) event from the relay(s) specified in the URI. The **wallet service** will have sent that event to those relays earlier, and the relays will hold it as a replaceable event.
|
||||||
|
|
||||||
|
|
@ -36,6 +36,7 @@ The info event should be a replaceable event that is published by the **wallet s
|
||||||
a plaintext string with the supported commands, space-separated, eg. `pay_invoice get_balance`. Only the `pay_invoice` command is described in this NIP, but other commands might be defined in different NIPs.
|
a plaintext string with the supported commands, space-separated, eg. `pay_invoice get_balance`. Only the `pay_invoice` command is described in this NIP, but other commands might be defined in different NIPs.
|
||||||
|
|
||||||
Both the request and response events SHOULD contain one `p` tag, containing the public key of the **wallet service** if this is a request, and the public key of the **user** if this is a response. The response event SHOULD contain an `e` tag with the id of the request event it is responding to.
|
Both the request and response events SHOULD contain one `p` tag, containing the public key of the **wallet service** if this is a request, and the public key of the **user** if this is a response. The response event SHOULD contain an `e` tag with the id of the request event it is responding to.
|
||||||
|
Optionally, a request can have an `expiration` tag that has a unix timestamp in seconds. If the request is received after this timestamp, it should be ignored.
|
||||||
|
|
||||||
The content of requests and responses is encrypted with [NIP04](https://github.com/nostr-protocol/nips/blob/master/04.md), and is a JSON-RPCish object with a semi-fixed structure:
|
The content of requests and responses is encrypted with [NIP04](https://github.com/nostr-protocol/nips/blob/master/04.md), and is a JSON-RPCish object with a semi-fixed structure:
|
||||||
|
|
||||||
|
|
@ -80,7 +81,7 @@ If the command was successful, the `error` field must be null.
|
||||||
## Nostr Wallet Connect URI
|
## Nostr Wallet Connect URI
|
||||||
**client** discovers **wallet service** by scanning a QR code, handling a deeplink or pasting in a URI.
|
**client** discovers **wallet service** by scanning a QR code, handling a deeplink or pasting in a URI.
|
||||||
|
|
||||||
The **wallet service** generates this connection URI with protocol `nostr+walletconnect:` and base path it's hex-encoded `pubkey` with the following query string parameters:
|
The **wallet service** generates this connection URI with protocol `nostr+walletconnect://` and base path it's hex-encoded `pubkey` with the following query string parameters:
|
||||||
|
|
||||||
- `relay` Required. URL of the relay where the **wallet service** is connected and will be listening for events. May be more than one.
|
- `relay` Required. URL of the relay where the **wallet service** is connected and will be listening for events. May be more than one.
|
||||||
- `secret` Required. 32-byte randomly generated hex encoded string. The **client** MUST use this to sign events and encrypt payloads when communicating with the **wallet service**.
|
- `secret` Required. 32-byte randomly generated hex encoded string. The **client** MUST use this to sign events and encrypt payloads when communicating with the **wallet service**.
|
||||||
|
|
@ -94,7 +95,7 @@ The **client** should then store this connection and use it when the user wants
|
||||||
|
|
||||||
### Example connection string
|
### Example connection string
|
||||||
```sh
|
```sh
|
||||||
nostr+walletconnect:b889ff5b1513b641e2a139f661a661364979c5beee91842f8f0ef42ab558e9d4?relay=wss%3A%2F%2Frelay.damus.io&secret=71a8c14c1407c113601079c4302dab36460f0ccd0ad506f1f2dc73b5100e4f3c
|
nostr+walletconnect://b889ff5b1513b641e2a139f661a661364979c5beee91842f8f0ef42ab558e9d4?relay=wss%3A%2F%2Frelay.damus.io&secret=71a8c14c1407c113601079c4302dab36460f0ccd0ad506f1f2dc73b5100e4f3c
|
||||||
```
|
```
|
||||||
|
|
||||||
## Commands
|
## Commands
|
||||||
|
|
@ -108,7 +109,8 @@ Request:
|
||||||
{
|
{
|
||||||
"method": "pay_invoice",
|
"method": "pay_invoice",
|
||||||
"params": {
|
"params": {
|
||||||
"invoice": "lnbc50n1..." // bolt11 invoice
|
"invoice": "lnbc50n1...", // bolt11 invoice
|
||||||
|
"amount": 123, // invoice amount in msats, optional
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
@ -126,10 +128,282 @@ Response:
|
||||||
Errors:
|
Errors:
|
||||||
- `PAYMENT_FAILED`: The payment failed. This may be due to a timeout, exhausting all routes, insufficient capacity or similar.
|
- `PAYMENT_FAILED`: The payment failed. This may be due to a timeout, exhausting all routes, insufficient capacity or similar.
|
||||||
|
|
||||||
|
### `multi_pay_invoice`
|
||||||
|
|
||||||
|
Description: Requests payment of multiple invoices.
|
||||||
|
|
||||||
|
Request:
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"method": "multi_pay_invoice",
|
||||||
|
"params": {
|
||||||
|
"invoices": [
|
||||||
|
{"id":"4da52c32a1", "invoice": "lnbc1...", "amount": 123}, // bolt11 invoice and amount in msats, amount is optional
|
||||||
|
{"id":"3da52c32a1", "invoice": "lnbc50n1..."},
|
||||||
|
],
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Response:
|
||||||
|
|
||||||
|
For every invoice in the request, a separate response event is sent. To differentiate between the responses, each
|
||||||
|
response event contains an `d` tag with the id of the invoice it is responding to, if no id was given, then the
|
||||||
|
payment hash of the invoice should be used.
|
||||||
|
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"result_type": "multi_pay_invoice",
|
||||||
|
"result": {
|
||||||
|
"preimage": "0123456789abcdef..." // preimage of the payment
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Errors:
|
||||||
|
- `PAYMENT_FAILED`: The payment failed. This may be due to a timeout, exhausting all routes, insufficient capacity or similar.
|
||||||
|
|
||||||
|
### `pay_keysend`
|
||||||
|
|
||||||
|
Request:
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"method": "pay_keysend",
|
||||||
|
"params": {
|
||||||
|
"amount": 123, // invoice amount in msats, required
|
||||||
|
"pubkey": "03...", // payee pubkey, required
|
||||||
|
"preimage": "0123456789abcdef...", // preimage of the payment, optional
|
||||||
|
"tlv_records: [ // tlv records, optional
|
||||||
|
{
|
||||||
|
"type": 5482373484, // tlv type
|
||||||
|
"value": "0123456789abcdef" // hex encoded tlv value
|
||||||
|
}
|
||||||
|
]
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Response:
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"result_type": "pay_keysend",
|
||||||
|
"result": {
|
||||||
|
"preimage": "0123456789abcdef...", // preimage of the payment
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Errors:
|
||||||
|
- `PAYMENT_FAILED`: The payment failed. This may be due to a timeout, exhausting all routes, insufficient capacity or similar.
|
||||||
|
|
||||||
|
### `multi_pay_keysend`
|
||||||
|
|
||||||
|
Description: Requests multiple keysend payments.
|
||||||
|
|
||||||
|
Has an array of keysends, these follow the same semantics as `pay_keysend`, just done in a batch
|
||||||
|
|
||||||
|
Request:
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"method": "multi_pay_keysend",
|
||||||
|
"params": {
|
||||||
|
"keysends": [
|
||||||
|
{"id": "4c5b24a351", pubkey": "03...", "amount": 123},
|
||||||
|
{"id": "3da52c32a1", "pubkey": "02...", "amount": 567, "preimage": "abc123..", "tlv_records": [{"type": 696969, "value": "77616c5f6872444873305242454d353736"}]},
|
||||||
|
],
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Response:
|
||||||
|
|
||||||
|
For every keysend in the request, a separate response event is sent. To differentiate between the responses, each
|
||||||
|
response event contains an `d` tag with the id of the keysend it is responding to, if no id was given, then the
|
||||||
|
pubkey should be used.
|
||||||
|
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"result_type": "multi_pay_keysend",
|
||||||
|
"result": {
|
||||||
|
"preimage": "0123456789abcdef..." // preimage of the payment
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Errors:
|
||||||
|
- `PAYMENT_FAILED`: The payment failed. This may be due to a timeout, exhausting all routes, insufficient capacity or similar.
|
||||||
|
|
||||||
|
### `make_invoice`
|
||||||
|
|
||||||
|
Request:
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"method": "make_invoice",
|
||||||
|
"params": {
|
||||||
|
"amount": 123, // value in msats
|
||||||
|
"description": "string", // invoice's description, optional
|
||||||
|
"description_hash": "string", // invoice's description hash, optional
|
||||||
|
"expiry": 213 // expiry in seconds from time invoice is created, optional
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Response:
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"result_type": "make_invoice",
|
||||||
|
"result": {
|
||||||
|
"type": "incoming", // "incoming" for invoices, "outgoing" for payments
|
||||||
|
"invoice": "string", // encoded invoice, optional
|
||||||
|
"description": "string", // invoice's description, optional
|
||||||
|
"description_hash": "string", // invoice's description hash, optional
|
||||||
|
"preimage": "string", // payment's preimage, optional if unpaid
|
||||||
|
"payment_hash": "string", // Payment hash for the payment
|
||||||
|
"amount": 123, // value in msats
|
||||||
|
"fees_paid": 123, // value in msats
|
||||||
|
"created_at": unixtimestamp, // invoice/payment creation time
|
||||||
|
"expires_at": unixtimestamp, // invoice expiration time, optional if not applicable
|
||||||
|
"metadata": {} // generic metadata that can be used to add things like zap/boostagram details for a payer name/comment/etc.
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
### `lookup_invoice`
|
||||||
|
|
||||||
|
Request:
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"method": "lookup_invoice",
|
||||||
|
"params": {
|
||||||
|
"payment_hash": "31afdf1..", // payment hash of the invoice, one of payment_hash or invoice is required
|
||||||
|
"invoice": "lnbc50n1..." // invoice to lookup
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Response:
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"result_type": "lookup_invoice",
|
||||||
|
"result": {
|
||||||
|
"type": "incoming", // "incoming" for invoices, "outgoing" for payments
|
||||||
|
"invoice": "string", // encoded invoice, optional
|
||||||
|
"description": "string", // invoice's description, optional
|
||||||
|
"description_hash": "string", // invoice's description hash, optional
|
||||||
|
"preimage": "string", // payment's preimage, optional if unpaid
|
||||||
|
"payment_hash": "string", // Payment hash for the payment
|
||||||
|
"amount": 123, // value in msats
|
||||||
|
"fees_paid": 123, // value in msats
|
||||||
|
"created_at": unixtimestamp, // invoice/payment creation time
|
||||||
|
"expires_at": unixtimestamp, // invoice expiration time, optional if not applicable
|
||||||
|
"settled_at": unixtimestamp, // invoice/payment settlement time, optional if unpaid
|
||||||
|
"metadata": {} // generic metadata that can be used to add things like zap/boostagram details for a payer name/comment/etc.
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Errors:
|
||||||
|
- `NOT_FOUND`: The invoice could not be found by the given parameters.
|
||||||
|
|
||||||
|
### `list_transactions`
|
||||||
|
|
||||||
|
Lists invoices and payments. If `type` is not specified, both invoices and payments are returned.
|
||||||
|
The `from` and `until` parameters are timestamps in seconds since epoch. If `from` is not specified, it defaults to 0.
|
||||||
|
If `until` is not specified, it defaults to the current time. Transactions are returned in descending order of creation
|
||||||
|
time.
|
||||||
|
|
||||||
|
Request:
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"method": "list_transactions",
|
||||||
|
"params": {
|
||||||
|
"from": 1693876973, // starting timestamp in seconds since epoch (inclusive), optional
|
||||||
|
"until": 1703225078, // ending timestamp in seconds since epoch (inclusive), optional
|
||||||
|
"limit": 10, // maximum number of invoices to return, optional
|
||||||
|
"offset": 0, // offset of the first invoice to return, optional
|
||||||
|
"unpaid": true, // include unpaid invoices, optional, default false
|
||||||
|
"type": "incoming", // "incoming" for invoices, "outgoing" for payments, undefined for both
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Response:
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"result_type": "list_transactions",
|
||||||
|
"result": {
|
||||||
|
"transactions": [
|
||||||
|
{
|
||||||
|
"type": "incoming", // "incoming" for invoices, "outgoing" for payments
|
||||||
|
"invoice": "string", // encoded invoice, optional
|
||||||
|
"description": "string", // invoice's description, optional
|
||||||
|
"description_hash": "string", // invoice's description hash, optional
|
||||||
|
"preimage": "string", // payment's preimage, optional if unpaid
|
||||||
|
"payment_hash": "string", // Payment hash for the payment
|
||||||
|
"amount": 123, // value in msats
|
||||||
|
"fees_paid": 123, // value in msats
|
||||||
|
"created_at": unixtimestamp, // invoice/payment creation time
|
||||||
|
"expires_at": unixtimestamp, // invoice expiration time, optional if not applicable
|
||||||
|
"settled_at": unixtimestamp, // invoice/payment settlement time, optional if unpaid
|
||||||
|
"metadata": {} // generic metadata that can be used to add things like zap/boostagram details for a payer name/comment/etc.
|
||||||
|
}
|
||||||
|
],
|
||||||
|
},
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
### `get_balance`
|
||||||
|
|
||||||
|
Request:
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"method": "get_balance",
|
||||||
|
"params": {
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Response:
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"result_type": "get_balance",
|
||||||
|
"result": {
|
||||||
|
"balance": 10000, // user's balance in msats
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
### `get_info`
|
||||||
|
|
||||||
|
Request:
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"method": "get_info",
|
||||||
|
"params": {
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Response:
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"result_type": "get_info",
|
||||||
|
"result": {
|
||||||
|
"alias": "string",
|
||||||
|
"color": "hex string",
|
||||||
|
"pubkey": "hex string",
|
||||||
|
"network": "string", // mainnet, testnet, signet, or regtest
|
||||||
|
"block_height": 1,
|
||||||
|
"block_hash": "hex string",
|
||||||
|
"methods": ["pay_invoice", "get_balance", "make_invoice", "lookup_invoice", "list_transactions", "get_info"], // list of supported methods for this connection
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
## Example pay invoice flow
|
## Example pay invoice flow
|
||||||
|
|
||||||
0. The user scans the QR code generated by the **wallet service** with their **client** application, they follow a `nostr+walletconnect:` deeplink or configure the connection details manually.
|
0. The user scans the QR code generated by the **wallet service** with their **client** application, they follow a `nostr+walletconnect://` deeplink or configure the connection details manually.
|
||||||
1. **client** sends an event to the **wallet service** service with kind `23194`. The content is a `pay_invoice` request. The private key is the secret from the connection string above.
|
1. **client** sends an event to the **wallet service** with kind `23194`. The content is a `pay_invoice` request. The private key is the secret from the connection string above.
|
||||||
2. **wallet service** verifies that the author's key is authorized to perform the payment, decrypts the payload and sends the payment.
|
2. **wallet service** verifies that the author's key is authorized to perform the payment, decrypts the payload and sends the payment.
|
||||||
3. **wallet service** responds to the event by sending an event with kind `23195` and content being a response either containing an error message or a preimage.
|
3. **wallet service** responds to the event by sending an event with kind `23195` and content being a response either containing an error message or a preimage.
|
||||||
|
|
||||||
|
|
|
||||||
60
48.md
Normal file
60
48.md
Normal file
|
|
@ -0,0 +1,60 @@
|
||||||
|
NIP-48
|
||||||
|
======
|
||||||
|
|
||||||
|
Proxy Tags
|
||||||
|
----------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
Nostr events bridged from other protocols such as ActivityPub can link back to the source object by including a `"proxy"` tag, in the form:
|
||||||
|
|
||||||
|
```
|
||||||
|
["proxy", <id>, <protocol>]
|
||||||
|
```
|
||||||
|
|
||||||
|
Where:
|
||||||
|
|
||||||
|
- `<id>` is the ID of the source object. The ID format varies depending on the protocol. The ID must be universally unique, regardless of the protocol.
|
||||||
|
- `<protocol>` is the name of the protocol, e.g. `"activitypub"`.
|
||||||
|
|
||||||
|
Clients may use this information to reconcile duplicated content bridged from other protocols, or to display a link to the source object.
|
||||||
|
|
||||||
|
Proxy tags may be added to any event kind, and doing so indicates that the event did not originate on the Nostr protocol, and instead originated elsewhere on the web.
|
||||||
|
|
||||||
|
### Supported protocols
|
||||||
|
|
||||||
|
This list may be extended in the future.
|
||||||
|
|
||||||
|
| Protocol | ID format | Example |
|
||||||
|
| -------- | --------- | ------- |
|
||||||
|
| `activitypub` | URL | `https://gleasonator.com/objects/9f524868-c1a0-4ee7-ad51-aaa23d68b526` |
|
||||||
|
| `atproto` | AT URI | `at://did:plc:zhbjlbmir5dganqhueg7y4i3/app.bsky.feed.post/3jt5hlibeol2i` |
|
||||||
|
| `rss` | URL with guid fragment | `https://soapbox.pub/rss/feed.xml#https%3A%2F%2Fsoapbox.pub%2Fblog%2Fmostr-fediverse-nostr-bridge` |
|
||||||
|
| `web` | URL | `https://twitter.com/jack/status/20` |
|
||||||
|
|
||||||
|
### Examples
|
||||||
|
|
||||||
|
ActivityPub object:
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"kind": 1,
|
||||||
|
"content": "I'm vegan btw",
|
||||||
|
"tags": [
|
||||||
|
[
|
||||||
|
"proxy",
|
||||||
|
"https://gleasonator.com/objects/8f6fac53-4f66-4c6e-ac7d-92e5e78c3e79",
|
||||||
|
"activitypub"
|
||||||
|
]
|
||||||
|
],
|
||||||
|
"pubkey": "79c2cae114ea28a981e7559b4fe7854a473521a8d22a66bbab9fa248eb820ff6",
|
||||||
|
"created_at": 1691091365,
|
||||||
|
"id": "55920b758b9c7b17854b6e3d44e6a02a83d1cb49e1227e75a30426dea94d4cb2",
|
||||||
|
"sig": "a72f12c08f18e85d98fb92ae89e2fe63e48b8864c5e10fbdd5335f3c9f936397a6b0a7350efe251f8168b1601d7012d4a6d0ee6eec958067cf22a14f5a5ea579"
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
### See also
|
||||||
|
|
||||||
|
- [FEP-fffd: Proxy Objects](https://codeberg.org/fediverse/fep/src/branch/main/fep/fffd/fep-fffd.md)
|
||||||
|
- [Mostr bridge](https://mostr.pub/)
|
||||||
126
49.md
Normal file
126
49.md
Normal file
|
|
@ -0,0 +1,126 @@
|
||||||
|
|
||||||
|
NIP-49
|
||||||
|
======
|
||||||
|
|
||||||
|
Private Key Encryption
|
||||||
|
----------------------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
This NIP defines a method by which clients can encrypt (and decrypt) a user's private key with a password.
|
||||||
|
|
||||||
|
Symmetric Encryption Key derivation
|
||||||
|
-----------------------------------
|
||||||
|
|
||||||
|
PASSWORD = Read from the user. The password should be unicode normalized to NFKC format to ensure that the password can be entered identically on other computers/clients.
|
||||||
|
|
||||||
|
LOG\_N = Let the user or implementer choose one byte representing a power of 2 (e.g. 18 represents 262,144) which is used as the number of rounds for scrypt. Larger numbers take more time and more memory, and offer better protection:
|
||||||
|
|
||||||
|
| LOG_N | MEMORY REQUIRED | APPROX TIME ON FAST COMPUTER |
|
||||||
|
|-------|-----------------|----------------------------- |
|
||||||
|
| 16 | 64 MiB | 100 ms |
|
||||||
|
| 18 | 256 MiB | |
|
||||||
|
| 20 | 1 GiB | 2 seconds |
|
||||||
|
| 21 | 2 GiB | |
|
||||||
|
| 22 | 4 GiB | |
|
||||||
|
|
||||||
|
SALT = 16 random bytes
|
||||||
|
|
||||||
|
SYMMETRIC_KEY = scrypt(password=PASSWORD, salt=SALT, log\_n=LOG\_N, r=8, p=1)
|
||||||
|
|
||||||
|
The symmetric key should be 32 bytes long.
|
||||||
|
|
||||||
|
This symmetric encryption key is temporary and should be zeroed and discarded after use and not stored or reused for any other purpose.
|
||||||
|
|
||||||
|
|
||||||
|
Encrypting a private key
|
||||||
|
------------------------
|
||||||
|
|
||||||
|
The private key encryption process is as follows:
|
||||||
|
|
||||||
|
PRIVATE\_KEY = User's private (secret) secp256k1 key as 32 raw bytes (not hex or bech32 encoded!)
|
||||||
|
|
||||||
|
KEY\_SECURITY\_BYTE = one of:
|
||||||
|
|
||||||
|
* 0x00 - if the key has been known to have been handled insecurely (stored unencrypted, cut and paste unencrypted, etc)
|
||||||
|
* 0x01 - if the key has NOT been known to have been handled insecurely (stored unencrypted, cut and paste unencrypted, etc)
|
||||||
|
* 0x02 - if the client does not track this data
|
||||||
|
|
||||||
|
ASSOCIATED\_DATA = KEY\_SECURITY\_BYTE
|
||||||
|
|
||||||
|
NONCE = 24 byte random nonce
|
||||||
|
|
||||||
|
CIPHERTEXT = XChaCha20-Poly1305(
|
||||||
|
plaintext=PRIVATE\_KEY,
|
||||||
|
associated_data=ASSOCIATED\_DATA,
|
||||||
|
nonce=NONCE,
|
||||||
|
key=SYMMETRIC\_KEY
|
||||||
|
)
|
||||||
|
|
||||||
|
VERSION\_NUMBER = 0x02
|
||||||
|
|
||||||
|
CIPHERTEXT_CONCATENATION = concat(
|
||||||
|
VERSION\_NUMBER,
|
||||||
|
LOG\_N,
|
||||||
|
SALT,
|
||||||
|
NONCE,
|
||||||
|
ASSOCIATED\_DATA,
|
||||||
|
CIPHERTEXT
|
||||||
|
)
|
||||||
|
|
||||||
|
ENCRYPTED\_PRIVATE\_KEY = bech32_encode('ncryptsec', CIPHERTEXT\_CONCATENATION)
|
||||||
|
|
||||||
|
The output prior to bech32 encoding should be 91 bytes long.
|
||||||
|
|
||||||
|
The decryption process operates in the reverse.
|
||||||
|
|
||||||
|
|
||||||
|
Test Data
|
||||||
|
---------
|
||||||
|
|
||||||
|
## Password Unicode Normalization
|
||||||
|
|
||||||
|
The following password input: "ÅΩẛ̣"
|
||||||
|
- Unicode Codepoints: U+212B U+2126 U+1E9B U+0323
|
||||||
|
- UTF-8 bytes: [0xE2, 0x84, 0xAB, 0xE2, 0x84, 0xA6, 0xE1, 0xBA, 0x9B, 0xCC, 0xA3]
|
||||||
|
|
||||||
|
Should be converted into the unicode normalized NFKC format prior to use in scrypt: "ÅΩẛ̣"
|
||||||
|
- Unicode Codepoints: U+00C5 U+03A9 U+1E69
|
||||||
|
- UTF-8 bytes: [0xC3, 0x85, 0xCE, 0xA9, 0xE1, 0xB9, 0xA9]
|
||||||
|
|
||||||
|
## Encryption
|
||||||
|
|
||||||
|
The encryption process is non-deterministic due to the random nonce.
|
||||||
|
|
||||||
|
## Decryption
|
||||||
|
|
||||||
|
The following encrypted private key:
|
||||||
|
|
||||||
|
`ncryptsec1qgg9947rlpvqu76pj5ecreduf9jxhselq2nae2kghhvd5g7dgjtcxfqtd67p9m0w57lspw8gsq6yphnm8623nsl8xn9j4jdzz84zm3frztj3z7s35vpzmqf6ksu8r89qk5z2zxfmu5gv8th8wclt0h4p`
|
||||||
|
|
||||||
|
When decrypted with password='nostr' and log_n=16 yields the following hex-encoded private key:
|
||||||
|
|
||||||
|
`3501454135014541350145413501453fefb02227e449e57cf4d3a3ce05378683`
|
||||||
|
|
||||||
|
Discussion
|
||||||
|
----------
|
||||||
|
|
||||||
|
### On Key Derivation
|
||||||
|
|
||||||
|
Passwords make poor cryptographic keys. Prior to use as a cryptographic key, two things need to happen:
|
||||||
|
|
||||||
|
1. An encryption key needs to be deterministically created from the password such that is has a uniform functionally random distribution of bits, such that the symmetric encryption algorithm's assumptions are valid, and
|
||||||
|
2. A slow irreversible algorithm should be injected into the process, so that brute-force attempts to decrypt by trying many passwords are severely hampered.
|
||||||
|
|
||||||
|
These are achieved using a password-based key derivation function. We use scrypt, which has been proven to be maximally memory hard and which several cryptographers have indicated to the author is better than argon2 even though argon2 won a competition in 2015.
|
||||||
|
|
||||||
|
### On the symmetric encryption algorithm
|
||||||
|
|
||||||
|
XChaCha20-Poly1305 is typically favored by cryptographers over AES and is less associated with the U.S. government. It (or it's earlier variant without the 'X') is gaining wide usage, is used in TLS and OpenSSH, and is available in most modern crypto libraries.
|
||||||
|
|
||||||
|
Recommendations
|
||||||
|
---------
|
||||||
|
|
||||||
|
It is not recommended that users publish these encrypted private keys to nostr, as cracking a key may become easier when an attacker can amass many encrypted private keys.
|
||||||
|
|
||||||
|
It is recommended that clients zero out the memory of passwords and private keys before freeing that memory.
|
||||||
8
50.md
8
50.md
|
|
@ -4,7 +4,7 @@ NIP-50
|
||||||
Search Capability
|
Search Capability
|
||||||
-----------------
|
-----------------
|
||||||
|
|
||||||
`draft` `optional` `author:brugeman` `author:mikedilger` `author:fiatjaf`
|
`draft` `optional`
|
||||||
|
|
||||||
## Abstract
|
## Abstract
|
||||||
|
|
||||||
|
|
@ -41,9 +41,13 @@ implementation details between relays.
|
||||||
Clients MAY verify that events returned by a relay match the specified query in a way that suits the
|
Clients MAY verify that events returned by a relay match the specified query in a way that suits the
|
||||||
client's use case, and MAY stop querying relays that have low precision.
|
client's use case, and MAY stop querying relays that have low precision.
|
||||||
|
|
||||||
Relays SHOULD exclude spam from search results by default if they supports some form of spam filtering.
|
Relays SHOULD exclude spam from search results by default if they support some form of spam filtering.
|
||||||
|
|
||||||
## Extensions
|
## Extensions
|
||||||
|
|
||||||
Relay MAY support these extensions:
|
Relay MAY support these extensions:
|
||||||
- `include:spam` - turn off spam filtering, if it was enabled by default
|
- `include:spam` - turn off spam filtering, if it was enabled by default
|
||||||
|
- `domain:<domain>` - include only events from users whose valid nip05 domain matches the domain
|
||||||
|
- `language:<two letter ISO 639-1 language code>` - include only events of a specified language
|
||||||
|
- `sentiment:<negative/neutral/positive>` - include only events of a specific sentiment
|
||||||
|
- `nsfw:<true/false>` - include or exclude nsfw events (default: true)
|
||||||
|
|
|
||||||
189
51.md
189
51.md
|
|
@ -2,111 +2,142 @@ NIP-51
|
||||||
======
|
======
|
||||||
|
|
||||||
Lists
|
Lists
|
||||||
-------------------------
|
-----
|
||||||
|
|
||||||
`draft` `optional` `author:fiatjaf` `author:arcbtc` `author:monlovesmango` `author:eskema` `depends:33`
|
`draft` `optional`
|
||||||
|
|
||||||
A "list" event is defined as having a list of public and/or private tags. Public tags will be listed in the event `tags`. Private tags will be encrypted in the event `content`. Encryption for private tags will use [NIP-04 - Encrypted Direct Message](04.md) encryption, using the list author's private and public key for the shared secret. A distinct event kind should be used for each list type created.
|
This NIP defines lists of things that users can create. Lists can contain references to anything, and these references can be **public** or **private**.
|
||||||
|
|
||||||
If a list type should only be defined once per user (like the 'Mute' list), the list type's events should follow the specification for [NIP-16 - Replaceable Events](16.md). These lists may be referred to as 'replaceable lists'.
|
Public items in a list are specified in the event `tags` array, while private items are specified in a JSON array that mimics the structure of the event `tags` array, but stringified and encrypted using the same scheme from [NIP-04](04.md) (the shared key is computed using the author's public and private key) and stored in the `.content`.
|
||||||
|
|
||||||
Otherwise, the list type's events should follow the specification for [NIP-33 - Parameterized Replaceable Events](33.md), where the list name will be used as the 'd' parameter. These lists may be referred to as 'parameterized replaceable lists'.
|
When new items are added to an existing list, clients SHOULD append them to the end of the list, so they are stored in chronological order.
|
||||||
|
|
||||||
## Replaceable List Event Example
|
## Types of lists
|
||||||
|
|
||||||
Lets say a user wants to create a 'Mute' list and has keys:
|
## Standard lists
|
||||||
```
|
|
||||||
priv: fb505c65d4df950f5d28c9e4d285ee12ffaf315deef1fc24e3c7cd1e7e35f2b1
|
|
||||||
pub: b1a5c93edcc8d586566fde53a20bdb50049a97b15483cb763854e57016e0fa3d
|
|
||||||
```
|
|
||||||
The user wants to publicly include these users:
|
|
||||||
|
|
||||||
```json
|
Standard lists use non-parameterized replaceable events, meaning users may only have a single list of each kind. They have special meaning and clients may rely on them to augment a user's profile or browsing experience.
|
||||||
["p", "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d"],
|
|
||||||
["p", "32e1827635450ebb3c5a7d12c1f8e7b2b514439ac10a67eef3d9fd9c5c68e245"]
|
|
||||||
```
|
|
||||||
and privately include these users (below is the JSON that would be encrypted and placed in the event content):
|
|
||||||
|
|
||||||
```json
|
For example, _mute list_ can contain the public keys of spammers and bad actors users don't want to see in their feeds or receive annoying notifications from.
|
||||||
[
|
|
||||||
["p", "9ec7a778167afb1d30c4833de9322da0c08ba71a69e1911d5578d3144bb56437"],
|
|
||||||
["p", "8c0da4862130283ff9e67d889df264177a508974e2feb96de139804ea66d6168"]
|
|
||||||
]
|
|
||||||
```
|
|
||||||
|
|
||||||
Then the user would create a 'Mute' list event like below:
|
| name | kind | description | expected tag items |
|
||||||
|
| --- | --- | --- | --- |
|
||||||
|
| Mute list | 10000 | things the user doesn't want to see in their feeds | `"p"` (pubkeys), `"t"` (hashtags), `"word"` (lowercase string), `"e"` (threads) |
|
||||||
|
| Pinned notes | 10001 | events the user intends to showcase in their profile page | `"e"` (kind:1 notes) |
|
||||||
|
| Bookmarks | 10003 | uncategorized, "global" list of things a user wants to save | `"e"` (kind:1 notes), `"a"` (kind:30023 articles), `"t"` (hashtags), `"r"` (URLs) |
|
||||||
|
| Communities | 10004 | [NIP-72](72.md) communities the user belongs to | `"a"` (kind:34550 community definitions) |
|
||||||
|
| Public chats | 10005 | [NIP-28](28.md) chat channels the user is in | `"e"` (kind:40 channel definitions) |
|
||||||
|
| Blocked relays | 10006 | relays clients should never connect to | `"relay"` (relay URLs) |
|
||||||
|
| Search relays | 10007 | relays clients should use when performing search queries | `"relay"` (relay URLs) |
|
||||||
|
| Simple groups | 10009 | [NIP-29](29.md) groups the user is in | `"group"` ([NIP-29](29.md) group ids + mandatory relay URL) |
|
||||||
|
| Interests | 10015 | topics a user may be interested in and pointers | `"t"` (hashtags) and `"a"` (kind:30015 interest set) |
|
||||||
|
| Emojis | 10030 | user preferred emojis and pointers to emoji sets | `"emoji"` (see [NIP-30](30.md)) and `"a"` (kind:30030 emoji set) |
|
||||||
|
| Good wiki authors | 10101 | [NIP-54](54.md) user recommended wiki authors | `"p"` (pubkeys) |
|
||||||
|
| Good wiki relays | 10102 | [NIP-54](54.md) relays deemed to only host useful articles | `"relay"` (relay URLs) |
|
||||||
|
|
||||||
|
## Sets
|
||||||
|
|
||||||
|
Sets are lists with well-defined meaning that can enhance the functionality and the UI of clients that rely on them. Unlike standard lists, users are expected to have more than one set of each kind, therefore each of them must be assigned a different `"d"` identifier.
|
||||||
|
|
||||||
|
For example, _relay sets_ can be displayed in a dropdown UI to give users the option to switch to which relays they will publish an event or from which relays they will read the replies to an event; _curation sets_ can be used by apps to showcase curations made by others tagged to different topics.
|
||||||
|
|
||||||
|
Aside from their main identifier, the `"d"` tag, sets can optionally have a `"title"`, an `"image"` and a `"description"` tags that can be used to enhance their UI.
|
||||||
|
|
||||||
|
| name | kind | description | expected tag items |
|
||||||
|
| --- | --- | --- | --- |
|
||||||
|
| Follow sets | 30000 | categorized groups of users a client may choose to check out in different circumstances | `"p"` (pubkeys) |
|
||||||
|
| Relay sets | 30002 | user-defined relay groups the user can easily pick and choose from during various operations | `"relay"` (relay URLs) |
|
||||||
|
| Bookmark sets | 30003 | user-defined bookmarks categories , for when bookmarks must be in labeled separate groups | `"e"` (kind:1 notes), `"a"` (kind:30023 articles), `"t"` (hashtags), `"r"` (URLs) |
|
||||||
|
| Curation sets | 30004 | groups of articles picked by users as interesting and/or belonging to the same category | `"a"` (kind:30023 articles), `"e"` (kind:1 notes) |
|
||||||
|
| Curation sets | 30005 | groups of videos picked by users as interesting and/or belonging to the same category | `"a"` (kind:34235 videos) |
|
||||||
|
| Interest sets | 30015 | interest topics represented by a bunch of "hashtags" | `"t"` (hashtags) |
|
||||||
|
| Emoji sets | 30030 | categorized emoji groups | `"emoji"` (see [NIP-30](30.md)) |
|
||||||
|
| Release artifact sets | 30063 | groups of files of a software release | `"e"` (kind:1063 [file metadata](94.md) events), `"i"` (application identifier, typically reverse domain notation), `"version"` |
|
||||||
|
|
||||||
|
## Deprecated standard lists
|
||||||
|
|
||||||
|
Some clients have used these lists in the past, but they should work on transitioning to the [standard formats](#standard-lists) above.
|
||||||
|
|
||||||
|
| kind | "d" tag | use instead |
|
||||||
|
| --- | --- | --- |
|
||||||
|
| 30000 | `"mute"` | kind 10000 _mute list_ |
|
||||||
|
| 30001 | `"pin"` | kind 10001 _pin list_ |
|
||||||
|
| 30001 | `"bookmark"` | kind 10003 _bookmarks list_ |
|
||||||
|
| 30001 | `"communities"` | kind 10004 _communities list_ |
|
||||||
|
|
||||||
|
## Examples
|
||||||
|
|
||||||
|
### A _mute list_ with some public items and some encrypted items
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
|
"id": "a92a316b75e44cfdc19986c634049158d4206fcc0b7b9c7ccbcdabe28beebcd0",
|
||||||
|
"pubkey": "854043ae8f1f97430ca8c1f1a090bdde6488bd5115c7a45307a2a212750ae4cb",
|
||||||
|
"created_at": 1699597889,
|
||||||
"kind": 10000,
|
"kind": 10000,
|
||||||
"tags": [
|
"tags": [
|
||||||
["p", "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d"],
|
["p", "07caba282f76441955b695551c3c5c742e5b9202a3784780f8086fdcdc1da3a9"],
|
||||||
["p", "32e1827635450ebb3c5a7d12c1f8e7b2b514439ac10a67eef3d9fd9c5c68e245"],
|
["p", "a55c15f5e41d5aebd236eca5e0142789c5385703f1a7485aa4b38d94fd18dcc4"]
|
||||||
],
|
],
|
||||||
"content": "VezuSvWak++ASjFMRqBPWS3mK5pZ0vRLL325iuIL4S+r8n9z+DuMau5vMElz1tGC/UqCDmbzE2kwplafaFo/FnIZMdEj4pdxgptyBV1ifZpH3TEF6OMjEtqbYRRqnxgIXsuOSXaerWgpi0pm+raHQPseoELQI/SZ1cvtFqEUCXdXpa5AYaSd+quEuthAEw7V1jP+5TDRCEC8jiLosBVhCtaPpLcrm8HydMYJ2XB6Ixs=?iv=/rtV49RFm0XyFEwG62Eo9A==",
|
"content": "TJob1dQrf2ndsmdbeGU+05HT5GMnBSx3fx8QdDY/g3NvCa7klfzgaQCmRZuo1d3WQjHDOjzSY1+MgTK5WjewFFumCcOZniWtOMSga9tJk1ky00tLoUUzyLnb1v9x95h/iT/KpkICJyAwUZ+LoJBUzLrK52wNTMt8M5jSLvCkRx8C0BmEwA/00pjOp4eRndy19H4WUUehhjfV2/VV/k4hMAjJ7Bb5Hp9xdmzmCLX9+64+MyeIQQjQAHPj8dkSsRahP7KS3MgMpjaF8nL48Bg5suZMxJayXGVp3BLtgRZx5z5nOk9xyrYk+71e2tnP9IDvSMkiSe76BcMct+m7kGVrRcavDI4n62goNNh25IpghT+a1OjjkpXt9me5wmaL7fxffV1pchdm+A7KJKIUU3kLC7QbUifF22EucRA9xiEyxETusNludBXN24O3llTbOy4vYFsq35BeZl4v1Cse7n2htZicVkItMz3wjzj1q1I1VqbnorNXFgllkRZn4/YXfTG/RMnoK/bDogRapOV+XToZ+IvsN0BqwKSUDx+ydKpci6htDRF2WDRkU+VQMqwM0CoLzy2H6A2cqyMMMD9SLRRzBg==?iv=S3rFeFr1gsYqmQA7bNnNTQ==",
|
||||||
...other fields
|
"sig": "1173822c53261f8cffe7efbf43ba4a97a9198b3e402c2a1df130f42a8985a2d0d3430f4de350db184141e45ca844ab4e5364ea80f11d720e36357e1853dba6ca"
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
|
### A _curation set_ of articles and notes about yaks
|
||||||
## Parameterized Replaceable List Event Example
|
|
||||||
|
|
||||||
Lets say a user wants to create a 'Categorized People' list of `nostr` people and has keys:
|
|
||||||
```
|
|
||||||
priv: fb505c65d4df950f5d28c9e4d285ee12ffaf315deef1fc24e3c7cd1e7e35f2b1
|
|
||||||
pub: b1a5c93edcc8d586566fde53a20bdb50049a97b15483cb763854e57016e0fa3d
|
|
||||||
```
|
|
||||||
The user wants to publicly include these users:
|
|
||||||
|
|
||||||
```json
|
|
||||||
["p", "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d"],
|
|
||||||
["p", "32e1827635450ebb3c5a7d12c1f8e7b2b514439ac10a67eef3d9fd9c5c68e245"]
|
|
||||||
```
|
|
||||||
and privately include these users (below is the JSON that would be encrypted and placed in the event content):
|
|
||||||
|
|
||||||
```json
|
|
||||||
[
|
|
||||||
["p", "9ec7a778167afb1d30c4833de9322da0c08ba71a69e1911d5578d3144bb56437"],
|
|
||||||
["p", "8c0da4862130283ff9e67d889df264177a508974e2feb96de139804ea66d6168"]
|
|
||||||
]
|
|
||||||
```
|
|
||||||
|
|
||||||
Then the user would create a 'Categorized People' list event like below:
|
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"kind": 30000,
|
"id": "567b41fc9060c758c4216fe5f8d3df7c57daad7ae757fa4606f0c39d4dd220ef",
|
||||||
|
"pubkey": "d6dc95542e18b8b7aec2f14610f55c335abebec76f3db9e58c254661d0593a0c",
|
||||||
|
"created_at": 1695327657,
|
||||||
|
"kind": 30004,
|
||||||
"tags": [
|
"tags": [
|
||||||
["d", "nostr"],
|
["d", "jvdy9i4"],
|
||||||
["p", "3bf0c63fcb93463407af97a5e5ee64fa883d107ef9e558472c4eb9aaaefa459d"],
|
["name", "Yaks"],
|
||||||
["p", "32e1827635450ebb3c5a7d12c1f8e7b2b514439ac10a67eef3d9fd9c5c68e245"],
|
["picture", "https://cdn.britannica.com/40/188540-050-9AC748DE/Yak-Himalayas-Nepal.jpg"],
|
||||||
|
["about", "The domestic yak, also known as the Tartary ox, grunting ox, or hairy cattle, is a species of long-haired domesticated cattle found throughout the Himalayan region of the Indian subcontinent, the Tibetan Plateau, Gilgit-Baltistan, Tajikistan and as far north as Mongolia and Siberia."],
|
||||||
|
["a", "30023:26dc95542e18b8b7aec2f14610f55c335abebec76f3db9e58c254661d0593a0c:95ODQzw3ajNoZ8SyMDOzQ"],
|
||||||
|
["a", "30023:54af95542e18b8b7aec2f14610f55c335abebec76f3db9e58c254661d0593a0c:1-MYP8dAhramH9J5gJWKx"],
|
||||||
|
["a", "30023:f8fe95542e18b8b7aec2f14610f55c335abebec76f3db9e58c254661d0593a0c:D2Tbd38bGrFvU0bIbvSMt"],
|
||||||
|
["e", "d78ba0d5dce22bfff9db0a9e996c9ef27e2c91051de0c4e1da340e0326b4941e"]
|
||||||
],
|
],
|
||||||
"content": "VezuSvWak++ASjFMRqBPWS3mK5pZ0vRLL325iuIL4S+r8n9z+DuMau5vMElz1tGC/UqCDmbzE2kwplafaFo/FnIZMdEj4pdxgptyBV1ifZpH3TEF6OMjEtqbYRRqnxgIXsuOSXaerWgpi0pm+raHQPseoELQI/SZ1cvtFqEUCXdXpa5AYaSd+quEuthAEw7V1jP+5TDRCEC8jiLosBVhCtaPpLcrm8HydMYJ2XB6Ixs=?iv=/rtV49RFm0XyFEwG62Eo9A==",
|
"content": "",
|
||||||
...other fields
|
"sig": "a9a4e2192eede77e6c9d24ddfab95ba3ff7c03fbd07ad011fff245abea431fb4d3787c2d04aad001cb039cb8de91d83ce30e9a94f82ac3c5a2372aa1294a96bd"
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
## List Event Kinds
|
### A _release artifact set_ of an Example App
|
||||||
|
|
||||||
| kind | list type |
|
```json
|
||||||
| ------ | ----------------------- |
|
{
|
||||||
| 10000 | Mute |
|
"id": "567b41fc9060c758c4216fe5f8d3df7c57daad7ae757fa4606f0c39d4dd220ef",
|
||||||
| 10001 | Pin |
|
"pubkey": "d6dc95542e18b8b7aec2f14610f55c335abebec76f3db9e58c254661d0593a0c",
|
||||||
| 30000 | Categorized People |
|
"created_at": 1695327657,
|
||||||
| 30001 | Categorized Bookmarks |
|
"kind": 30063,
|
||||||
|
"tags": [
|
||||||
|
["d", "ak8dy3v7"],
|
||||||
|
["i", "com.example.app"],
|
||||||
|
["version", "0.0.1"],
|
||||||
|
["title", "Example App"],
|
||||||
|
["image", "http://cdn.site/p/com.example.app/icon.png"],
|
||||||
|
["e", "d78ba0d5dce22bfff9db0a9e996c9ef27e2c91051de0c4e1da340e0326b4941e"], // Windows exe
|
||||||
|
["e", "f27e2c91051de0c4e1da0d5dce22bfff9db0a9340e0326b4941ed78bae996c9e"], // MacOS dmg
|
||||||
|
["e", "9d24ddfab95ba3ff7c03fbd07ad011fff245abea431fb4d3787c2d04aad02332"], // Linux AppImage
|
||||||
|
["e", "340e0326b340e0326b4941ed78ba340e0326b4941ed78ba340e0326b49ed78ba"] // PWA
|
||||||
|
],
|
||||||
|
"content": "Example App is a decentralized marketplace for apps",
|
||||||
|
"sig": "a9a4e2192eede77e6c9d24ddfab95ba3ff7c03fbd07ad011fff245abea431fb4d3787c2d04aad001cb039cb8de91d83ce30e9a94f82ac3c5a2372aa1294a96bd"
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
### Mute List
|
## Encryption process pseudocode
|
||||||
|
|
||||||
An event with kind `10000` is defined as a replaceable list event for listing content a user wants to mute. Any standardized tag can be included in a Mute List.
|
```scala
|
||||||
|
val private_items = [
|
||||||
### Pin List
|
["p", "07caba282f76441955b695551c3c5c742e5b9202a3784780f8086fdcdc1da3a9"],
|
||||||
|
["a", "a55c15f5e41d5aebd236eca5e0142789c5385703f1a7485aa4b38d94fd18dcc4"],
|
||||||
An event with kind `10001` is defined as a replaceable list event for listing content a user wants to pin. Any standardized tag can be included in a Pin List.
|
]
|
||||||
|
val base64blob = nip04.encrypt(json.encode_to_string(private_items))
|
||||||
### Categorized People List
|
event.content = base64blob
|
||||||
|
```
|
||||||
An event with kind `30000` is defined as a parameterized replaceable list event for categorizing people. The 'd' parameter for this event holds the category name of the list. The tags included in these lists MUST follow the format of kind 3 events as defined in [NIP-02 - Contact List and Petnames](02.md).
|
|
||||||
|
|
||||||
### Categorized Bookmarks List
|
|
||||||
|
|
||||||
An event with kind `30001` is defined as a parameterized replaceable list event for categorizing bookmarks. The 'd' parameter for this event holds the category name of the list. Any standardized tag can be included in a Categorized Bookmarks List.
|
|
||||||
|
|
|
||||||
219
52.md
Normal file
219
52.md
Normal file
|
|
@ -0,0 +1,219 @@
|
||||||
|
NIP-52
|
||||||
|
======
|
||||||
|
|
||||||
|
Calendar Events
|
||||||
|
---------------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
This specification defines calendar events representing an occurrence at a specific moment or between moments. These calendar events are _parameterized replaceable_ and deletable per [NIP-09](09.md).
|
||||||
|
|
||||||
|
Unlike the term `calendar event` specific to this NIP, the term `event` is used broadly in all the NIPs to describe any Nostr event. The distinction is being made here to discern between the two terms.
|
||||||
|
|
||||||
|
## Calendar Events
|
||||||
|
|
||||||
|
There are two types of calendar events represented by different kinds: date-based and time-based calendar events. Calendar events are not required to be part of a [calendar](#calendar).
|
||||||
|
|
||||||
|
### Date-Based Calendar Event
|
||||||
|
|
||||||
|
This kind of calendar event starts on a date and ends before a different date in the future. Its use is appropriate for all-day or multi-day events where time and time zone hold no significance. e.g., anniversary, public holidays, vacation days.
|
||||||
|
|
||||||
|
#### Format
|
||||||
|
|
||||||
|
The format uses a parameterized replaceable event kind `31922`.
|
||||||
|
|
||||||
|
The `.content` of these events should be a detailed description of the calendar event. It is required but can be an empty string.
|
||||||
|
|
||||||
|
The list of tags are as follows:
|
||||||
|
* `d` (required) universally unique identifier (UUID). Generated by the client creating the calendar event.
|
||||||
|
* `title` (required) title of the calendar event
|
||||||
|
* `start` (required) inclusive start date in ISO 8601 format (YYYY-MM-DD). Must be less than `end`, if it exists.
|
||||||
|
* `end` (optional) exclusive end date in ISO 8601 format (YYYY-MM-DD). If omitted, the calendar event ends on the same date as `start`.
|
||||||
|
* `location` (optional, repeated) location of the calendar event. e.g. address, GPS coordinates, meeting room name, link to video call
|
||||||
|
* `g` (optional) [geohash](https://en.wikipedia.org/wiki/Geohash) to associate calendar event with a searchable physical location
|
||||||
|
* `p` (optional, repeated) 32-bytes hex pubkey of a participant, optional recommended relay URL, and participant's role in the meeting
|
||||||
|
* `t` (optional, repeated) hashtag to categorize calendar event
|
||||||
|
* `r` (optional, repeated) references / links to web pages, documents, video calls, recorded videos, etc.
|
||||||
|
|
||||||
|
The following tags are deprecated:
|
||||||
|
* `name` name of the calendar event. Use only if `title` is not available.
|
||||||
|
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"id": <32-bytes lowercase hex-encoded SHA-256 of the the serialized event data>,
|
||||||
|
"pubkey": <32-bytes lowercase hex-encoded public key of the event creator>,
|
||||||
|
"created_at": <Unix timestamp in seconds>,
|
||||||
|
"kind": 31922,
|
||||||
|
"content": "<description of calendar event>",
|
||||||
|
"tags": [
|
||||||
|
["d", "<UUID>"],
|
||||||
|
|
||||||
|
["title", "<title of calendar event>"],
|
||||||
|
|
||||||
|
// Dates
|
||||||
|
["start", "<YYYY-MM-DD>"],
|
||||||
|
["end", "<YYYY-MM-DD>"],
|
||||||
|
|
||||||
|
// Location
|
||||||
|
["location", "<location>"],
|
||||||
|
["g", "<geohash>"],
|
||||||
|
|
||||||
|
// Participants
|
||||||
|
["p", "<32-bytes hex of a pubkey>", "<optional recommended relay URL>", "<role>"],
|
||||||
|
["p", "<32-bytes hex of a pubkey>", "<optional recommended relay URL>", "<role>"],
|
||||||
|
|
||||||
|
// Hashtags
|
||||||
|
["t", "<tag>"],
|
||||||
|
["t", "<tag>"],
|
||||||
|
|
||||||
|
// Reference links
|
||||||
|
["r", "<url>"],
|
||||||
|
["r", "<url>"]
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
### Time-Based Calendar Event
|
||||||
|
|
||||||
|
This kind of calendar event spans between a start time and end time.
|
||||||
|
|
||||||
|
#### Format
|
||||||
|
|
||||||
|
The format uses a parameterized replaceable event kind `31923`.
|
||||||
|
|
||||||
|
The `.content` of these events should be a detailed description of the calendar event. It is required but can be an empty string.
|
||||||
|
|
||||||
|
The list of tags are as follows:
|
||||||
|
* `d` (required) universally unique identifier (UUID). Generated by the client creating the calendar event.
|
||||||
|
* `title` (required) title of the calendar event
|
||||||
|
* `start` (required) inclusive start Unix timestamp in seconds. Must be less than `end`, if it exists.
|
||||||
|
* `end` (optional) exclusive end Unix timestamp in seconds. If omitted, the calendar event ends instantaneously.
|
||||||
|
* `start_tzid` (optional) time zone of the start timestamp, as defined by the IANA Time Zone Database. e.g., `America/Costa_Rica`
|
||||||
|
* `end_tzid` (optional) time zone of the end timestamp, as defined by the IANA Time Zone Database. e.g., `America/Costa_Rica`. If omitted and `start_tzid` is provided, the time zone of the end timestamp is the same as the start timestamp.
|
||||||
|
* `location` (optional, repeated) location of the calendar event. e.g. address, GPS coordinates, meeting room name, link to video call
|
||||||
|
* `g` (optional) [geohash](https://en.wikipedia.org/wiki/Geohash) to associate calendar event with a searchable physical location
|
||||||
|
* `p` (optional, repeated) 32-bytes hex pubkey of a participant, optional recommended relay URL, and participant's role in the meeting
|
||||||
|
* `t` (optional, repeated) hashtag to categorize calendar event
|
||||||
|
* `r` (optional, repeated) references / links to web pages, documents, video calls, recorded videos, etc.
|
||||||
|
|
||||||
|
The following tags are deprecated:
|
||||||
|
* `name` name of the calendar event. Use only if `title` is not available.
|
||||||
|
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"id": <32-bytes lowercase hex-encoded SHA-256 of the the serialized event data>,
|
||||||
|
"pubkey": <32-bytes lowercase hex-encoded public key of the event creator>,
|
||||||
|
"created_at": <Unix timestamp in seconds>,
|
||||||
|
"kind": 31923,
|
||||||
|
"content": "<description of calendar event>",
|
||||||
|
"tags": [
|
||||||
|
["d", "<UUID>"],
|
||||||
|
|
||||||
|
["title", "<title of calendar event>"],
|
||||||
|
|
||||||
|
// Timestamps
|
||||||
|
["start", "<Unix timestamp in seconds>"],
|
||||||
|
["end", "<Unix timestamp in seconds>"],
|
||||||
|
|
||||||
|
["start_tzid", "<IANA Time Zone Database identifier>"],
|
||||||
|
["end_tzid", "<IANA Time Zone Database identifier>"],
|
||||||
|
|
||||||
|
// Location
|
||||||
|
["location", "<location>"],
|
||||||
|
["g", "<geohash>"],
|
||||||
|
|
||||||
|
// Participants
|
||||||
|
["p", "<32-bytes hex of a pubkey>", "<optional recommended relay URL>", "<role>"],
|
||||||
|
["p", "<32-bytes hex of a pubkey>", "<optional recommended relay URL>", "<role>"],
|
||||||
|
|
||||||
|
// Hashtags
|
||||||
|
["t", "<tag>"],
|
||||||
|
["t", "<tag>"],
|
||||||
|
|
||||||
|
// Reference links
|
||||||
|
["r", "<url>"],
|
||||||
|
["r", "<url>"]
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## Calendar
|
||||||
|
|
||||||
|
A calendar is a collection of calendar events, represented as a custom replaceable list event using kind `31924`. A user can have multiple calendars. One may create a calendar to segment calendar events for specific purposes. e.g., personal, work, travel, meetups, and conferences.
|
||||||
|
|
||||||
|
### Format
|
||||||
|
|
||||||
|
The `.content` of these events should be a detailed description of the calendar. It is required but can be an empty string.
|
||||||
|
|
||||||
|
The format uses a custom replaceable list of kind `31924` with a list of tags as described below:
|
||||||
|
* `d` (required) universally unique identifier. Generated by the client creating the calendar.
|
||||||
|
* `title` (required) calendar title
|
||||||
|
* `a` (repeated) reference tag to kind `31922` or `31923` calendar event being responded to
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"id": <32-bytes lowercase hex-encoded SHA-256 of the the serialized event data>,
|
||||||
|
"pubkey": <32-bytes lowercase hex-encoded public key of the event creator>,
|
||||||
|
"created_at": <Unix timestamp in seconds>,
|
||||||
|
"kind": 31924,
|
||||||
|
"content": "<description of calendar>",
|
||||||
|
"tags": [
|
||||||
|
["d", "<UUID>"],
|
||||||
|
["title", "<calendar title>"],
|
||||||
|
["a", "<31922 or 31923>:<calendar event author pubkey>:<d-identifier of calendar event>", "<optional relay url>"],
|
||||||
|
["a", "<31922 or 31923>:<calendar event author pubkey>:<d-identifier of calendar event>", "<optional relay url>"]
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## Calendar Event RSVP
|
||||||
|
|
||||||
|
A calendar event RSVP is a response to a calendar event to indicate a user's attendance intention.
|
||||||
|
|
||||||
|
If a calendar event tags a pubkey, that can be interpreted as the calendar event creator inviting that user to attend. Clients MAY choose to prompt the user to RSVP for the calendar event.
|
||||||
|
|
||||||
|
Any user may RSVP, even if they were not tagged on the calendar event. Clients MAY choose to prompt the calendar event creator to invite the user who RSVP'd. Clients also MAY choose to ignore these RSVPs.
|
||||||
|
|
||||||
|
This NIP is intentionally not defining who is authorized to attend a calendar event if the user who RSVP'd has not been tagged. It is up to the calendar event creator to determine the semantics.
|
||||||
|
|
||||||
|
This NIP is also intentionally not defining what happens if a calendar event changes after an RSVP is submitted.
|
||||||
|
|
||||||
|
### Format
|
||||||
|
|
||||||
|
The format uses a parameterized replaceable event kind `31925`.
|
||||||
|
|
||||||
|
The `.content` of these events is optional and should be a free-form note that adds more context to this calendar event response.
|
||||||
|
|
||||||
|
The list of tags are as follows:
|
||||||
|
* `a` (required) reference tag to kind `31922` or `31923` calendar event being responded to.
|
||||||
|
* `d` (required) universally unique identifier. Generated by the client creating the calendar event RSVP.
|
||||||
|
* `status` (required) `accepted`, `declined`, or `tentative`. Determines attendance status to the referenced calendar event.
|
||||||
|
* `fb` (optional) `free` or `busy`. Determines if the user would be free or busy for the duration of the calendar event. This tag must be omitted or ignored if the `status` label is set to `declined`.
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"id": <32-bytes lowercase hex-encoded SHA-256 of the the serialized event data>,
|
||||||
|
"pubkey": <32-bytes lowercase hex-encoded public key of the event creator>,
|
||||||
|
"created_at": <Unix timestamp in seconds>,
|
||||||
|
"kind": 31925,
|
||||||
|
"content": "<note>",
|
||||||
|
"tags": [
|
||||||
|
["a", "<31922 or 31923>:<calendar event author pubkey>:<d-identifier of calendar event>", "<optional relay url>"],
|
||||||
|
["d", "<UUID>"],
|
||||||
|
["status", "<accepted/declined/tentative>"],
|
||||||
|
["fb", "<free/busy>"],
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## Unsolved Limitations
|
||||||
|
|
||||||
|
* No private events
|
||||||
|
|
||||||
|
## Intentionally Unsupported Scenarios
|
||||||
|
|
||||||
|
### Recurring Calendar Events
|
||||||
|
|
||||||
|
Recurring calendar events come with a lot of complexity, making it difficult for software and humans to deal with. This complexity includes time zone differences between invitees, daylight savings, leap years, multiple calendar systems, one-off changes in schedule or other metadata, etc.
|
||||||
|
|
||||||
|
This NIP intentionally omits support for recurring calendar events and pushes that complexity up to clients to manually implement if they desire. i.e., individual calendar events with duplicated metadata represent recurring calendar events.
|
||||||
122
53.md
Normal file
122
53.md
Normal file
|
|
@ -0,0 +1,122 @@
|
||||||
|
NIP-53
|
||||||
|
======
|
||||||
|
|
||||||
|
Live Activities
|
||||||
|
---------------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
Service providers want to offer live activities to the Nostr network in such a way that participants can easily log and query by clients. This NIP describes a general framework to advertise the involvement of pubkeys in such live activities.
|
||||||
|
|
||||||
|
## Concepts
|
||||||
|
|
||||||
|
### Live Event
|
||||||
|
|
||||||
|
A special event with `kind:30311` "Live Event" is defined as a _parameterized replaceable event_ of public `p` tags. Each `p` tag SHOULD have a **displayable** marker name for the current role (e.g. `Host`, `Speaker`, `Participant`) of the user in the event and the relay information MAY be empty. This event will be constantly updated as participants join and leave the activity.
|
||||||
|
|
||||||
|
For example:
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"kind": 30311,
|
||||||
|
"tags": [
|
||||||
|
["d", "<unique identifier>"],
|
||||||
|
["title", "<name of the event>"],
|
||||||
|
["summary", "<description>"],
|
||||||
|
["image", "<preview image url>"],
|
||||||
|
["t", "hashtag"]
|
||||||
|
["streaming", "<url>"],
|
||||||
|
["recording", "<url>"], // used to place the edited video once the activity is over
|
||||||
|
["starts", "<unix timestamp in seconds>"],
|
||||||
|
["ends", "<unix timestamp in seconds>"],
|
||||||
|
["status", "<planned, live, ended>"],
|
||||||
|
["current_participants", "<number>"],
|
||||||
|
["total_participants", "<number>"],
|
||||||
|
["p", "91cf9..4e5ca", "wss://provider1.com/", "Host", "<proof>"],
|
||||||
|
["p", "14aeb..8dad4", "wss://provider2.com/nostr", "Speaker"],
|
||||||
|
["p", "612ae..e610f", "ws://provider3.com/ws", "Participant"],
|
||||||
|
["relays", "wss://one.com", "wss://two.com", ...]
|
||||||
|
],
|
||||||
|
"content": "",
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
A distinct `d` tag should be used for each activity. All other tags are optional.
|
||||||
|
|
||||||
|
Providers SHOULD keep the participant list small (e.g. under 1000 users) and, when limits are reached, Providers SHOULD select which participants get named in the event. Clients should not expect a comprehensive list. Once the activity ends, the event can be deleted or updated to summarize the activity and provide async content (e.g. recording of the event).
|
||||||
|
|
||||||
|
Clients are expected to subscribe to `kind:30311` events in general or for given follow lists and statuses. Clients MAY display participants' roles in activities as well as access points to join the activity.
|
||||||
|
|
||||||
|
Live Activity management clients are expected to constantly update `kind:30311` during the event. Clients MAY choose to consider `status=live` events after 1hr without any update as `ended`. The `starts` and `ends` timestamp SHOULD be updated when the status changes to and from `live`
|
||||||
|
|
||||||
|
The activity MUST be linked to using the [NIP-19](19.md) `naddr` code along with the `a` tag.
|
||||||
|
|
||||||
|
### Proof of Agreement to Participate
|
||||||
|
|
||||||
|
Event owners can add proof as the 5th term in each `p` tag to clarify the participant's agreement in joining the event. The proof is a signed SHA256 of the complete `a` Tag of the event (`kind:pubkey:dTag`) by each `p`'s private key, encoded in hex.
|
||||||
|
|
||||||
|
Clients MAY only display participants if the proof is available or MAY display participants as "invited" if the proof is not available.
|
||||||
|
|
||||||
|
This feature is important to avoid malicious event owners adding large account holders to the event, without their knowledge, to lure their followers into the malicious owner's trap.
|
||||||
|
|
||||||
|
### Live Chat Message
|
||||||
|
|
||||||
|
Event `kind:1311` is live chat's channel message. Clients MUST include the `a` tag of the activity with a `root` marker. Other Kind-1 tags such as `reply` and `mention` can also be used.
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"kind": 1311,
|
||||||
|
"tags": [
|
||||||
|
["a", "30311:<Community event author pubkey>:<d-identifier of the community>", "<Optional relay url>", "root"],
|
||||||
|
],
|
||||||
|
"content": "Zaps to live streams is beautiful.",
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## Use Cases
|
||||||
|
|
||||||
|
Common use cases include meeting rooms/workshops, watch-together activities, or event spaces, such as [zap.stream](https://zap.stream).
|
||||||
|
|
||||||
|
## Example
|
||||||
|
|
||||||
|
### Live Streaming
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"id": "57f28dbc264990e2c61e80a883862f7c114019804208b14da0bff81371e484d2",
|
||||||
|
"pubkey": "1597246ac22f7d1375041054f2a4986bd971d8d196d7997e48973263ac9879ec",
|
||||||
|
"created_at": 1687182672,
|
||||||
|
"kind": 30311,
|
||||||
|
"tags": [
|
||||||
|
["d", "demo-cf-stream"],
|
||||||
|
["title", "Adult Swim Metalocalypse"],
|
||||||
|
["summary", "Live stream from IPTV-ORG collection"],
|
||||||
|
["streaming", "https://adultswim-vodlive.cdn.turner.com/live/metalocalypse/stream.m3u8"],
|
||||||
|
["starts", "1687182672"],
|
||||||
|
["status", "live"],
|
||||||
|
["t", "animation"],
|
||||||
|
["t", "iptv"],
|
||||||
|
["image", "https://i.imgur.com/CaKq6Mt.png"]
|
||||||
|
],
|
||||||
|
"content": "",
|
||||||
|
"sig": "5bc7a60f5688effa5287244a24768cbe0dcd854436090abc3bef172f7f5db1410af4277508dbafc4f70a754a891c90ce3b966a7bc47e7c1eb71ff57640f3d389"
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
### Live Streaming chat message
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"id": "97aa81798ee6c5637f7b21a411f89e10244e195aa91cb341bf49f718e36c8188",
|
||||||
|
"pubkey": "3f770d65d3a764a9c5cb503ae123e62ec7598ad035d836e2a810f3877a745b24",
|
||||||
|
"created_at": 1687286726,
|
||||||
|
"kind": 1311,
|
||||||
|
"tags": [
|
||||||
|
["a", "30311:1597246ac22f7d1375041054f2a4986bd971d8d196d7997e48973263ac9879ec:demo-cf-stream", "", "root"]
|
||||||
|
],
|
||||||
|
"content": "Zaps to live streams is beautiful.",
|
||||||
|
"sig": "997f62ddfc0827c121043074d50cfce7a528e978c575722748629a4137c45b75bdbc84170bedc723ef0a5a4c3daebf1fef2e93f5e2ddb98e5d685d022c30b622"
|
||||||
|
}
|
||||||
|
````
|
||||||
117
54.md
Normal file
117
54.md
Normal file
|
|
@ -0,0 +1,117 @@
|
||||||
|
NIP-54
|
||||||
|
======
|
||||||
|
|
||||||
|
Wiki
|
||||||
|
----
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
This NIP defines `kind:30818` (a _parameterized replaceable event_) for long-form text content similar to [NIP-23](23.md), but with one important difference: articles are meant to be descriptions, or encyclopedia entries, of particular subjects, and it's expected that multiple people will write articles about the exact same subjects, with either small variations or completely independent content.
|
||||||
|
|
||||||
|
Articles are identified by lowercase, normalized ascii `d` tags.
|
||||||
|
|
||||||
|
### Articles
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"content": "A wiki is a hypertext publication collaboratively edited and managed by its own audience.",
|
||||||
|
"tags": [
|
||||||
|
["d", "wiki"],
|
||||||
|
["title", "Wiki"],
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
### `d` tag normalization rules
|
||||||
|
|
||||||
|
- Any non-letter character MUST be converted to a `-`.
|
||||||
|
- All letters MUST be converted to lowercase.
|
||||||
|
|
||||||
|
### Content rules
|
||||||
|
|
||||||
|
The content should be Markdown, following the same rules as of [NIP-23](23.md), although it takes some extra (optional) metadata tags:
|
||||||
|
|
||||||
|
- `title`: for when the display title should be different from the `d` tag.
|
||||||
|
- `summary`: for display in lists.
|
||||||
|
- `a` and `e`: for referencing the original event a wiki article was forked from.
|
||||||
|
|
||||||
|
One extra functionality is added: **wikilinks**. Unlike normal Markdown links `[]()` that link to webpages, wikilinks `[[]]` link to other articles in the wiki. In this case, the wiki is the entirety of Nostr. Clicking on a wikilink should cause the client to ask relays for events with `d` tags equal to the target of that wikilink.
|
||||||
|
|
||||||
|
Wikilinks can take these two forms:
|
||||||
|
|
||||||
|
1. `[[Target Page]]` -- in this case it will link to the page `target-page` (according to `d` tag normalization rules above) and be displayed as `Target Page`;
|
||||||
|
2. `[[target page|see this]]` -- in this case it will link to the page `target-page`, but will be displayed as `see this`.
|
||||||
|
|
||||||
|
### Merge Requests
|
||||||
|
|
||||||
|
Event `kind:818` represents a request to merge from a forked article into the source. It is directed to a pubkey and references the original article and the modified event.
|
||||||
|
|
||||||
|
[INSERT EVENT EXAMPLE]
|
||||||
|
|
||||||
|
### Redirects
|
||||||
|
|
||||||
|
Event `kind:30819` is also defined to stand for "wiki redirects", i.e. if one thinks `Shell structure` should redirect to `Thin-shell structure` they can issue one of these events instead of replicating the content. These events can be used for automatically redirecting between articles on a client, but also for generating crowdsourced "disambiguation" pages ([common in Wikipedia](https://en.wikipedia.org/wiki/Help:Disambiguation)).
|
||||||
|
|
||||||
|
[INSERT EVENT EXAMPLE]
|
||||||
|
|
||||||
|
How to decide what article to display
|
||||||
|
-------------------------------------
|
||||||
|
|
||||||
|
As there could be many articles for each given name, some kind of prioritization must be done by clients. Criteria for this should vary between users and clients, but some means that can be used are described below:
|
||||||
|
|
||||||
|
### Reactions
|
||||||
|
|
||||||
|
[NIP-25](25.md) reactions are very simple and can be used to create a simple web-of-trust between wiki article writers and their content. While just counting a raw number of "likes" is unproductive, reacting to any wiki article event with a `+` can be interpreted as a recommendation for that article specifically and a partial recommendation of the author of that article. When 2 or 3-level deep recommendations are followed, suddenly a big part of all the articles may have some form of tagging.
|
||||||
|
|
||||||
|
### Relays
|
||||||
|
|
||||||
|
[NIP-51](51.md) lists of relays can be created with the kind 10102 and then used by wiki clients in order to determine where to query articles first and to rank these differently in relation to other events fetched from other relays.
|
||||||
|
|
||||||
|
### Contact lists
|
||||||
|
|
||||||
|
[NIP-02](02.md) contact lists can form the basis of a recommendation system that is then expanded with relay lists and reaction lists through nested queries. These lists form a good starting point only because they are so widespread.
|
||||||
|
|
||||||
|
### Wiki-related contact lists
|
||||||
|
|
||||||
|
[NIP-51](51.md) lists can also be used to create a list of users that are trusted only in the context of wiki authorship or wiki curationship.
|
||||||
|
|
||||||
|
Forks
|
||||||
|
---------
|
||||||
|
Wiki-events can tag other wiki-events with a `fork` marker to specify that this event came from a different version. Both `a` and `e` tags SHOULD be used and have the `fork` marker applied, to identify the exact version it was forked from.
|
||||||
|
|
||||||
|
Deference
|
||||||
|
---------
|
||||||
|
Wiki-events can tag other wiki-events with a `defer` marker to indicate that it considers someone else's entry as a "better" version of itself. If using a `defer` marker both `a` and `e` tags SHOULD be used.
|
||||||
|
|
||||||
|
This is a stronger signal of trust than a `+` reaction.
|
||||||
|
|
||||||
|
This marker is useful when a user edits someone else's entry; if the original author includes the editor's changes and the editor doesn't want to keep/maintain an independent version, the `link` tag could effectively be a considered a "deletion" of the editor's version and putting that pubkey's WoT weight behind the original author's version.
|
||||||
|
|
||||||
|
Why Markdown?
|
||||||
|
-------------
|
||||||
|
|
||||||
|
If the idea is to make a wiki then the most obvious text format to use is probably the mediawiki/wikitext format used by Wikipedia since it's widely deployed in all mediawiki installations and used for decades with great success. However, it turns out that format is very bloated and convoluted, has way too many features and probably because of that it doesn't have many alternative implementations out there, and the ones that exist are not complete and don't look very trustworthy. Also it is very much a centralized format that can probably be changed at the whims of the Wikipedia owners.
|
||||||
|
|
||||||
|
On the other hand, Markdown has proven to work well for small scale wikis and one of the biggest wikis in the planet (which is not very often thought of as a wiki), [StackOverflow](https://stackoverflow.com) and its child sites, and also one of the biggest "personal wiki" software, [Obsidian](https://obsidian.md/). Markdown can probably deliver 95% of the functionality of wikitext. When augmented with tables, diagram generators and MathJax (which are common extensions that exist in the wild and can be included in this NIP) that rate probably goes to 99%, and its simplicity is a huge benefit that can't be overlooked. Wikitext format can also be transpíled into Markdown using Pandoc. Given all that, I think it's a reasonable suspicion that mediawiki is not inherently better than Markdown, the success of Wikipedia probably cannot be predicated on the syntax language choice.
|
||||||
|
|
||||||
|
# Appendix 1: Merge requests
|
||||||
|
Users can request other users to get their entries merged into someone else's entry by creating a `kind:818` event.
|
||||||
|
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"content": "I added information about how to make hot ice-creams",
|
||||||
|
"kind": 818,
|
||||||
|
"tags": [
|
||||||
|
[ "a", "30818:<destination-pubkey>:hot-ice-creams", "<relay-url>" ],
|
||||||
|
[ "e", "<version-against-which-the-modification-was-made>", "<relay-url>' ],
|
||||||
|
[ "p", "<destination-pubkey>" ],
|
||||||
|
[ "e", "<version-to-be-merged>", "<relay-url>", "source" ]
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
`.content`: an optional explanation detailing why this merge is being requested.
|
||||||
|
`a` tag: tag of the article which should be modified (i.e. the target of this merge request).
|
||||||
|
`e` tag: optional version of the article in which this modifications is based
|
||||||
|
`e` tag with `source` marker: the ID of the event that should be merged. This event id MUST be of a `kind:30818` as defined in this NIP.
|
||||||
|
|
||||||
|
The destination-pubkey (the pubkey being requested to merge something into their article can create [[NIP-25]] reactions that tag the `kind:818` event with `+` or `-`
|
||||||
24
56.md
24
56.md
|
|
@ -1,16 +1,17 @@
|
||||||
|
|
||||||
NIP-56
|
NIP-56
|
||||||
======
|
======
|
||||||
|
|
||||||
Reporting
|
Reporting
|
||||||
---------
|
---------
|
||||||
|
|
||||||
`draft` `optional` `author:jb55`
|
`optional`
|
||||||
|
|
||||||
A report is a `kind 1984` note that is used to report other notes for spam,
|
A report is a `kind 1984` event that signals to users and relays that
|
||||||
illegal and explicit content.
|
some referenced content is objectionable. The definition of objectionable is
|
||||||
|
obviously subjective and all agents on the network (users, apps, relays, etc.)
|
||||||
|
may consume and take action on them as they see fit.
|
||||||
|
|
||||||
The content MAY contain additional information submitted by the entity
|
The `content` MAY contain additional information submitted by the entity
|
||||||
reporting the content.
|
reporting the content.
|
||||||
|
|
||||||
Tags
|
Tags
|
||||||
|
|
@ -25,10 +26,12 @@ A `report type` string MUST be included as the 3rd entry to the `e` or `p` tag
|
||||||
being reported, which consists of the following report types:
|
being reported, which consists of the following report types:
|
||||||
|
|
||||||
- `nudity` - depictions of nudity, porn, etc.
|
- `nudity` - depictions of nudity, porn, etc.
|
||||||
|
- `malware` - virus, trojan horse, worm, robot, spyware, adware, back door, ransomware, rootkit, kidnapper, etc.
|
||||||
- `profanity` - profanity, hateful speech, etc.
|
- `profanity` - profanity, hateful speech, etc.
|
||||||
- `illegal` - something which may be illegal in some jurisdiction
|
- `illegal` - something which may be illegal in some jurisdiction
|
||||||
- `spam` - spam
|
- `spam` - spam
|
||||||
- `impersonation` - someone pretending to be someone else
|
- `impersonation` - someone pretending to be someone else
|
||||||
|
- `other` - for reports that don't fit in the above categories
|
||||||
|
|
||||||
Some report tags only make sense for profile reports, such as `impersonation`
|
Some report tags only make sense for profile reports, such as `impersonation`
|
||||||
|
|
||||||
|
|
@ -42,9 +45,9 @@ Example events
|
||||||
{
|
{
|
||||||
"kind": 1984,
|
"kind": 1984,
|
||||||
"tags": [
|
"tags": [
|
||||||
["p", <pubkey>, "nudity"]
|
["p", <pubkey>, "nudity"],
|
||||||
["L", "social.nos.ontology"],
|
["L", "social.nos.ontology"],
|
||||||
["l", "NS-nud", "social.nos.ontology"],
|
["l", "NS-nud", "social.nos.ontology"]
|
||||||
],
|
],
|
||||||
"content": "",
|
"content": "",
|
||||||
...
|
...
|
||||||
|
|
@ -63,10 +66,9 @@ Example events
|
||||||
{
|
{
|
||||||
"kind": 1984,
|
"kind": 1984,
|
||||||
"tags": [
|
"tags": [
|
||||||
["p", <impersonator pubkey>, "impersonation"],
|
["p", <impersonator pubkey>, "impersonation"]
|
||||||
["p", <victim pubkey>]
|
|
||||||
],
|
],
|
||||||
"content": "Profile is imitating #[1]",
|
"content": "Profile is impersonating nostr:<victim bech32 pubkey>",
|
||||||
...
|
...
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
@ -75,7 +77,7 @@ Client behavior
|
||||||
---------------
|
---------------
|
||||||
|
|
||||||
Clients can use reports from friends to make moderation decisions if they
|
Clients can use reports from friends to make moderation decisions if they
|
||||||
choose to. For instance, if 3+ of your friends report a profile as explicit,
|
choose to. For instance, if 3+ of your friends report a profile for `nudity`,
|
||||||
clients can have an option to automatically blur photos from said account.
|
clients can have an option to automatically blur photos from said account.
|
||||||
|
|
||||||
|
|
||||||
|
|
|
||||||
33
57.md
33
57.md
|
|
@ -4,7 +4,7 @@ NIP-57
|
||||||
Lightning Zaps
|
Lightning Zaps
|
||||||
--------------
|
--------------
|
||||||
|
|
||||||
`draft` `optional` `author:jb55` `author:kieran`
|
`draft` `optional`
|
||||||
|
|
||||||
This NIP defines two new event types for recording lightning payments between users. `9734` is a `zap request`, representing a payer's request to a recipient's lightning wallet for an invoice. `9735` is a `zap receipt`, representing the confirmation by the recipient's lightning wallet that the invoice issued in response to a `zap request` has been paid.
|
This NIP defines two new event types for recording lightning payments between users. `9734` is a `zap request`, representing a payer's request to a recipient's lightning wallet for an invoice. `9735` is a `zap receipt`, representing the confirmation by the recipient's lightning wallet that the invoice issued in response to a `zap request` has been paid.
|
||||||
|
|
||||||
|
|
@ -36,7 +36,7 @@ A `zap request` is an event of kind `9734` that is _not_ published to relays, bu
|
||||||
In addition, the event MAY include the following tags:
|
In addition, the event MAY include the following tags:
|
||||||
|
|
||||||
- `e` is an optional hex-encoded event id. Clients MUST include this if zapping an event rather than a person.
|
- `e` is an optional hex-encoded event id. Clients MUST include this if zapping an event rather than a person.
|
||||||
- `a` is an optional NIP-33 event coordinate that allows tipping parameterized replaceable events such as NIP-23 long-form notes.
|
- `a` is an optional event coordinate that allows tipping parameterized replaceable events such as NIP-23 long-form notes.
|
||||||
|
|
||||||
Example:
|
Example:
|
||||||
|
|
||||||
|
|
@ -45,7 +45,7 @@ Example:
|
||||||
"kind": 9734,
|
"kind": 9734,
|
||||||
"content": "Zap!",
|
"content": "Zap!",
|
||||||
"tags": [
|
"tags": [
|
||||||
["relays", "wss://nostr-pub.wellorder.com"],
|
["relays", "wss://nostr-pub.wellorder.com", "wss://anotherrelay.example.com"],
|
||||||
["amount", "21000"],
|
["amount", "21000"],
|
||||||
["lnurl", "lnurl1dp68gurn8ghj7um5v93kketj9ehx2amn9uh8wetvdskkkmn0wahz7mrww4excup0dajx2mrv92x9xp"],
|
["lnurl", "lnurl1dp68gurn8ghj7um5v93kketj9ehx2amn9uh8wetvdskkkmn0wahz7mrww4excup0dajx2mrv92x9xp"],
|
||||||
["p", "04c915daefee38317fa734444acee390a8269fe5810b2241e5e6dd343dfbecc9"],
|
["p", "04c915daefee38317fa734444acee390a8269fe5810b2241e5e6dd343dfbecc9"],
|
||||||
|
|
@ -66,7 +66,7 @@ A signed `zap request` event is not published, but is instead sent using a HTTP
|
||||||
- `nostr` is the `9734` `zap request` event, JSON encoded then URI encoded
|
- `nostr` is the `9734` `zap request` event, JSON encoded then URI encoded
|
||||||
- `lnurl` is the lnurl pay url of the recipient, encoded using bech32 with the prefix `lnurl`
|
- `lnurl` is the lnurl pay url of the recipient, encoded using bech32 with the prefix `lnurl`
|
||||||
|
|
||||||
This request should return a JSON response with a `pr` key, which is the invoice the sender must pay to finalize his zap. Here is an example flow:
|
This request should return a JSON response with a `pr` key, which is the invoice the sender must pay to finalize his zap. Here is an example flow in javascript:
|
||||||
|
|
||||||
```javascript
|
```javascript
|
||||||
const senderPubkey // The sender's pubkey
|
const senderPubkey // The sender's pubkey
|
||||||
|
|
@ -78,7 +78,7 @@ const sats = 21
|
||||||
const amount = sats * 1000
|
const amount = sats * 1000
|
||||||
const relays = ['wss://nostr-pub.wellorder.net']
|
const relays = ['wss://nostr-pub.wellorder.net']
|
||||||
const event = encodeURI(JSON.stringify(await signEvent({
|
const event = encodeURI(JSON.stringify(await signEvent({
|
||||||
kind: [9734],
|
kind: 9734,
|
||||||
content: "",
|
content: "",
|
||||||
pubkey: senderPubkey,
|
pubkey: senderPubkey,
|
||||||
created_at: Math.round(Date.now() / 1000),
|
created_at: Math.round(Date.now() / 1000),
|
||||||
|
|
@ -110,7 +110,8 @@ When a client sends a `zap request` event to a server's lnurl-pay callback URL,
|
||||||
4. It MUST have 0 or 1 `e` tags
|
4. It MUST have 0 or 1 `e` tags
|
||||||
5. There should be a `relays` tag with the relays to send the `zap receipt` to.
|
5. There should be a `relays` tag with the relays to send the `zap receipt` to.
|
||||||
6. If there is an `amount` tag, it MUST be equal to the `amount` query parameter.
|
6. If there is an `amount` tag, it MUST be equal to the `amount` query parameter.
|
||||||
7. If there is an `a` tag, it MUST be a valid NIP-33 event coordinate
|
7. If there is an `a` tag, it MUST be a valid event coordinate
|
||||||
|
8. There MUST be 0 or 1 `P` tags. If there is one, it MUST be equal to the `zap receipt`'s `pubkey`.
|
||||||
|
|
||||||
The event MUST then be stored for use later, when the invoice is paid.
|
The event MUST then be stored for use later, when the invoice is paid.
|
||||||
|
|
||||||
|
|
@ -126,9 +127,9 @@ When receiving a payment, the following steps are executed:
|
||||||
|
|
||||||
The following should be true of the `zap receipt` event:
|
The following should be true of the `zap receipt` event:
|
||||||
|
|
||||||
- The content SHOULD be empty.
|
- The `content` SHOULD be empty.
|
||||||
- The `created_at` date SHOULD be set to the invoice `paid_at` date for idempotency.
|
- The `created_at` date SHOULD be set to the invoice `paid_at` date for idempotency.
|
||||||
- `tags` MUST include the `p` tag AND optional `e` tag from the `zap request`.
|
- `tags` MUST include the `p` tag (zap recipient) AND optional `e` tag from the `zap request` AND optional `a` tag from the `zap request` AND optional `P` tag from the pubkey of the zap request (zap sender).
|
||||||
- The `zap receipt` MUST have a `bolt11` tag containing the description hash bolt11 invoice.
|
- The `zap receipt` MUST have a `bolt11` tag containing the description hash bolt11 invoice.
|
||||||
- The `zap receipt` MUST contain a `description` tag which is the JSON-encoded invoice description.
|
- The `zap receipt` MUST contain a `description` tag which is the JSON-encoded invoice description.
|
||||||
- `SHA256(description)` MUST match the description hash in the bolt11 invoice.
|
- `SHA256(description)` MUST match the description hash in the bolt11 invoice.
|
||||||
|
|
@ -148,13 +149,13 @@ Example `zap receipt`:
|
||||||
"kind": 9735,
|
"kind": 9735,
|
||||||
"tags": [
|
"tags": [
|
||||||
["p", "32e1827635450ebb3c5a7d12c1f8e7b2b514439ac10a67eef3d9fd9c5c68e245"],
|
["p", "32e1827635450ebb3c5a7d12c1f8e7b2b514439ac10a67eef3d9fd9c5c68e245"],
|
||||||
|
["P", "97c70a44366a6535c145b333f973ea86dfdc2d7a99da618c40c64705ad98e322"],
|
||||||
["e", "3624762a1274dd9636e0c552b53086d70bc88c165bc4dc0f9e836a1eaf86c3b8"],
|
["e", "3624762a1274dd9636e0c552b53086d70bc88c165bc4dc0f9e836a1eaf86c3b8"],
|
||||||
["bolt11", "lnbc10u1p3unwfusp5t9r3yymhpfqculx78u027lxspgxcr2n2987mx2j55nnfs95nxnzqpp5jmrh92pfld78spqs78v9euf2385t83uvpwk9ldrlvf6ch7tpascqhp5zvkrmemgth3tufcvflmzjzfvjt023nazlhljz2n9hattj4f8jq8qxqyjw5qcqpjrzjqtc4fc44feggv7065fqe5m4ytjarg3repr5j9el35xhmtfexc42yczarjuqqfzqqqqqqqqlgqqqqqqgq9q9qxpqysgq079nkq507a5tw7xgttmj4u990j7wfggtrasah5gd4ywfr2pjcn29383tphp4t48gquelz9z78p4cq7ml3nrrphw5w6eckhjwmhezhnqpy6gyf0"],
|
["bolt11", "lnbc10u1p3unwfusp5t9r3yymhpfqculx78u027lxspgxcr2n2987mx2j55nnfs95nxnzqpp5jmrh92pfld78spqs78v9euf2385t83uvpwk9ldrlvf6ch7tpascqhp5zvkrmemgth3tufcvflmzjzfvjt023nazlhljz2n9hattj4f8jq8qxqyjw5qcqpjrzjqtc4fc44feggv7065fqe5m4ytjarg3repr5j9el35xhmtfexc42yczarjuqqfzqqqqqqqqlgqqqqqqgq9q9qxpqysgq079nkq507a5tw7xgttmj4u990j7wfggtrasah5gd4ywfr2pjcn29383tphp4t48gquelz9z78p4cq7ml3nrrphw5w6eckhjwmhezhnqpy6gyf0"],
|
||||||
["description", "{\"pubkey\":\"32e1827635450ebb3c5a7d12c1f8e7b2b514439ac10a67eef3d9fd9c5c68e245\",\"content\":\"\",\"id\":\"d9cc14d50fcb8c27539aacf776882942c1a11ea4472f8cdec1dea82fab66279d\",\"created_at\":1674164539,\"sig\":\"77127f636577e9029276be060332ea565deaf89ff215a494ccff16ae3f757065e2bc59b2e8c113dd407917a010b3abd36c8d7ad84c0e3ab7dab3a0b0caa9835d\",\"kind\":9734,\"tags\":[[\"e\",\"3624762a1274dd9636e0c552b53086d70bc88c165bc4dc0f9e836a1eaf86c3b8\"],[\"p\",\"32e1827635450ebb3c5a7d12c1f8e7b2b514439ac10a67eef3d9fd9c5c68e245\"],[\"relays\",\"wss://relay.damus.io\",\"wss://nostr-relay.wlvs.space\",\"wss://nostr.fmt.wiz.biz\",\"wss://relay.nostr.bg\",\"wss://nostr.oxtr.dev\",\"wss://nostr.v0l.io\",\"wss://brb.io\",\"wss://nostr.bitcoiner.social\",\"ws://monad.jb55.com:8080\",\"wss://relay.snort.social\"]]}"],
|
["description", "{\"pubkey\":\"97c70a44366a6535c145b333f973ea86dfdc2d7a99da618c40c64705ad98e322\",\"content\":\"\",\"id\":\"d9cc14d50fcb8c27539aacf776882942c1a11ea4472f8cdec1dea82fab66279d\",\"created_at\":1674164539,\"sig\":\"77127f636577e9029276be060332ea565deaf89ff215a494ccff16ae3f757065e2bc59b2e8c113dd407917a010b3abd36c8d7ad84c0e3ab7dab3a0b0caa9835d\",\"kind\":9734,\"tags\":[[\"e\",\"3624762a1274dd9636e0c552b53086d70bc88c165bc4dc0f9e836a1eaf86c3b8\"],[\"p\",\"32e1827635450ebb3c5a7d12c1f8e7b2b514439ac10a67eef3d9fd9c5c68e245\"],[\"relays\",\"wss://relay.damus.io\",\"wss://nostr-relay.wlvs.space\",\"wss://nostr.fmt.wiz.biz\",\"wss://relay.nostr.bg\",\"wss://nostr.oxtr.dev\",\"wss://nostr.v0l.io\",\"wss://brb.io\",\"wss://nostr.bitcoiner.social\",\"ws://monad.jb55.com:8080\",\"wss://relay.snort.social\"]]}"],
|
||||||
["preimage", "5d006d2cf1e73c7148e7519a4c68adc81642ce0e25a432b2434c99f97344c15f"]
|
["preimage", "5d006d2cf1e73c7148e7519a4c68adc81642ce0e25a432b2434c99f97344c15f"]
|
||||||
],
|
],
|
||||||
"content": "",
|
"content": "",
|
||||||
"sig": "b0a3c5c984ceb777ac455b2f659505df51585d5fd97a0ec1fdb5f3347d392080d4b420240434a3afd909207195dac1e2f7e3df26ba862a45afd8bfe101c2b1cc"
|
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
|
|
@ -166,18 +167,22 @@ A client can retrieve `zap receipt`s on events and pubkeys using a NIP-01 filter
|
||||||
- The `invoiceAmount` contained in the `bolt11` tag of the `zap receipt` MUST equal the `amount` tag of the `zap request` (if present).
|
- The `invoiceAmount` contained in the `bolt11` tag of the `zap receipt` MUST equal the `amount` tag of the `zap request` (if present).
|
||||||
- The `lnurl` tag of the `zap request` (if present) SHOULD equal the recipient's `lnurl`.
|
- The `lnurl` tag of the `zap request` (if present) SHOULD equal the recipient's `lnurl`.
|
||||||
|
|
||||||
### Appendix G: `zap` tag on zapped event
|
### Appendix G: `zap` tag on other events
|
||||||
|
|
||||||
When an event includes a `zap` tag, clients SHOULD calculate the lnurl pay request based on its value instead of the profile's field. An optional third argument on the tag specifies the type of value, either `lud06` or `lud16`.
|
When an event includes one or more `zap` tags, clients wishing to zap it SHOULD calculate the lnurl pay request based on the tags value instead of the event author's profile field. The tag's second argument is the `hex` string of the receiver's pub key and the third argument is the relay to download the receiver's metadata (Kind-0). An optional fourth parameter specifies the weight (a generalization of a percentage) assigned to the respective receiver. Clients should parse all weights, calculate a sum, and then a percentage to each receiver. If weights are not present, CLIENTS should equally divide the zap amount to all receivers. If weights are only partially present, receivers without a weight should not be zapped (`weight = 0`).
|
||||||
|
|
||||||
```json
|
```js
|
||||||
{
|
{
|
||||||
"tags": [
|
"tags": [
|
||||||
[ "zap", "pablo@f7z.io", "lud16" ]
|
[ "zap", "82341f882b6eabcd2ba7f1ef90aad961cf074af15b9ef44a09f9d2a8fbfbe6a2", "wss://nostr.oxtr.dev", "1" ], // 25%
|
||||||
|
[ "zap", "fa984bd7dbb282f07e16e7ae87b26a2a7b9b90b7246a44771f0cf5ae58018f52", "wss://nostr.wine/", "1" ], // 25%
|
||||||
|
[ "zap", "460c25e682fda7832b52d1f22d3d22b3176d972f60dcdc3212ed8c92ef85065c", "wss://nos.lol/", "2" ] // 50%
|
||||||
]
|
]
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
|
Clients MAY display the zap split configuration in the note.
|
||||||
|
|
||||||
## Future Work
|
## Future Work
|
||||||
|
|
||||||
Zaps can be extended to be more private by encrypting `zap request` notes to the target user, but for simplicity it has been left out of this initial draft.
|
Zaps can be extended to be more private by encrypting `zap request` notes to the target user, but for simplicity it has been left out of this initial draft.
|
||||||
|
|
|
||||||
22
58.md
22
58.md
|
|
@ -4,20 +4,14 @@ NIP-58
|
||||||
Badges
|
Badges
|
||||||
------
|
------
|
||||||
|
|
||||||
`draft` `optional` `author:cameri`
|
`draft` `optional`
|
||||||
|
|
||||||
Three special events are used to define, award and display badges in
|
Three special events are used to define, award and display badges in
|
||||||
user profiles:
|
user profiles:
|
||||||
|
|
||||||
1. A "Badge Definition" event is defined as a parameterized replaceable event
|
1. A "Badge Definition" event is defined as a parameterized replaceable event with kind `30009` having a `d` tag with a value that uniquely identifies the badge (e.g. `bravery`) published by the badge issuer. Badge definitions can be updated.
|
||||||
with kind `30009` having a `d` tag with a value that uniquely identifies
|
|
||||||
the badge (e.g. `bravery`) published by the badge issuer. Badge definitions can
|
|
||||||
be updated.
|
|
||||||
|
|
||||||
2. A "Badge Award" event is a kind `8` event with a single `a` tag referencing
|
2. A "Badge Award" event is a kind `8` event with a single `a` tag referencing a "Badge Definition" event and one or more `p` tags, one for each pubkey the badge issuer wishes to award. Awarded badges are immutable and non-transferrable.
|
||||||
a "Define Badge" event and one or more `p` tags, one for each pubkey the
|
|
||||||
badge issuer wishes to award. The value for the `a` tag MUST follow the format
|
|
||||||
defined in [NIP-33](33.md). Awarded badges are immutable and non-transferrable.
|
|
||||||
|
|
||||||
3. A "Profile Badges" event is defined as a parameterized replaceable event
|
3. A "Profile Badges" event is defined as a parameterized replaceable event
|
||||||
with kind `30008` with a `d` tag with the value `profile_badges`.
|
with kind `30008` with a `d` tag with the value `profile_badges`.
|
||||||
|
|
@ -34,7 +28,7 @@ The following tags MAY be present:
|
||||||
- A `name` tag with a short name for the badge.
|
- A `name` tag with a short name for the badge.
|
||||||
- `image` tag whose value is the URL of a high-resolution image representing the badge. The second value optionally specifies the dimensions of the image as `width`x`height` in pixels. Badge recommended dimensions is 1024x1024 pixels.
|
- `image` tag whose value is the URL of a high-resolution image representing the badge. The second value optionally specifies the dimensions of the image as `width`x`height` in pixels. Badge recommended dimensions is 1024x1024 pixels.
|
||||||
- A `description` tag whose value MAY contain a textual representation of the
|
- A `description` tag whose value MAY contain a textual representation of the
|
||||||
image, the meaning behind the badge, or the reason of it's issuance.
|
image, the meaning behind the badge, or the reason of its issuance.
|
||||||
- One or more `thumb` tags whose first value is an URL pointing to a thumbnail version of the image referenced in the `image` tag. The second value optionally specifies the dimensions of the thumbnail as `width`x`height` in pixels.
|
- One or more `thumb` tags whose first value is an URL pointing to a thumbnail version of the image referenced in the `image` tag. The second value optionally specifies the dimensions of the thumbnail as `width`x`height` in pixels.
|
||||||
|
|
||||||
### Badge Award event
|
### Badge Award event
|
||||||
|
|
@ -68,8 +62,6 @@ Users MAY choose to decorate their profiles with badges for fame, notoriety, rec
|
||||||
|
|
||||||
### Recommendations
|
### Recommendations
|
||||||
|
|
||||||
Badge issuers MAY include some Proof of Work as per [NIP-13](13.md) when minting Badge Definitions or Badge Awards to embed them with a combined energy cost, arguably making them more special and valuable for users that wish to collect them.
|
|
||||||
|
|
||||||
Clients MAY whitelist badge issuers (pubkeys) for the purpose of ensuring they retain a valuable/special factor for their users.
|
Clients MAY whitelist badge issuers (pubkeys) for the purpose of ensuring they retain a valuable/special factor for their users.
|
||||||
|
|
||||||
Badge image recommended aspect ratio is 1:1 with a high-res size of 1024x1024 pixels.
|
Badge image recommended aspect ratio is 1:1 with a high-res size of 1024x1024 pixels.
|
||||||
|
|
@ -91,7 +83,7 @@ Clients SHOULD attempt to render the most appropriate badge thumbnail according
|
||||||
["name", "Medal of Bravery"],
|
["name", "Medal of Bravery"],
|
||||||
["description", "Awarded to users demonstrating bravery"],
|
["description", "Awarded to users demonstrating bravery"],
|
||||||
["image", "https://nostr.academy/awards/bravery.png", "1024x1024"],
|
["image", "https://nostr.academy/awards/bravery.png", "1024x1024"],
|
||||||
["thumb", "https://nostr.academy/awards/bravery_256x256.png", "256x256"],
|
["thumb", "https://nostr.academy/awards/bravery_256x256.png", "256x256"]
|
||||||
],
|
],
|
||||||
...
|
...
|
||||||
}
|
}
|
||||||
|
|
@ -107,7 +99,7 @@ Clients SHOULD attempt to render the most appropriate badge thumbnail according
|
||||||
"tags": [
|
"tags": [
|
||||||
["a", "30009:alice:bravery"],
|
["a", "30009:alice:bravery"],
|
||||||
["p", "bob", "wss://relay"],
|
["p", "bob", "wss://relay"],
|
||||||
["p", "charlie", "wss://relay"],
|
["p", "charlie", "wss://relay"]
|
||||||
],
|
],
|
||||||
...
|
...
|
||||||
}
|
}
|
||||||
|
|
@ -125,7 +117,7 @@ Honorable Bob The Brave:
|
||||||
["a", "30009:alice:bravery"],
|
["a", "30009:alice:bravery"],
|
||||||
["e", "<bravery badge award event id>", "wss://nostr.academy"],
|
["e", "<bravery badge award event id>", "wss://nostr.academy"],
|
||||||
["a", "30009:alice:honor"],
|
["a", "30009:alice:honor"],
|
||||||
["e", "<honor badge award event id>", "wss://nostr.academy"],
|
["e", "<honor badge award event id>", "wss://nostr.academy"]
|
||||||
],
|
],
|
||||||
...
|
...
|
||||||
}
|
}
|
||||||
|
|
|
||||||
252
59.md
Normal file
252
59.md
Normal file
|
|
@ -0,0 +1,252 @@
|
||||||
|
NIP-59
|
||||||
|
======
|
||||||
|
|
||||||
|
Gift Wrap
|
||||||
|
---------
|
||||||
|
|
||||||
|
`optional`
|
||||||
|
|
||||||
|
This NIP defines a protocol for encapsulating any nostr event. This makes it possible to obscure most metadata
|
||||||
|
for a given event, perform collaborative signing, and more.
|
||||||
|
|
||||||
|
This NIP *does not* define any messaging protocol. Applications of this NIP should be defined separately.
|
||||||
|
|
||||||
|
This NIP relies on [NIP-44](./44.md)'s versioned encryption algorithms.
|
||||||
|
|
||||||
|
# Overview
|
||||||
|
|
||||||
|
This protocol uses three main concepts to protect the transmission of a target event: `rumor`s, `seal`s, and `gift wrap`s.
|
||||||
|
|
||||||
|
- A `rumor` is a regular nostr event, but is **not signed**. This means that if it is leaked, it cannot be verified.
|
||||||
|
- A `rumor` is serialized to JSON, encrypted, and placed in the `content` field of a `seal`. The `seal` is then
|
||||||
|
signed by the author of the note. The only information publicly available on a `seal` is who signed it, but not what was said.
|
||||||
|
- A `seal` is serialized to JSON, encrypted, and placed in the `content` field of a `gift wrap`.
|
||||||
|
|
||||||
|
This allows the isolation of concerns across layers:
|
||||||
|
|
||||||
|
- A rumor carries the content but is unsigned, which means if leaked it will be rejected by relays and clients,
|
||||||
|
and can't be authenticated. This provides a measure of deniability.
|
||||||
|
- A seal identifies the author without revealing the content or the recipient.
|
||||||
|
- A gift wrap can add metadata (recipient, tags, a different author) without revealing the true author.
|
||||||
|
|
||||||
|
# Protocol Description
|
||||||
|
|
||||||
|
## 1. The Rumor Event Kind
|
||||||
|
|
||||||
|
A `rumor` is the same thing as an unsigned event. Any event kind can be made a `rumor` by removing the signature.
|
||||||
|
|
||||||
|
## 2. The Seal Event Kind
|
||||||
|
|
||||||
|
A `seal` is a `kind:13` event that wraps a `rumor` with the sender's regular key. The `seal` is **always** encrypted
|
||||||
|
to a receiver's pubkey but there is no `p` tag pointing to the receiver. There is no way to know who the rumor is for
|
||||||
|
without the receiver's or the sender's private key. The only public information in this event is who is signing it.
|
||||||
|
|
||||||
|
```js
|
||||||
|
{
|
||||||
|
"id": "<id>",
|
||||||
|
"pubkey": "<real author's pubkey>",
|
||||||
|
"content": "<encrypted rumor>",
|
||||||
|
"kind": 13,
|
||||||
|
"created_at": 1686840217,
|
||||||
|
"tags": [],
|
||||||
|
"sig": "<real author's pubkey signature>"
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Tags MUST must always be empty in a `kind:13`. The inner event MUST always be unsigned.
|
||||||
|
|
||||||
|
## 3. Gift Wrap Event Kind
|
||||||
|
|
||||||
|
A `gift wrap` event is a `kind:1059` event that wraps any other event. `tags` SHOULD include any information
|
||||||
|
needed to route the event to its intended recipient, including the recipient's `p` tag or [NIP-13](13.md) proof of work.
|
||||||
|
|
||||||
|
```js
|
||||||
|
{
|
||||||
|
"id": "<id>",
|
||||||
|
"pubkey": "<random, one-time-use pubkey>",
|
||||||
|
"content": "<encrypted kind 13>",
|
||||||
|
"kind": 1059,
|
||||||
|
"created_at": 1686840217,
|
||||||
|
"tags": [["p", "<recipient pubkey>"]],
|
||||||
|
"sig": "<random, one-time-use pubkey signature>"
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
# Encrypting Payloads
|
||||||
|
|
||||||
|
Encryption is done following [NIP-44](44.md) on the JSON-encoded event. Place the encryption payload in the `.content`
|
||||||
|
of the wrapper event (either a `seal` or a `gift wrap`).
|
||||||
|
|
||||||
|
# Other Considerations
|
||||||
|
|
||||||
|
If a `rumor` is intended for more than one party, or if the author wants to retain an encrypted copy, a single
|
||||||
|
`rumor` may be wrapped and addressed for each recipient individually.
|
||||||
|
|
||||||
|
The canonical `created_at` time belongs to the `rumor`. All other timestamps SHOULD be tweaked to thwart
|
||||||
|
time-analysis attacks. Note that some relays don't serve events dated in the future, so all timestamps
|
||||||
|
SHOULD be in the past.
|
||||||
|
|
||||||
|
Relays may choose not to store gift wrapped events due to them not being publicly useful. Clients MAY choose
|
||||||
|
to attach a certain amount of proof-of-work to the wrapper event per [NIP-13](13.md) in a bid to demonstrate that
|
||||||
|
the event is not spam or a denial-of-service attack.
|
||||||
|
|
||||||
|
To protect recipient metadata, relays SHOULD guard access to `kind 1059` events based on user AUTH. When
|
||||||
|
possible, clients should only send wrapped events to relays that offer this protection.
|
||||||
|
|
||||||
|
To protect recipient metadata, relays SHOULD only serve `kind 1059` events intended for the marked recipient.
|
||||||
|
When possible, clients should only send wrapped events to `read` relays for the recipient that implement
|
||||||
|
AUTH, and refuse to serve wrapped events to non-recipients.
|
||||||
|
|
||||||
|
# An Example
|
||||||
|
|
||||||
|
Let's send a wrapped `kind 1` message between two parties asking "Are you going to the party tonight?"
|
||||||
|
|
||||||
|
- Author private key: `0beebd062ec8735f4243466049d7747ef5d6594ee838de147f8aab842b15e273`
|
||||||
|
- Recipient private key: `e108399bd8424357a710b606ae0c13166d853d327e47a6e5e038197346bdbf45`
|
||||||
|
- Ephemeral wrapper key: `4f02eac59266002db5801adc5270700ca69d5b8f761d8732fab2fbf233c90cbd`
|
||||||
|
|
||||||
|
Note that this messaging protocol should not be used in practice, this is just an example. Refer to other
|
||||||
|
NIPs for concrete messaging protocols that depend on gift wraps.
|
||||||
|
|
||||||
|
## 1. Create an event
|
||||||
|
|
||||||
|
Create a `kind 1` event with the message, the receivers, and any other tags you want, signed by the author.
|
||||||
|
Do not sign the event.
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"created_at": 1691518405,
|
||||||
|
"content": "Are you going to the party tonight?",
|
||||||
|
"tags": [],
|
||||||
|
"kind": 1,
|
||||||
|
"pubkey": "611df01bfcf85c26ae65453b772d8f1dfd25c264621c0277e1fc1518686faef9",
|
||||||
|
"id": "9dd003c6d3b73b74a85a9ab099469ce251653a7af76f523671ab828acd2a0ef9"
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## 2. Seal the rumor
|
||||||
|
|
||||||
|
Encrypt the JSON-encoded `rumor` with a conversation key derived using the author's private key and
|
||||||
|
the recipient's public key. Place the result in the `content` field of a `kind 13` `seal` event. Sign
|
||||||
|
it with the author's key.
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"content": "AqBCdwoS7/tPK+QGkPCadJTn8FxGkd24iApo3BR9/M0uw6n4RFAFSPAKKMgkzVMoRyR3ZS/aqATDFvoZJOkE9cPG/TAzmyZvr/WUIS8kLmuI1dCA+itFF6+ULZqbkWS0YcVU0j6UDvMBvVlGTzHz+UHzWYJLUq2LnlynJtFap5k8560+tBGtxi9Gx2NIycKgbOUv0gEqhfVzAwvg1IhTltfSwOeZXvDvd40rozONRxwq8hjKy+4DbfrO0iRtlT7G/eVEO9aJJnqagomFSkqCscttf/o6VeT2+A9JhcSxLmjcKFG3FEK3Try/WkarJa1jM3lMRQqVOZrzHAaLFW/5sXano6DqqC5ERD6CcVVsrny0tYN4iHHB8BHJ9zvjff0NjLGG/v5Wsy31+BwZA8cUlfAZ0f5EYRo9/vKSd8TV0wRb9DQ=",
|
||||||
|
"kind": 13,
|
||||||
|
"created_at": 1703015180,
|
||||||
|
"pubkey": "611df01bfcf85c26ae65453b772d8f1dfd25c264621c0277e1fc1518686faef9",
|
||||||
|
"tags": [],
|
||||||
|
"id": "28a87d7c074d94a58e9e89bb3e9e4e813e2189f285d797b1c56069d36f59eaa7",
|
||||||
|
"sig": "02fc3facf6621196c32912b1ef53bac8f8bfe9db51c0e7102c073103586b0d29c3f39bdaa1e62856c20e90b6c7cc5dc34ca8bb6a528872cf6e65e6284519ad73"
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## 3. Wrap the seal
|
||||||
|
|
||||||
|
Encrypt the JSON-encoded `kind 13` event with your ephemeral, single-use random key. Place the result
|
||||||
|
in the `content` field of a `kind 1059`. Add a single `p` tag containing the recipient's public key.
|
||||||
|
Sign the `gift wrap` using the random key generated in the previous step.
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"content": "AhC3Qj/QsKJFWuf6xroiYip+2yK95qPwJjVvFujhzSguJWb/6TlPpBW0CGFwfufCs2Zyb0JeuLmZhNlnqecAAalC4ZCugB+I9ViA5pxLyFfQjs1lcE6KdX3euCHBLAnE9GL/+IzdV9vZnfJH6atVjvBkNPNzxU+OLCHO/DAPmzmMVx0SR63frRTCz6Cuth40D+VzluKu1/Fg2Q1LSst65DE7o2efTtZ4Z9j15rQAOZfE9jwMCQZt27rBBK3yVwqVEriFpg2mHXc1DDwHhDADO8eiyOTWF1ghDds/DxhMcjkIi/o+FS3gG1dG7gJHu3KkGK5UXpmgyFKt+421m5o++RMD/BylS3iazS1S93IzTLeGfMCk+7IKxuSCO06k1+DaasJJe8RE4/rmismUvwrHu/HDutZWkvOAhd4z4khZo7bJLtiCzZCZ74lZcjOB4CYtuAX2ZGpc4I1iOKkvwTuQy9BWYpkzGg3ZoSWRD6ty7U+KN+fTTmIS4CelhBTT15QVqD02JxfLF7nA6sg3UlYgtiGw61oH68lSbx16P3vwSeQQpEB5JbhofW7t9TLZIbIW/ODnI4hpwj8didtk7IMBI3Ra3uUP7ya6vptkd9TwQkd/7cOFaSJmU+BIsLpOXbirJACMn+URoDXhuEtiO6xirNtrPN8jYqpwvMUm5lMMVzGT3kMMVNBqgbj8Ln8VmqouK0DR+gRyNb8fHT0BFPwsHxDskFk5yhe5c/2VUUoKCGe0kfCcX/EsHbJLUUtlHXmTqaOJpmQnW1tZ/siPwKRl6oEsIJWTUYxPQmrM2fUpYZCuAo/29lTLHiHMlTbarFOd6J/ybIbICy2gRRH/LFSryty3Cnf6aae+A9uizFBUdCwTwffc3vCBae802+R92OL78bbqHKPbSZOXNC+6ybqziezwG+OPWHx1Qk39RYaF0aFsM4uZWrFic97WwVrH5i+/Nsf/OtwWiuH0gV/SqvN1hnkxCTF/+XNn/laWKmS3e7wFzBsG8+qwqwmO9aVbDVMhOmeUXRMkxcj4QreQkHxLkCx97euZpC7xhvYnCHarHTDeD6nVK+xzbPNtzeGzNpYoiMqxZ9bBJwMaHnEoI944Vxoodf51cMIIwpTmmRvAzI1QgrfnOLOUS7uUjQ/IZ1Qa3lY08Nqm9MAGxZ2Ou6R0/Z5z30ha/Q71q6meAs3uHQcpSuRaQeV29IASmye2A2Nif+lmbhV7w8hjFYoaLCRsdchiVyNjOEM4VmxUhX4VEvw6KoCAZ/XvO2eBF/SyNU3Of4SO",
|
||||||
|
"kind": 1059,
|
||||||
|
"created_at": 1703021488,
|
||||||
|
"pubkey": "18b1a75918f1f2c90c23da616bce317d36e348bcf5f7ba55e75949319210c87c",
|
||||||
|
"id": "5c005f3ccf01950aa8d131203248544fb1e41a0d698e846bd419cec3890903ac",
|
||||||
|
"sig": "35fabdae4634eb630880a1896a886e40fd6ea8a60958e30b89b33a93e6235df750097b04f9e13053764251b8bc5dd7e8e0794a3426a90b6bcc7e5ff660f54259",
|
||||||
|
"tags": [["p", "166bf3765ebd1fc55decfe395beff2ea3b2a4e0a8946e7eb578512b555737c99"]],
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## 4. Broadcast Selectively
|
||||||
|
|
||||||
|
Broadcast the `kind 1059` event to the recipient's relays only. Delete all the other events.
|
||||||
|
|
||||||
|
# Code Samples
|
||||||
|
|
||||||
|
## JavaScript
|
||||||
|
|
||||||
|
```javascript
|
||||||
|
import {bytesToHex} from "@noble/hashes/utils"
|
||||||
|
import type {EventTemplate, UnsignedEvent, Event} from "nostr-tools"
|
||||||
|
import {getPublicKey, getEventHash, nip19, nip44, finalizeEvent, generateSecretKey} from "nostr-tools"
|
||||||
|
|
||||||
|
type Rumor = UnsignedEvent & {id: string}
|
||||||
|
|
||||||
|
const TWO_DAYS = 2 * 24 * 60 * 60
|
||||||
|
|
||||||
|
const now = () => Math.round(Date.now() / 1000)
|
||||||
|
const randomNow = () => Math.round(now() - (Math.random() * TWO_DAYS))
|
||||||
|
|
||||||
|
const nip44ConversationKey = (privateKey: Uint8Array, publicKey: string) =>
|
||||||
|
nip44.v2.utils.getConversationKey(bytesToHex(privateKey), publicKey)
|
||||||
|
|
||||||
|
const nip44Encrypt = (data: EventTemplate, privateKey: Uint8Array, publicKey: string) =>
|
||||||
|
nip44.v2.encrypt(JSON.stringify(data), nip44ConversationKey(privateKey, publicKey))
|
||||||
|
|
||||||
|
const nip44Decrypt = (data: Event, privateKey: Uint8Array) =>
|
||||||
|
JSON.parse(nip44.v2.decrypt(data.content, nip44ConversationKey(privateKey, data.pubkey)))
|
||||||
|
|
||||||
|
const createRumor = (event: Partial<UnsignedEvent>, privateKey: Uint8Array) => {
|
||||||
|
const rumor = {
|
||||||
|
created_at: now(),
|
||||||
|
content: "",
|
||||||
|
tags: [],
|
||||||
|
...event,
|
||||||
|
pubkey: getPublicKey(privateKey),
|
||||||
|
} as any
|
||||||
|
|
||||||
|
rumor.id = getEventHash(rumor)
|
||||||
|
|
||||||
|
return rumor as Rumor
|
||||||
|
}
|
||||||
|
|
||||||
|
const createSeal = (rumor: Rumor, privateKey: Uint8Array, recipientPublicKey: string) => {
|
||||||
|
return finalizeEvent(
|
||||||
|
{
|
||||||
|
kind: 13,
|
||||||
|
content: nip44Encrypt(rumor, privateKey, recipientPublicKey),
|
||||||
|
created_at: randomNow(),
|
||||||
|
tags: [],
|
||||||
|
},
|
||||||
|
privateKey
|
||||||
|
) as Event
|
||||||
|
}
|
||||||
|
|
||||||
|
const createWrap = (event: Event, recipientPublicKey: string) => {
|
||||||
|
const randomKey = generateSecretKey()
|
||||||
|
|
||||||
|
return finalizeEvent(
|
||||||
|
{
|
||||||
|
kind: 1059,
|
||||||
|
content: nip44Encrypt(event, randomKey, recipientPublicKey),
|
||||||
|
created_at: randomNow(),
|
||||||
|
tags: [["p", recipientPublicKey]],
|
||||||
|
},
|
||||||
|
randomKey
|
||||||
|
) as Event
|
||||||
|
}
|
||||||
|
|
||||||
|
// Test case using the above example
|
||||||
|
const senderPrivateKey = nip19.decode(`nsec1p0ht6p3wepe47sjrgesyn4m50m6avk2waqudu9rl324cg2c4ufesyp6rdg`).data
|
||||||
|
const recipientPrivateKey = nip19.decode(`nsec1uyyrnx7cgfp40fcskcr2urqnzekc20fj0er6de0q8qvhx34ahazsvs9p36`).data
|
||||||
|
const recipientPublicKey = getPublicKey(recipientPrivateKey)
|
||||||
|
|
||||||
|
const rumor = createRumor(
|
||||||
|
{
|
||||||
|
kind: 1,
|
||||||
|
content: "Are you going to the party tonight?",
|
||||||
|
},
|
||||||
|
senderPrivateKey
|
||||||
|
)
|
||||||
|
|
||||||
|
const seal = createSeal(rumor, senderPrivateKey, recipientPublicKey)
|
||||||
|
const wrap = createWrap(seal, recipientPublicKey)
|
||||||
|
|
||||||
|
// Recipient unwraps with his/her private key.
|
||||||
|
|
||||||
|
const unwrappedSeal = nip44Decrypt(wrap, recipientPrivateKey)
|
||||||
|
const unsealedRumor = nip44Decrypt(unwrappedSeal, recipientPrivateKey)
|
||||||
|
```
|
||||||
98
65.md
98
65.md
|
|
@ -4,63 +4,13 @@ NIP-65
|
||||||
Relay List Metadata
|
Relay List Metadata
|
||||||
-------------------
|
-------------------
|
||||||
|
|
||||||
`draft` `optional` `author:mikedilger`
|
`draft` `optional`
|
||||||
|
|
||||||
A special replaceable event meaning "Relay List Metadata" is defined as an event with kind `10002` having a list of `r` tags, one for each relay the author uses to either read or write to.
|
Defines a replaceable event using `kind:10002` to advertise preferred relays for discovering a user's content and receiving fresh content from others.
|
||||||
|
|
||||||
The primary purpose of this relay list is to advertise to others, not for configuring one's client.
|
The event MUST include a list of `r` tags with relay URIs and a `read` or `write` marker. Relays marked as `read` / `write` are called READ / WRITE relays, respectively. If the marker is omitted, the relay is used for both purposes.
|
||||||
|
|
||||||
The content is not used and SHOULD be an empty string.
|
The `.content` is not used.
|
||||||
|
|
||||||
The `r` tags can have a second parameter as either `read` or `write`. If it is omitted, it means the author uses the relay for both purposes.
|
|
||||||
|
|
||||||
Clients SHOULD, as with all replaceable events, use only the most recent kind-10002 event they can find.
|
|
||||||
|
|
||||||
### The meaning of read and write
|
|
||||||
|
|
||||||
Write relays are for events that are intended for anybody (e.g. your followers). Read relays are for events that address a particular person.
|
|
||||||
|
|
||||||
Clients SHOULD write feed-related events created by their user to their user's write relays.
|
|
||||||
|
|
||||||
Clients SHOULD read feed-related events created by another from at least some of that other person's write relays. Explicitly, they SHOULD NOT expect them to be available at their user's read relays. It SHOULD NOT be presumed that the user's read relays coincide with the write relays of the people the user follows.
|
|
||||||
|
|
||||||
Clients SHOULD read events that tag their user from their user's read relays.
|
|
||||||
|
|
||||||
Clients SHOULD write events that tag a person to at least some of that person's read relays. Explicitly, they SHOULD NOT expect that person will pick them up from their user's write relays. It SHOULD NOT be presumed that the user's write relays coincide with the read relays of the person being tagged.
|
|
||||||
|
|
||||||
Clients SHOULD presume that if their user has a pubkey in their ContactList (kind 3) that it is because they wish to see that author's feed-related events. But clients MAY presume otherwise.
|
|
||||||
|
|
||||||
### Motivation
|
|
||||||
|
|
||||||
There is a common nostr use case where users wish to follow the content produced by other users. This is evidenced by the implicit meaning of the Contact List in [NIP-02](02.md)
|
|
||||||
|
|
||||||
Because users don't often share the same sets of relays, ad-hoc solutions have arisen to get that content, but these solutions negatively impact scalability and decentralization:
|
|
||||||
|
|
||||||
- Most people are sending their posts to the same most popular relays in order to be more widely seen
|
|
||||||
- Many people are pulling from a large number of relays (including many duplicate events) in order to get more data
|
|
||||||
- Events are being copied between relays, oftentimes to many different relays
|
|
||||||
|
|
||||||
### Purposes
|
|
||||||
|
|
||||||
The purpose of this NIP is to help clients find the events of the people they follow, to help tagged events get to the people tagged, and to help nostr scale better.
|
|
||||||
|
|
||||||
### Suggestions
|
|
||||||
|
|
||||||
It is suggested that people spread their kind `10002` events to many relays, but write their normal feed-related events to a much smaller number of relays (between 2 to 6 relays). It is suggested that clients offer a way for users to spread their kind `10002` events to many more relays than they normally post to.
|
|
||||||
|
|
||||||
Authors may post events outside of the feed that they wish their followers to follow by posting them to relays outside of those listed in their "Relay List Metadata". For example, an author may want to reply to someone without all of their followers watching.
|
|
||||||
|
|
||||||
It is suggested that relays allow any user to write their own kind `10002` event (optionally with AUTH to verify it is their own) even if they are not otherwise subscribed to the relay because
|
|
||||||
|
|
||||||
- finding where someone posts is rather important
|
|
||||||
- these events do not have content that needs management
|
|
||||||
- relays only need to store one replaceable event per pubkey to offer this service
|
|
||||||
|
|
||||||
### Why not in kind `0` Metadata
|
|
||||||
|
|
||||||
Even though this is user related metadata, it is a separate event from kind `0` in order to keep it small (as it should be widely spread) and to not have content that may require moderation by relay operators so that it is more acceptable to relays.
|
|
||||||
|
|
||||||
### Example
|
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
|
|
@ -69,8 +19,46 @@ Even though this is user related metadata, it is a separate event from kind `0`
|
||||||
["r", "wss://alicerelay.example.com"],
|
["r", "wss://alicerelay.example.com"],
|
||||||
["r", "wss://brando-relay.com"],
|
["r", "wss://brando-relay.com"],
|
||||||
["r", "wss://expensive-relay.example2.com", "write"],
|
["r", "wss://expensive-relay.example2.com", "write"],
|
||||||
["r", "wss://nostr-relay.example.com", "read"],
|
["r", "wss://nostr-relay.example.com", "read"]
|
||||||
],
|
],
|
||||||
"content": "",
|
"content": "",
|
||||||
...other fields
|
...other fields
|
||||||
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
|
This NIP doesn't fully replace relay lists that are designed to configure a client's usage of relays (such as `kind:3` style relay lists). Clients MAY use other relay lists in situations where a `kind:10002` relay list cannot be found.
|
||||||
|
|
||||||
|
## When to Use Read and Write Relays
|
||||||
|
|
||||||
|
When seeking events **from** a user, Clients SHOULD use the WRITE relays of the user's `kind:10002`.
|
||||||
|
|
||||||
|
When seeking events **about** a user, where the user was tagged, Clients SHOULD use the READ relays of the user's `kind:10002`.
|
||||||
|
|
||||||
|
When broadcasting an event, Clients SHOULD:
|
||||||
|
|
||||||
|
- Broadcast the event to the WRITE relays of the author
|
||||||
|
- Broadcast the event all READ relays of each tagged user
|
||||||
|
|
||||||
|
## Motivation
|
||||||
|
|
||||||
|
The old model of using a fixed relay list per user centralizes in large relay operators:
|
||||||
|
|
||||||
|
- Most users submit their posts to the same highly popular relays, aiming to achieve greater visibility among a broader audience
|
||||||
|
- Many users are pulling events from a large number of relays in order to get more data at the expense of duplication
|
||||||
|
- Events are being copied between relays, oftentimes to many different relays
|
||||||
|
|
||||||
|
This NIP allows Clients to connect directly with the most up-to-date relay set from each individual user, eliminating the need of broadcasting events to popular relays.
|
||||||
|
|
||||||
|
## Final Considerations
|
||||||
|
|
||||||
|
1. Clients SHOULD guide users to keep `kind:10002` lists small (2-4 relays).
|
||||||
|
|
||||||
|
2. Clients SHOULD spread an author's `kind:10002` event to as many relays as viable.
|
||||||
|
|
||||||
|
3. `kind:10002` events should primarily be used to advertise the user's preferred relays to others. A user's own client may use other heuristics for selecting relays for fetching data.
|
||||||
|
|
||||||
|
4. DMs SHOULD only be broadcasted to the author's WRITE relays and to the receiver's READ relays to keep maximum privacy.
|
||||||
|
|
||||||
|
5. If a relay signals support for this NIP in their [NIP-11](11.md) document that means they're willing to accept kind 10002 events from a broad range of users, not only their paying customers or whitelisted group.
|
||||||
|
|
||||||
|
6. Clients SHOULD deduplicate connections by normalizing relay URIs according to [RFC 3986](https://datatracker.ietf.org/doc/html/rfc3986#section-6).
|
||||||
|
|
|
||||||
118
71.md
Normal file
118
71.md
Normal file
|
|
@ -0,0 +1,118 @@
|
||||||
|
NIP-71
|
||||||
|
======
|
||||||
|
|
||||||
|
Video Events
|
||||||
|
---------------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
This specification defines video events representing a dedicated post of externally hosted content. These video events are _parameterized replaceable_ and deletable per [NIP-09](09.md).
|
||||||
|
|
||||||
|
Unlike a `kind 1` event with a video attached, Video Events are meant to contain all additional metadata concerning the subject media and to be surfaced in video-specific clients rather than general micro-blogging clients. The thought is for events of this kind to be referenced in a Netflix, YouTube, or TikTok like nostr client where the video itself is at the center of the experience.
|
||||||
|
|
||||||
|
## Video Events
|
||||||
|
|
||||||
|
There are two types of video events represented by different kinds: horizontal and vertical video events. This is meant to allow clients to cater to each as the viewing experience for horizontal (landscape) videos is often different than that of vertical (portrait) videos (Stories, Reels, Shorts, etc).
|
||||||
|
|
||||||
|
#### Format
|
||||||
|
|
||||||
|
The format uses a parameterized replaceable event kind `34235` for horizontal videos and `34236` for vertical videos.
|
||||||
|
|
||||||
|
The `.content` of these events is a summary or description on the video content.
|
||||||
|
|
||||||
|
The list of tags are as follows:
|
||||||
|
* `d` (required) universally unique identifier (UUID). Generated by the client creating the video event.
|
||||||
|
* `url` (required) the url to the video file
|
||||||
|
* `m` a string indicating the data type of the file. The [MIME types](https://developer.mozilla.org/en-US/docs/Web/HTTP/Basics_of_HTTP/MIME_types/Common_types) format must be used, and they should be lowercase.
|
||||||
|
* `title` (required) title of the video
|
||||||
|
* `"published_at"`, for the timestamp in unix seconds (stringified) of the first time the video was published
|
||||||
|
* `x` containing the SHA-256 hexencoded string of the file.
|
||||||
|
* `size` (optional) size of file in bytes
|
||||||
|
* `dim` (optional) size of file in pixels in the form `<width>x<height>`
|
||||||
|
* `duration` (optional) video duration in seconds
|
||||||
|
* `magnet` (optional) URI to magnet file
|
||||||
|
* `i` (optional) torrent infohash
|
||||||
|
* `text-track` (optional, repeated) link to WebVTT file for video, type of supplementary information (captions/subtitles/chapters/metadata), optional language code
|
||||||
|
* `thumb` (optional) url of thumbnail with same aspect ratio
|
||||||
|
* `image` (optional) url of preview image with same dimensions
|
||||||
|
* `content-warning` (optional) warning about content of NSFW video
|
||||||
|
* `alt` (optional) description for accessibility
|
||||||
|
* `segment` (optional, repeated) start timestamp in format `HH:MM:SS.sss`, end timestamp in format `HH:MM:SS.sss`, chapter/segment title, chapter thumbnail-url
|
||||||
|
* `t` (optional, repeated) hashtag to categorize video
|
||||||
|
* `p` (optional, repeated) 32-bytes hex pubkey of a participant in the video, optional recommended relay URL
|
||||||
|
* `r` (optional, repeated) references / links to web pages
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"id": <32-bytes lowercase hex-encoded SHA-256 of the the serialized event data>,
|
||||||
|
"pubkey": <32-bytes lowercase hex-encoded public key of the event creator>,
|
||||||
|
"created_at": <Unix timestamp in seconds>,
|
||||||
|
"kind": 34235 | 34236,
|
||||||
|
"content": "<summary / description of video>",
|
||||||
|
"tags": [
|
||||||
|
["d", "<UUID>"],
|
||||||
|
|
||||||
|
["title", "<title of video>"],
|
||||||
|
["thumb", "<thumbnail image for video>"],
|
||||||
|
["published_at", "<unix timestamp>"],
|
||||||
|
["alt", <description>],
|
||||||
|
|
||||||
|
// Video Data
|
||||||
|
["url",<string with URI of file>],
|
||||||
|
["m", <MIME type>],
|
||||||
|
["x",<Hash SHA-256>],
|
||||||
|
["size", <size of file in bytes>],
|
||||||
|
["duration", <duration of video in seconds>],
|
||||||
|
["dim", <size of file in pixels>],
|
||||||
|
["magnet",<magnet URI> ],
|
||||||
|
["i",<torrent infohash>],
|
||||||
|
["text-track", "<encoded `kind 6000` event>", "<recommended relay urls>"],
|
||||||
|
["content-warning", "<reason>"],
|
||||||
|
["segment", <start>, <end>, "<title>", "<thumbnail URL>"],
|
||||||
|
|
||||||
|
// Participants
|
||||||
|
["p", "<32-bytes hex of a pubkey>", "<optional recommended relay URL>"],
|
||||||
|
["p", "<32-bytes hex of a pubkey>", "<optional recommended relay URL>"],
|
||||||
|
|
||||||
|
// Hashtags
|
||||||
|
["t", "<tag>"],
|
||||||
|
["t", "<tag>"],
|
||||||
|
|
||||||
|
// Reference links
|
||||||
|
["r", "<url>"],
|
||||||
|
["r", "<url>"]
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## Video View
|
||||||
|
|
||||||
|
A video event view is a response to a video event to track a user's view or progress viewing the video.
|
||||||
|
|
||||||
|
### Format
|
||||||
|
|
||||||
|
The format uses a parameterized replaceable event kind `34237`.
|
||||||
|
|
||||||
|
The `.content` of these events is optional and could be a free-form note that acts like a bookmark for the user.
|
||||||
|
|
||||||
|
The list of tags are as follows:
|
||||||
|
* `a` (required) reference tag to kind `34235` or `34236` video event being viewed
|
||||||
|
* `d` (required) same as `a` reference tag value
|
||||||
|
* `viewed` (optional, repeated) timestamp of the user's start time in seconds, timestamp of the user's end time in seconds
|
||||||
|
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"id": <32-bytes lowercase hex-encoded SHA-256 of the the serialized event data>,
|
||||||
|
"pubkey": <32-bytes lowercase hex-encoded public key of the event creator>,
|
||||||
|
"created_at": <Unix timestamp in seconds>,
|
||||||
|
"kind": 34237,
|
||||||
|
"content": "<note>",
|
||||||
|
"tags": [
|
||||||
|
["a", "<34235 | 34236>:<video event author pubkey>:<d-identifier of video event>", "<optional relay url>"],
|
||||||
|
["e", "<event-id", "<relay-url>"]
|
||||||
|
["d", "<34235 | 34236>:<video event author pubkey>:<d-identifier of video event>"],
|
||||||
|
["viewed", <start>, <end>],
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
101
72.md
Normal file
101
72.md
Normal file
|
|
@ -0,0 +1,101 @@
|
||||||
|
NIP-72
|
||||||
|
======
|
||||||
|
|
||||||
|
Moderated Communities (Reddit Style)
|
||||||
|
------------------------------------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
The goal of this NIP is to create moderator-approved public communities around a topic. It defines the replaceable event `kind:34550` to define the community and the current list of moderators/administrators. Users that want to post into the community, simply tag any Nostr event with the community's `a` tag. Moderators issue an approval event `kind:4550` that links the community with the new post.
|
||||||
|
|
||||||
|
# Community Definition
|
||||||
|
|
||||||
|
`kind:34550` SHOULD include any field that helps define the community and the set of moderators. `relay` tags MAY be used to describe the preferred relay to download requests and approvals.
|
||||||
|
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"created_at": <Unix timestamp in seconds>,
|
||||||
|
"kind": 34550,
|
||||||
|
"tags": [
|
||||||
|
["d", "<community-d-identifier>"],
|
||||||
|
["description", "<Community description>"],
|
||||||
|
["image", "<Community image url>", "<Width>x<Height>"],
|
||||||
|
|
||||||
|
//.. other tags relevant to defining the community
|
||||||
|
|
||||||
|
// moderators
|
||||||
|
["p", "<32-bytes hex of a pubkey1>", "<optional recommended relay URL>", "moderator"],
|
||||||
|
["p", "<32-bytes hex of a pubkey2>", "<optional recommended relay URL>", "moderator"],
|
||||||
|
["p", "<32-bytes hex of a pubkey3>", "<optional recommended relay URL>", "moderator"],
|
||||||
|
|
||||||
|
// relays used by the community (w/optional marker)
|
||||||
|
["relay", "<relay hosting author kind 0>", "author"],
|
||||||
|
["relay", "<relay where to send and receive requests>", "requests"],
|
||||||
|
["relay", "<relay where to send and receive approvals>", "approvals"],
|
||||||
|
["relay", "<relay where to post requests to and fetch approvals from>"]
|
||||||
|
],
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
# New Post Request
|
||||||
|
|
||||||
|
Any Nostr event can be submitted to a community by anyone for approval. Clients MUST add the community's `a` tag to the new post event in order to be presented for the moderator's approval.
|
||||||
|
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"kind": 1,
|
||||||
|
"tags": [
|
||||||
|
["a", "34550:<community event author pubkey>:<community-d-identifier>", "<optional-relay-url>"],
|
||||||
|
],
|
||||||
|
"content": "hello world",
|
||||||
|
// ...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Community management clients MAY filter all mentions to a given `kind:34550` event and request moderators to approve each submission. Moderators MAY delete his/her approval of a post at any time using event deletions (See [NIP-09](09.md)).
|
||||||
|
|
||||||
|
# Post Approval by moderators
|
||||||
|
|
||||||
|
The post-approval event MUST include `a` tags of the communities the moderator is posting into (one or more), the `e` tag of the post and `p` tag of the author of the post (for approval notifications). The event SHOULD also include the stringified `post request` event inside the `.content` ([NIP-18-style](18.md)) and a `k` tag with the original post's event kind to allow filtering of approved posts by kind.
|
||||||
|
|
||||||
|
```jsonc
|
||||||
|
{
|
||||||
|
"pubkey": "<32-bytes lowercase hex-encoded public key of the event creator>",
|
||||||
|
"kind": 4550,
|
||||||
|
"tags": [
|
||||||
|
["a", "34550:<event-author-pubkey>:<community-d-identifier>", "<optional-relay-url>"],
|
||||||
|
["e", "<post-id>", "<optional-relay-url>"],
|
||||||
|
["p", "<port-author-pubkey>", "<optional-relay-url>"],
|
||||||
|
["k", "<post-request-kind>"]
|
||||||
|
],
|
||||||
|
"content": "<the full approved event, JSON-encoded>",
|
||||||
|
// ...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
It's recommended that multiple moderators approve posts to avoid deleting them from the community when a moderator is removed from the owner's list. In case the full list of moderators must be rotated, the new moderator set must sign new approvals for posts in the past or the community will restart. The owner can also periodically copy and re-sign of each moderator's approval events to make sure posts don't disappear with moderators.
|
||||||
|
|
||||||
|
Post Approvals of replaceable events can be created in three ways: (i) by tagging the replaceable event as an `e` tag if moderators want to approve each individual change to the replaceable event; (ii) by tagging the replaceable event as an `a` tag if the moderator authorizes the replaceable event author to make changes without additional approvals and (iii) by tagging the replaceable event with both its `e` and `a` tag which empowers clients to display the original and updated versions of the event, with appropriate remarks in the UI. Since relays are instructed to delete old versions of a replaceable event, the `.content` of an `e`-approval MUST have the specific version of the event or Clients might not be able to find that version of the content anywhere.
|
||||||
|
|
||||||
|
Clients SHOULD evaluate any non-`34550:*` `a` tag as posts to be included in all `34550:*` `a` tags.
|
||||||
|
|
||||||
|
# Displaying
|
||||||
|
|
||||||
|
Community clients SHOULD display posts that have been approved by at least 1 moderator or by the community owner.
|
||||||
|
|
||||||
|
The following filter displays the approved posts.
|
||||||
|
|
||||||
|
```json
|
||||||
|
[
|
||||||
|
"REQ",
|
||||||
|
"_",
|
||||||
|
{
|
||||||
|
"authors": ["<owner-pubkey>", "<moderator1-pubkey>", "<moderator2-pubkey>", "<moderator3-pubkey>", ...],
|
||||||
|
"kinds": [4550],
|
||||||
|
"#a": ["34550:<Community event author pubkey>:<d-identifier of the community>"],
|
||||||
|
}
|
||||||
|
]
|
||||||
|
```
|
||||||
|
|
||||||
|
Clients MAY hide approvals by blocked moderators at the user's request.
|
||||||
85
75.md
Normal file
85
75.md
Normal file
|
|
@ -0,0 +1,85 @@
|
||||||
|
NIP-75
|
||||||
|
======
|
||||||
|
|
||||||
|
Zap Goals
|
||||||
|
---------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
This NIP defines an event for creating fundraising goals. Users can contribute funds towards the goal by zapping the goal event.
|
||||||
|
|
||||||
|
## Nostr Event
|
||||||
|
|
||||||
|
A `kind:9041` event is used.
|
||||||
|
|
||||||
|
The `.content` contains a human-readable description of the goal.
|
||||||
|
|
||||||
|
The following tags are defined as REQUIRED.
|
||||||
|
|
||||||
|
- `amount` - target amount in milisats.
|
||||||
|
- `relays` - a list of relays the zaps to this goal will be sent to and tallied from.
|
||||||
|
|
||||||
|
Example event:
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"kind": 9041,
|
||||||
|
"tags": [
|
||||||
|
["relays", "wss://alicerelay.example.com", "wss://bobrelay.example.com", ...],
|
||||||
|
["amount", "210000"],
|
||||||
|
],
|
||||||
|
"content": "Nostrasia travel expenses",
|
||||||
|
...
|
||||||
|
```
|
||||||
|
|
||||||
|
The following tags are OPTIONAL.
|
||||||
|
|
||||||
|
- `closed_at` - timestamp for determining which zaps are included in the tally. Zap receipts published after the `closed_at` timestamp SHOULD NOT count towards the goal progress.
|
||||||
|
- `image` - an image for the goal
|
||||||
|
- `summary` - a brief description
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"kind": 9041,
|
||||||
|
"tags": [
|
||||||
|
["relays", "wss://alicerelay.example.com", "wss://bobrelay.example.com", ...],
|
||||||
|
["amount", "210000"],
|
||||||
|
["closed_at", "<unix timestamp in seconds>"],
|
||||||
|
["image", "<image URL>"],
|
||||||
|
["summary", "<description of the goal>"],
|
||||||
|
],
|
||||||
|
"content": "Nostrasia travel expenses",
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
The goal MAY include an `r` or `a` tag linking to a URL or parameterized replaceable event.
|
||||||
|
|
||||||
|
The goal MAY include multiple beneficiary pubkeys by specifying [`zap` tags](57.md#appendix-g-zap-tag-on-other-events).
|
||||||
|
|
||||||
|
Parameterized replaceable events can link to a goal by using a `goal` tag specifying the event id and an optional relay hint.
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
...
|
||||||
|
"kind": 3xxxx,
|
||||||
|
"tags": [
|
||||||
|
...
|
||||||
|
["goal", "<event id>", "<Relay URL (optional)>"],
|
||||||
|
],
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## Client behavior
|
||||||
|
|
||||||
|
Clients MAY display funding goals on user profiles.
|
||||||
|
|
||||||
|
When zapping a goal event, clients MUST include the relays in the `relays` tag of the goal event in the zap request `relays` tag.
|
||||||
|
|
||||||
|
When zapping a parameterized replaceable event with a `goal` tag, clients SHOULD tag the goal event id in the `e` tag of the zap request.
|
||||||
|
|
||||||
|
## Use cases
|
||||||
|
|
||||||
|
- Fundraising clients
|
||||||
|
- Adding funding goals to events such as long form posts, badges or live streams
|
||||||
2
78.md
2
78.md
|
|
@ -4,7 +4,7 @@ NIP-78
|
||||||
Arbitrary custom app data
|
Arbitrary custom app data
|
||||||
-------------------------
|
-------------------------
|
||||||
|
|
||||||
`draft` `optional` `author:sandwich` `author:fiatjaf`
|
`draft` `optional`
|
||||||
|
|
||||||
The goal of this NIP is to enable [remoteStorage](https://remotestorage.io/)-like capabilities for custom applications that do not care about interoperability.
|
The goal of this NIP is to enable [remoteStorage](https://remotestorage.io/)-like capabilities for custom applications that do not care about interoperability.
|
||||||
|
|
||||||
|
|
|
||||||
42
84.md
Normal file
42
84.md
Normal file
|
|
@ -0,0 +1,42 @@
|
||||||
|
NIP-84
|
||||||
|
======
|
||||||
|
|
||||||
|
Highlights
|
||||||
|
----------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
This NIP defines `kind:9802`, a "highlight" event, to signal content a user finds valuable.
|
||||||
|
|
||||||
|
## Format
|
||||||
|
The `.content` of these events is the highlighted portion of the text.
|
||||||
|
|
||||||
|
`.content` might be empty for highlights of non-text based media (e.g. NIP-94 audio/video).
|
||||||
|
|
||||||
|
### References
|
||||||
|
Events SHOULD tag the source of the highlight, whether nostr-native or not.
|
||||||
|
`a` or `e` tags should be used for nostr events and `r` tags for URLs.
|
||||||
|
|
||||||
|
When tagging a URL, clients generating these events SHOULD do a best effort of cleaning the URL from trackers
|
||||||
|
or obvious non-useful information from the query string.
|
||||||
|
|
||||||
|
### Attribution
|
||||||
|
Clients MAY include one or more `p` tags, tagging the original authors of the material being highlighted; this is particularly
|
||||||
|
useful when highlighting non-nostr content for which the client might be able to get a nostr pubkey somehow
|
||||||
|
(e.g. prompting the user or reading a `<meta name="nostr:nprofile1..." />` tag on the document). A role MAY be included as the
|
||||||
|
last value of the tag.
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"tags": [
|
||||||
|
["p", "<pubkey-hex>", "<relay-url>", "author"],
|
||||||
|
["p", "<pubkey-hex>", "<relay-url>", "author"],
|
||||||
|
["p", "<pubkey-hex>", "<relay-url>", "editor"]
|
||||||
|
],
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
### Context
|
||||||
|
Clients MAY include a `context` tag, useful when the highlight is a subset of a paragraph and displaying the
|
||||||
|
surrounding content might be beneficial to give context to the highlight.
|
||||||
59
89.md
59
89.md
|
|
@ -4,15 +4,17 @@ NIP-89
|
||||||
Recommended Application Handlers
|
Recommended Application Handlers
|
||||||
--------------------------------
|
--------------------------------
|
||||||
|
|
||||||
`draft` `optional` `author:pablof7z`
|
`draft` `optional`
|
||||||
|
|
||||||
This NIP describes `kind:31989` and `kind:31990`: a way to discover applications that can handle unknown event-kinds.
|
This NIP describes `kind:31989` and `kind:31990`: a way to discover applications that can handle unknown event-kinds.
|
||||||
|
|
||||||
## Rationale
|
## Rationale
|
||||||
|
|
||||||
Nostr's discoverability and transparent event interaction is one of its most interesting/novel mechanics.
|
Nostr's discoverability and transparent event interaction is one of its most interesting/novel mechanics.
|
||||||
This NIP provides a simple way for clients to discover applications that handle events of a specific kind to ensure smooth cross-client and cross-kind interactions.
|
This NIP provides a simple way for clients to discover applications that handle events of a specific kind to ensure smooth cross-client and cross-kind interactions.
|
||||||
|
|
||||||
### Parties involved
|
### Parties involved
|
||||||
|
|
||||||
There are three actors to this workflow:
|
There are three actors to this workflow:
|
||||||
|
|
||||||
* application that handles a specific event kind (note that an application doesn't necessarily need to be a distinct entity and it could just be the same pubkey as user A)
|
* application that handles a specific event kind (note that an application doesn't necessarily need to be a distinct entity and it could just be the same pubkey as user A)
|
||||||
|
|
@ -22,9 +24,9 @@ There are three actors to this workflow:
|
||||||
* user B, who seeks a recommendation for an app that handles a specific event kind
|
* user B, who seeks a recommendation for an app that handles a specific event kind
|
||||||
* Queries for `kind:31989` and, based on results, queries for `kind:31990`
|
* Queries for `kind:31989` and, based on results, queries for `kind:31990`
|
||||||
|
|
||||||
# Events
|
## Events
|
||||||
|
|
||||||
## Recommendation event
|
### Recommendation event
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"kind": 31989,
|
"kind": 31989,
|
||||||
|
|
@ -48,7 +50,7 @@ The third value of the tag SHOULD be the platform where this recommendation migh
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"kind": 31990,
|
"kind": 31990,
|
||||||
"pubkey": <pubkey>,
|
"pubkey": "<application-pubkey>",
|
||||||
"content": "<optional-kind:0-style-metadata>",
|
"content": "<optional-kind:0-style-metadata>",
|
||||||
"tags": [
|
"tags": [
|
||||||
["d", <random-id>],
|
["d", <random-id>],
|
||||||
|
|
@ -61,29 +63,40 @@ The third value of the tag SHOULD be the platform where this recommendation migh
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
* `content` is an optional `set_metadata`-like stringified JSON object, as described in NIP-01. This content is useful when the pubkey creating the `kind:31990` is not an application. If `content` is empty, the `kind:0` of the pubkey should be used to display application information (e.g. name, picture, web, LUD16, etc.)
|
* `content` is an optional `metadata`-like stringified JSON object, as described in NIP-01. This content is useful when the pubkey creating the `kind:31990` is not an application. If `content` is empty, the `kind:0` of the pubkey should be used to display application information (e.g. name, picture, web, LUD16, etc.)
|
||||||
|
|
||||||
* `k` tags' value is the event kind that is supported by this `kind:31990`.
|
* `k` tags' value is the event kind that is supported by this `kind:31990`.
|
||||||
Using a `k` tag(s) (instead of having the kind onf the NIP-33 `d` tag) provides:
|
Using a `k` tag(s) (instead of having the kind of the `d` tag) provides:
|
||||||
* Multiple `k` tags can exist in the same event if the application supports more than one event kind and their handler URLs are the same.
|
* Multiple `k` tags can exist in the same event if the application supports more than one event kind and their handler URLs are the same.
|
||||||
* The same pubkey can have multiple events with different apps that handle the same event kind.
|
* The same pubkey can have multiple events with different apps that handle the same event kind.
|
||||||
|
|
||||||
* `bech32` in a URL MUST be replaced by clients with the NIP-19-encoded entity that should be loaded by the application.
|
* `bech32` in a URL MUST be replaced by clients with the NIP-19-encoded entity that should be loaded by the application.
|
||||||
|
|
||||||
Multiple tags might be registered by the app, following NIP-19 nomenclature as the second value of the array.
|
Multiple tags might be registered by the app, following NIP-19 nomenclature as the second value of the array.
|
||||||
|
|
||||||
A tag without a second value in the array SHOULD be considered a generic handler for any NIP-19 entity that is not handled by a different tag.
|
A tag without a second value in the array SHOULD be considered a generic handler for any NIP-19 entity that is not handled by a different tag.
|
||||||
|
|
||||||
# User flow
|
# Client tag
|
||||||
|
When publishing events, clients MAY include a `client` tag. Identifying the client that published the note. This tag is a tuple of `name`, `address` identifying a handler event and, a relay `hint` for finding the handler event. This has privacy implications for users, so clients SHOULD allow users to opt-out of using this tag.
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"kind": 1,
|
||||||
|
"tags": [
|
||||||
|
["client", "My Client", "31990:app1-pubkey:<d-identifier>", "wss://relay1"]
|
||||||
|
]
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## User flow
|
||||||
A user A who uses a non-`kind:1`-centric nostr app could choose to announce/recommend a certain kind-handler application.
|
A user A who uses a non-`kind:1`-centric nostr app could choose to announce/recommend a certain kind-handler application.
|
||||||
|
|
||||||
When user B sees an unknown event kind, e.g. in a social-media centric nostr client, the client would allow user B to interact with the unknown-kind event (e.g. tapping on it).
|
When user B sees an unknown event kind, e.g. in a social-media centric nostr client, the client would allow user B to interact with the unknown-kind event (e.g. tapping on it).
|
||||||
|
|
||||||
The client MIGHT query for the user's and the user's follows handler.
|
The client MIGHT query for the user's and the user's follows handler.
|
||||||
|
|
||||||
# Example
|
## Example
|
||||||
|
|
||||||
## User A recommends a `kind:31337`-handler
|
### User A recommends a `kind:31337`-handler
|
||||||
User A might be a user of Zapstr, a `kind:31337`-centric client (tracks). Using Zapstr, user A publishes an event recommending Zapstr as a `kind:31337`-handler.
|
User A might be a user of Zapstr, a `kind:31337`-centric client (tracks). Using Zapstr, user A publishes an event recommending Zapstr as a `kind:31337`-handler.
|
||||||
|
|
||||||
```json
|
```json
|
||||||
|
|
@ -92,25 +105,27 @@ User A might be a user of Zapstr, a `kind:31337`-centric client (tracks). Using
|
||||||
"tags": [
|
"tags": [
|
||||||
["d", "31337"],
|
["d", "31337"],
|
||||||
["a", "31990:1743058db7078661b94aaf4286429d97ee5257d14a86d6bfa54cb0482b876fb0:abcd", <relay-url>, "web"]
|
["a", "31990:1743058db7078661b94aaf4286429d97ee5257d14a86d6bfa54cb0482b876fb0:abcd", <relay-url>, "web"]
|
||||||
]
|
],
|
||||||
|
...
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
## User B interacts with a `kind:31337`-handler
|
### User B interacts with a `kind:31337`-handler
|
||||||
User B might see in their timeline an event referring to a `kind:31337` event
|
User B might see in their timeline an event referring to a `kind:31337` event (e.g. a `kind:1` tagging a `kind:31337`).
|
||||||
(e.g. a `kind:1` tagging a `kind:31337`).
|
|
||||||
|
|
||||||
User B's client, not knowing how to handle a `kind:31337` might display the event
|
User B's client, not knowing how to handle a `kind:31337` might display the event using its `alt` tag (as described in NIP-31). When the user clicks on the event, the application queries for a handler for this `kind`:
|
||||||
using its `alt` tag (as described in NIP-31). When the user clicks on the event,
|
|
||||||
the application queries for a handler for this `kind`:
|
|
||||||
|
|
||||||
`["REQ", <id>, '[{ "kinds": [31989], "#d": ["31337"], 'authors': [<user>, <users-contact-list>] }]']`
|
```json
|
||||||
|
["REQ", <id>, '[{ "kinds": [31989], "#d": ["31337"], 'authors': [<user>, <users-contact-list>] }]']
|
||||||
|
```
|
||||||
|
|
||||||
User B, who follows User A, sees that `kind:31989` event and fetches the `a`-tagged event for the app and handler information.
|
User B, who follows User A, sees that `kind:31989` event and fetches the `a`-tagged event for the app and handler information.
|
||||||
|
|
||||||
User B's client sees the application's `kind:31990` which includes the information to redirect the user to the relevant URL with the desired entity replaced in the URL.
|
User B's client sees the application's `kind:31990` which includes the information to redirect the user to the relevant URL with the desired entity replaced in the URL.
|
||||||
|
|
||||||
## Alternative query bypassing `kind:31989`
|
### Alternative query bypassing `kind:31989`
|
||||||
Alternatively, users might choose to query directly for `kind:31990` for an event kind. Clients SHOULD be careful doing this and use spam-prevention mechanisms to avoid directing users to malicious handlers.
|
Alternatively, users might choose to query directly for `kind:31990` for an event kind. Clients SHOULD be careful doing this and use spam-prevention mechanisms or querying high-quality restricted relays to avoid directing users to malicious handlers.
|
||||||
|
|
||||||
`["REQ", <id>, '[{ "kinds": [31990], "#k": [<desired-event-kind>], 'authors': [...] }]']`
|
```json
|
||||||
|
["REQ", <id>, '[{ "kinds": [31990], "#k": [<desired-event-kind>], 'authors': [...] }]']
|
||||||
|
```
|
||||||
|
|
|
||||||
230
90.md
Normal file
230
90.md
Normal file
|
|
@ -0,0 +1,230 @@
|
||||||
|
NIP-90
|
||||||
|
======
|
||||||
|
|
||||||
|
Data Vending Machine
|
||||||
|
--------------------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
This NIP defines the interaction between customers and Service Providers for performing on-demand computation.
|
||||||
|
|
||||||
|
Money in, data out.
|
||||||
|
|
||||||
|
## Kinds
|
||||||
|
This NIP reserves the range `5000-7000` for data vending machine use.
|
||||||
|
|
||||||
|
| Kind | Description |
|
||||||
|
| ---- | ----------- |
|
||||||
|
| 5000-5999 | Job request kinds |
|
||||||
|
| 6000-6999 | Job result |
|
||||||
|
| 7000 | Job feedback |
|
||||||
|
|
||||||
|
Job results always use a kind number that is `1000` higher than the job request kind. (e.g. request: `kind:5001` gets a result: `kind:6001`).
|
||||||
|
|
||||||
|
Job request types are defined [separately](https://github.com/nostr-protocol/data-vending-machines/tree/master/kinds).
|
||||||
|
|
||||||
|
## Rationale
|
||||||
|
Nostr can act as a marketplace for data processing, where users request jobs to be processed in certain ways (e.g., "speech-to-text", "summarization", etc.), but they don't necessarily care about "who" processes the data.
|
||||||
|
|
||||||
|
This NIP is not to be confused with a 1:1 marketplace; instead, it describes a flow where a user announces a desired output, willingness to pay, and service providers compete to fulfill the job requirement in the best way possible.
|
||||||
|
|
||||||
|
### Actors
|
||||||
|
There are two actors in the workflow described in this NIP:
|
||||||
|
* Customers (npubs who request a job)
|
||||||
|
* Service providers (npubs who fulfill jobs)
|
||||||
|
|
||||||
|
## Job request (`kind:5000-5999`)
|
||||||
|
A request to process data, published by a customer. This event signals that a customer is interested in receiving the result of some kind of compute.
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"kind": 5xxx, // kind in 5000-5999 range
|
||||||
|
"content": "",
|
||||||
|
"tags": [
|
||||||
|
[ "i", "<data>", "<input-type>", "<relay>", "<marker>" ],
|
||||||
|
[ "output", "<mime-type>" ],
|
||||||
|
[ "relays", "wss://..." ],
|
||||||
|
[ "bid", "<msat-amount>" ],
|
||||||
|
[ "t", "bitcoin" ]
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
All tags are optional.
|
||||||
|
|
||||||
|
* `i` tag: Input data for the job (zero or more inputs)
|
||||||
|
* `<data>`: The argument for the input
|
||||||
|
* `<input-type>`: The way this argument should be interpreted. MUST be one of:
|
||||||
|
* `url`: A URL to be fetched of the data that should be processed.
|
||||||
|
* `event`: A Nostr event ID.
|
||||||
|
* `job`: The output of a previous job with the specified event ID. The dermination of which output to build upon is up to the service provider to decide (e.g. waiting for a signaling from the customer, waiting for a payment, etc.)
|
||||||
|
* `text`: `<data>` is the value of the input, no resolution is needed
|
||||||
|
* `<relay>`: If `event` or `job` input-type, the relay where the event/job was published, otherwise optional or empty string
|
||||||
|
* `<marker>`: An optional field indicating how this input should be used within the context of the job
|
||||||
|
* `output`: Expected output format. Different job request `kind` defines this more precisely.
|
||||||
|
* `param`: Optional parameters for the job as key (first argument)/value (second argument). Different job request `kind` defines this more precisely. (e.g. `[ "param", "lang", "es" ]`)
|
||||||
|
* `bid`: Customer MAY specify a maximum amount (in millisats) they are willing to pay
|
||||||
|
* `relays`: List of relays where Service Providers SHOULD publish responses to
|
||||||
|
* `p`: Service Providers the customer is interested in. Other SPs MIGHT still choose to process the job
|
||||||
|
|
||||||
|
## Encrypted Params
|
||||||
|
|
||||||
|
If the user wants to keep the input parameters a secret, they can encrypt the `i` and `param` tags with the service provider's 'p' tag and add it to the content field. Add a tag `encrypted` as tags. Encryption for private tags will use [NIP-04 - Encrypted Direct Message encryption](https://github.com/nostr-protocol/nips/blob/master/04.md), using the user's private and service provider's public key for the shared secret
|
||||||
|
|
||||||
|
```json
|
||||||
|
[
|
||||||
|
["i", "what is the capital of France? ", "text"],
|
||||||
|
["param", "model", "LLaMA-2"],
|
||||||
|
["param", "max_tokens", "512"],
|
||||||
|
["param", "temperature", "0.5"],
|
||||||
|
["param", "top-k", "50"],
|
||||||
|
["param", "top-p", "0.7"],
|
||||||
|
["param", "frequency_penalty", "1"]
|
||||||
|
]
|
||||||
|
|
||||||
|
```
|
||||||
|
|
||||||
|
This param data will be encrypted and added to the `content` field and `p` tag should be present
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"content": "BE2Y4xvS6HIY7TozIgbEl3sAHkdZoXyLRRkZv4fLPh3R7LtviLKAJM5qpkC7D6VtMbgIt4iNcMpLtpo...",
|
||||||
|
"tags": [
|
||||||
|
["p", "04f74530a6ede6b24731b976b8e78fb449ea61f40ff10e3d869a3030c4edc91f"],
|
||||||
|
["encrypted"]
|
||||||
|
],
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
|
||||||
|
## Job result (`kind:6000-6999`)
|
||||||
|
|
||||||
|
Service providers publish job results, providing the output of the job result. They should tag the original job request event id as well as the customer's pubkey.
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"pubkey": "<service-provider pubkey>",
|
||||||
|
"content": "<payload>",
|
||||||
|
"kind": 6xxx,
|
||||||
|
"tags": [
|
||||||
|
["request", "<job-request>"],
|
||||||
|
["e", "<job-request-id>", "<relay-hint>"],
|
||||||
|
["i", "<input-data>"],
|
||||||
|
["p", "<customer's-pubkey>"],
|
||||||
|
["amount", "requested-payment-amount", "<optional-bolt11>"]
|
||||||
|
],
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
* `request`: The job request event stringified-JSON.
|
||||||
|
* `amount`: millisats that the Service Provider is requesting to be paid. An optional third value can be a bolt11 invoice.
|
||||||
|
* `i`: The original input(s) specified in the request.
|
||||||
|
|
||||||
|
## Encrypted Output
|
||||||
|
|
||||||
|
If the request has encrypted params, then output should be encrypted and placed in `content` field. If the output is encrypted, then avoid including `i` tag with input-data as clear text.
|
||||||
|
Add a tag encrypted to mark the output content as `encrypted`
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"pubkey": "<service-provider pubkey>",
|
||||||
|
"content": "<encrypted payload>",
|
||||||
|
"kind": 6xxx,
|
||||||
|
"tags": [
|
||||||
|
["request", "<job-request>"],
|
||||||
|
["e", "<job-request-id>", "<relay-hint>"],
|
||||||
|
["p", "<customer's-pubkey>"],
|
||||||
|
["amount", "requested-payment-amount", "<optional-bolt11>"],
|
||||||
|
["encrypted"]
|
||||||
|
],
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## Job feedback
|
||||||
|
|
||||||
|
Service providers can give feedback about a job back to the customer.
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"kind": 7000,
|
||||||
|
"content": "<empty-or-payload>",
|
||||||
|
"tags": [
|
||||||
|
["status", "<status>", "<extra-info>"],
|
||||||
|
["amount", "requested-payment-amount", "<bolt11>"],
|
||||||
|
["e", "<job-request-id>", "<relay-hint>"],
|
||||||
|
["p", "<customer's-pubkey>"],
|
||||||
|
],
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
* `content`: Either empty or a job-result (e.g. for partial-result samples)
|
||||||
|
* `amount` tag: as defined in the [Job Result](#job-result-kind6000-6999) section.
|
||||||
|
* `status` tag: Service Providers SHOULD indicate what this feedback status refers to. [Job Feedback Status](#job-feedback-status) defines status. Extra human-readable information can be added as an extra argument.
|
||||||
|
|
||||||
|
* NOTE: If the input params requires input to be encrypted, then `content` field will have encrypted payload with `p` tag as key.
|
||||||
|
|
||||||
|
### Job feedback status
|
||||||
|
|
||||||
|
| status | description |
|
||||||
|
| -------- | ------------- |
|
||||||
|
| `payment-required` | Service Provider requires payment before continuing. |
|
||||||
|
| `processing` | Service Provider is processing the job. |
|
||||||
|
| `error` | Service Provider was unable to process the job. |
|
||||||
|
| `success` | Service Provider successfully processed the job. |
|
||||||
|
| `partial` | Service Provider partially processed the job. The `.content` might include a sample of the partial results. |
|
||||||
|
|
||||||
|
Any job feedback event MIGHT include results in the `.content` field, as described in the [Job Result](#job-result-kind6000-6999) section. This is useful for service providers to provide a sample of the results that have been processed so far.
|
||||||
|
|
||||||
|
|
||||||
|
# Protocol Flow
|
||||||
|
|
||||||
|
* Customer publishes a job request (e.g. `kind:5000` speech-to-text).
|
||||||
|
* Service Providers MAY submit `kind:7000` job-feedback events (e.g. `payment-required`, `processing`, `error`, etc.).
|
||||||
|
* Upon completion, the service provider publishes the result of the job with a `kind:6000` job-result event.
|
||||||
|
* At any point, if there is an `amount` pending to be paid as instructed by the service provider, the user can pay the included `bolt11` or zap the job result event the service provider has sent to the user
|
||||||
|
|
||||||
|
Job feedback (`kind:7000`) and Job Results (`kind:6000-6999`) events MAY include an `amount` tag, this can be interpreted as a suggestion to pay. Service Providers MUST use the `payment-required` feedback event to signal that a payment is required and no further actions will be performed until the payment is sent.
|
||||||
|
|
||||||
|
Customers can always either pay the included `bolt11` invoice or zap the event requesting the payment and service providers should monitor for both if they choose to include a bolt11 invoice.
|
||||||
|
|
||||||
|
## Notes about the protocol flow
|
||||||
|
The flow is deliberately ambiguous, allowing vast flexibility for the interaction between customers and service providers so that service providers can model their behavior based on their own decisions/perceptions of risk.
|
||||||
|
|
||||||
|
Some service providers might choose to submit a `payment-required` as the first reaction before sending a `processing` or before delivering results, some might choose to serve partial results for the job (e.g. a sample), send a `payment-required` to deliver the rest of the results, and some service providers might choose to assess likelihood of payment based on an npub's past behavior and thus serve the job results before requesting payment for the best possible UX.
|
||||||
|
|
||||||
|
It's not up to this NIP to define how individual vending machines should choose to run their business.
|
||||||
|
|
||||||
|
# Cancellation
|
||||||
|
A job request might be canceled by publishing a `kind:5` delete request event tagging the job request event.
|
||||||
|
|
||||||
|
# Appendix 1: Job chaining
|
||||||
|
A Customer MAY request multiple jobs to be processed as a chain, where the output of a job is the input of another job. (e.g. podcast transcription -> summarization of the transcription). This is done by specifying as input an event id of a different job with the `job` type.
|
||||||
|
|
||||||
|
Service Providers MAY begin processing a subsequent job the moment they see the prior job's result, but they will likely wait for a zap to be published first. This introduces a risk that Service Provider of job #1 might delay publishing the zap event in order to have an advantage. This risk is up to Service Providers to mitigate or to decide whether the service provider of job #1 tends to have good-enough results so as to not wait for an explicit zap to assume the job was accepted.
|
||||||
|
|
||||||
|
This gives a higher level of flexibility to service providers (which sophisticated service providers would take anyway).
|
||||||
|
|
||||||
|
# Appendix 2: Service provider discoverability
|
||||||
|
Service Providers MAY use NIP-89 announcements to advertise their support for job kinds:
|
||||||
|
|
||||||
|
```js
|
||||||
|
{
|
||||||
|
"kind": 31990,
|
||||||
|
"pubkey": "<pubkey>",
|
||||||
|
"content": "{
|
||||||
|
\"name\": \"Translating DVM\",
|
||||||
|
\"about\": \"I'm a DVM specialized in translating Bitcoin content.\"
|
||||||
|
}",
|
||||||
|
"tags": [
|
||||||
|
["k", "5005"], // e.g. translation
|
||||||
|
["t", "bitcoin"] // e.g. optionally advertises it specializes in bitcoin audio transcription that won't confuse "Drivechains" with "Ridechains"
|
||||||
|
],
|
||||||
|
...
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Customers can use NIP-89 to see what service providers their follows use.
|
||||||
45
92.md
Normal file
45
92.md
Normal file
|
|
@ -0,0 +1,45 @@
|
||||||
|
NIP-92
|
||||||
|
======
|
||||||
|
|
||||||
|
Media Attachments
|
||||||
|
-----------------
|
||||||
|
|
||||||
|
Media attachments (images, videos, and other files) may be added to events by including a URL in the event content, along with a matching `imeta` tag.
|
||||||
|
|
||||||
|
`imeta` ("inline metadata") tags add information about media URLs in the event's content. Each `imeta` tag SHOULD match a URL in the event content. Clients may replace imeta URLs with rich previews.
|
||||||
|
|
||||||
|
The `imeta` tag is variadic, and each entry is a space-delimited key/value pair.
|
||||||
|
Each `imeta` tag MUST have a `url`, and at least one other field. `imeta` may include
|
||||||
|
any field specified by [NIP 94](./94.md). There SHOULD be only one `imeta` tag per URL.
|
||||||
|
|
||||||
|
## Example
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"content": "More image metadata tests don’t mind me https://nostr.build/i/my-image.jpg",
|
||||||
|
"kind": 1,
|
||||||
|
"tags": [
|
||||||
|
[
|
||||||
|
"imeta",
|
||||||
|
"url https://nostr.build/i/my-image.jpg",
|
||||||
|
"m image/jpeg",
|
||||||
|
"blurhash eVF$^OI:${M{o#*0-nNFxakD-?xVM}WEWB%iNKxvR-oetmo#R-aen$",
|
||||||
|
"dim 3024x4032",
|
||||||
|
"alt A scenic photo overlooking the coast of Costa Rica",
|
||||||
|
"x <sha256 hash as specified in NIP 94>",
|
||||||
|
"fallback https://nostrcheck.me/alt1.jpg",
|
||||||
|
"fallback https://void.cat/alt1.jpg"
|
||||||
|
]
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## Recommended client behavior
|
||||||
|
|
||||||
|
When uploading files during a new post, clients MAY include this metadata
|
||||||
|
after the file is uploaded and included in the post.
|
||||||
|
|
||||||
|
When pasting URLs during post composition, the client MAY download the file
|
||||||
|
and add this metadata before the post is sent.
|
||||||
|
|
||||||
|
The client MAY ignore `imeta` tags that do not match the URL in the event content.
|
||||||
28
94.md
28
94.md
|
|
@ -4,43 +4,49 @@ NIP-94
|
||||||
File Metadata
|
File Metadata
|
||||||
-------------
|
-------------
|
||||||
|
|
||||||
`draft` `optional` `author:frbitten` `author:kieran` `author:lovvtide` `author:fiatjaf` `author:staab`
|
`draft` `optional`
|
||||||
|
|
||||||
The purpose of this NIP is to allow an organization and classification of shared files. So that relays can filter and organize in any way that is of interest. With that, multiple types of filesharing clients can be created. NIP-94 support is not expected to be implemented by "social" clients that deal with kind:1 notes or by longform clients that deal with kind:30023 articles.
|
The purpose of this NIP is to allow an organization and classification of shared files. So that relays can filter and organize in any way that is of interest. With that, multiple types of filesharing clients can be created. NIP-94 support is not expected to be implemented by "social" clients that deal with `kind:1` notes or by longform clients that deal with `kind:30023` articles.
|
||||||
|
|
||||||
## Event format
|
## Event format
|
||||||
|
|
||||||
This NIP specifies the use of the `1063` event type, having in `content` a description of the file content, and a list of tags described below:
|
This NIP specifies the use of the `1063` event type, having in `content` a description of the file content, and a list of tags described below:
|
||||||
|
|
||||||
* `url` the url to download the file
|
* `url` the url to download the file
|
||||||
* `m` a string indicating the data type of the file. The MIME types format must be used (https://developer.mozilla.org/en-US/docs/Web/HTTP/Basics_of_HTTP/MIME_types/Common_types)
|
* `m` a string indicating the data type of the file. The [MIME types](https://developer.mozilla.org/en-US/docs/Web/HTTP/Basics_of_HTTP/MIME_types/Common_types) format must be used, and they should be lowercase.
|
||||||
* `"aes-256-gcm"` (optional) key and nonce for AES-GCM encryption with tagSize always 128bits
|
|
||||||
* `x` containing the SHA-256 hexencoded string of the file.
|
* `x` containing the SHA-256 hexencoded string of the file.
|
||||||
|
* `ox` containing the SHA-256 hexencoded string of the original file, before any transformations done by the upload server
|
||||||
* `size` (optional) size of file in bytes
|
* `size` (optional) size of file in bytes
|
||||||
* `dim` (optional) size of file in pixels in the form `<width>x<height>`
|
* `dim` (optional) size of file in pixels in the form `<width>x<height>`
|
||||||
* `magnet` (optional) URI to magnet file
|
* `magnet` (optional) URI to magnet file
|
||||||
* `i` (optional) torrent infohash
|
* `i` (optional) torrent infohash
|
||||||
* `blurhash`(optional) the [blurhash](https://github.com/woltapp/blurhash) to show while the file is being loaded by the client
|
* `blurhash`(optional) the [blurhash](https://github.com/woltapp/blurhash) to show while the file is being loaded by the client
|
||||||
|
* `thumb` (optional) url of thumbnail with same aspect ratio
|
||||||
|
* `image` (optional) url of preview image with same dimensions
|
||||||
|
* `summary` (optional) text excerpt
|
||||||
|
* `alt` (optional) description for accessibility
|
||||||
|
* `fallback` (optional) zero or more fallback file sources in case `url` fails
|
||||||
|
|
||||||
```json
|
```json
|
||||||
{
|
{
|
||||||
"id": <32-bytes lowercase hex-encoded sha256 of the the serialized event data>,
|
|
||||||
"pubkey": <32-bytes lowercase hex-encoded public key of the event creator>,
|
|
||||||
"created_at": <unix timestamp in seconds>,
|
|
||||||
"kind": 1063,
|
"kind": 1063,
|
||||||
"tags": [
|
"tags": [
|
||||||
["url",<string with URI of file>],
|
["url",<string with URI of file>],
|
||||||
["aes-256-gcm",<key>, <iv>],
|
|
||||||
["m", <MIME type>],
|
["m", <MIME type>],
|
||||||
["x",<Hash SHA-256>],
|
["x",<Hash SHA-256>],
|
||||||
|
["ox",<Hash SHA-256>],
|
||||||
["size", <size of file in bytes>],
|
["size", <size of file in bytes>],
|
||||||
["dim", <size of file in pixels>],
|
["dim", <size of file in pixels>],
|
||||||
["magnet",<magnet URI> ],
|
["magnet",<magnet URI> ],
|
||||||
["i",<torrent infohash>],
|
["i",<torrent infohash>],
|
||||||
["blurhash", <value>]
|
["blurhash", <value>],
|
||||||
|
["thumb", <string with thumbnail URI>],
|
||||||
|
["image", <string with preview URI>],
|
||||||
|
["summary", <excerpt>],
|
||||||
|
["alt", <description>]
|
||||||
],
|
],
|
||||||
"content": <description>,
|
"content": "<caption>",
|
||||||
"sig": <64-bytes hex of the signature of the sha256 hash of the serialized event data, which is the same as the "id" field>
|
...
|
||||||
}
|
}
|
||||||
```
|
```
|
||||||
|
|
||||||
|
|
|
||||||
295
96.md
Normal file
295
96.md
Normal file
|
|
@ -0,0 +1,295 @@
|
||||||
|
NIP-96
|
||||||
|
======
|
||||||
|
|
||||||
|
HTTP File Storage Integration
|
||||||
|
-----------------------------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
## Introduction
|
||||||
|
|
||||||
|
This NIP defines a REST API for HTTP file storage servers intended to be used in conjunction with the nostr network.
|
||||||
|
The API will enable nostr users to upload files and later reference them by url on nostr notes.
|
||||||
|
|
||||||
|
The spec DOES NOT use regular nostr events through websockets for
|
||||||
|
storing, requesting nor retrieving data because, for simplicity, the server
|
||||||
|
will not have to learn anything about nostr relays.
|
||||||
|
|
||||||
|
## Server Adaptation
|
||||||
|
|
||||||
|
File storage servers wishing to be accessible by nostr users should opt-in by making available an https route at `/.well-known/nostr/nip96.json` with `api_url`:
|
||||||
|
|
||||||
|
```js
|
||||||
|
{
|
||||||
|
// Required
|
||||||
|
// File upload and deletion are served from this url
|
||||||
|
// Also downloads if "download_url" field is absent or empty string
|
||||||
|
"api_url": "https://your-file-server.example/custom-api-path",
|
||||||
|
// Optional
|
||||||
|
// If absent, downloads are served from the api_url
|
||||||
|
"download_url": "https://a-cdn.example/a-path",
|
||||||
|
// Optional
|
||||||
|
// Note: This field is not meant to be set by HTTP Servers.
|
||||||
|
// Use this if you are a nostr relay using your /.well-known/nostr/nip96.json
|
||||||
|
// just to redirect to someone else's http file storage server's /.well-known/nostr/nip96.json
|
||||||
|
// In this case, "api_url" field must be an empty string
|
||||||
|
"delegated_to_url": "https://your-file-server.example",
|
||||||
|
// Optional
|
||||||
|
"supported_nips": [60],
|
||||||
|
// Optional
|
||||||
|
"tos_url": "https://your-file-server.example/terms-of-service",
|
||||||
|
// Optional
|
||||||
|
"content_types": ["image/jpeg", "video/webm", "audio/*"],
|
||||||
|
// Optional
|
||||||
|
"plans": {
|
||||||
|
// "free" is the only standardized plan key and
|
||||||
|
// clients may use its presence to learn if server offers free storage
|
||||||
|
"free": {
|
||||||
|
"name": "Free Tier",
|
||||||
|
// Default is true
|
||||||
|
// All plans MUST support NIP-98 uploads
|
||||||
|
// but some plans may also allow uploads without it
|
||||||
|
"is_nip98_required": true,
|
||||||
|
"url": "https://...", // plan's landing page if there is one
|
||||||
|
"max_byte_size": 10485760,
|
||||||
|
// Range in days / 0 for no expiration
|
||||||
|
// [7, 0] means it may vary from 7 days to unlimited persistence,
|
||||||
|
// [0, 0] means it has no expiration
|
||||||
|
// early expiration may be due to low traffic or any other factor
|
||||||
|
"file_expiration": [14, 90],
|
||||||
|
"media_transformations": {
|
||||||
|
"image": [
|
||||||
|
'resizing'
|
||||||
|
]
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
### Relay Hints
|
||||||
|
|
||||||
|
Note: This section is not meant to be used by HTTP Servers.
|
||||||
|
|
||||||
|
A nostr relay MAY redirect to someone else's HTTP file storage server by
|
||||||
|
adding a `/.well-known/nostr/nip96.json` with "delegated_to_url" field
|
||||||
|
pointing to the url where the server hosts its own
|
||||||
|
`/.well-known/nostr/nip96.json`. In this case, the "api_url" field must
|
||||||
|
be an empty string and all other fields must be absent.
|
||||||
|
|
||||||
|
If the nostr relay is also an HTTP file storage server,
|
||||||
|
it must use the "api_url" field instead.
|
||||||
|
|
||||||
|
### List of Supporting File Storage Servers
|
||||||
|
|
||||||
|
See https://github.com/aljazceru/awesome-nostr#nip-96-file-storage-servers.
|
||||||
|
|
||||||
|
## Upload
|
||||||
|
|
||||||
|
A file can be uploaded one at a time to `https://your-file-server.example/custom-api-path` (route from `https://your-file-server.example/.well-known/nostr/nip96.json` "api_url" field) as `multipart/form-data` content type using `POST` method with the file object set to the `file` form data field.
|
||||||
|
|
||||||
|
`Clients` must add an [NIP-98](98.md) `Authorization` header (**optionally** with the encoded `payload` tag set to the base64-encoded 256-bit SHA-256 hash of the file - not the hash of the whole request body).
|
||||||
|
If using an html form, use an `Authorization` form data field instead.
|
||||||
|
|
||||||
|
These following **optional** form data fields MAY be used by `servers` and SHOULD be sent by `clients`:
|
||||||
|
- `expiration`: string of the UNIX timestamp in seconds. Empty string if file should be stored forever. The server isn't required to honor this;
|
||||||
|
- `size`: string of the file byte size. This is just a value the server can use to reject early if the file size exceeds the server limits;
|
||||||
|
- `alt`: (recommended) strict description text for visibility-impaired users;
|
||||||
|
- `caption`: loose description;
|
||||||
|
- `media_type`: "avatar" or "banner". Informs the server if the file will be used as an avatar or banner. If absent, the server will interpret it as a normal upload, without special treatment;
|
||||||
|
- `content_type`: mime type such as "image/jpeg". This is just a value the server can use to reject early if the mime type isn't supported.
|
||||||
|
|
||||||
|
|
||||||
|
Others custom form data fields may be used depending on specific `server` support.
|
||||||
|
The `server` isn't required to store any metadata sent by `clients`.
|
||||||
|
|
||||||
|
Note for `clients`: if using an HTML form, it is important for the `file` form field to be the **last** one, or be re-ordered right before sending or be appended as the last field of XHR2's FormData object.
|
||||||
|
|
||||||
|
The `filename` embedded in the file may not be honored by the `server`, which could internally store just the SHA-256 hash value as the file name, ignoring extra metadata.
|
||||||
|
The hash is enough to uniquely identify a file, that's why it will be used on the "download" and "delete" routes.
|
||||||
|
|
||||||
|
The `server` MUST link the user's `pubkey` string (which is embedded in the decoded header value) as the owner of the file so to later allow them to delete the file.
|
||||||
|
Note that if a file with the same hash of a previously received file (so the same file) is uploaded by another user, the server doesn't need to store the new file.
|
||||||
|
It should just add the new user's `pubkey` to the list of the owners of the already stored file with said hash (if it wants to save space by keeping just one copy of the same file, because multiple uploads of the same file results in the same file hash).
|
||||||
|
|
||||||
|
The `server` MAY also store the `Authorization` header/field value (decoded or not) for accountability purpose as this proves that the user with the unique pubkey did ask for the upload of the file with a specific hash. However, storing the pubkey is sufficient to establish ownership.
|
||||||
|
|
||||||
|
The `server` MUST reject with 413 Payload Too Large if file size exceeds limits.
|
||||||
|
|
||||||
|
The `server` MUST reject with 400 Bad Request status if some fields are invalid.
|
||||||
|
|
||||||
|
The `server` MUST reply to the upload with 200 OK status if the `payload` tag value contains an already used SHA-256 hash (if file is already owned by the same pubkey) or reject the upload with 403 Forbidden status if it isn't the same of the received file.
|
||||||
|
|
||||||
|
The `server` MAY reject the upload with 402 Payment Required status if the user has a pending payment (Payment flow is not strictly required. Server owners decide if the storage is free or not. Monetization schemes may be added later to correlated NIPs.).
|
||||||
|
|
||||||
|
On successful uploads the `server` MUST reply with **201 Created** HTTP status code or **202 Accepted** if a `processing_url` field is added
|
||||||
|
to the response so that the `client` can follow the processing status (see [Delayed Processing](#delayed-processing) section).
|
||||||
|
|
||||||
|
The upload response is a json object as follows:
|
||||||
|
|
||||||
|
```js
|
||||||
|
{
|
||||||
|
// "success" if successful or "error" if not
|
||||||
|
status: "success",
|
||||||
|
// Free text success, failure or info message
|
||||||
|
message: "Upload successful.",
|
||||||
|
// Optional. See "Delayed Processing" section
|
||||||
|
processing_url: "...",
|
||||||
|
// This uses the NIP-94 event format but DO NOT need
|
||||||
|
// to fill some fields like "id", "pubkey", "created_at" and "sig"
|
||||||
|
//
|
||||||
|
// This holds the download url ("url"),
|
||||||
|
// the ORIGINAL file hash before server transformations ("ox")
|
||||||
|
// and, optionally, all file metadata the server wants to make available
|
||||||
|
//
|
||||||
|
// nip94_event field is absent if unsuccessful upload
|
||||||
|
nip94_event: {
|
||||||
|
// Required tags: "url" and "ox"
|
||||||
|
tags: [
|
||||||
|
// Can be same from /.well-known/nostr/nip96.json's "download_url" field
|
||||||
|
// (or "api_url" field if "download_url" is absent or empty) with appended
|
||||||
|
// original file hash.
|
||||||
|
//
|
||||||
|
// Note we appended .png file extension to the `ox` value
|
||||||
|
// (it is optional but extremely recommended to add the extension as it will help nostr clients
|
||||||
|
// with detecting the file type by using regular expression)
|
||||||
|
//
|
||||||
|
// Could also be any url to download the file
|
||||||
|
// (using or not using the /.well-known/nostr/nip96.json's "download_url" prefix),
|
||||||
|
// for load balancing purposes for example.
|
||||||
|
["url", "https://your-file-server.example/custom-api-path/719171db19525d9d08dd69cb716a18158a249b7b3b3ec4bbdec5698dca104b7b.png"],
|
||||||
|
// SHA-256 hash of the ORIGINAL file, before transformations.
|
||||||
|
// The server MUST store it even though it represents the ORIGINAL file because
|
||||||
|
// users may try to download/delete the transformed file using this value
|
||||||
|
["ox", "719171db19525d9d08dd69cb716a18158a249b7b3b3ec4bbdec5698dca104b7b"],
|
||||||
|
// Optional. SHA-256 hash of the saved file after any server transformations.
|
||||||
|
// The server can but does not need to store this value.
|
||||||
|
["x", "543244319525d9d08dd69cb716a18158a249b7b3b3ec4bbde5435543acb34443"],
|
||||||
|
// Optional. Recommended for helping clients to easily know file type before downloading it.
|
||||||
|
["m", "image/png"]
|
||||||
|
// Optional. Recommended for helping clients to reserve an adequate UI space to show the file before downloading it.
|
||||||
|
["dim", "800x600"]
|
||||||
|
// ... other optional NIP-94 tags
|
||||||
|
],
|
||||||
|
content: ""
|
||||||
|
},
|
||||||
|
// ... other custom fields (please consider adding them to this NIP or to NIP-94 tags)
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
Note that if the server didn't apply any transformation to the received file, both `nip94_event.tags.*.ox` and `nip94_event.tags.*.x` fields will have the same value. The server MUST link the saved file to the SHA-256 hash of the **original** file before any server transformations (the `nip94_event.tags.*.ox` tag value). The **original** file's SHA-256 hash will be used to identify the saved file when downloading or deleting it.
|
||||||
|
|
||||||
|
`Clients` may upload the same file to one or many `servers`.
|
||||||
|
After successful upload, the `client` may optionally generate and send to any set of nostr `relays` a [NIP-94](94.md) event by including the missing fields.
|
||||||
|
|
||||||
|
Alternatively, instead of using NIP-94, the `client` can share or embed on a nostr note just the above url.
|
||||||
|
|
||||||
|
### Delayed Processing
|
||||||
|
|
||||||
|
Sometimes the server may want to place the uploaded file in a processing queue for deferred file processing.
|
||||||
|
|
||||||
|
In that case, the server MUST serve the original file while the processing isn't done, then swap the original file for the processed one when the processing is over. The upload response is the same as usual but some optional metadata like `nip94_event.tags.*.x` and `nip94_event.tags.*.size` won't be available.
|
||||||
|
|
||||||
|
The expected resulting metadata that is known in advance should be returned on the response.
|
||||||
|
For example, if the file processing would change a file from "jpg" to "webp",
|
||||||
|
use ".webp" extension on the `nip94_event.tags.*.url` field value and set "image/webp" to the `nip94_event.tags.*.m` field.
|
||||||
|
If some metadata are unknown before processing ends, omit them from the response.
|
||||||
|
|
||||||
|
The upload response MAY include a `processing_url` field informing a temporary url that may be used by clients to check if
|
||||||
|
the file processing is done.
|
||||||
|
|
||||||
|
If the processing isn't done, the server should reply at the `processing_url` url with **200 OK** and the following JSON:
|
||||||
|
|
||||||
|
```
|
||||||
|
{
|
||||||
|
// It should be "processing". If "error" it would mean the processing failed.
|
||||||
|
status: "processing",
|
||||||
|
message: "Processing. Please check again later for updated status.",
|
||||||
|
percentage: 15 // Processing percentage. An integer between 0 and 100.
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
When the processing is over, the server replies at the `processing_url` url with **201 Created** status and a regular successful JSON response already mentioned before (now **without** a `processing_url` field), possibly including optional metadata at `nip94_event.tags.*` fields
|
||||||
|
that weren't available before processing.
|
||||||
|
|
||||||
|
### File compression
|
||||||
|
|
||||||
|
File compression and other transformations like metadata stripping can be applied by the server.
|
||||||
|
However, for all file actions, such as download and deletion, the **original** file SHA-256 hash is what identifies the file in the url string.
|
||||||
|
|
||||||
|
## Download
|
||||||
|
|
||||||
|
`Servers` must make available the route `https://your-file-server.example/custom-api-path/<sha256-file-hash>(.ext)` (route taken from `https://your-file-server.example/.well-known/nostr/nip96.json` "api_url" or "download_url" field) with `GET` method for file download.
|
||||||
|
|
||||||
|
The primary file download url informed at the upload's response field `nip94_event.tags.*.url`
|
||||||
|
can be that or not (it can be any non-standard url the server wants).
|
||||||
|
If not, the server still MUST also respond to downloads at the standard url
|
||||||
|
mentioned on the previous paragraph, to make it possible for a client
|
||||||
|
to try downloading a file on any NIP-96 compatible server by knowing just the SHA-256 file hash.
|
||||||
|
|
||||||
|
Note that the "\<sha256-file-hash\>" part is from the **original** file, **not** from the **transformed** file if the uploaded file went through any server transformation.
|
||||||
|
|
||||||
|
Supporting ".ext", meaning "file extension", is required for `servers`. It is optional, although recommended, for `clients` to append it to the path.
|
||||||
|
When present it may be used by `servers` to know which `Content-Type` header to send (e.g.: "Content-Type": "image/png" for ".png" extension).
|
||||||
|
The file extension may be absent because the hash is the only needed string to uniquely identify a file.
|
||||||
|
|
||||||
|
Example: `https://your-file-server.example/custom-api-path/719171db19525d9d08dd69cb716a18158a249b7b3b3ec4bbdec5698dca104b7b.png`
|
||||||
|
|
||||||
|
### Media Transformations
|
||||||
|
|
||||||
|
`Servers` may respond to some media transformation query parameters and ignore those they don't support by serving
|
||||||
|
the original media file without transformations.
|
||||||
|
|
||||||
|
#### Image Transformations
|
||||||
|
|
||||||
|
##### Resizing
|
||||||
|
|
||||||
|
Upon upload, `servers` may create resized image variants, such as thumbnails, respecting the original aspect ratio.
|
||||||
|
`Clients` may use the `w` query parameter to request an image version with the desired pixel width.
|
||||||
|
`Servers` can then serve the variant with the closest width to the parameter value
|
||||||
|
or an image variant generated on the fly.
|
||||||
|
|
||||||
|
Example: `https://your-file-server.example/custom-api-path/<sha256-file-hash>.png?w=32`
|
||||||
|
|
||||||
|
## Deletion
|
||||||
|
|
||||||
|
`Servers` must make available the route `https://deletion.domain/deletion-path/<sha256-file-hash>(.ext)` (route taken from `https://your-file-server.example/.well-known/nostr/nip96.json` "api_url" field) with `DELETE` method for file deletion.
|
||||||
|
|
||||||
|
Note that the "\<sha256-file-hash\>" part is from the **original** file, **not** from the **transformed** file if the uploaded file went through any server transformation.
|
||||||
|
|
||||||
|
The extension is optional as the file hash is the only needed file identification.
|
||||||
|
|
||||||
|
`Clients` should send a `DELETE` request to the server deletion route in the above format. It must include a NIP-98 `Authorization` header.
|
||||||
|
|
||||||
|
The `server` should reject deletes from users other than the original uploader. The `pubkey` encoded on the header value identifies the user.
|
||||||
|
|
||||||
|
It should be noted that more than one user may have uploaded the same file (with the same hash). In this case, a delete must not really delete the file but just remove the user's `pubkey` from the file owners list (considering the server keeps just one copy of the same file, because multiple uploads of the same file results
|
||||||
|
in the same file hash).
|
||||||
|
|
||||||
|
The successful response is a 200 OK one with just basic JSON fields:
|
||||||
|
|
||||||
|
```
|
||||||
|
{
|
||||||
|
status: "success",
|
||||||
|
message: "File deleted."
|
||||||
|
}
|
||||||
|
```
|
||||||
|
|
||||||
|
## Selecting a Server
|
||||||
|
|
||||||
|
Note: HTTP File Storage Server developers may skip this section. This is meant for client developers.
|
||||||
|
|
||||||
|
A File Server Preference event is a kind 10096 replaceable event meant to select one or more servers the user wants
|
||||||
|
to upload files to. Servers are listed as `server` tags:
|
||||||
|
|
||||||
|
```js
|
||||||
|
{
|
||||||
|
// ...
|
||||||
|
"kind": 10096,
|
||||||
|
"content": "",
|
||||||
|
"tags": [
|
||||||
|
["server", "https://file.server.one"],
|
||||||
|
["server", "https://file.server.two"]
|
||||||
|
]
|
||||||
|
}
|
||||||
|
```
|
||||||
26
98.md
26
98.md
|
|
@ -2,13 +2,13 @@ NIP-98
|
||||||
======
|
======
|
||||||
|
|
||||||
HTTP Auth
|
HTTP Auth
|
||||||
-------------------------
|
---------
|
||||||
|
|
||||||
`draft` `optional` `author:kieran` `author:melvincarvalho`
|
`draft` `optional`
|
||||||
|
|
||||||
This NIP defines an ephemerial event used to authorize requests to HTTP servers using nostr events.
|
This NIP defines an ephemeral event used to authorize requests to HTTP servers using nostr events.
|
||||||
|
|
||||||
This is useful for HTTP services which are build for Nostr and deal with Nostr user accounts.
|
This is useful for HTTP services which are built for Nostr and deal with Nostr user accounts.
|
||||||
|
|
||||||
## Nostr event
|
## Nostr event
|
||||||
|
|
||||||
|
|
@ -16,7 +16,7 @@ A `kind 27235` (In reference to [RFC 7235](https://www.rfc-editor.org/rfc/rfc723
|
||||||
|
|
||||||
The `content` SHOULD be empty.
|
The `content` SHOULD be empty.
|
||||||
|
|
||||||
The following tags are defined as REQUIRED.
|
The following tags MUST be included.
|
||||||
|
|
||||||
* `u` - absolute URL
|
* `u` - absolute URL
|
||||||
* `method` - HTTP Request Method
|
* `method` - HTTP Request Method
|
||||||
|
|
@ -30,14 +30,8 @@ Example event:
|
||||||
"kind": 27235,
|
"kind": 27235,
|
||||||
"created_at": 1682327852,
|
"created_at": 1682327852,
|
||||||
"tags": [
|
"tags": [
|
||||||
[
|
["u", "https://api.snort.social/api/v1/n5sp/list"],
|
||||||
"u",
|
["method", "GET"]
|
||||||
"https://api.snort.social/api/v1/n5sp/list"
|
|
||||||
],
|
|
||||||
[
|
|
||||||
"method",
|
|
||||||
"GET"
|
|
||||||
]
|
|
||||||
],
|
],
|
||||||
"sig": "5ed9d8ec958bc854f997bdc24ac337d005af372324747efe4a00e24f4c30437ff4dd8308684bed467d9d6be3e5a517bb43b1732cc7d33949a3aaf86705c22184"
|
"sig": "5ed9d8ec958bc854f997bdc24ac337d005af372324747efe4a00e24f4c30437ff4dd8308684bed467d9d6be3e5a517bb43b1732cc7d33949a3aaf86705c22184"
|
||||||
}
|
}
|
||||||
|
|
@ -45,7 +39,7 @@ Example event:
|
||||||
|
|
||||||
Servers MUST perform the following checks in order to validate the event:
|
Servers MUST perform the following checks in order to validate the event:
|
||||||
1. The `kind` MUST be `27235`.
|
1. The `kind` MUST be `27235`.
|
||||||
2. The `created_at` MUST be within a reasonable time window (suggestion 60 seconds).
|
2. The `created_at` timestamp MUST be within a reasonable time window (suggestion 60 seconds).
|
||||||
3. The `u` tag MUST be exactly the same as the absolute request URL (including query parameters).
|
3. The `u` tag MUST be exactly the same as the absolute request URL (including query parameters).
|
||||||
4. The `method` tag MUST be the same HTTP method used for the requested resource.
|
4. The `method` tag MUST be the same HTTP method used for the requested resource.
|
||||||
|
|
||||||
|
|
@ -53,11 +47,11 @@ When the request contains a body (as in POST/PUT/PATCH methods) clients SHOULD i
|
||||||
|
|
||||||
If one of the checks was to fail the server SHOULD respond with a 401 Unauthorized response code.
|
If one of the checks was to fail the server SHOULD respond with a 401 Unauthorized response code.
|
||||||
|
|
||||||
All other checks which server MAY do are OPTIONAL, and implementation specific.
|
Servers MAY perform additional implementation-specific validation checks.
|
||||||
|
|
||||||
## Request Flow
|
## Request Flow
|
||||||
|
|
||||||
Using the `Authorization` header, the `kind 27235` event MUST be `base64` encoded and use the Authorization scheme `Nostr`
|
Using the `Authorization` HTTP header, the `kind 27235` event MUST be `base64` encoded and use the Authorization scheme `Nostr`
|
||||||
|
|
||||||
Example HTTP Authorization header:
|
Example HTTP Authorization header:
|
||||||
```
|
```
|
||||||
|
|
|
||||||
86
99.md
Normal file
86
99.md
Normal file
|
|
@ -0,0 +1,86 @@
|
||||||
|
NIP-99
|
||||||
|
======
|
||||||
|
|
||||||
|
Classified Listings
|
||||||
|
-------------------
|
||||||
|
|
||||||
|
`draft` `optional`
|
||||||
|
|
||||||
|
This NIP defines `kind:30402`: a parameterized replaceable event to describe classified listings that list any arbitrary product, service, or other thing for sale or offer and includes enough structured metadata to make them useful.
|
||||||
|
|
||||||
|
The category of classifieds includes a very broad range of physical goods, services, work opportunities, rentals, free giveaways, personals, etc. and is distinct from the more strictly structured marketplaces defined in [NIP-15](https://github.com/nostr-protocol/nips/blob/master/15.md) that often sell many units of specific products through very specific channels.
|
||||||
|
|
||||||
|
The structure of these events is very similar to [NIP-23](https://github.com/nostr-protocol/nips/blob/master/23.md) long-form content events.
|
||||||
|
|
||||||
|
### Draft / Inactive Listings
|
||||||
|
|
||||||
|
`kind:30403` has the same structure as `kind:30402` and is used to save draft or inactive classified listings.
|
||||||
|
|
||||||
|
### Content
|
||||||
|
|
||||||
|
The `.content` field should be a description of what is being offered and by whom. These events should be a string in Markdown syntax.
|
||||||
|
|
||||||
|
### Author
|
||||||
|
|
||||||
|
The `.pubkey` field of these events are treated as the party creating the listing.
|
||||||
|
|
||||||
|
### Metadata
|
||||||
|
|
||||||
|
- For "tags"/"hashtags" (i.e. categories or keywords of relevance for the listing) the `"t"` event tag should be used, as per [NIP-12](https://github.com/nostr-protocol/nips/blob/master/12.md).
|
||||||
|
- For images, whether included in the markdown content or not, clients SHOULD use `image` tags as described in [NIP-58](https://github.com/nostr-protocol/nips/blob/master/58.md). This allows clients to display images in carousel format more easily.
|
||||||
|
|
||||||
|
The following tags, used for structured metadata, are standardized and SHOULD be included. Other tags may be added as necessary.
|
||||||
|
|
||||||
|
- `"title"`, a title for the listing
|
||||||
|
- `"summary"`, for short tagline or summary for the listing
|
||||||
|
- `"published_at"`, for the timestamp (in unix seconds – converted to string) of the first time the listing was published.
|
||||||
|
- `"location"`, for the location.
|
||||||
|
- `"price"`, for the price of the thing being listed. This is an array in the format `[ "price", "<number>", "<currency>", "<frequency>" ]`.
|
||||||
|
- `"price"` is the name of the tag
|
||||||
|
- `"<number>"` is the amount in numeric format (but included in the tag as a string)
|
||||||
|
- `"<currency>"` is the currency unit in 3-character ISO 4217 format or ISO 4217-like currency code (e.g. `"btc"`, `"eth"`).
|
||||||
|
- `"<frequency>"` is optional and can be used to describe recurring payments. SHOULD be in noun format (hour, day, week, month, year, etc.)
|
||||||
|
- - `"status"` (optional), the status of the listing. SHOULD be either "active" or "sold".
|
||||||
|
|
||||||
|
#### `price` examples
|
||||||
|
|
||||||
|
- $50 one-time payment `["price", "50", "USD"]`
|
||||||
|
- €15 per month `["price", "15", "EUR", "month"]`
|
||||||
|
- £50,000 per year `["price", "50000", "GBP", "year"]`
|
||||||
|
|
||||||
|
Other standard tags that might be useful.
|
||||||
|
|
||||||
|
- `"g"`, a geohash for more precise location
|
||||||
|
|
||||||
|
## Example Event
|
||||||
|
|
||||||
|
```json
|
||||||
|
{
|
||||||
|
"kind": 30402,
|
||||||
|
"created_at": 1675642635,
|
||||||
|
// Markdown content
|
||||||
|
"content": "Lorem [ipsum][nostr:nevent1qqst8cujky046negxgwwm5ynqwn53t8aqjr6afd8g59nfqwxpdhylpcpzamhxue69uhhyetvv9ujuetcv9khqmr99e3k7mg8arnc9] dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur. Excepteur sint occaecat cupidatat non proident, sunt in culpa qui officia deserunt mollit anim id est laborum.\n\nRead more at nostr:naddr1qqzkjurnw4ksz9thwden5te0wfjkccte9ehx7um5wghx7un8qgs2d90kkcq3nk2jry62dyf50k0h36rhpdtd594my40w9pkal876jxgrqsqqqa28pccpzu.",
|
||||||
|
"tags": [
|
||||||
|
["d", "lorem-ipsum"],
|
||||||
|
["title", "Lorem Ipsum"],
|
||||||
|
["published_at", "1296962229"],
|
||||||
|
["t", "electronics"],
|
||||||
|
["image", "https://url.to.img", "256x256"],
|
||||||
|
["summary", "More lorem ipsum that is a little more than the title"],
|
||||||
|
["location", "NYC"],
|
||||||
|
["price", "100", "USD"],
|
||||||
|
[
|
||||||
|
"e",
|
||||||
|
"b3e392b11f5d4f28321cedd09303a748acfd0487aea5a7450b3481c60b6e4f87",
|
||||||
|
"wss://relay.example.com"
|
||||||
|
],
|
||||||
|
[
|
||||||
|
"a",
|
||||||
|
"30023:a695f6b60119d9521934a691347d9f78e8770b56da16bb255ee286ddf9fda919:ipsum",
|
||||||
|
"wss://relay.nostr.org"
|
||||||
|
]
|
||||||
|
],
|
||||||
|
"pubkey": "...",
|
||||||
|
"id": "..."
|
||||||
|
}
|
||||||
|
```
|
||||||
49
BREAKING.md
Normal file
49
BREAKING.md
Normal file
|
|
@ -0,0 +1,49 @@
|
||||||
|
# Breaking Changes
|
||||||
|
|
||||||
|
This is a history of NIP changes that potentially break pre-existing implementations, in
|
||||||
|
reverse chronological order.
|
||||||
|
|
||||||
|
| Date | Commit | NIP | Change |
|
||||||
|
| ----------- | --------- | -------- | ------ |
|
||||||
|
| 2024-05-25 | [5d1d1c17](https://github.com/nostr-protocol/nips/commit/5d1d1c17) | [NIP-71](71.md) | 'aes-256-gcm' tag was removed |
|
||||||
|
| 2024-04-30 | [bad88262](https://github.com/nostr-protocol/nips/commit/bad88262) | [NIP-34](34.md) | 'earliest-unique-commit' tag was removed (use 'r' tag instead) |
|
||||||
|
| 2024-02-25 | [4a171cb0](https://github.com/nostr-protocol/nips/commit/4a171cb0) | [NIP-18](18.md) | quote repost should use `q` tag |
|
||||||
|
| 2024-02-21 | [c6cd655c](https://github.com/nostr-protocol/nips/commit/c6cd655c) | [NIP-46](46.md) | Params were stringified |
|
||||||
|
| 2024-02-16 | [cbec02ab](https://github.com/nostr-protocol/nips/commit/cbec02ab) | [NIP-49](49.md) | Password first normalized to NFKC |
|
||||||
|
| 2024-02-15 | [afbb8dd0](https://github.com/nostr-protocol/nips/commit/afbb8dd0) | [NIP-39](39.md) | PGP identity was removed |
|
||||||
|
| 2024-02-07 | [d3dad114](https://github.com/nostr-protocol/nips/commit/d3dad114) | [NIP-46](46.md) | Connection token format was changed |
|
||||||
|
| 2024-01-30 | [1a2b21b6](https://github.com/nostr-protocol/nips/commit/1a2b21b6) | [NIP-59](59.md) | 'p' tag became optional |
|
||||||
|
| 2023-01-27 | [c2f34817](https://github.com/nostr-protocol/nips/commit/c2f34817) | [NIP-47](47.md) | optional expiration tag should be honored |
|
||||||
|
| 2024-01-10 | [3d8652ea](https://github.com/nostr-protocol/nips/commit/3d8652ea) | [NIP-02](02.md) | list entries should be chronological |
|
||||||
|
| 2024-01-10 | [3d8652ea](https://github.com/nostr-protocol/nips/commit/3d8652ea) | [NIP-51](51.md) | list entries should be chronological |
|
||||||
|
| 2023-12-30 | [29869821](https://github.com/nostr-protocol/nips/commit/29869821) | [NIP-52](52.md) | 'name' tag was removed (use 'title' tag instead) |
|
||||||
|
| 2023-12-27 | [17c67ef5](https://github.com/nostr-protocol/nips/commit/17c67ef5) | [NIP-94](94.md) | 'aes-256-gcm' tag was removed |
|
||||||
|
| 2023-12-03 | [0ba45895](https://github.com/nostr-protocol/nips/commit/0ba45895) | [NIP-01](01.md) | WebSocket status code `4000` was replaced by 'CLOSED' message |
|
||||||
|
| 2023-11-28 | [6de35f9e](https://github.com/nostr-protocol/nips/commit/6de35f9e) | [NIP-89](89.md) | 'client' tag value was changed |
|
||||||
|
| 2023-11-20 | [7822a8b1](https://github.com/nostr-protocol/nips/commit/7822a8b1) | [NIP-51](51.md) | `kind: 30000` and `kind: 30001` were deprecated |
|
||||||
|
| 2023-11-11 | [cbdca1e9](https://github.com/nostr-protocol/nips/commit/cbdca1e9) | [NIP-84](84.md) | 'range' tag was removed |
|
||||||
|
| 2023-11-07 | [108b7f16](https://github.com/nostr-protocol/nips/commit/108b7f16) | [NIP-01](01.md) | 'OK' message must have 4 items |
|
||||||
|
| 2023-10-17 | [cf672b76](https://github.com/nostr-protocol/nips/commit/cf672b76) | [NIP-03](03.md) | 'block' tag was removed |
|
||||||
|
| 2023-09-29 | [7dc6385f](https://github.com/nostr-protocol/nips/commit/7dc6385f) | [NIP-57](57.md) | optional 'a' tag was included in `zap receipt` |
|
||||||
|
| 2023-08-21 | [89915e02](https://github.com/nostr-protocol/nips/commit/89915e02) | [NIP-11](11.md) | 'min_prefix' was removed |
|
||||||
|
| 2023-08-20 | [37c4375e](https://github.com/nostr-protocol/nips/commit/37c4375e) | [NIP-01](01.md) | replaceable events with same timestamp should be retained event with lowest id |
|
||||||
|
| 2023-08-15 | [88ee873c](https://github.com/nostr-protocol/nips/commit/88ee873c) | [NIP-15](15.md) | 'countries' tag was renamed to 'regions' |
|
||||||
|
| 2023-08-14 | [72bb8a12](https://github.com/nostr-protocol/nips/commit/72bb8a12) | [NIP-12](12.md) | NIP-12, 16, 20 and 33 were merged into NIP-01 |
|
||||||
|
| 2023-08-14 | [72bb8a12](https://github.com/nostr-protocol/nips/commit/72bb8a12) | [NIP-16](16.md) | NIP-12, 16, 20 and 33 were merged into NIP-01 |
|
||||||
|
| 2023-08-14 | [72bb8a12](https://github.com/nostr-protocol/nips/commit/72bb8a12) | [NIP-20](20.md) | NIP-12, 16, 20 and 33 were merged into NIP-01 |
|
||||||
|
| 2023-08-14 | [72bb8a12](https://github.com/nostr-protocol/nips/commit/72bb8a12) | [NIP-33](33.md) | NIP-12, 16, 20 and 33 were merged into NIP-01 |
|
||||||
|
| 2023-08-11 | [d87f8617](https://github.com/nostr-protocol/nips/commit/d87f8617) | [NIP-25](25.md) | empty `content` should be considered as "+" |
|
||||||
|
| 2023-08-01 | [5d63b157](https://github.com/nostr-protocol/nips/commit/5d63b157) | [NIP-57](57.md) | 'zap' tag was changed |
|
||||||
|
| 2023-07-15 | [d1814405](https://github.com/nostr-protocol/nips/commit/d1814405) | [NIP-01](01.md) | `since` and `until` filters should be `since <= created_at <= until` |
|
||||||
|
| 2023-07-12 | [a1cd2bd8](https://github.com/nostr-protocol/nips/commit/a1cd2bd8) | [NIP-25](25.md) | custom emoji was supported |
|
||||||
|
| 2023-06-18 | [83cbd3e1](https://github.com/nostr-protocol/nips/commit/83cbd3e1) | [NIP-11](11.md) | 'image' was renamed to 'icon' |
|
||||||
|
| 2023-04-13 | [bf0a0da6](https://github.com/nostr-protocol/nips/commit/bf0a0da6) | [NIP-15](15.md) | different NIP was re-added as NIP-15 |
|
||||||
|
| 2023-04-09 | [fb5b7c73](https://github.com/nostr-protocol/nips/commit/fb5b7c73) | [NIP-15](15.md) | NIP-15 was merged into NIP-01 |
|
||||||
|
| 2023-03-15 | [e1004d3d](https://github.com/nostr-protocol/nips/commit/e1004d3d) | [NIP-19](19.md) | `1: relay` was changed to optionally |
|
||||||
|
|
||||||
|
Breaking changes prior to 2023-03-01 are not yet documented.
|
||||||
|
|
||||||
|
## NOTES
|
||||||
|
|
||||||
|
- If it isn't clear that a change is breaking or not, we list it.
|
||||||
|
- The date is the date it was merged, not necessarily the date of the commit.
|
||||||
233
README.md
233
README.md
|
|
@ -1,18 +1,21 @@
|
||||||
# NIPs
|
# NIPs
|
||||||
|
|
||||||
NIPs stand for **Nostr Implementation Possibilities**.
|
NIPs stand for **Nostr Implementation Possibilities**.
|
||||||
|
|
||||||
They exist to document what may be implemented by [Nostr](https://github.com/nostr-protocol/nostr)-compatible _relay_ and _client_ software.
|
They exist to document what may be implemented by [Nostr](https://github.com/nostr-protocol/nostr)-compatible _relay_ and _client_ software.
|
||||||
|
|
||||||
---
|
---
|
||||||
|
|
||||||
- [List](#list)
|
- [List](#list)
|
||||||
- [Event Kinds](#event-kinds)
|
- [Event Kinds](#event-kinds)
|
||||||
- [Event Kind Ranges](#event-kind-ranges)
|
|
||||||
- [Message Types](#message-types)
|
- [Message Types](#message-types)
|
||||||
- [Client to Relay](#client-to-relay)
|
- [Client to Relay](#client-to-relay)
|
||||||
- [Relay to Client](#relay-to-client)
|
- [Relay to Client](#relay-to-client)
|
||||||
- [Standardized Tags](#standardized-tags)
|
- [Standardized Tags](#standardized-tags)
|
||||||
- [Criteria for acceptance of NIPs](#criteria-for-acceptance-of-nips)
|
- [Criteria for acceptance of NIPs](#criteria-for-acceptance-of-nips)
|
||||||
|
- [Is this repository a centralizing factor?](#is-this-repository-a-centralizing-factor)
|
||||||
|
- [How this repository works](#how-this-repository-works)
|
||||||
|
- [Breaking Changes](#breaking-changes)
|
||||||
- [License](#license)
|
- [License](#license)
|
||||||
|
|
||||||
---
|
---
|
||||||
|
|
@ -20,9 +23,9 @@ They exist to document what may be implemented by [Nostr](https://github.com/nos
|
||||||
## List
|
## List
|
||||||
|
|
||||||
- [NIP-01: Basic protocol flow description](01.md)
|
- [NIP-01: Basic protocol flow description](01.md)
|
||||||
- [NIP-02: Contact List and Petnames](02.md)
|
- [NIP-02: Follow List](02.md)
|
||||||
- [NIP-03: OpenTimestamps Attestations for Events](03.md)
|
- [NIP-03: OpenTimestamps Attestations for Events](03.md)
|
||||||
- [NIP-04: Encrypted Direct Message](04.md)
|
- [NIP-04: Encrypted Direct Message](04.md) --- **unrecommended**: deprecated in favor of [NIP-17](17.md)
|
||||||
- [NIP-05: Mapping Nostr keys to DNS-based internet identifiers](05.md)
|
- [NIP-05: Mapping Nostr keys to DNS-based internet identifiers](05.md)
|
||||||
- [NIP-06: Basic key derivation from mnemonic seed phrase](06.md)
|
- [NIP-06: Basic key derivation from mnemonic seed phrase](06.md)
|
||||||
- [NIP-07: `window.nostr` capability for web browsers](07.md)
|
- [NIP-07: `window.nostr` capability for web browsers](07.md)
|
||||||
|
|
@ -30,95 +33,171 @@ They exist to document what may be implemented by [Nostr](https://github.com/nos
|
||||||
- [NIP-09: Event Deletion](09.md)
|
- [NIP-09: Event Deletion](09.md)
|
||||||
- [NIP-10: Conventions for clients' use of `e` and `p` tags in text events](10.md)
|
- [NIP-10: Conventions for clients' use of `e` and `p` tags in text events](10.md)
|
||||||
- [NIP-11: Relay Information Document](11.md)
|
- [NIP-11: Relay Information Document](11.md)
|
||||||
- [NIP-12: Generic Tag Queries](12.md)
|
|
||||||
- [NIP-13: Proof of Work](13.md)
|
- [NIP-13: Proof of Work](13.md)
|
||||||
- [NIP-14: Subject tag in text events.](14.md)
|
- [NIP-14: Subject tag in text events](14.md)
|
||||||
- [NIP-15: Nostr Marketplace (for resilient marketplaces)](15.md)
|
- [NIP-15: Nostr Marketplace (for resilient marketplaces)](15.md)
|
||||||
- [NIP-16: Event Treatment](16.md)
|
- [NIP-17: Private Direct Messages](17.md)
|
||||||
- [NIP-18: Reposts](18.md)
|
- [NIP-18: Reposts](18.md)
|
||||||
- [NIP-19: bech32-encoded entities](19.md)
|
- [NIP-19: bech32-encoded entities](19.md)
|
||||||
- [NIP-20: Command Results](20.md)
|
- [NIP-21: `nostr:` URI scheme](21.md)
|
||||||
- [NIP-21: `nostr:` URL scheme](21.md)
|
|
||||||
- [NIP-22: Event `created_at` Limits](22.md)
|
|
||||||
- [NIP-23: Long-form Content](23.md)
|
- [NIP-23: Long-form Content](23.md)
|
||||||
|
- [NIP-24: Extra metadata fields and tags](24.md)
|
||||||
- [NIP-25: Reactions](25.md)
|
- [NIP-25: Reactions](25.md)
|
||||||
- [NIP-26: Delegated Event Signing](26.md)
|
- [NIP-26: Delegated Event Signing](26.md)
|
||||||
- [NIP-27: Text Note References](27.md)
|
- [NIP-27: Text Note References](27.md)
|
||||||
- [NIP-28: Public Chat](28.md)
|
- [NIP-28: Public Chat](28.md)
|
||||||
|
- [NIP-29: Relay-based Groups](29.md)
|
||||||
- [NIP-30: Custom Emoji](30.md)
|
- [NIP-30: Custom Emoji](30.md)
|
||||||
- [NIP-31: Dealing with Unknown Events](31.md)
|
- [NIP-31: Dealing with Unknown Events](31.md)
|
||||||
- [NIP-32: Labeling](32.md)
|
- [NIP-32: Labeling](32.md)
|
||||||
- [NIP-33: Parameterized Replaceable Events](33.md)
|
- [NIP-34: `git` stuff](34.md)
|
||||||
|
- [NIP-35: Torrents](35.md)
|
||||||
- [NIP-36: Sensitive Content](36.md)
|
- [NIP-36: Sensitive Content](36.md)
|
||||||
|
- [NIP-38: User Statuses](38.md)
|
||||||
- [NIP-39: External Identities in Profiles](39.md)
|
- [NIP-39: External Identities in Profiles](39.md)
|
||||||
- [NIP-40: Expiration Timestamp](40.md)
|
- [NIP-40: Expiration Timestamp](40.md)
|
||||||
- [NIP-42: Authentication of clients to relays](42.md)
|
- [NIP-42: Authentication of clients to relays](42.md)
|
||||||
|
- [NIP-44: Versioned Encryption](44.md)
|
||||||
- [NIP-45: Counting results](45.md)
|
- [NIP-45: Counting results](45.md)
|
||||||
- [NIP-46: Nostr Connect](46.md)
|
- [NIP-46: Nostr Connect](46.md)
|
||||||
- [NIP-47: Wallet Connect](47.md)
|
- [NIP-47: Wallet Connect](47.md)
|
||||||
- [NIP-50: Keywords filter](50.md)
|
- [NIP-48: Proxy Tags](48.md)
|
||||||
|
- [NIP-49: Private Key Encryption](49.md)
|
||||||
|
- [NIP-50: Search Capability](50.md)
|
||||||
- [NIP-51: Lists](51.md)
|
- [NIP-51: Lists](51.md)
|
||||||
|
- [NIP-52: Calendar Events](52.md)
|
||||||
|
- [NIP-53: Live Activities](53.md)
|
||||||
|
- [NIP-54: Wiki](54.md)
|
||||||
- [NIP-56: Reporting](56.md)
|
- [NIP-56: Reporting](56.md)
|
||||||
- [NIP-57: Lightning Zaps](57.md)
|
- [NIP-57: Lightning Zaps](57.md)
|
||||||
- [NIP-58: Badges](58.md)
|
- [NIP-58: Badges](58.md)
|
||||||
|
- [NIP-59: Gift Wrap](59.md)
|
||||||
- [NIP-65: Relay List Metadata](65.md)
|
- [NIP-65: Relay List Metadata](65.md)
|
||||||
|
- [NIP-71: Video Events](71.md)
|
||||||
|
- [NIP-72: Moderated Communities](72.md)
|
||||||
|
- [NIP-75: Zap Goals](75.md)
|
||||||
- [NIP-78: Application-specific data](78.md)
|
- [NIP-78: Application-specific data](78.md)
|
||||||
|
- [NIP-84: Highlights](84.md)
|
||||||
- [NIP-89: Recommended Application Handlers](89.md)
|
- [NIP-89: Recommended Application Handlers](89.md)
|
||||||
|
- [NIP-90: Data Vending Machines](90.md)
|
||||||
|
- [NIP-92: Media Attachments](92.md)
|
||||||
- [NIP-94: File Metadata](94.md)
|
- [NIP-94: File Metadata](94.md)
|
||||||
|
- [NIP-96: HTTP File Storage Integration](96.md)
|
||||||
- [NIP-98: HTTP Auth](98.md)
|
- [NIP-98: HTTP Auth](98.md)
|
||||||
|
- [NIP-99: Classified Listings](99.md)
|
||||||
|
|
||||||
## Event Kinds
|
## Event Kinds
|
||||||
|
|
||||||
| kind | description | NIP |
|
| kind | description | NIP |
|
||||||
| ------- | -------------------------- | ----------- |
|
| ------------- | -------------------------- | ------------------------ |
|
||||||
| `0` | Metadata | [1](01.md) |
|
| `0` | Metadata | [01](01.md) |
|
||||||
| `1` | Short Text Note | [1](01.md) |
|
| `1` | Short Text Note | [01](01.md) |
|
||||||
| `2` | Recommend Relay | [1](01.md) |
|
| `2` | Recommend Relay | 01 (deprecated) |
|
||||||
| `3` | Contacts | [2](02.md) |
|
| `3` | Follows | [02](02.md) |
|
||||||
| `4` | Encrypted Direct Messages | [4](04.md) |
|
| `4` | Encrypted Direct Messages | [04](04.md) |
|
||||||
| `5` | Event Deletion | [9](09.md) |
|
| `5` | Event Deletion | [09](09.md) |
|
||||||
| `6` | Repost | [18](18.md) |
|
| `6` | Repost | [18](18.md) |
|
||||||
| `7` | Reaction | [25](25.md) |
|
| `7` | Reaction | [25](25.md) |
|
||||||
| `8` | Badge Award | [58](58.md) |
|
| `8` | Badge Award | [58](58.md) |
|
||||||
|
| `9` | Group Chat Message | [29](29.md) |
|
||||||
|
| `10` | Group Chat Threaded Reply | [29](29.md) |
|
||||||
|
| `11` | Group Thread | [29](29.md) |
|
||||||
|
| `12` | Group Thread Reply | [29](29.md) |
|
||||||
|
| `13` | Seal | [59](59.md) |
|
||||||
|
| `14` | Direct Message | [17](17.md) |
|
||||||
| `16` | Generic Repost | [18](18.md) |
|
| `16` | Generic Repost | [18](18.md) |
|
||||||
| `40` | Channel Creation | [28](28.md) |
|
| `40` | Channel Creation | [28](28.md) |
|
||||||
| `41` | Channel Metadata | [28](28.md) |
|
| `41` | Channel Metadata | [28](28.md) |
|
||||||
| `42` | Channel Message | [28](28.md) |
|
| `42` | Channel Message | [28](28.md) |
|
||||||
| `43` | Channel Hide Message | [28](28.md) |
|
| `43` | Channel Hide Message | [28](28.md) |
|
||||||
| `44` | Channel Mute User | [28](28.md) |
|
| `44` | Channel Mute User | [28](28.md) |
|
||||||
|
| `818` | Merge Requests | [54](54.md) |
|
||||||
|
| `1021` | Bid | [15](15.md) |
|
||||||
|
| `1022` | Bid confirmation | [15](15.md) |
|
||||||
|
| `1040` | OpenTimestamps | [03](03.md) |
|
||||||
|
| `1059` | Gift Wrap | [59](59.md) |
|
||||||
| `1063` | File Metadata | [94](94.md) |
|
| `1063` | File Metadata | [94](94.md) |
|
||||||
|
| `1311` | Live Chat Message | [53](53.md) |
|
||||||
|
| `1617` | Patches | [34](34.md) |
|
||||||
|
| `1621` | Issues | [34](34.md) |
|
||||||
|
| `1622` | Replies | [34](34.md) |
|
||||||
|
| `1630`-`1633` | Status | [34](34.md) |
|
||||||
|
| `1971` | Problem Tracker | [nostrocket][nostrocket] |
|
||||||
| `1984` | Reporting | [56](56.md) |
|
| `1984` | Reporting | [56](56.md) |
|
||||||
| `1985` | Label | [32](32.md) |
|
| `1985` | Label | [32](32.md) |
|
||||||
|
| `2003` | Torrent | [35](35.md) |
|
||||||
|
| `2004` | Torrent Comment | [35](35.md) |
|
||||||
|
| `2022` | Coinjoin Pool | [joinstr][joinstr] |
|
||||||
|
| `4550` | Community Post Approval | [72](72.md) |
|
||||||
|
| `5000`-`5999` | Job Request | [90](90.md) |
|
||||||
|
| `6000`-`6999` | Job Result | [90](90.md) |
|
||||||
|
| `7000` | Job Feedback | [90](90.md) |
|
||||||
|
| `9000`-`9030` | Group Control Events | [29](29.md) |
|
||||||
|
| `9041` | Zap Goal | [75](75.md) |
|
||||||
| `9734` | Zap Request | [57](57.md) |
|
| `9734` | Zap Request | [57](57.md) |
|
||||||
| `9735` | Zap | [57](57.md) |
|
| `9735` | Zap | [57](57.md) |
|
||||||
| `10000` | Mute List | [51](51.md) |
|
| `9802` | Highlights | [84](84.md) |
|
||||||
| `10001` | Pin List | [51](51.md) |
|
| `10000` | Mute list | [51](51.md) |
|
||||||
|
| `10001` | Pin list | [51](51.md) |
|
||||||
| `10002` | Relay List Metadata | [65](65.md) |
|
| `10002` | Relay List Metadata | [65](65.md) |
|
||||||
|
| `10003` | Bookmark list | [51](51.md) |
|
||||||
|
| `10004` | Communities list | [51](51.md) |
|
||||||
|
| `10005` | Public chats list | [51](51.md) |
|
||||||
|
| `10006` | Blocked relays list | [51](51.md) |
|
||||||
|
| `10007` | Search relays list | [51](51.md) |
|
||||||
|
| `10009` | User groups | [51](51.md), [29](29.md) |
|
||||||
|
| `10015` | Interests list | [51](51.md) |
|
||||||
|
| `10030` | User emoji list | [51](51.md) |
|
||||||
|
| `10050` | Relay list to receive DMs | [17](17.md) |
|
||||||
|
| `10096` | File storage server list | [96](96.md) |
|
||||||
| `13194` | Wallet Info | [47](47.md) |
|
| `13194` | Wallet Info | [47](47.md) |
|
||||||
|
| `21000` | Lightning Pub RPC | [Lightning.Pub][lnpub] |
|
||||||
| `22242` | Client Authentication | [42](42.md) |
|
| `22242` | Client Authentication | [42](42.md) |
|
||||||
| `23194` | Wallet Request | [47](47.md) |
|
| `23194` | Wallet Request | [47](47.md) |
|
||||||
| `23195` | Wallet Response | [47](47.md) |
|
| `23195` | Wallet Response | [47](47.md) |
|
||||||
| `24133` | Nostr Connect | [46](46.md) |
|
| `24133` | Nostr Connect | [46](46.md) |
|
||||||
| `27235` | HTTP Auth | [98](98.md) |
|
| `27235` | HTTP Auth | [98](98.md) |
|
||||||
| `30000` | Categorized People List | [51](51.md) |
|
| `30000` | Follow sets | [51](51.md) |
|
||||||
| `30001` | Categorized Bookmark List | [51](51.md) |
|
| `30001` | Generic lists | [51](51.md) |
|
||||||
|
| `30002` | Relay sets | [51](51.md) |
|
||||||
|
| `30003` | Bookmark sets | [51](51.md) |
|
||||||
|
| `30004` | Curation sets | [51](51.md) |
|
||||||
|
| `30005` | Video sets | [51](51.md) |
|
||||||
| `30008` | Profile Badges | [58](58.md) |
|
| `30008` | Profile Badges | [58](58.md) |
|
||||||
| `30009` | Badge Definition | [58](58.md) |
|
| `30009` | Badge Definition | [58](58.md) |
|
||||||
|
| `30015` | Interest sets | [51](51.md) |
|
||||||
| `30017` | Create or update a stall | [15](15.md) |
|
| `30017` | Create or update a stall | [15](15.md) |
|
||||||
| `30018` | Create or update a product | [15](15.md) |
|
| `30018` | Create or update a product | [15](15.md) |
|
||||||
|
| `30019` | Marketplace UI/UX | [15](15.md) |
|
||||||
|
| `30020` | Product sold as an auction | [15](15.md) |
|
||||||
| `30023` | Long-form Content | [23](23.md) |
|
| `30023` | Long-form Content | [23](23.md) |
|
||||||
|
| `30024` | Draft Long-form Content | [23](23.md) |
|
||||||
|
| `30030` | Emoji sets | [51](51.md) |
|
||||||
|
| `30063` | Release artifact sets | [51](51.md) |
|
||||||
| `30078` | Application-specific Data | [78](78.md) |
|
| `30078` | Application-specific Data | [78](78.md) |
|
||||||
|
| `30311` | Live Event | [53](53.md) |
|
||||||
|
| `30315` | User Statuses | [38](38.md) |
|
||||||
|
| `30402` | Classified Listing | [99](99.md) |
|
||||||
|
| `30403` | Draft Classified Listing | [99](99.md) |
|
||||||
|
| `30617` | Repository announcements | [34](34.md) |
|
||||||
|
| `30818` | Wiki article | [54](54.md) |
|
||||||
|
| `30819` | Redirects | [54](54.md) |
|
||||||
|
| `31890` | Feed | [NUD: Custom Feeds](https://wikifreedia.xyz/cip-01/97c70a44366a6535c1) |
|
||||||
|
| `31922` | Date-Based Calendar Event | [52](52.md) |
|
||||||
|
| `31923` | Time-Based Calendar Event | [52](52.md) |
|
||||||
|
| `31924` | Calendar | [52](52.md) |
|
||||||
|
| `31925` | Calendar Event RSVP | [52](52.md) |
|
||||||
| `31989` | Handler recommendation | [89](89.md) |
|
| `31989` | Handler recommendation | [89](89.md) |
|
||||||
| `31990` | Handler information | [89](89.md) |
|
| `31990` | Handler information | [89](89.md) |
|
||||||
|
| `34235` | Video Event | [71](71.md) |
|
||||||
|
| `34236` | Short-form Portrait Video Event | [71](71.md) |
|
||||||
|
| `34237` | Video View Event | [71](71.md) |
|
||||||
|
| `34550` | Community Definition | [72](72.md) |
|
||||||
|
| `39000-9` | Group metadata events | [29](29.md) |
|
||||||
|
|
||||||
### Event Kind Ranges
|
[NUD: Custom Feeds]: https://wikifreedia.xyz/cip-01/97c70a44366a6535c1
|
||||||
|
[nostrocket]: https://github.com/nostrocket/NIPS/blob/main/Problems.md
|
||||||
| range | description | NIP |
|
[lnpub]: https://github.com/shocknet/Lightning.Pub/blob/master/proto/autogenerated/client.md
|
||||||
| ---------------- | -------------------------------- | ----------- |
|
[joinstr]: https://gitlab.com/1440000bytes/joinstr/-/blob/main/NIP.md
|
||||||
| `1000`--`9999` | Regular Events | [16](16.md) |
|
|
||||||
| `10000`--`19999` | Replaceable Events | [16](16.md) |
|
|
||||||
| `20000`--`29999` | Ephemeral Events | [16](16.md) |
|
|
||||||
| `30000`--`39999` | Parameterized Replaceable Events | [33](33.md) |
|
|
||||||
|
|
||||||
## Message types
|
## Message types
|
||||||
|
|
||||||
|
|
@ -126,73 +205,109 @@ They exist to document what may be implemented by [Nostr](https://github.com/nos
|
||||||
|
|
||||||
| type | description | NIP |
|
| type | description | NIP |
|
||||||
| ------- | --------------------------------------------------- | ----------- |
|
| ------- | --------------------------------------------------- | ----------- |
|
||||||
|
| `EVENT` | used to publish events | [01](01.md) |
|
||||||
|
| `REQ` | used to request events and subscribe to new updates | [01](01.md) |
|
||||||
|
| `CLOSE` | used to stop previous subscriptions | [01](01.md) |
|
||||||
| `AUTH` | used to send authentication events | [42](42.md) |
|
| `AUTH` | used to send authentication events | [42](42.md) |
|
||||||
| `CLOSE` | used to stop previous subscriptions | [1](01.md) |
|
|
||||||
| `COUNT` | used to request event counts | [45](45.md) |
|
| `COUNT` | used to request event counts | [45](45.md) |
|
||||||
| `EVENT` | used to publish events | [1](01.md) |
|
|
||||||
| `REQ` | used to request events and subscribe to new updates | [1](01.md) |
|
|
||||||
|
|
||||||
### Relay to Client
|
### Relay to Client
|
||||||
|
|
||||||
| type | description | NIP |
|
| type | description | NIP |
|
||||||
| -------- | ------------------------------------------------------- | ----------- |
|
| -------- | ------------------------------------------------------- | ----------- |
|
||||||
|
| `EOSE` | used to notify clients all stored events have been sent | [01](01.md) |
|
||||||
|
| `EVENT` | used to send events requested to clients | [01](01.md) |
|
||||||
|
| `NOTICE` | used to send human-readable messages to clients | [01](01.md) |
|
||||||
|
| `OK` | used to notify clients if an EVENT was successful | [01](01.md) |
|
||||||
|
| `CLOSED` | used to notify clients that a REQ was ended and why | [01](01.md) |
|
||||||
| `AUTH` | used to send authentication challenges | [42](42.md) |
|
| `AUTH` | used to send authentication challenges | [42](42.md) |
|
||||||
| `COUNT` | used to send requested event counts to clients | [45](45.md) |
|
| `COUNT` | used to send requested event counts to clients | [45](45.md) |
|
||||||
| `EOSE` | used to notify clients all stored events have been sent | [1](01.md) |
|
|
||||||
| `EVENT` | used to send events requested to clients | [1](01.md) |
|
|
||||||
| `NOTICE` | used to send human-readable messages to clients | [1](01.md) |
|
|
||||||
| `OK` | used to notify clients if an EVENT was successful | [20](20.md) |
|
|
||||||
|
|
||||||
Please update these lists when proposing NIPs introducing new event kinds.
|
Please update these lists when proposing NIPs introducing new event kinds.
|
||||||
|
|
||||||
When experimenting with kinds, keep in mind the classification introduced by [NIP-16](16.md) and [NIP-33](33.md).
|
|
||||||
|
|
||||||
## Standardized Tags
|
## Standardized Tags
|
||||||
|
|
||||||
| name | value | other parameters | NIP |
|
| name | value | other parameters | NIP |
|
||||||
| ----------------- | ------------------------------------ | -------------------- | ------------------------ |
|
| ----------------- | ------------------------------------ | ------------------------------- | ------------------------------------- |
|
||||||
| `a` | coordinates to an event | relay URL | [33](33.md), [23](23.md) |
|
| `e` | event id (hex) | relay URL, marker, pubkey (hex) | [01](01.md), [10](10.md) |
|
||||||
| `alt` | Alt tag | -- | [31](31.md) |
|
| `p` | pubkey (hex) | relay URL, petname | [01](01.md), [02](02.md) |
|
||||||
| `d` | identifier | -- | [33](33.md) |
|
| `a` | coordinates to an event | relay URL | [01](01.md) |
|
||||||
| `e` | event id (hex) | relay URL, marker | [1](01.md), [10](10.md) |
|
| `d` | identifier | -- | [01](01.md) |
|
||||||
| `g` | geohash | -- | [12](12.md) |
|
| `g` | geohash | -- | [52](52.md) |
|
||||||
| `i` | identity | proof | [39](39.md) |
|
| `i` | identity | proof | [39](39.md) |
|
||||||
|
| `k` | kind number (string) | -- | [18](18.md), [25](25.md), [72](72.md) |
|
||||||
| `l` | label, label namespace | annotations | [32](32.md) |
|
| `l` | label, label namespace | annotations | [32](32.md) |
|
||||||
| `L` | label namespace | -- | [32](32.md) |
|
| `L` | label namespace | -- | [32](32.md) |
|
||||||
| `p` | pubkey (hex) | relay URL | [1](01.md) |
|
| `m` | MIME type | -- | [94](94.md) |
|
||||||
| `r` | a reference (URL, etc) | -- | [12](12.md) |
|
| `q` | event id (hex) | relay URL | [18](18.md) |
|
||||||
| `t` | hashtag | -- | [12](12.md) |
|
| `r` | a reference (URL, etc) | petname | |
|
||||||
| `amount` | millisats | -- | [57](57.md) |
|
| `r` | relay url | marker | [65](65.md) |
|
||||||
|
| `t` | hashtag | -- | |
|
||||||
|
| `alt` | summary | -- | [31](31.md) |
|
||||||
|
| `amount` | millisatoshis, stringified | -- | [57](57.md) |
|
||||||
| `bolt11` | `bolt11` invoice | -- | [57](57.md) |
|
| `bolt11` | `bolt11` invoice | -- | [57](57.md) |
|
||||||
| `challenge` | challenge string | -- | [42](42.md) |
|
| `challenge` | challenge string | -- | [42](42.md) |
|
||||||
|
| `client` | name, address | relay URL | [89](89.md) |
|
||||||
|
| `clone` | git clone URL | -- | [34](34.md) |
|
||||||
| `content-warning` | reason | -- | [36](36.md) |
|
| `content-warning` | reason | -- | [36](36.md) |
|
||||||
| `delegation` | pubkey, conditions, delegation token | -- | [26](26.md) |
|
| `delegation` | pubkey, conditions, delegation token | -- | [26](26.md) |
|
||||||
| `description` | badge description | -- | [58](58.md) |
|
| `description` | description | -- | [34](34.md), [57](57.md), [58](58.md) |
|
||||||
| `description` | invoice description | -- | [57](57.md) |
|
| `emoji` | shortcode, image URL | -- | [30](30.md) |
|
||||||
| `emoji` | shortcode | image URL | [30](30.md) |
|
| `encrypted` | -- | -- | [90](90.md) |
|
||||||
| `expiration` | unix timestamp (string) | -- | [40](40.md) |
|
| `expiration` | unix timestamp (string) | -- | [40](40.md) |
|
||||||
|
| `goal` | event id (hex) | relay URL | [75](75.md) |
|
||||||
| `image` | image URL | dimensions in pixels | [23](23.md), [58](58.md) |
|
| `image` | image URL | dimensions in pixels | [23](23.md), [58](58.md) |
|
||||||
|
| `imeta` | inline metadata | -- | [92](92.md) |
|
||||||
| `lnurl` | `bech32` encoded `lnurl` | -- | [57](57.md) |
|
| `lnurl` | `bech32` encoded `lnurl` | -- | [57](57.md) |
|
||||||
| `name` | badge name | -- | [58](58.md) |
|
| `location` | location string | -- | [52](52.md), [99](99.md) |
|
||||||
| `nonce` | random | -- | [13](13.md) |
|
| `name` | name | -- | [34](34.md), [58](58.md) |
|
||||||
|
| `nonce` | random | difficulty | [13](13.md) |
|
||||||
| `preimage` | hash of `bolt11` invoice | -- | [57](57.md) |
|
| `preimage` | hash of `bolt11` invoice | -- | [57](57.md) |
|
||||||
|
| `price` | price | currency, frequency | [99](99.md) |
|
||||||
|
| `proxy` | external ID | protocol | [48](48.md) |
|
||||||
| `published_at` | unix timestamp (string) | -- | [23](23.md) |
|
| `published_at` | unix timestamp (string) | -- | [23](23.md) |
|
||||||
| `relay` | relay url | -- | [42](42.md) |
|
| `relay` | relay url | -- | [42](42.md), [17](17.md) |
|
||||||
| `relays` | relay list | -- | [57](57.md) |
|
| `relays` | relay list | -- | [57](57.md) |
|
||||||
| `subject` | subject | -- | [14](14.md) |
|
| `server` | file storage server url | -- | [96](96.md) |
|
||||||
|
| `subject` | subject | -- | [14](14.md), [17](17.md) |
|
||||||
| `summary` | article summary | -- | [23](23.md) |
|
| `summary` | article summary | -- | [23](23.md) |
|
||||||
| `thumb` | badge thumbnail | dimensions in pixels | [58](58.md) |
|
| `thumb` | badge thumbnail | dimensions in pixels | [58](58.md) |
|
||||||
| `title` | article title | -- | [23](23.md) |
|
| `title` | article title | -- | [23](23.md) |
|
||||||
| `zap` | profile name | type of value | [57](57.md) |
|
| `web` | webpage URL | -- | [34](34.md) |
|
||||||
|
| `zap` | pubkey (hex), relay URL | weight | [57](57.md) |
|
||||||
|
|
||||||
## Criteria for acceptance of NIPs
|
## Criteria for acceptance of NIPs
|
||||||
|
|
||||||
1. They should be implemented in at least two clients and one relay -- when applicable.
|
1. They should be fully implemented in at least two clients and one relay -- when applicable.
|
||||||
2. They should make sense.
|
2. They should make sense.
|
||||||
3. They should be optional and backwards-compatible: care must be taken such that clients and relays that choose to not implement them do not stop working when interacting with the ones that choose to.
|
3. They should be optional and backwards-compatible: care must be taken such that clients and relays that choose to not implement them do not stop working when interacting with the ones that choose to.
|
||||||
4. There should be no more than one way of doing the same thing.
|
4. There should be no more than one way of doing the same thing.
|
||||||
5. Other rules will be made up when necessary.
|
5. Other rules will be made up when necessary.
|
||||||
|
|
||||||
|
## Is this repository a centralizing factor?
|
||||||
|
|
||||||
|
To promote interoperability, we standards that everybody can follow, and we need them to define a **single way of doing each thing** without ever hurting **backwards-compatibility**, and for that purpose there is no way around getting everybody to agree on the same thing and keep a centralized index of these standards. However the fact that such index exists doesn't hurt the decentralization of Nostr. _At any point the central index can be challenged if it is failing to fulfill the needs of the protocol_ and it can migrate to other places and be maintained by other people.
|
||||||
|
|
||||||
|
It can even fork into multiple and then some clients would go one way, others would go another way, and some clients would adhere to both competing standards. This would hurt the simplicity, openness and interoperability of Nostr a little, but everything would still work in the short term.
|
||||||
|
|
||||||
|
There is a list of notable Nostr software developers who have commit access to this repository, but that exists mostly for practical reasons, as by the nature of the thing we're dealing with the repository owner can revoke membership and rewrite history as they want -- and if these actions are unjustified or perceived as bad or evil the community must react.
|
||||||
|
|
||||||
|
## How this repository works
|
||||||
|
|
||||||
|
Standards may emerge in two ways: the first way is that someone starts doing something, then others copy it; the second way is that someone has an idea of a new standard that could benefit multiple clients and the protocol in general without breaking **backwards-compatibility** and the principle of having **a single way of doing things**, then they write that idea and submit it to this repository, other interested parties read it and give their feedback, then once most people reasonably agree we codify that in a NIP which client and relay developers that are interested in the feature can proceed to implement.
|
||||||
|
|
||||||
|
These two ways of standardizing things are supported by this repository. Although the second is preferred, an effort will be made to codify standards emerged outside this repository into NIPs that can be later referenced and easily understood and implemented by others -- but obviously as in any human system discretion may be applied when standards are considered harmful.
|
||||||
|
|
||||||
|
## Breaking Changes
|
||||||
|
|
||||||
|
[Breaking Changes](BREAKING.md)
|
||||||
|
|
||||||
## License
|
## License
|
||||||
|
|
||||||
All NIPs are public domain.
|
All NIPs are public domain.
|
||||||
|
|
||||||
|
## Contributors
|
||||||
|
|
||||||
|
<a align="center" href="https://github.com/nostr-protocol/nips/graphs/contributors">
|
||||||
|
<img src="https://contrib.rocks/image?repo=nostr-protocol/nips" />
|
||||||
|
</a>
|
||||||
|
|
|
||||||
Loading…
Reference in New Issue
Block a user